
What Do You Need to Know About CVE-2023-33299 Vulnerability in FortiNAC?
What is CVE-2023-33299?
Discovered by security researcher Florian Hauser of CODE WHITE, CVE-2023-33299 is a deserialization of untrusted data vulnerability, classified under CWE-502. Simply put, this vulnerability is a loophole that allows an unauthenticated user to execute unauthorized code or commands through specifically designed requests to the tcp/1050 service.
The severity of this vulnerability is high, with a CVSS base score of 9.8, indicating it’s critical. This score is determined by Fortinet Inc. and indicates that the vulnerability can be exploited remotely, with a high impact on confidentiality, integrity, and availability.
How to exploit CVE-2023-33299?
While specific details about how to exploit this vulnerability have not been disclosed, an attacker could craft a special request to the tcp/1050 service to exploit this vulnerability. By doing so, the attacker could execute unauthorized code or commands.
How critical is CVE-2023-33299?
With a CVSS base score of 9.8, CVE-2023-33299 is considered a critical vulnerability. It allows remote execution of unauthorized code or commands without the need for authentication, thus opening up the potential for malicious hackers to extract or manipulate sensitive data from affected systems.
Impacted products by CVE-2023-33299
If you are using any of the following FortiNAC versions, you are vulnerable to this attack:
Are there any exploits in the wild for CVE-2023-33299?
As of the date of this writing, there have not been any publicly disclosed exploits for CVE-2023-33299. However, the existence of this vulnerability underscores the need for organizations to regularly monitor cybersecurity news, apply patches, and update systems to prevent potential exploitation.
How to detect CVE-2023-33299?
Detection of the exploitation of this vulnerability would likely require network monitoring tools to observe any unusual or unauthorized network activity related to tcp/1050 service. It’s important to note that standard network monitoring might not always be able to detect exploits of this vulnerability due to their potential sophistication.
How to fix or mitigate CVE-2023-33299?
Fortinet has already addressed this critical security flaw and released updates for FortiNAC versions 7.2.2, 9.1.10, 9.2.8, and 9.4.3.
Users of affected versions are urged to immediately update to the following versions for optimal protection:
In order to protect your systems against potential threats, it is highly recommended to update even if your network has not shown any signs of intrusion.
As our digital world expands, and the complexity of our networks grows, vigilance and quick response to potential vulnerabilities is key in maintaining the security of your network. Staying informed about the latest security news and immediately applying patches and updates is essential to keep your networks secure.
How Can SOCRadar Help?
SOCRadar helps organizations for staying up-to-date on the latest security threats and vulnerabilities. It gathers information on all known vulnerabilities and presents it in a way that is easy to act upon, using alerts to help you prioritize your actions and stay informed about any potential threats to your organization.
You can utilize SOCRadar’s Vulnerability Intelligence module to access detailed information on vulnerabilities, allowing you to effectively manage any related issues and prioritize the necessary patches.
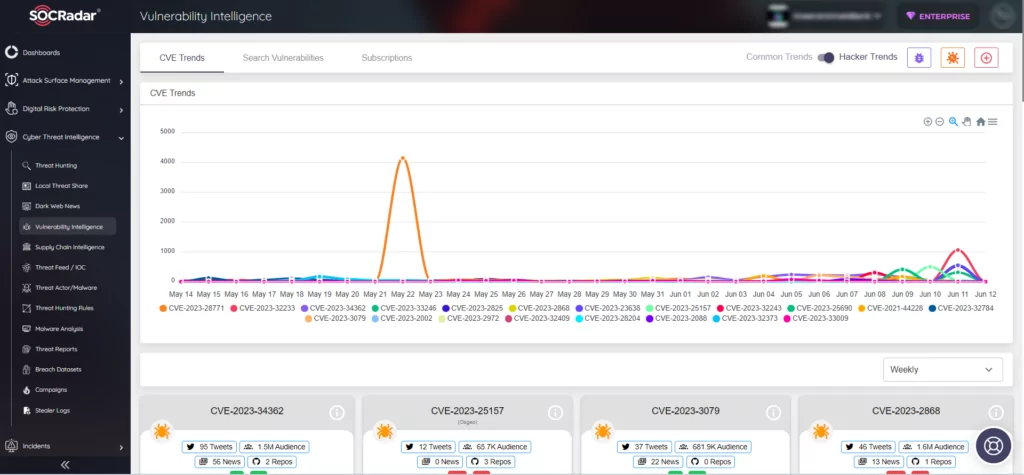
Additionally, with SOCRadar’s Attack Surface Management, you have the capability to monitor vulnerabilities in automatically identified products within your organization’s digital footprint in real time. This empowers security teams to take a proactive approach toward prioritizing vulnerabilities by accessing contextual intelligence.





































