
The Week in Dark Web – February 13, 2023 – Ransomware and Data Leaks
Powered by DarkMirror™
LockBit and Play ransomware groups continue their attacks in hacking spree mode. The attack that victimized the UK’s leading postal service, Royal Mail, became the hottest cyber incident of the past week.
A10 Networks was also in the headlines last week with an alarming data breach.
Here are other notable news from the dark web.
Find out if your data has been exposed.
The New Ransomware Victim of LockBit 3.0: Royal Mail Group
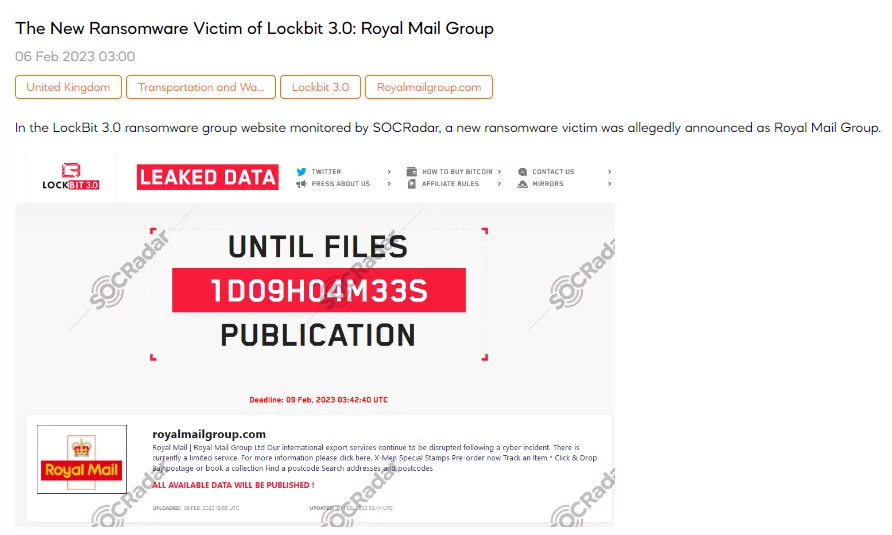
On February 6, a SOCRadar dark web researcher found a post that the LockBit ransomware group claimed responsibility for the cyberattack on Royal Mail, the UK’s leading mail delivery service. In the case of non-payment of the ransom, LockBit says that the data allegedly belonging to the Royal Mail Group will be leaked on February 9.
New Victim of Play Ransomware: A10 Networks
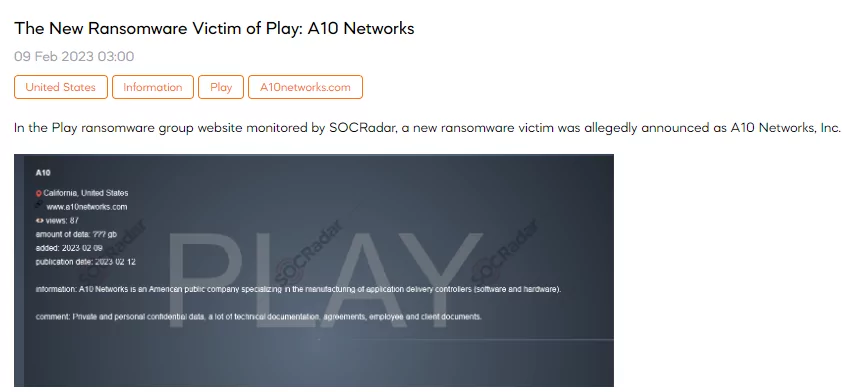
SOCRadar found a new post about A10 Network on the website belonging to the Play Ransomware group. A10 Networks is an American public company specializing in manufacturing application delivery controllers (software and hardware). Play Ransomware group claims to contain sensitive private and personal data, agreements, technical documents, and employee and customer documents.
Play ransomware has previously attacked many companies, including Texas-based cloud computing provider Rackspace.
Credit Cards Belonging to the United States are on Sale
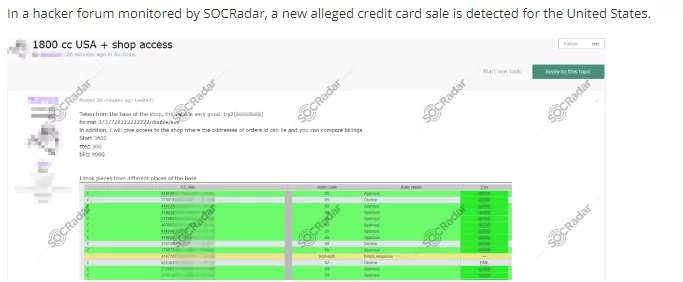
SOCRadar detected a post selling credit card credentials of US citizens. The threat actor claimed to have obtained the cards, which it said were of good validity, from a shopping store and also said it would give access to the shopping store to compare the data.
Database of Deutsche Bahn is on Sale
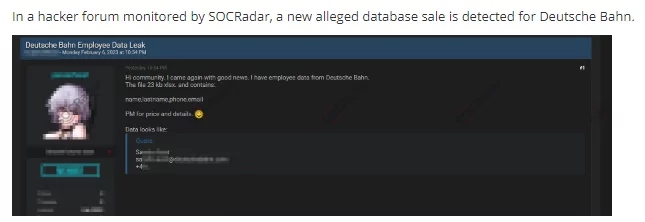
On February 6, a SOCRadar dark web researcher detected a post selling a Deutsche Bahn database. Deutsche Bahn is the national railway company of Germany. The database contains the name, last name, phone and email of the Deutsche Bahn employees. The information’s price is unknown; the threat actor directs people to DM.
Database of LinkedIn is on Sale
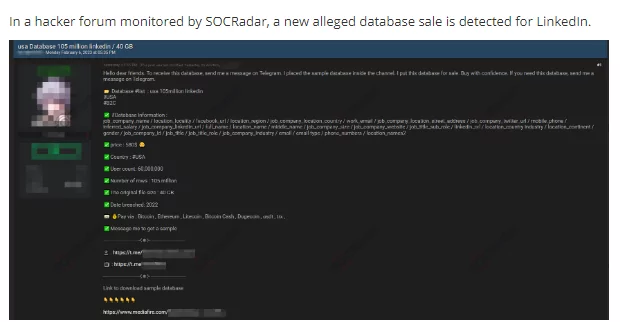
On February 6, SOCRadar detected a post selling the LinkedIn database. The threat actor claims that 40GB of data belongs to 60 million users. The price for the database is $580; the threat actor directs people to Telegram.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.




































