
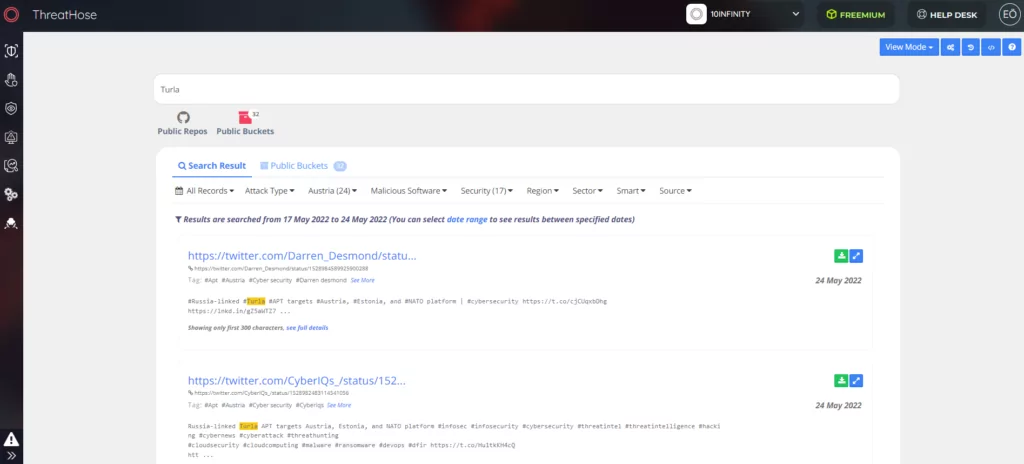
Turla Reconnaissance Campaign Targets Eastern Europe
The reconnaissance and espionage campaign of the Russia-linked Turla hacker group against the Austrian Economic Chamber, Baltic Defense College, and NATO’s Joint Advanced Distributed Learning (JDAL) platform has emerged. Experts think that the recent economic sanctions against Russia and the NATO membership agendas of Sweden and Finland may be the motivation behind the campaign.
War Became an Attraction for Threat Actors
In the last few months, there has been a noticeable increase in the activities of hacker groups originating from Russia and Belarus in Eastern Europe. One of them, the cyber espionage group Turla, which is generally known for its attacks on the foreign ministries and defense institutions of the states, continues a phishing campaign with two domains. According to Google Threat Analysis Group research, threat actors APT 28 (Fancy Bear), Turla, COLDRIVER, and Ghostwriter are running active phishing campaigns using similar techniques.
Turla Starts With a Phishing Attempt
According to the blog published by Sekoia, the typosquatting domains used in the attack “War Bulletin 19.00 CET 27.04.docx” redirect to a Word document. Inside this file is an embedded PNG file named “logo.png.” According to researchers from Sekoia, this file is for reconnaissance purposes. Through this file, Turla can gain access to the IP address that it can use in future attacks.
PNG file can be detected with the following YARA rule:
rule apt_TURLA_ExternalPNGDocument_strings {
meta:
id=”51413d41-d0f4-4e1a-9f12-322921e48977″
version = “1.0”
intrusion_set = “TURLA”
description = “Detects external logo embedded in DOCX documents”
source = “SEKOIA”
creation_date = “2022-05-05”
modification_date = “2022-05-05”
classification = “TLP:GREEN”
strings:
$s1 = “/relationships/image”
$s2 = /[0-9]{3,10}/logo.png/
$s3 = “TargetMode=”External”/><"
condition:
$s1 in (filesize-400..filesize) and
$s2 in (filesize-400..filesize) and
$s3 in (filesize-400..filesize)
}
Findings of SOCRadar Analysts
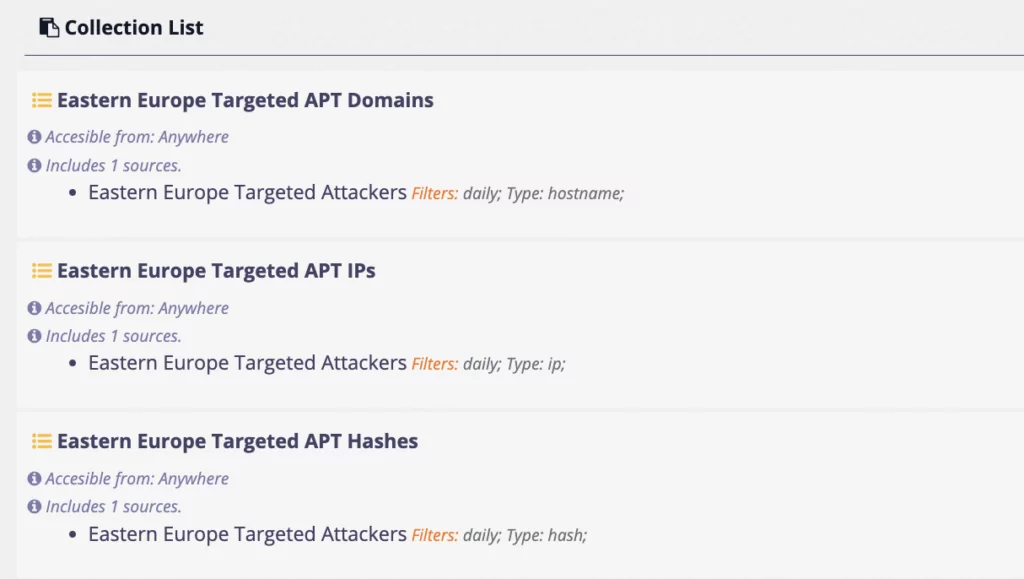
IOCs related to Turla and Lately Active Threat Actors in Eastern Europe
Hash:
f6e755e2af0231a614975d64ea3c8116
f223e046dd4e3f98bfeb1263a78ff080
694fb9d8ffeddf9988e6ae8946a50ee195ebb3021b0d0b0370f5246a497c4353
710faabf217a5cd3431670558603a45edb1e01970f2a8710514c2cc3dd8c2424
39d242660c6d5dbe97d5725bbfed0f583344d18840ccd902fffdd71af12e20ec
0bcc92ee840f4fb2d15092b4e25f902e24828955b9ed170e642504f10388a4dc
0f1d80eab41d3fe73f79627ced907b4f
165be7620b78fe37cf25c797ee5b49e7
22a8b4a7c7a467ea7fcf0a3930c99ecb482095093839683b400f58e2cdda176f
27e7d2054a68510c974add24f33c1c7ef06ef68028cca021cd6b5e67363e2bea
34a6c9a80f781973ecec2c13984018102bc28af82691b484cbe2ee89c6dfc7e2
38abeb8a68e9207da3e6ead88a9682ec
454e6c3d8c1c982cd301b4dd82ec3431935c28adea78ed8160d731ab0bed6cb7
487e88b358e714b8259bac79eac2629321e46b35b32d643cb785e670f0b3b94a
48afbdc27f3ff243ac2689e2ebd9f33c
Domains:
wkoinfo.webredirect[.]org
jadlactnato.webredirect[.]org
baltdefcol.webredirect[.]org
wkoinfo.webredirect[.]org
cache-dns[.]com
docs-shared[.]com
documents-forwarding[.]com
documents-preview[.]com
protection-link[.]online
webresources[.]live
noreply.accountsverify[.]top
microsoftonline.email-verify[.]top
lt-microsoftgroup.serure-email[.]online
facebook.com-validation[.]top
lt-meta.com-verification[.]top
lt-facebook.com-verification[.]top
secure@facebookgroup[.]lt
IPs:
45.153.241[.]162
79.110.52[.]218
149.154.157[.]11
Documents:
23.03.2022 : Neue USA Exportkontrollen und Sanktionen: Fokus Russland – Was müssen österreichische Unternehmen jetzt beachten? – WKO.at
IOCs related to Turla:
Infrastructure
45.153.241[.]162
79.110.52[.]218
149.154.157[.]11
baltdefcol.webredirect[.]org
wkoinfo.webredirect[.]org
jadlactnato.webredirect[.]org
Document hashes
f6e755e2af0231a614975d64ea3c8116
f223e046dd4e3f98bfeb1263a78ff080
About Turla
Turla is believed to be administered by the Federal Security Service of the Russian Federation (FSB). Also known as Uroburos, Venomous Bear, or Snake, the group has been active for over 25 years. The group, which became famous for the “Moonlight Maze” attack, in which they accessed the sensitive data of the US Department of Defense, has been silent for a while. The last time they came up with a breach against some European government organizations was in 2020.
Use SOCRadar® FOR FREE 1 YEAR
With SOCRadar® Free Edition, you’ll be able to:
- Prevent Ransomware attacks with Free External Attack Surface Management
- Get Instant alerts for fraudulent domains against phishing and BEC attacks
- Monitor Deep Web and Dark Net for threat trends
- Get vulnerability intelligence when a critical zero-day is disclosed
- Get IOC search & APT tracking & threat hunting in one place
- Get notified with data breach detection
Free for 12 months for one corporate domain and 100 auto-discovered digital assets.
Get Free Access.




































