Cyber Threat Intelligence
Your Shield Against Cyber Adversaries is even stronger now!
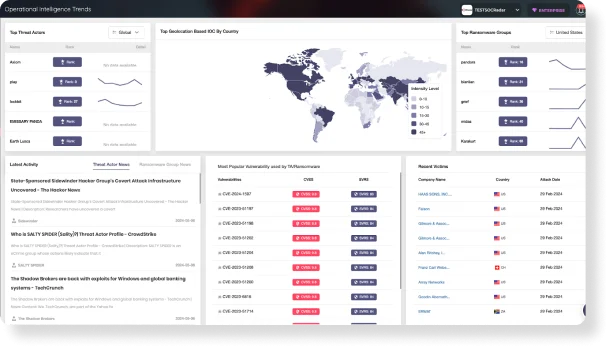
SOCRadar offers a horizon beyond traditional CTI products with its redesigned and enriched Cyber Threat Intelligence. Do not tire of juggling different aspects of threat intelligence. As one of the most robust data providers in the cyber security landscape, SOCRadar delivers actionable, contextual insights within five user-friendly modules based on core CTI principles.
Values of Cyber Threat Intelligence
Cyberattacks often start with planning in hidden corners of the web. Even tiny pieces of information can save your organization from a devastating cyberattack. SOCRadar acts as your eyes and ears, monitoring hacker forums, Telegram channels, instant messaging platforms, dark web markets, social media platforms, and many other communications tools on the dark/deep and surface web attackers use to organize an attack.
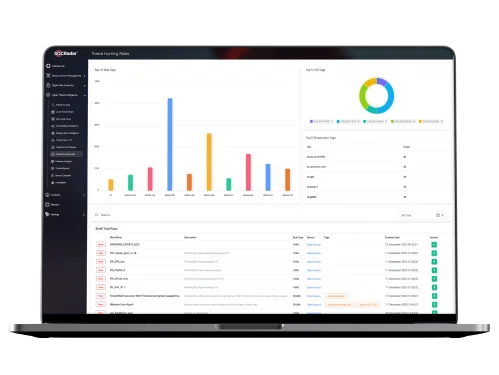
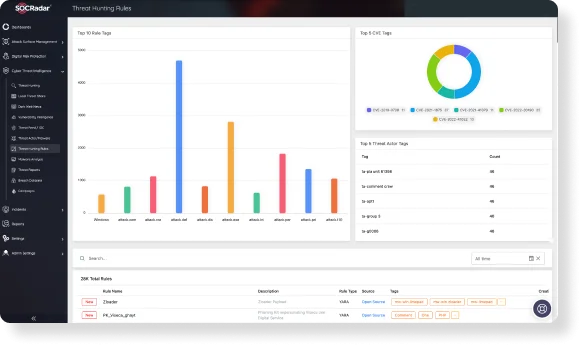
SOCRadar provides a procedure for searching for cyber threats that are hidden out lurking in the data and empowers you with an advanced threat-hunting approach.
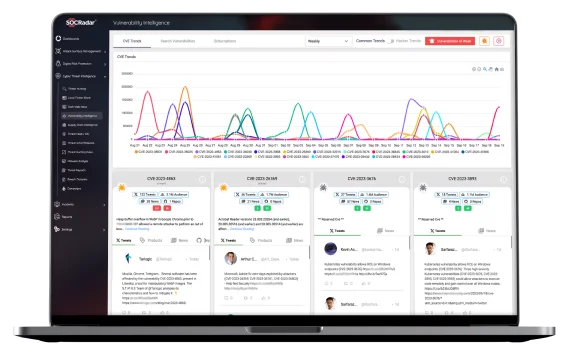
This is a contest against time! Research shows that threat actors scan for vulnerable endpoints within 15 minutes of a new CVE being publicly disclosed. Patching all the vulnerabilities discovered during scans is almost mission-impossible. Therefore, security analysts need prioritization.
“Which vulnerability is more critical for my organization?” is an essential question, and that is the exact point at which SOCRadar vulnerability intelligence comes into play. Assigning risk rankings to each vulnerability throughout the entire digital footprint of an organization, SOCRadar provides security experts with a comprehensive view of the organization’s real threats, not a bunch of irrelative CVE lists.
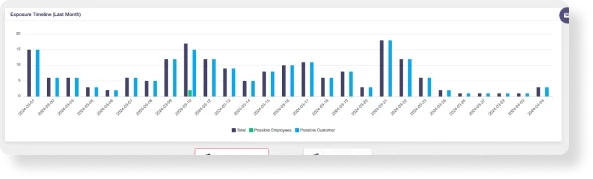
Modern cyberattacks frequently exploit stolen credentials.
We provide comprehensive insights into info-stealer incidents, real-world breach datasets, and previous breaches affecting domains similar to yours. Taking it a step further, SOCRadar empowers you with access information obtained from stealer logs.
Learn from past breaches, be aware of employee compromise access information, and proactively protect your business and data integrity.
What is the cyber attacker’s TTP?
What are the goals of the cyber attacker?
What mitigation strategies are provided for incoming attacks?
Modern cyberattacks are complex, but you can gain a decisive advantage with the right tools. With SOCRadar Cyber Threat Intelligence, equip yourself with the knowledge to proactively mitigate incoming attacks and implement robust detection and remediation strategies.
Empower your security team with the intelligence to guide the periodic security action plan – with SOCRadar’s advanced Cyber Threat Intelligence;
- Get real-time insights on potential attacks, including motivations, timing, and methods.
- Gain in-depth profiles of known threat actors and ransomware groups.
- Monitor dynamic changes and trends in the cyber threat landscape and adjust your security posture accordingly.
See Threats Before They Strike

Visibility Into Dark Web
Gain in-depth and actionable threat intelligence to profile current and future threats.

Accelerate Investigation
Get fast, relevant and accurate results from the darkest parts of the internet.

Respond Quicker
Combat and mitigate identified threats by understanding adversarial capabilities.

Shed Light On APT Actors
Get essential insights into the latest activities of state-sponsored APT groups.

API-Ready Feeds
Consuming threat intelligence feeds by leveraging millions of data points in the wild.

Trends Visualization
Access vulnerability trends as well as auto-aggregated, customizable news.
Free Threat
Intelligence for SOC
Analysts
Contextualized Threat Intelligence is a game changer.
- Monitor threat actors in an MITRE ATT&CK-compliant structure
- Benefit customized search engine in threat hunting
- Learn what hackers talk about your organization
Why do SOC Teams need Threat Intelligence?
Preemptive detection provides SOC teams a competitive advantage in their fight against cyber attackers.
With contextualized threat intelligence, SOC analysts have clear guidelines for effective threat hunting.


According to Gartner, “threat intelligence is evidence-based knowledge, including context, mechanism, indicators, implications, and actionable advice, about an existing or emerging menace or hazard to assets that can be used to inform decisions regarding the subject’s response to that menace or hazard”.
EC Council’s definition is very similar, “threat intelligence is the analysis of data using tools and techniques to generate meaningful information about existing or emerging threats targeting the organization that helps mitigate risks”.
Cyber threat intelligence aims to help institutions and organizations understand the risks of cyber attacks or cyber threats. These attacks can range from zero-day attacks, crypto viruses, APTs (Advanced Persistent Threats), botnets, or exploits. These threats are reported with the intelligence activities after being reviewed by CTI analysts to provide special protection methods to assist in an active defense in your organization.
The skilled, well-funded, well-organized, and highly-sophisticated cyber attackers use techniques that reveal security strategies to the technology alone. To develop a defense strategy against attackers, organizations need to know how hackers operate, how they function, and what techniques they use.
Cyber-threat intelligence allows companies to identify the dynamics and consequences of risks, improve security plans and structures, and reduce their attack potential to minimize damage and defend their network.
CTI can identify and analyze cyber threats against your business. Therefore, CTI can help you to:
- Focus on actionable alarms; the legacy threat intelligence solution provided only feeds and (Indicator of Compromise) IOCs, which were not actionable. But organizations started to need more and more of the latest intelligence about them. With real-time intelligence on threat actors, botnets, malware, and data from the dark web and the deep internet, organizations need to detect phishing domains targeting their customers.
- Collect, Verify, and Prioritize External Threats; CTI can deliver the hard work for your business with enriched intelligence that allows you to apply smarter defense and improvement processes.
- Detect Forgotten Assets and Monitor Attack Surface in Real-time; CTI can determine the blind spots by following the changing attack surface all the time.
- Prevent Data Loss; by using CTI, cyber threats can be detected, and security breaches can be prevented from disclosing confidential information.
Various threatening knowledge and theoretical approaches are useful at various businesses’ levels. The four categories of cyber threat intelligence have to do with different objectives:
- Strategic Cyber Threat Intelligence; It utilizes comprehensive pattern and emerging risk analysis to provide an outline of future cyber-attack implications.
- Operational Cyber Threat Intelligence; It is mainly used to make resource management decisions regarding actual and potential risks, historical resources, affiliations, and motives of threat actors.
- Tactical Cyber Threat Intelligence; Primarily, its main target is a technically trained audience and allows them to learn more specific details on threat actors’ tactics, techniques, and procedures (TTPs).
- Technical Cyber Threat Intelligence; It focuses on the technological details suggesting a cyber-security threat, such as phishing email lines or malicious URLs.
| Information | Intelligence |
| Unfiltered and raw data | Processed and sorted data |
| Not evaluated | Evaluated by Threat Intelligence Analysts |
| Too much-aggregated data | Only useful data |
| Not actionable | Actionable |
| Disconnected, incomplete, irrelevant | Connected, completed, and relevant |
Usually, cyber threat intelligence and cyber intelligence terms are used for the same meaning. But in theory, the two terms have different contexts.
CTI is the collection and revealing of threats that may harm business elements and security at any level to institutions and organizations. It is a type of intelligence that enables early measures to be taken by detecting the goals, methods, or types of attacks of the attackers as a result of analyzing the data collected and enriched from electronic media through a process.
CTI provides information on malicious actors, their tools, their infrastructure, and their methods for;
- Identifying types of attacks,
- Defining, guiding, and prioritizing operational requirements,
- Understanding threat actor capability, tactics, techniques, and procedures,
- Deploying detection systems,
- Developing defense strategies.
- Cyber intelligence (CI) translates the data obtained from the attackers’ networks into an operative report through “standard intelligence approaches.”
As can be understood from the definitions, while CTI focuses information on cyber threats, CI focuses on useful Intel from the Internet.