
Telegram 2.0: A New Era of Privacy
On December 6, 2022, Telegram shared a new update blog on its blog page. In this blog post, specific topics attract attention, primarily based on privacy, and will attract cybercriminals. Telegram is known to be used more and more frequently by cyber criminals, and SOCRadar has covered this topic in its previous blog post published on March 24, 2022. This article will discuss Telegram and its new features coming with this update from a threat intelligence perspective.
About Telegram and Its Features
Telegram is a messaging app focusing more on security and privacy than other mainstream messaging apps. The users of this app can send photos, videos, and files of any type (documents, zip, mp3, mp4, etc.) Also, Telegram is a cloud-based messenger that allows transferring files of large size (up to 2 GB), unlike other messaging apps; for example, the maximum allowed size of a file to send in WhatsApp is only 100 MB.

Telegram offers an extra layer of privacy and security by providing the “Secret Chats” messaging option. This feature encrypts chats between the messaging users’ devices, making it impossible to forward written messages to other conversations. Also, users can delete any messages and files stored on both devices in the secret chat.
What Does Telegram Mean by “No-SIM Signup”?
Telegram requires verification from a phone number before it can be used. To ensure anonymity from this situation, Telegram allows users to get an anonymous number through its own platform, Fragment.
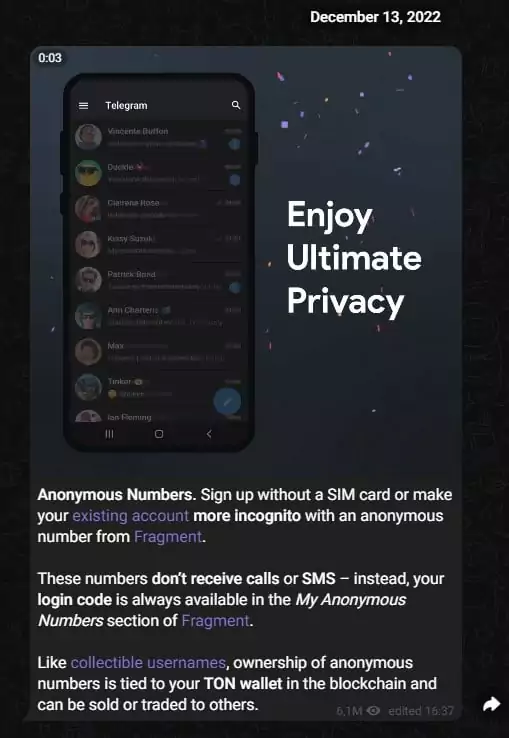
The Tonkeeper wallet can receive anonymous numbers through the Fragment platform using Telegram’s own cryptocurrency, The Open Network (TON). There are numbers with the +888 area code on the Fragment platform. While numbers with various patterns, such as 0000 0123, are bid at high values, such as 3,000 TON, buying relatively more randomly generated numbers at a current price of 40 TON is possible.
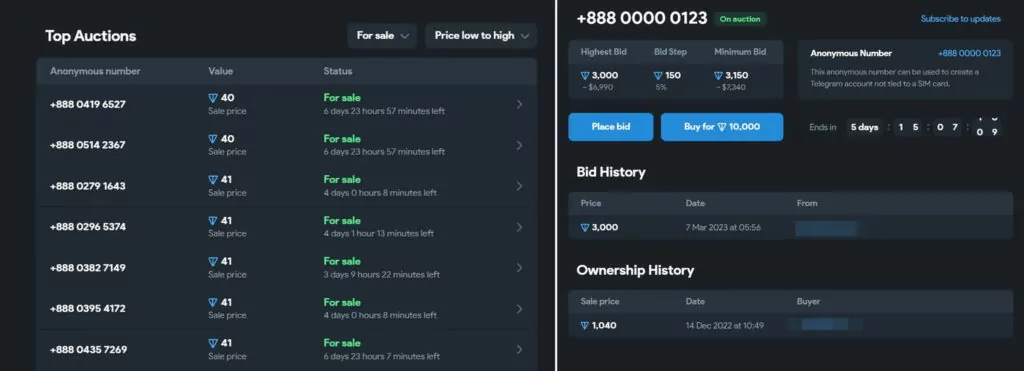
Apart from Anonymous numbers, Fragment also sells and auctions usernames, as seen below:
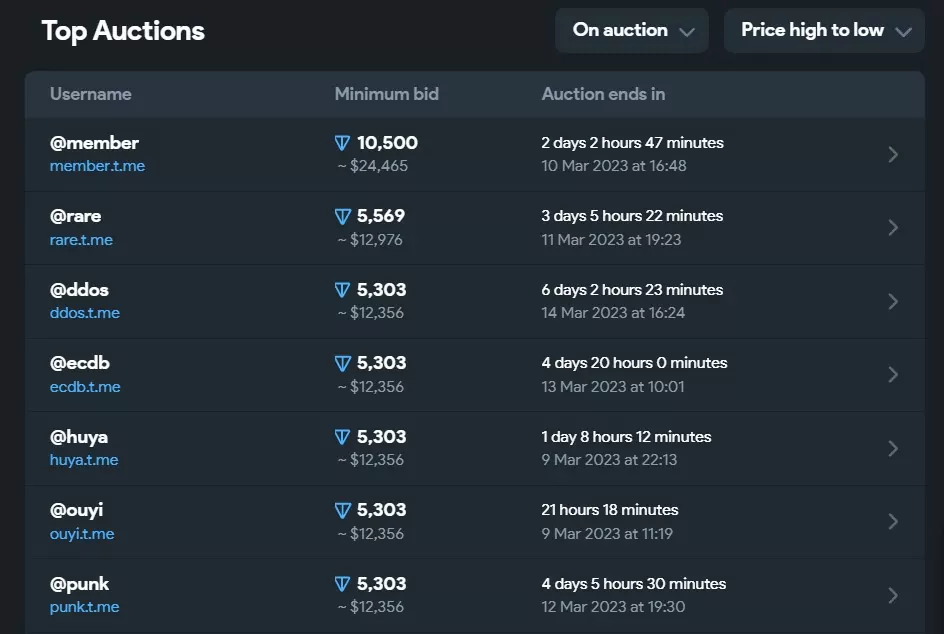
Telegram’s system does not allow users to manually create a 4-letter username, so it can be said that usernames with a length of 4-letter sold through Fragment are valuable because of this limitation.
What is Telegram “Auto-Delete All Chats” Feature?
In 2017 and 2019, Telegram added the ability to delete messages and then the ability to delete sent or received messages in both directions. In December 2022’s update blog post, a new feature was added where this ability could be performed in an automated way.
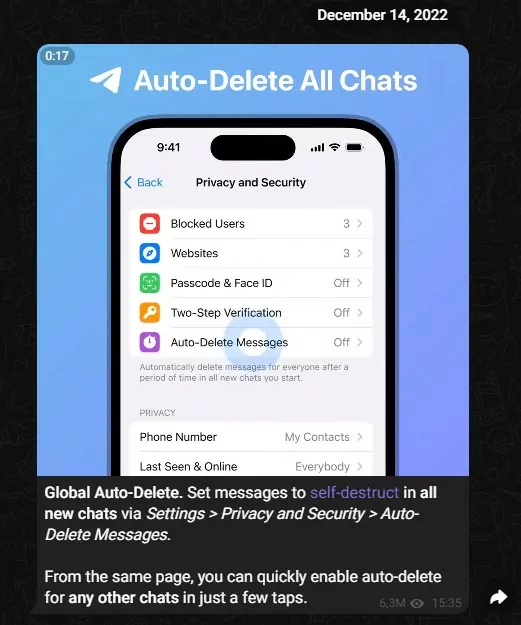
Using this new feature, a user can set a timer to automatically delete their own message, or a group administrator can set a timer to automatically delete any message in the group 24 hours or 7 days after it was posted. Telegram links this topic to Control Your Digital Footprint in its description.
Conclusion and Predictions
While Telegram’s launch of “Anonymous Numbers” and “Auto-Delete All Chats” features will be useful for users who care about their security and privacy, however, they can also be abused by cybercriminals in their malicious activities.
As a result of Telegram’s latest development, it can be predicted that the transition from dark web forums that can only be accessed through tools such as Tor Networks to Telegram will increase.
In addition, it can be predicted that the use of file-sharing platforms such as Mega will decrease due to this transition, and the effectiveness of cybercriminals will increase even more as they move more quickly.
Although security researchers monitor the communications of threat actor Telegram groups, the possibility that some cyber activities are carried out more secretly due to the auto-delete feature should also be considered. At this point, using a CTI solution capable of continuous monitoring in real-time will prevent possible information loss.
SOCRadar continuously monitors the dark web and social media (Twitter, Telegram, etc.) for the security of its customers. Organizations cannot allocate many resources to monitoring the dark web and social media. So, through SOCRadar’s alerting process, organizations can reinforce their security posture.




































