Recent Data Breaches: Capita, Toyota, and Discord
[Update] June 6, 2023: Capita was previously unable to confirm whether hackers had exfiltrated any data. Some USS (Universities Superannuation Scheme) members claimed that their data was affected following the breach. Added the subheadings: “USS Members Confirm Misuse of Their Data Following the Capita Data Breach” and “About Capita’s Exposed S3 Bucket.”
Data breaches have become increasingly common, with recent incidents impacting companies like Capita, Toyota and Discord, exposing the sensitive information of customers.
Such breaches can have severe financial and reputational consequences, making it essential for companies to prioritize cybersecurity measures to prevent and respond to these incidents. Meanwhile, individuals must remain vigilant and take precautions to protect themselves against potential harm resulting from data breaches.
Capita Cyberattack: Customers’ Data Potentially Stolen

In early April, a cyberattack hit UK outsourcing company Capita, which has since informed its customers that their data may have been stolen.
The attack mainly affected the company’s access to internal Microsoft Office 365 applications, causing some disruption to services provided to individual clients but not affecting the majority of client services.
The company initially reported that there was no evidence of customer, supplier, or colleague data being compromised, but on April 17, the Black Basta ransomware gang claimed to have stolen personal and financial data, including bank account details, physical addresses, and passport scans.
Capita now expects to incur costs of approximately £15m to £20m associated with the cyber incident, which potentially affected around 0.1% of its server estate. While the incident was interrupted by Capita, some data may have been exfiltrated, including customer, supplier, or colleague data.
The UK’s largest pension scheme, the Universities Superannuation Scheme (USS), was notified by Capita that their members’ data was taken by hackers who had access to servers containing personal information of around 470,000 active, deferred, and retired members.
The exposed information includes names, dates of birth, National Insurance numbers, and USS member numbers.
While Capita is unable to confirm whether the hackers definitively took this data, they advise that it is assumed to have been exfiltrated.
You can read the new update from the company here.
USS Members Confirm Misuse of Their Data Following the Capita Data Breach
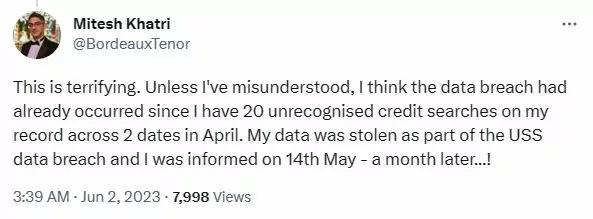
Some USS members claimed that their data was affected following the breach. In April and May, a member noticed suspicious credit card and bank account applications in their name; there are others who agree to have experienced a similar scenario.
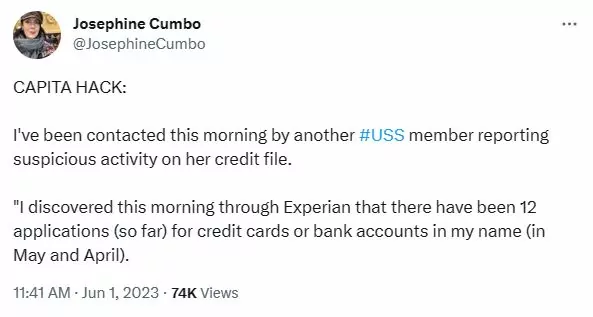
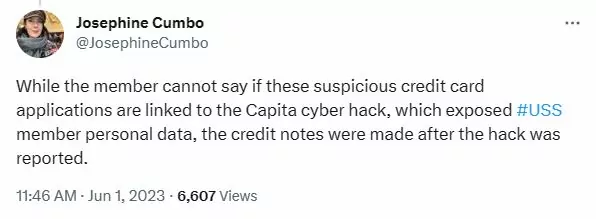
Another member reported seeing numerous credit searches on their record in April. The member also stated that they believe the data breach has already occurred due to the hack rather than Capita’s insecure S3 bucket incident.
About Capita’s Exposed S3 Bucket
On April 24, 2023, researcher Kevin Beaumont reported the exposed S3 bucket to Capita; the company then took the bucket offline. Capita informed in mid-May that the bucket did not contain any personal data. However, Adur Worthing Council later confirmed that the bucket contained personal data, as opposed to Capita’s statement.
The exposed S3 bucket is unrelated to the Black Basta hack, which caused the initial breach. Visit Kevin Beaumont’s Medium blog to learn more about the bucket’s exposure.
Toyota Discloses Data Breaches Impacting Over 2 Million Customers

Toyota Motor Corporation disclosed a security breach that exposed information of more than 2 million customers from November 6, 2013, to April 17, 2023. The breach was due to a database misconfiguration that allowed unauthorized access without authentication.
Customers who used T-Connect G-Link, G-Link Lite, or G-BOOK services were affected, and exposed data included vehicle identification numbers, chassis numbers, vehicle location information, and video footage taken from a camera installed on the car.
Toyota clarified that the exposed information cannot be used to identify the owners of the vehicles, and they have not found any abuse of the exposed data.
In addition, Toyota had previously warned customers in October 2022 that their personal information may have been exposed due to a mistakenly published source code on GitHub that contained an access key to customer data.
Discord Data Breach: Third-Party Account Compromised

Discord, the popular social platform for VoIP and instant messaging, has disclosed a data breach resulting from a compromise of a third-party customer service agent’s account. The incident led to unauthorized access to the support ticket queue, which contained user email addresses, messages, and related attachments exchanged with Discord support.
Discord immediately deactivated the compromised account and analyzed the affected machine for malware. The company has also improved its cybersecurity measures in partnership with its customer service partner to prevent future incidents.
Discord has announced that it is notifying impacted users and recommends they remain vigilant for suspicious messages or activity, such as fraud or phishing attempts.
Protecting Your Company’s Data with SOCRadar
SOCRadar has the ability to recognize any stolen login information that pertains to your company’s domains and inform your security team.
It can also detect any leaks of accounts and data, monitor multiple underground markets on the dark web for authentic login details, and discover privileged accounts and high-profile individuals for prompt investigation and response.
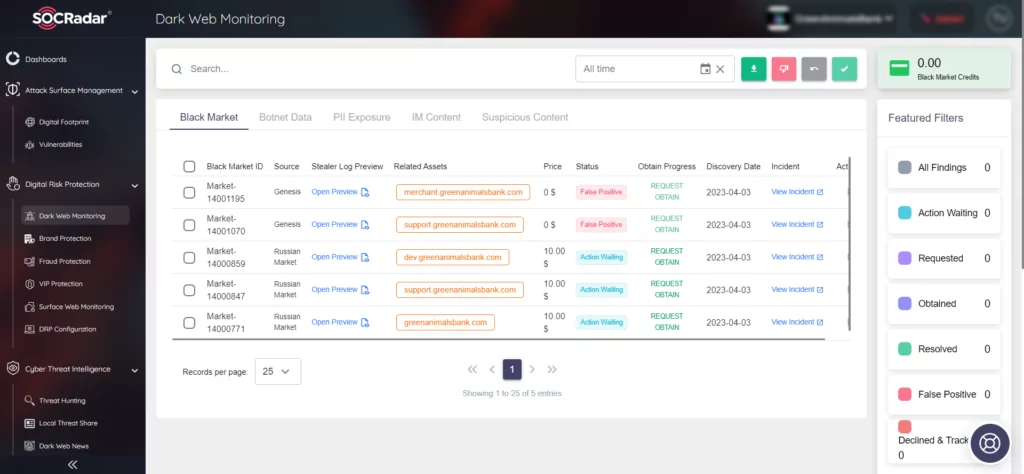
Additionally, SOCRadar can help protect your employees’ personally identifiable information (PII) from any unauthorized access by hackers to sensitive or confidential data.
Also, you can use our free AccountBreach Labs to check if your information has been exposed on the internet.