
VMware Fixes the Critical Vulnerability Affecting Some Products
Virtualization solutions continue to be one of the primary targets of cyber threats as they are widely used in companies.
US-based virtualization firm VMware has fixed a critical vulnerability in some of its products. In the update shared from the company, vulnerabilities that allow cyber threats to take over affected systems have been fixed.
How Does the Vulnerability Affect?
The “Heap Overflow” vulnerability, coded CVE-2021-22045 and given a “criticality level of 7.7”, allows threat actors to execute arbitrary code on the system if exploited.
In the advisory note shared by the company, it was stated that attackers with access to the CD-ROM-enabled virtual machine could exploit the vulnerability and execute code with hypervisor authority.
Which Products Does the Vulnerability Affect?
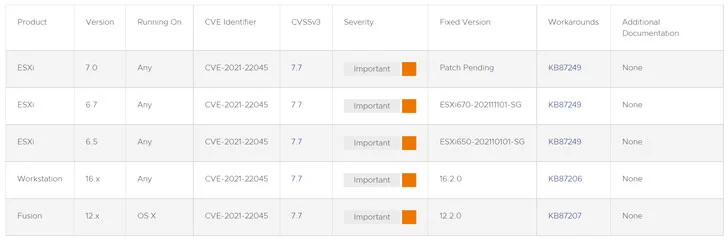
The vulnerability affects VMware’s Workstation versions 16, Fusion versions 12, and ESXi versions 6.5, 6.7, and 7.0.
How to Fix the Vulnerability?
The firm has released patches for its other affected products, except for version 7 of the ESXi product. The firm has also released a patch for its other affected products, except the seventh version of the ESXi product.
The company shared guidelines for ESXi, which includes the precautionary steps that users should follow.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free



































