
The Week in Dark Web – 28 March 2022 – Access Sales and Data Leaks
Powered by DarkMirror™
This week’s edition covers the latest dark web news from the past week. Again, rise of ransomware attacks, some database thefts, and stealing customer data, that took their place on the headlines this week. Click here to read the last weeks post.
Find out if your data has been exposed on the deep web.
Cuba Ransomware Group Leaked The Data of Metalcraft of Halton Hills
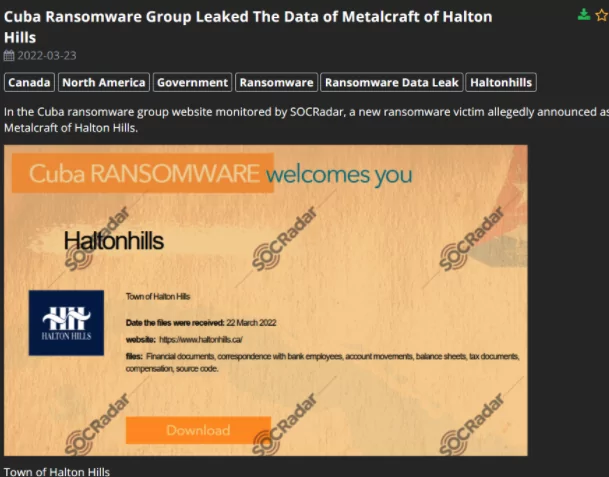
On March 22, a huge database of a town website was published on the dark web. The victim organization is based on the town they represent that originated in Canada. This leakage allegedly includes financial documents, correspondence with bank employees, account movements, balance sheets, tax documents, compensation and source code. The ransomware underlying that cyber attack is known as Cuba ransomware group, which is also in charge of various critical cyber attacks of decent companies and services, within the last year. This huge leakage of critical information of employees as well as financial records of the town administration, could result in more danger than it seems, as SOCRadar analysts state. That is, the ransomware group might use this leakage to access data of other services as well, or could use the leakage for their own profit.
Login Informations of Software AG are on Sale
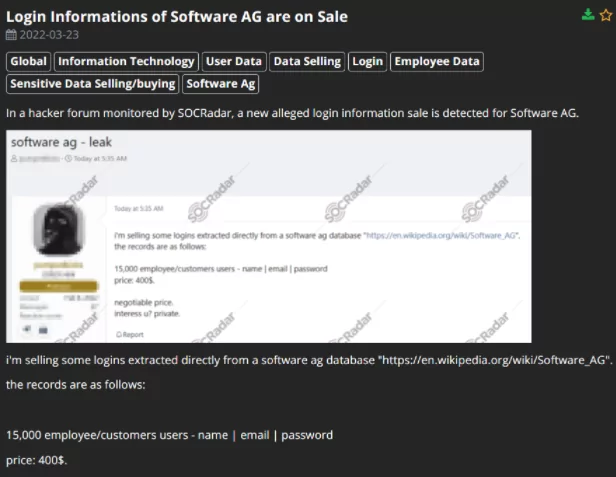
On March 23, the database covering 15.000 employees and customers’ login information was put on sale on the hacker forum monitored by SOCRadar. This leakage allegedly includes employees/customers’ names, usernames, emails, and even their passwords. This alleged login detail puts on sale for 400 dollars. The vendor claims that all login information that he had was obtained from a software ag database. SOCRadar analysts state that if the specialists do not pay attention to the leakage, the ransomware group could also reach the data on other platforms on the internet.
New JPG Silent Arbitrary Code Execution Builder is on Sale
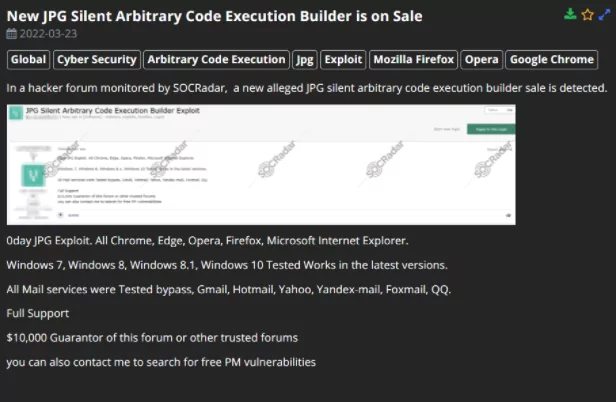
On March 23, a vulnerability threat known as JPG Silent Arbitrary Code Execution Builder was put up for sale in a hacker forum on the dark web. It is stated in the forum that all the well-known internet explorers and mail services in various operating systems were tested and the arbitrary code execution builder works. Arbitrary code execution (ACE) is an attacker’s capability to execute any code or commands of the attacker’s choice on a target computer or system without the victim’s knowledge. Therefore, this sale of specifically organized and produced ACE builders could lead to a dangerous situation for commonly used internet explorers and mail services.
Unauthorized RDWeb Access Sale is Detected for a Hungary Bank
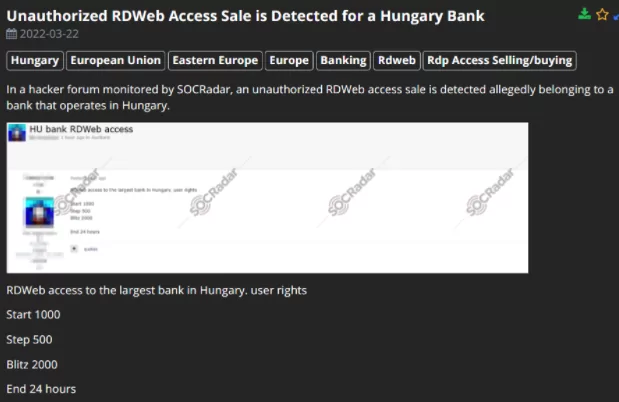
On March 22, a vast database of RD Web access (Remote Desktop Web Access) of a bank was put up for auction on the dark web. The vendor claims that this RD Web access belongs to the biggest bank in Hungary, and this vast database is on auction starting at 1,000 dollars. Remote Desktop Web Access (RD Web Access) is a technology that supplies remote access to applications operating on a Terminal Server without any VPN connection. Therefore, if nobody attends to solve this leakage, this could result in more damage than expected.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, it is simply not feasible to monitor all sources which can be time-consuming as well as challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by targeted country or industry.



































