Dark Web Profile: USDoD
[Update] October 17, 2024: See the subheading: “Brazilian Arrest Tied to USDoD”
[Update] August 26, 2024: See the subheading: “Is USDoD’s Identity Revealed?”
[Update] April 22, 2024: See the subheading: “Update on USDoD’s Activities: Departure from Public Breaches”[Update]
[Update] November 7, 2023: See the subheading: “UsDoD Continues Ambitious Claims; Now Its LinkedIn’s Turn.”
Emerging from the shadows of the cyber realm, “USDoD” first caught attention by exposing the data of 80,000 InfraGard members, revealing significant security lapses within the organization. This audacious act, coupled with a subsequent leak involving 3,200 Airbus vendors, has solidified his reputation in the cybersecurity world. Behind the pseudonym is a man in his mid-30s with roots in South America. Influenced by many, USDoD has been an eyecatcher for some time in the digital landscape.
Early Activities and Background of USDoD
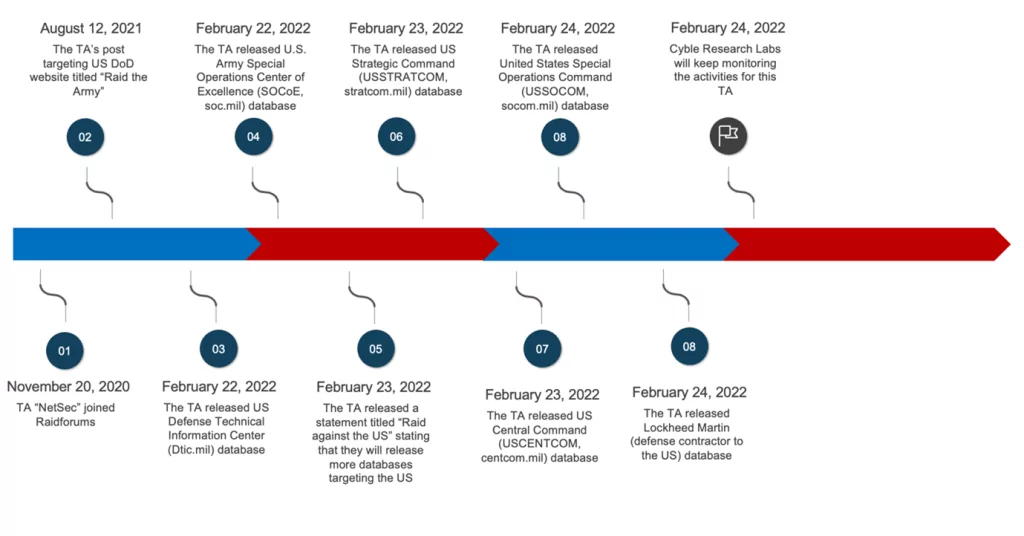
Previously known as “NetSec” on RaidForums, USDoD gained notoriety with his “#RaidAgainstTheUS campaign,” targeting the U.S. Army and defense contractors. In February 2022, a report highlighted his breaches of multiple U.S. defense databases, painting him as a pro-Russian threat actor. However, USDoD refutes this label, clarifying that his collaborations with Russians were based on personal or business connections, not political motivations. One such collaboration involved an AI project named “Tulip,” aimed at collecting military data.
His transition to the “USDoD” moniker occurred on Breached.vc in December 2022, where he posted data from InfraGard, a partnership between the FBI and private sector firms. Using social engineering, he impersonated a CEO and successfully gained membership, exposing a significant security lapse within InfraGard.
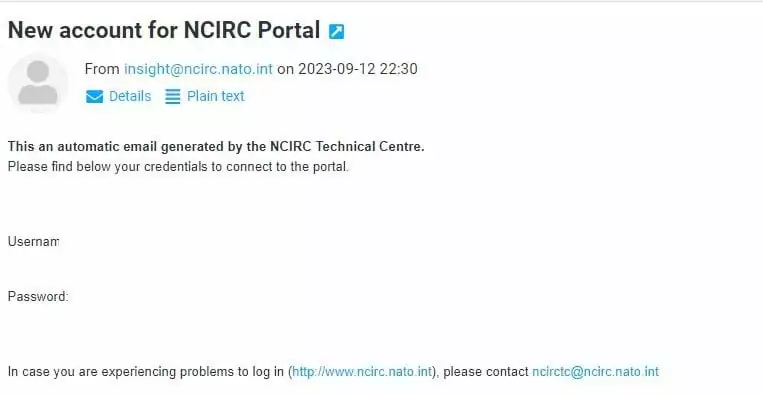
USDoD’s hacking approach heavily relies on social engineering, particularly impersonation. This technique has granted him access to high-profile entities, including NATO Cyber Center Defense and CEPOL. Despite targeting such entities, he remains confident, claiming to have protection in Spain from influential figures. His motivations intertwine personal vendettas with a love for challenging cyber exploits, revealing a multifaceted character behind the hacker alias.
Current Activities and Future of USDoD
Return to BreachForums and Airbus Breach
USDoD marked his return on BreachForums with a significant leak: data from 3,200 Airbus vendors. He accessed Airbus using an employee’s credentials from a Turkish airline, which he found in infostealer logs. His post also contained a warning for Lockheed Martin and Raytheon, though he later revealed this was a diversion while targeting other entities like Deloitte, NATO, and CEPOL.
Metropolitan Club of the City of Washington Database Breach
Most recently, USDoD has announced a security breach, revealing the database of the Metropolitan Club of the City of Washington. The incident stands apart from an earlier breach linked to the same threat actor and the “Ransomed.vc” ransomware group. He asserts that by obtaining Personal Identifiable Information (PII) about the General Manager, he was able to crack the login details for the organization’s admin panel.
Misunderstandings and Clarifications
Brian Krebs’ report on the Airbus leak, which tied the data release to the 9/11 anniversary, deeply upset USDoD. He clarified that the timing was unintentional and expressed his frustration with Krebs’ insinuations. USDoD emphasized that his actions were neither politically motivated nor terrorist-driven by saying, “I won’t attack Russia, China, South and North Korea, Israel, and Iran. The rest, I don’t care”.
UsDoD Continues Ambitious Claims; Now Its LinkedIn’s Turn
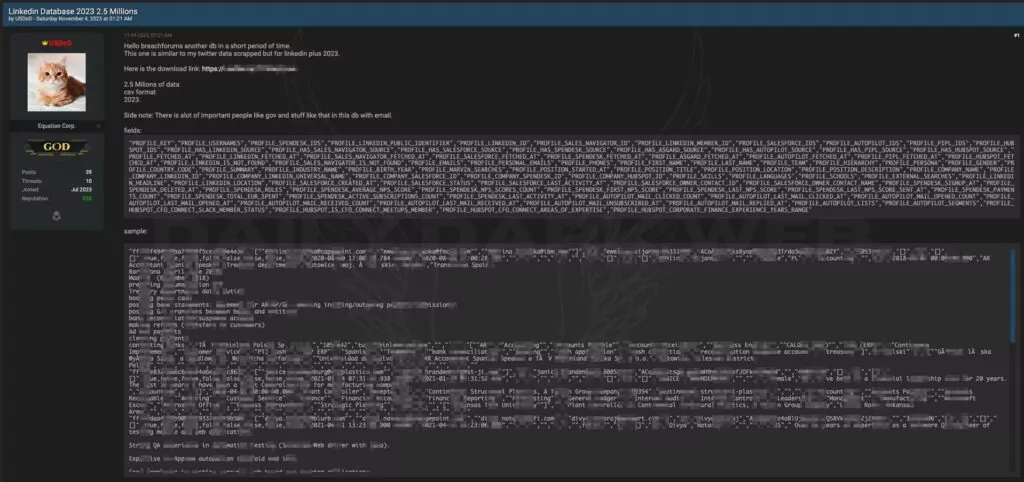
UsDoD, which managed to make a significant impact on its own, continues its operations. He claims to have released 2.5 million records, alleging a breach of the LinkedIn Database.
“haveibeenpwned” founder Troy Hunt made the following comment in his Twitter account, regarding this incident: “Interesting data. Allegedly 2.5M, but almost 6M unique addresses. One fellow Aussie has 5 addresses across telco, bank, publisher, and 2 e-comm sites. Their LinkedIn reflects this, so this data could tie together identities.”
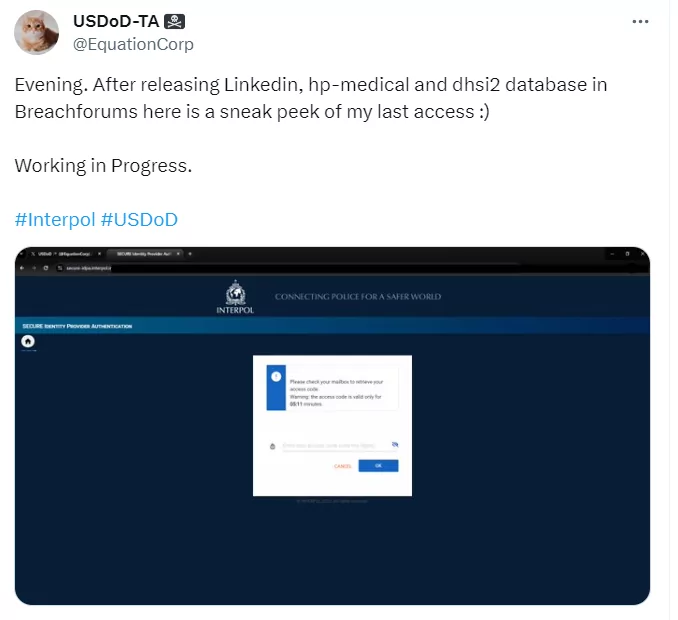
According to UsDoD’s statement, the actor shared alleged data breaches of the hp-medical and dhsi2 on “breachforums” recently, also shared a screenshot in his Twitter account from the Interpol website’s interface, labeling it as a preview of his upcoming operation.
**USDoD has expanded the amount of data leaked from LinkedIn. According to his claims, this new dataset comprises 35 million entries and expands to 12 gigabytes when uncompressed. Troy Hunt has shared that the additional collection of scraped and compiled data linked to LinkedIn has now been incorporated into Have I Been Pwned . This inclusion has introduced an extra 14 million unique e-mail addresses, increasing the total scope of the security breach to nearly 20 million records. It’s worth noting that 13% of these e-mail addresses were already present in Have I Been Pwned.
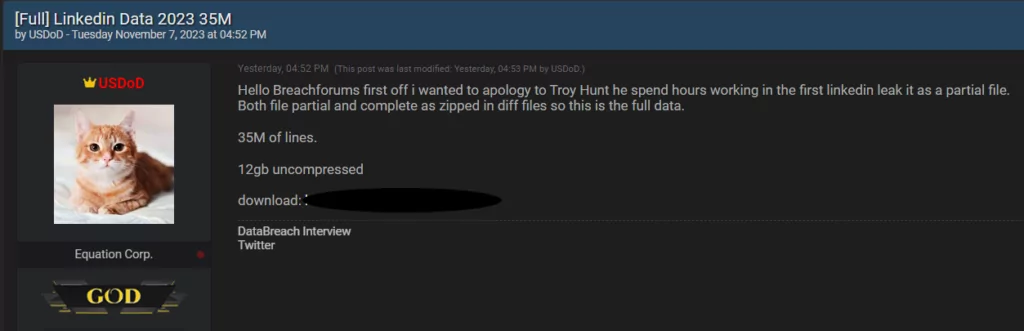
Furthermore, Troy Hunt published a blog post about the dataset. He stated that the dataset is a blend of data extracted from publicly available LinkedIn profiles, fictitious e-mail addresses, and, to a limited extent, information from other sources listed in the column headings. However, it’s important to note that the individuals are real, the companies are legitimate, the domains are authentic, and, in many instances, the e-mail addresses themselves are valid.
Real Targets and Motivations
Despite the public threats against Raytheon and Lockheed, USDoD’s real interests lay elsewhere. He targeted and accessed entities like CEPOL and NATO, aiming to understand their security and training methods. His ultimate goal? Full control and influence. He plans to establish a private company to sell military intelligence on the dark web, with Constellis being his first target.

USDoD’s Future Endeavors and BreachForums
USDoD’s vision extends beyond hacking. He aims to revitalize BreachForums, lamenting the lack of engagement from its current owner, ShinyHunters. He believes active participation from influential members can restore the forum’s former glory.
USDoD’s activities and plans are multifaceted; as he ventures into selling military intelligence and continues to challenge high-profile targets, defense entities should remain vigilant.
Update on USDoD’s Activities: Departure from Public Breaches
USDoD, known for his audacious breaches and public releases, has announced his departure from the threat landscape. In a post on a hacker forum, he bid farewell to the community and federal agencies, expressing his decision to step into the shadows and prioritize his personal life.
In his final act, USDoD shared a significant breach involving Bureau van Dijk Database 2024 and US Consumer Database, totaling millions of data entries. This farewell post marks the end of his public hacking endeavors.
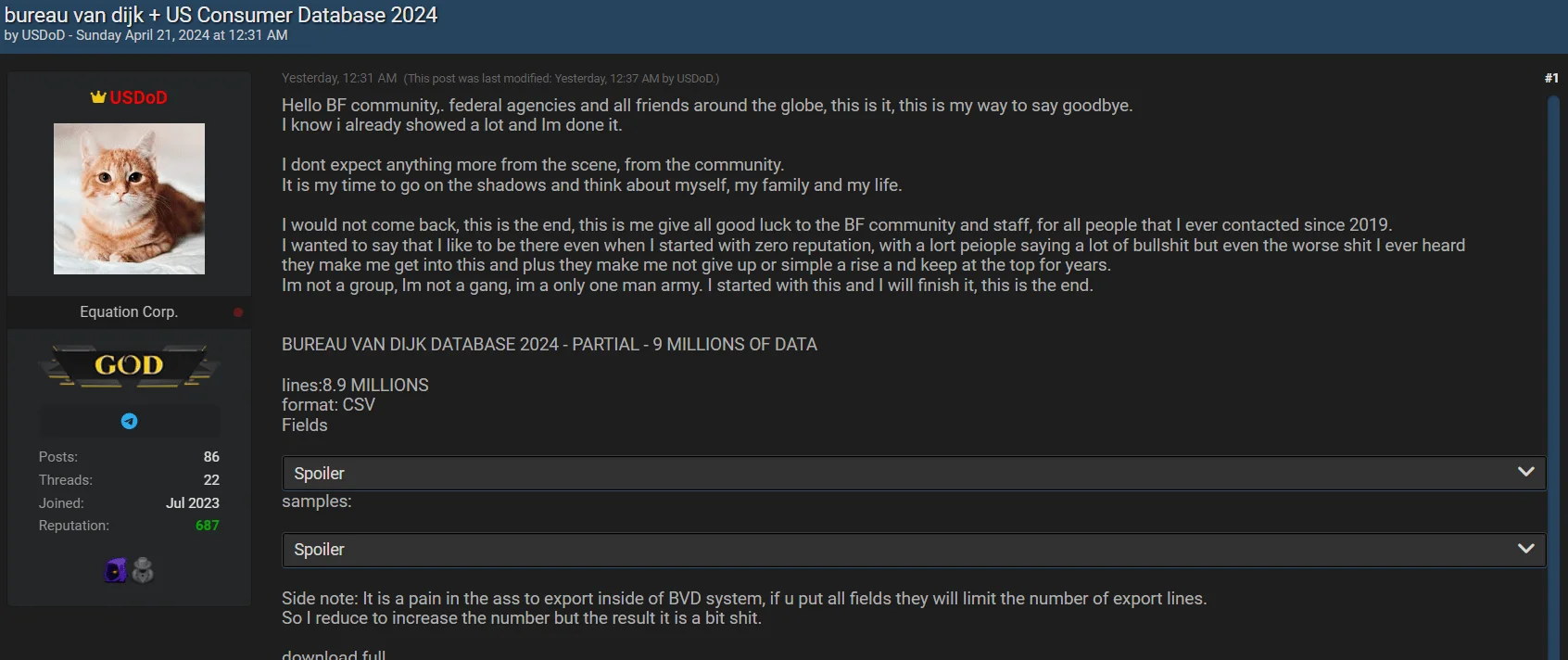
USDoD’s latest post in BreachForums
Here is the message from USDoD on the hacker forum:
“Hello BF community, federal agencies, and all friends around the globe, this is it, this is my way to say goodbye. I know I already showed a lot, and I’m done with it.
I don’t expect anything more from the scene, from the community. It is my time to go into the shadows and think about myself, my family, and my life.
I would not come back; this is the end. This is me giving all good luck to the BF community and staff, for all the people that I ever contacted since 2019. I wanted to say that I liked being there, even when I started with zero reputation, with a lot of people saying a lot of bullshit. But even the worst shit I ever heard, they made me get into this, and they made me not give up or simply rise and keep at the top for years.
I’m not a group, I’m not a gang, I’m an only one-man army. I started with this, and I will finish it. This is the end.”
In his farewell post, USDoD shared the following alleged breaches:
- Bureau van Dijk Database 2024: Partial data with 9 million entries
- US Consumer Database: 2.8 million entries
Therefore, these breaches mark his final act in the public hacking sphere, as he transitions away from dealing with public breaches.
USDoD’s departure from the scene could signify the end of an era in the cyber threat landscape. While his actions have garnered attention and concern, his decision to step back underscores the evolving nature of cybersecurity and the impact of individual actors in the digital realm.
In a recent interview, he didn’t indicate any intention to halt operations, asserting his ongoing commitment. However, he clarified that this isn’t exactly a retreat but rather a shift to independent work. It could be alleged that personal ambitions and a desire for reduced scrutiny from security forces may also drive this decision.
Conclusion
The enigmatic figure of “USDoD” stands as a testament to the evolving landscape of cybersecurity. From his audacious breaches to his intricate web of motivations, he represents the new age of hackers who blend personal vendettas, business ambitions, and sheer love for the challenge. His journey, from exposing significant security lapses in reputed organizations to announcing ambitious future plans, underscores the need for heightened vigilance in the digital realm. As the lines between personal, political, and professional motivations blur, entities worldwide must recognize and prepare for the multifaceted threats posed by individuals like USDoD. In a world where information is power, understanding the motivations and methods of those who seek to control it is paramount.
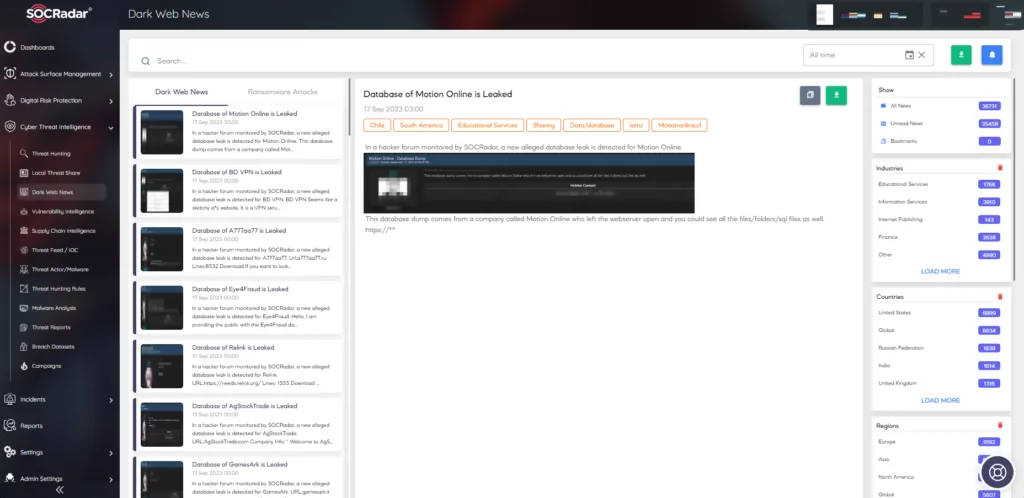
In today’s digital age, the dark web has become a hotbed for illicit activities, including the trade of stolen data and the planning of cyberattacks. SOCRadar’s dark web monitoring offers a solution to this growing threat. By continuously scanning the shadowy corners of the dark web, SOCRadar provides timely alerts to businesses and individuals when significant players make a move or when their sensitive information appears in these hidden realms. This system allows for swift action, minimizing potential damage and ensuring that stakeholders remain one step ahead of cyber adversaries.
Is USDoD’s Identity Revealed?
In a surprising twist, the hacker known as USDoD, linked to major data breaches, has revealed his identity. USDoD, also called EquationCorp, is actually Luan G., a 33-year-old from Minas Gerais, Brazil. This comes after his involvement in significant hacks, including leaking 3.2 billion Social Security Numbers from National Public Data and breaching the FBI’s InfraGard platform, exposing 87,000 members’ details.
Luan G. confessed after reportedly being doxed by CrowdStrike, a cybersecurity firm he previously targeted. However, Luan claims that other cybersecurity groups, like intel421 Plus, had already identified him before the InfraGard hack. In a statement to Hackread.com, Luan expressed his wish to leave cybercrime behind and contribute positively to Brazil, acknowledging that it’s time to take responsibility for his actions.
Revealing USDoD’s identity as a Brazilian citizen has legal consequences. While the extradition treaty between Brazil and the U.S. could allow Luan to face charges in the U.S., Brazil’s policy of not extraditing its citizens might prevent this. Even if not extradited, Luan could still face charges in Brazil. His desire to reform may influence a more lenient legal approach focused on rehabilitation.
Brazilian Arrest Tied to USDoD
In a significant breakthrough, Brazilian authorities arrested a 33-year-old male in “Operation Data Breach,” believed to be the infamous USDoD (aka EquationCorp), responsible for multiple large-scale cyberattacks. Although the press release didn’t explicitly name USDoD, the arrested individual boasted about compromising Infragard, a breach previously claimed by USDoD.
USDoD has been linked to major cyber incidents, including the National Public Data breach, which exposed the personal data of millions of Americans. His involvement had been referenced in U.S. court documents since 2022, notably in connection with the arrest of notorious hacker Pompompurin.