
What is Extended Detection and Response (XDR)?
Extended Detection and Response (XDR) is a security technology that delivers comprehensive visibility into data across networks and clouds in addition to apps and endpoints while implementing analytics and automation to detect, analyze, hunt, and remediate today’s and tomorrow’s threats.
It is more sophisticated and advanced progress of endpoint detection and response (EDR) technology. According to Gartner, the early XDR vendor candidates include Cisco, Fortinet, Fidelis Cybersecurity, McAfee, Microsoft, Palo Alto Networks, Trend Micro, Sophos, FireEye, and Symantec.
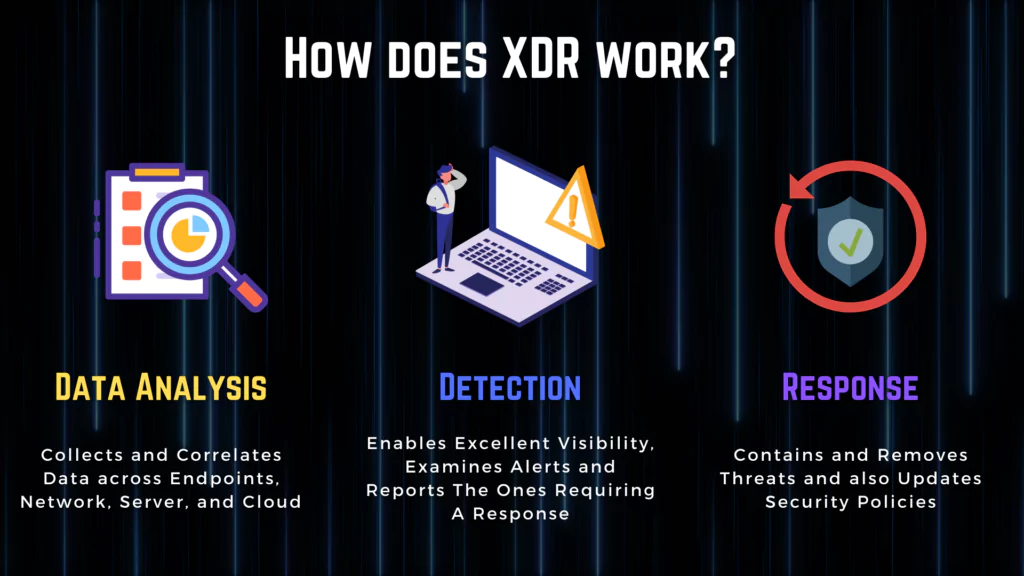
How does XDR work?
XDR collects data across various security layers, including endpoints and network, server, and cloud. Then, it applies data analysis to correlate context from numerous alerts from these data to surface a much smaller number of high-priority signals, providing avoidance of overwhelming volumes of security alerts to security teams.
XDR’s visibility allows it to examine signs and announce the ones that require a response. That same visibility enables it to create baselines of normal behavior within an environment to detect threats that use legitimate software and investigate their origins to prevent them from affecting other parts of the system.
Finally, XDR contains and removes threats it detects and also updates security policies to avoid a similar breach from occurring again. How XDR works can be summarized in three steps:
- Data Analysis
- Detection
- Response
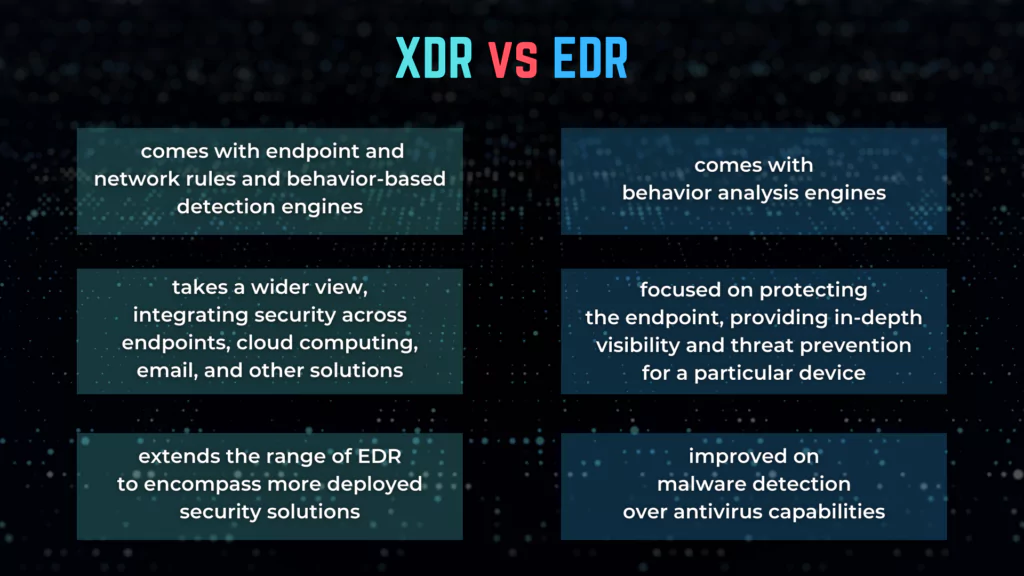
XDR vs. EDR
Both EDR (Endpoint Detection and Response) and XDR are created to provide automated threat detection, remediation, and response via deep data discernibility and the use of data analytics and threat intelligence.
Endpoint Detection and Response (EDR) solutions provide high protection for corporate endpoints. In contrast, XDR solutions integrate security visibility across the entire infrastructure, including endpoints, cloud infrastructure, mobile devices, and more.
Why do enterprises need XDR?
SOC teams need a platform that intelligently collects all relevant security data and reports related to advanced adversaries. XDR is also functionally similar to SIEM and SOAR solutions; however, the level of integration at deployment and the focus on threat detection and DFIR use cases are the differentiated features.
As adversaries apply more complicated tactics, techniques, and procedures (TTP) to bypass and exploit traditional security controls, SOC teams struggle to secure increasing numbers of vulnerable digital assets inside and outside the traditional network perimeter.
Enterprises need united and proactive security actions to protect the entire landscape of technology assets, spanning legacy not just endpoints but also mobile and cloud workloads. With bad actors, such as individual attackers, hacking groups, nation-states, or even potentially malicious insiders constantly circling, security and risk managers must deal with several disconnected security tools and data sets.
Security teams cope with the data that results in overloaded alerts, with lots of false positives and little data integration with analysis tools or incident response. Enterprise security and risk management leaders should consider the security benefits and productivity value of an XDRs olution.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free



































