Microsoft and SAP Release Security Updates to Address Critical Vulnerabilities
Microsoft has released new security updates on the Patch Tuesday April 2023, to address 97 vulnerabilities. One of these flaws is a zero-day vulnerability, which has been exploited in ransomware attacks, making it particularly concerning.
Seven vulnerabilities are classified as “Critical” since they allow remote code execution, while the remaining 90 are rated as “Important” in severity.
The vulnerabilities have been classified into different categories based on their potential impact. Here are the categories and the number of vulnerabilities in each category:
- 45 Remote Code Execution Vulnerabilities
- 20 Elevation of Privilege Vulnerabilities
- 10 Information Disclosure Vulnerabilities
- 9 Denial of Service Vulnerabilities
- 8 Security Feature Bypass Vulnerabilities
- 6 Spoofing Vulnerabilities
Microsoft’s Silent Patch for SQL Server Remote Code Execution Vulnerability: CVE-2023-23384
In February, Microsoft released a patch to address a vulnerability in its SQL Server that can enable remote code execution. This is a silent patch and has been just recently documented.
The vulnerability, CVE-2023-23384 (CVSS score: 7.3, High), relates to an out-of-band write bug in the SQLcmd tool, and if exploited, it could allow an unauthenticated attacker to execute code with elevated privileges. The attack complexity is high since the attacker can only control a few bytes at a time, and a server crash is more likely.
If you are using SQL Server, it is recommended to ensure that both the February and April updates have been installed.
Microsoft Zero-Day Actively Exploited to Distribute Ransomware
Microsoft has patched an actively exploited zero-day vulnerability used by attackers to distribute a new Nokoyawa ransomware strain in attacks.
The zero-day vulnerability tracked as CVE-2023-28252 has a CVSS score of 7.8. It is a vulnerability in the Windows Common Log File System (CLFS) driver, allowing privilege escalation. Exploiting CVE-2023-28252 will enable attackers to gain SYSTEM privileges.
The Nokoyawa ransomware gang first appeared in February 2022, and the gang has used at least five more CLFS exploits to target multiple industries since June 2022.
CVE-2023-28252 affects all supported Windows server and client versions. Local attackers can exploit the zero-day vulnerability in low-complexity attacks that do not require user interaction.
CISA has also added the CVE-2023-28252 vulnerability to its Known Exploited Vulnerabilities (KEV) list, instructing agencies to patch their systems by May 2.
SAP Security Patch Day Fixes Critical Vulnerabilities
Another significant patch this month came from SAP. In its April 2023 security updates, the software vendor has released 19 new notes, which include fixes for two critical vulnerabilities.
CVE-2023-27267 (CVSS score: 9.0, Critical): The vulnerability affects the OSCommand Bridge of SAP Diagnostics Agent, version 720, due to insufficient input validation and missing authentication. An attacker could exploit CVE-2023-27267 to execute scripts on connected agents, compromising the system completely.
CVE-2023-28765 (CVSS score: 9.8, Critical): It is an Information Disclosure vulnerability affecting SAP BusinessObjects Business Intelligence Platform, versions 420 and 430. It could allow an attacker with basic privileges to decrypt the lcmbiar file. If successful, the attacker could gain access to user passwords on the platform and take over their accounts.
CVE-2023-29186 (CVSS score: 8.7, High): Another important vulnerability mentioned in the patch is a Directory Traversal vulnerability in SAP NetWeaver 707, 737, 747, and 757. It may allow for uploading and overwriting files on the vulnerable SAP server.
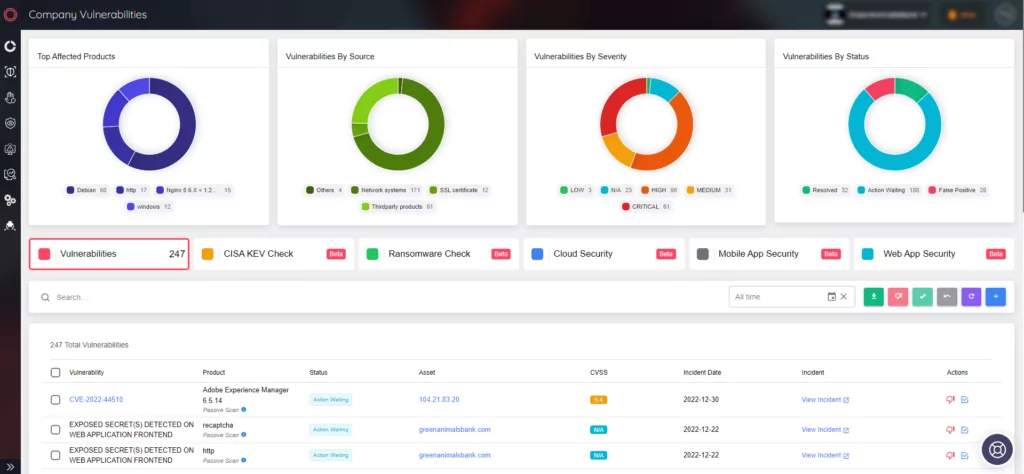
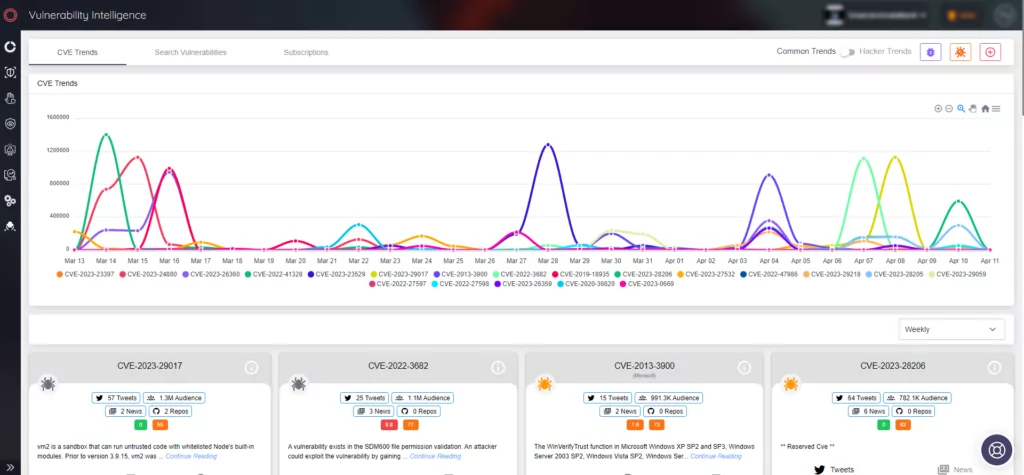
How SOCRadar Helps Organizations Stay Ahead of Vulnerabilities and Risks
SOCRadar is an effective threat intelligence platform that helps organizations stay informed about the latest vulnerabilities and risks. With its Vulnerability Intelligence module, users can easily search for and access detailed information on all known vulnerabilities, making prioritizing actions and managing patching efforts easier.
SOCRadar’s Attack Surface Management (ASM) module also enables users to discover their digital assets and receive alerts on emerging issues. The platform uses alarms to ensure that potential threats to your organization are promptly identified so that you can take the necessary measures to prevent any damage.