
New Victims of BlackCat and LockBit, Gentex Data Breach, and Education Institution Access Sales
Powered by DarkMirror™
Ransomware is on the headlines again in SOCRadar’s weekly dark web summary. Well-known cybercrime gangs LockBit and BlackCat (ALPHV) continue their attacks.
The BlackCat ransomware gang announced that they attacked Western Digital on their leak site. On the other hand, LockBit 3.0 added Banco de Venezuela to its highly long victim list.
Threat actors are not limited to “popular” names, of course. SOCRadar researchers observed small and medium-sized attacks also. Here’s the wrap-up of what happened on the dark web last week.
Find out if your data has been exposed.
The New Ransomware Victim of AlphVM BlackCat: Western Digital
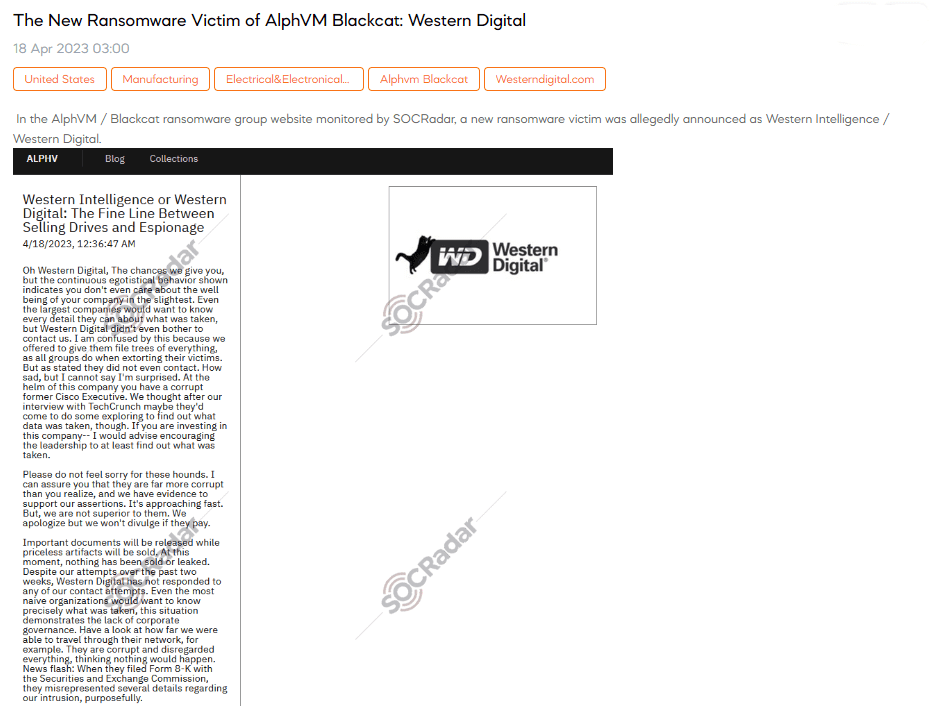
A SOCRadar dark web researcher discovered a post claiming that the AlphVM BlackCat gang had added Western Digital to its victim list. The threat actor claims they offered to provide file trees of everything they took, but Western Digital did not bother contacting them. The threat actor accuses Western Digital of being corrupt and lacking corporate governance. They also claim that the company misrepresented several details regarding the intrusion in their Form 8-K filing with the Securities and Exchange Commission.
The New Ransomware Victim of LockBit 3.0: Banco de Venezuela
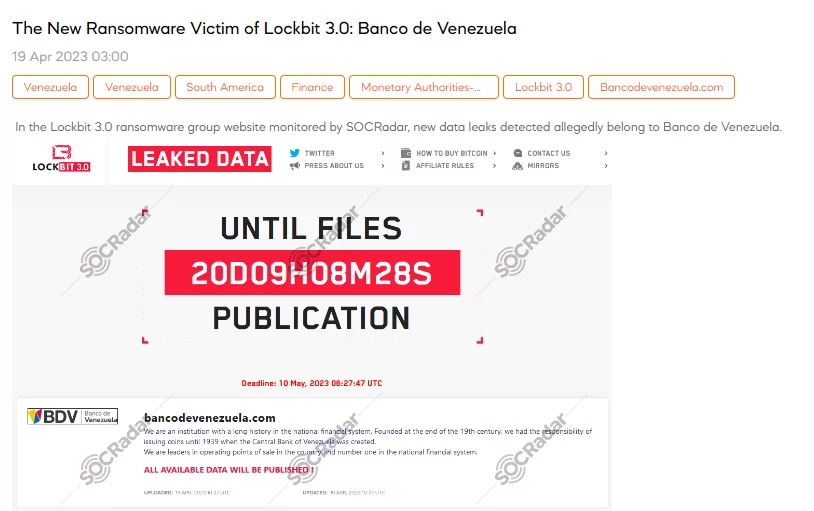
On April 19, SOCRadar detected a new ransomware announcement that the Banco de Venezuela had been attacked by the LockBit 3.0. The cybercrime organization shared nine images of some sensitive documents as examples of the data they seized.
Hacking Announcement is Detected for Gentex

A threat actor claimed on a Telegram channel that Gentex had experienced a data breach. According to the claims, the breach has resulted in the theft of approximately four terabytes of data, including sensitive information related to engineering, projects, manufacturing production, product marketing, quality management, management, and employees’ data.
Unauthorized Network Access Sale is Detected for a Turkish Education Institution
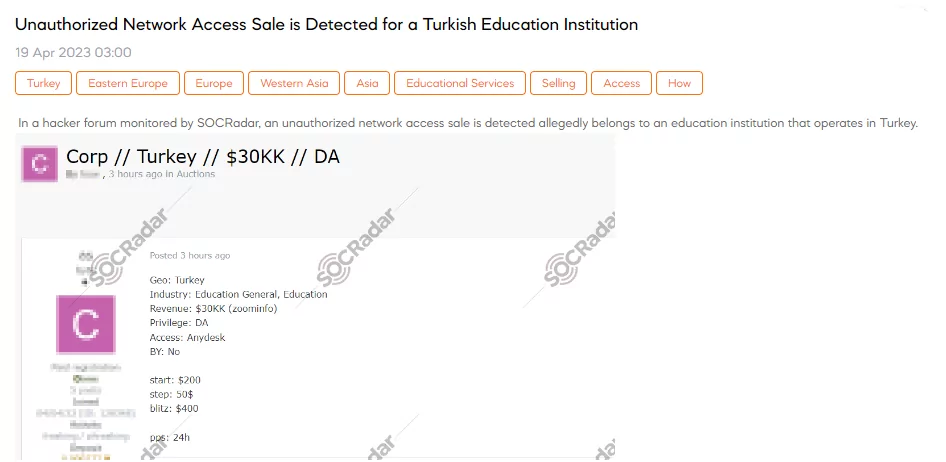
SOCRadar detected a sale offering unauthorized network access to a Turkish education institution. The sale includes access to the institution’s Domain Administrator (DA) privileges using the Anydesk software. The sale price starts at $200, with a step increase of $50 and a blitz option for $400.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.




































