
What Do You Need to Know About Zyxel NAS Products’ Command Injection Vulnerability CVE-2023-27992
Recently, a significant vulnerability was discovered in Zyxel NAS326, NAS540, and NAS542 firmware versions that could lead to a severe security risk. Known as CVE-2023-27992, this pre-authentication command injection vulnerability poses a critical threat, with a CVSS base score of 9.8, indicating a high level of severity.
What is CVE-2023-27992?
The pre-authentication command injection vulnerability was discovered in Zyxel’s NAS products, specifically NAS326, NAS540, and NAS542 firmware versions. It allows an unauthenticated attacker to execute operating system (OS) commands remotely by sending a crafted HTTP request. This vulnerability can be exploited with relative ease, making it a serious threat to any organization using these versions of Zyxel NAS products.
Impacted Products by CVE-2023-27992
The following Zyxel NAS products and versions are affected by this vulnerability:
Are there any exploits in the wild for CVE-2023-27992?
As of the time of writing, there are no known exploits for this vulnerability in the wild. However, due to the severity and the ease of exploitation of the vulnerability, it is likely that threat actors could soon start exploiting it if they haven’t already. This section will be updated as soon as new information becomes available.
Are there any threat actors actively exploiting CVE-2023-27992?
There are no known threat actors actively exploiting this vulnerability at the moment. Nonetheless, the high severity of the vulnerability indicates that it could potentially be a target for malicious actors. Organizations should remain vigilant and monitor for any suspicious activities.
How to Detect CVE-2023-27992
If the Zyxel NAS products and specific versions mentioned above are in use within your setup, you are susceptible to this vulnerability.
How to Mitigate CVE-2023-27992
Zyxel has already released patches to address the pre-authentication command injection vulnerability in the affected NAS versions:
Users are strongly advised to install these patches for optimal protection. However, Zyxel does not mention any other workarounds or mitigations.
How Can SOCRadar Help?
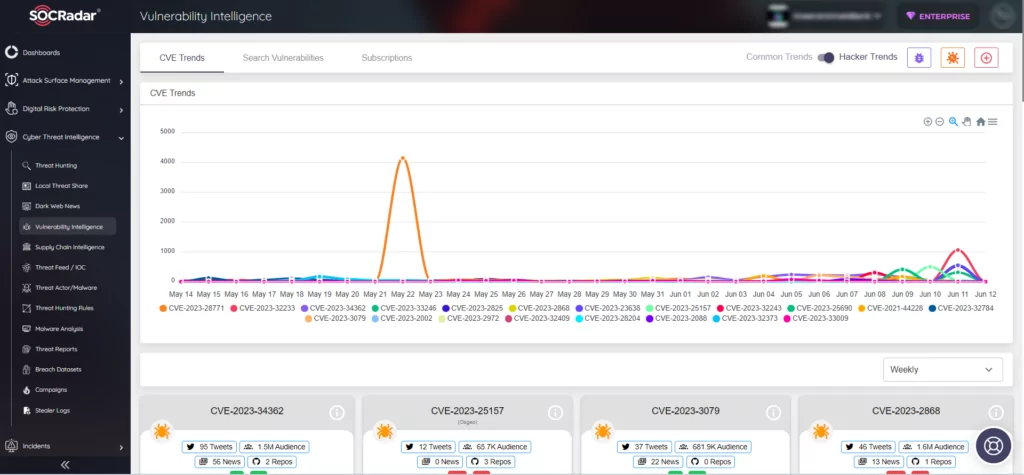
SOCRadar helps organizations for staying up-to-date on the latest security threats and vulnerabilities. It gathers information on all known vulnerabilities and presents it in a way that is easy to act upon, using alerts to help you prioritize your actions and stay informed about any potential threats to your organization.
You can utilize SOCRadar’s Vulnerability Intelligence module to access detailed information on vulnerabilities, allowing you to effectively manage any related issues and prioritize the necessary patches.
Additionally, with SOCRadar’s Attack Surface Management, you have the capability to monitor vulnerabilities in automatically identified products within your organization’s digital footprint in real time. This empowers security teams to take a proactive approach toward prioritizing vulnerabilities by accessing contextual intelligence.





































