Everything You Need to Know About the Alleged Twilio SendGrid Breach
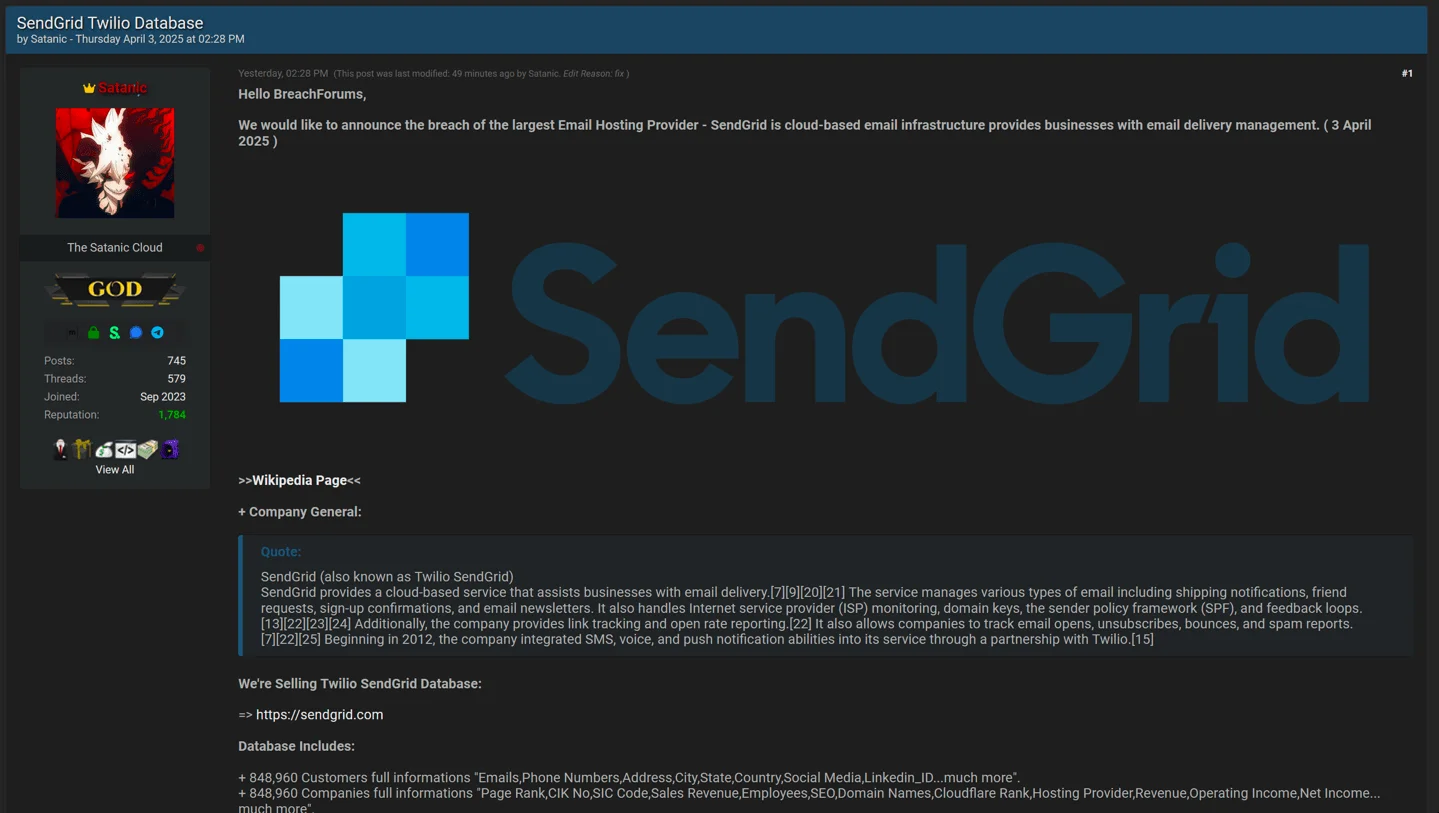
On April 3, 2025, a threat actor operating under the alias Satanic announced on BreachForums that they were in possession of a significant dataset allegedly obtained from Twilio SendGrid, a well-known provider of cloud-based email infrastructure services. The threat actor offered nearly 849,000 customer and company records for sale, describing a wide array of sensitive personal and organizational information.
The alleged incident has generated considerable attention within the cybersecurity community, especially given SendGrid’s critical role in managing transactional and marketing email delivery for numerous businesses worldwide.
1. Who is Behind the Alleged SendGrid Breach?
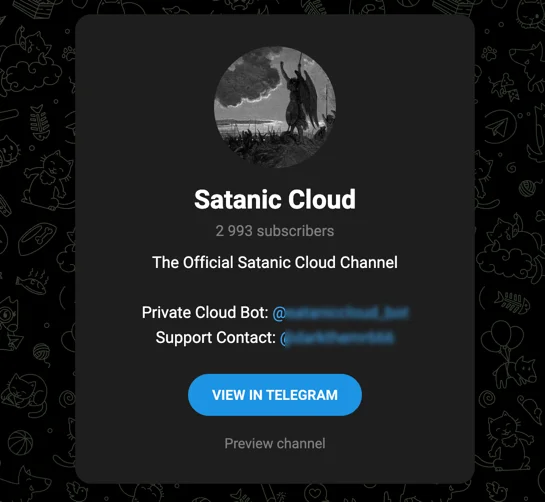
The threat actor attributing the breach to their actions is known by the pseudonym Satanic, a popular figure in various hacker forums and Telegram communities. Active since at least September 2023, this threat actor is known to manage a Telegram channel dedicated to distributing stolen credentials, including stealer logs and combolists.
Satanic initially gained notoriety by re-publishing previously leaked datasets, which contributed to a rapid rise in reputation across underground platforms. The actor has also been accused of repurposing data from other forums, including allegations from LeakBase administrators who claimed that Satanic reposted their content without authorization on BreachForums.
In past activities, Satanic has been associated with breach allegations involving several companies, including Rappi, Hot Topic, and the Tracelo platform.
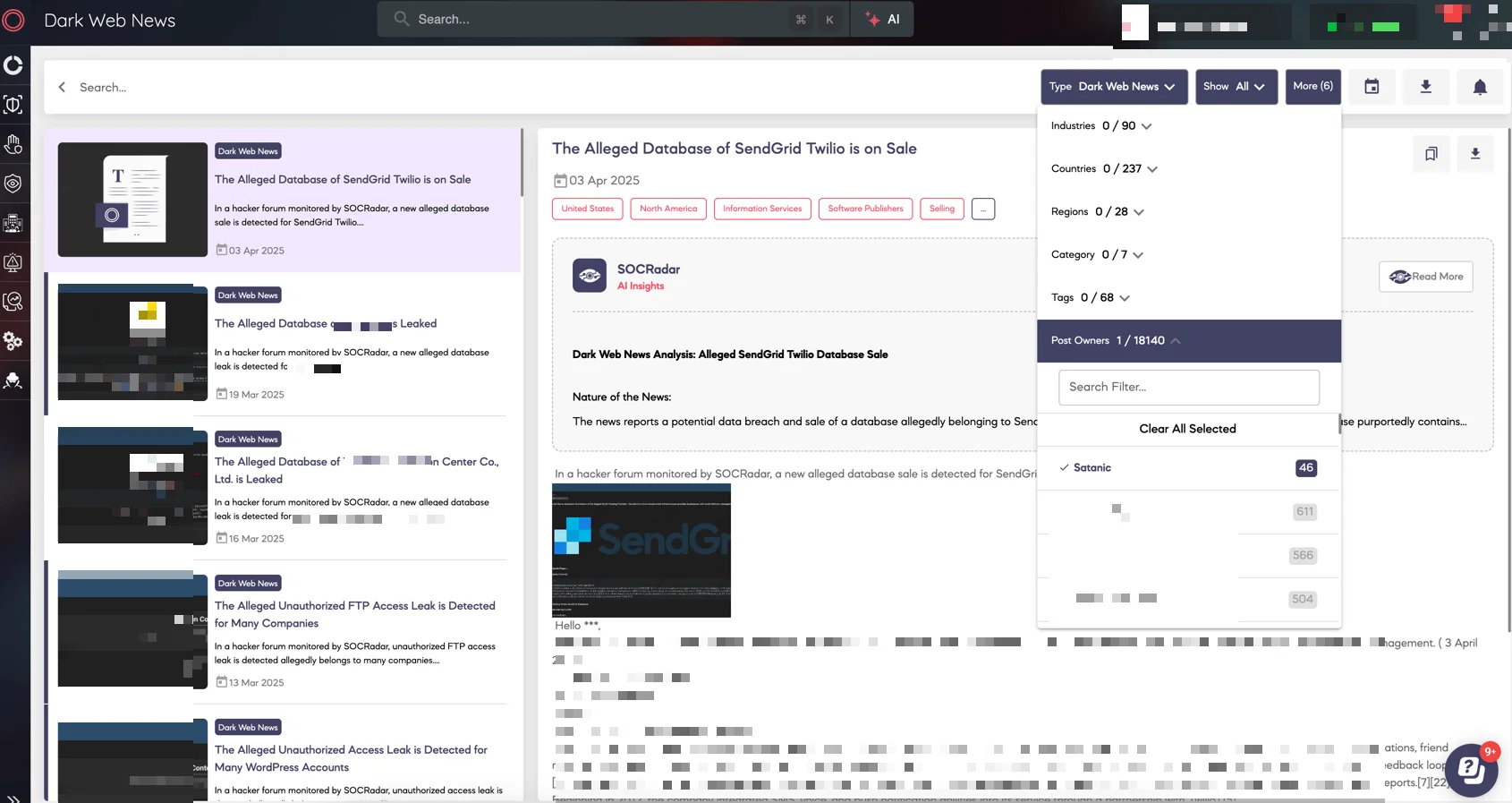
To stay up to date with actors like Satanic and monitor similar dark web activity, SOCRadar’s Dark Web News offers regularly updated threat intelligence reports that highlight emerging breaches, actor profiles, and underground movements.
These insights can help organizations understand the evolving tactics used by actors operating in darknet environments and take proactive security measures accordingly.
2. What Type of Data Was Allegedly Exposed?
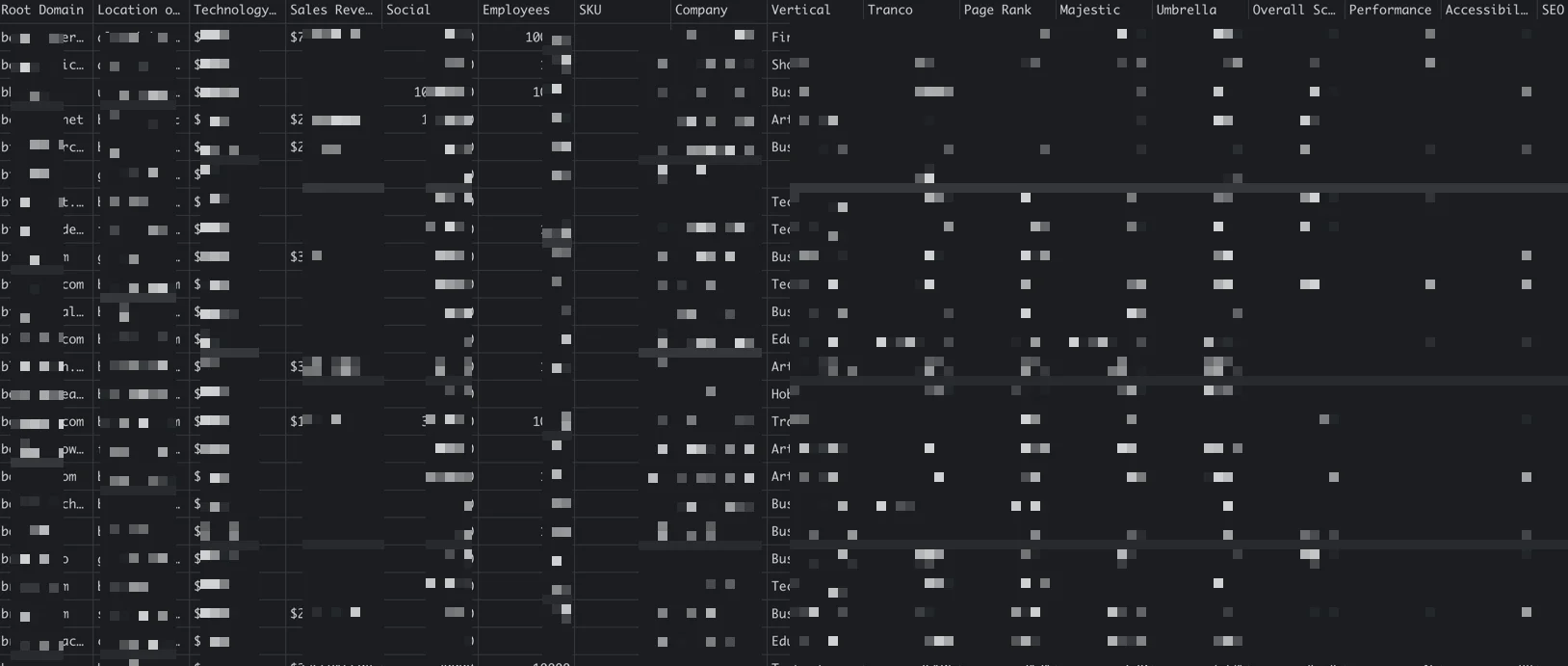
The threat actor claims to have obtained a database containing detailed records for approximately 848,960 individuals and companies. According to their statement, the exposed information includes:
- Personal and contact details, such as full names, email addresses, phone numbers, physical locations (including city, state, and country), as well as social media profiles and LinkedIn IDs.
- Corporate data, including company names, domain names, industry classification codes (CIK and SIC), employee numbers, revenue figures, and financial performance indicators like operating and net income.
- Technical and analytical attributes, such as SEO metrics, PageRank scores, hosting provider information, and Cloudflare rankings.
Additionally, the threat actor claims to possess employee-level data and internal organizational insights. If genuine, the breadth of this information could pose significant risks, including identity theft, phishing attacks, or corporate espionage.
3. What Sample Has Been Presented?
To support their claims, Satanic later shared a sample consisting of 10,000 records. This sample appears to include both customer and company-level data, as described in the original forum post.
Although the threat actor did not provide additional verification such as hashes or screenshots, the size and complexity of the sample suggest an effort to demonstrate the legitimacy of the dataset and attract interest from potential buyers or affected parties
4. When Did the Alleged Breach Occur?
The dataset was first introduced on April 3, 2025, through a post on BreachForums. However, no specific date or timeframe for the unauthorized access was disclosed by the actor. Twilio has not observed recent indications of a breach within its environment, leaving the exact timeline uncertain.
5. What Method Was Allegedly Used?
The threat actor has not provided specific technical details about how the alleged breach occurred. No references have been made to known vulnerabilities or direct exploitation of SendGrid infrastructure.
However, given the actor’s established history of distributing stealer logs—malicious data extracted from infected systems—it is possible that initial access may have been obtained through compromised credentials harvested from such logs. These types of data, which often include saved login details, session tokens, and browser-stored passwords, are commonly traded and weaponized within cybercriminal communities.
While this theory aligns with the actor’s prior activities, it remains speculative in the absence of concrete evidence or technical indicators.
6. What Is Twilio’s Official Response?
Twilio has publicly denied any compromise of its systems or those of SendGrid. A company spokesperson clarified:
“There is no evidence to suggest that Twilio or Twilio SendGrid was breached. To the best of our knowledge, after reviewing a sampling of this data, we believe that none of this data originated from SendGrid.”
This official stance has prompted discussion among cybercriminal forum members. Several high-profile participants expressed doubt over Twilio’s position, speculating whether the dataset could originate from third-party integrations or older incidents. These reactions reflect ongoing skepticism within cybercriminal circles but are not backed by independent verification at this time.
7. Who Might Be Affected?
If the threat actor’s claims are accurate, this incident may affect up to 849,000 customers and organizations globally. The presence of detailed personal and financial information in the sample indicates that the potential impact may extend to individuals, businesses, and even third-party platforms that utilize SendGrid for email delivery.
Due to the absence of independent validation, it remains unclear how much of the data is current, unique, or directly linked to SendGrid systems.
Incidents like the one allegedly involving SendGrid highlight how sensitive data can circulate across various dark web sources without organizations being immediately aware. For security teams, identifying whether company assets have been leaked—even indirectly—can be critical.
To help with this, SOCRadar Labs offers a Free Dark Web Report that allows organizations to instantly check if their email addresses, domains, or employee credentials have been exposed on dark web forums, black markets, or Telegram channels.
Without requiring a subscription, this free service scans a wide range of underground sources and provides insight into:
- Leaked credentials tied to your employees
- Mentions of your brand or domains on the dark web
- Data linked to infected machines within your infrastructure
- Listings of your information being offered for sale
You can try it by simply entering a company email address or domain name to receive a sample report and better understand your current risk exposure.
8. What Actions Should Organizations Take?
Although Twilio has denied any unauthorized access, organizations using SendGrid are encouraged to take the following precautionary steps:
- Review system logs for unusual activity related to email or user account access
- Rotate API keys and credentials associated with SendGrid or integrated services
- Enable multi-factor authentication (MFA) wherever possible
- Monitor dark web sources and data leak repositories for references to company domains or employee emails
- Engage threat intelligence providers to assess potential exposure
9. How Can Similar Incidents Be Prevented?
To improve resilience against future breaches, organizations should consider the following measures:
- Limit access permissions when integrating third-party platforms
- Perform regular audits of credentials and API usage
- Establish real-time monitoring for anomalies in outbound communications or bulk data activity
- Educate staff on data hygiene and phishing risks
- Maintain up-to-date inventories of all external service dependencies
How SOCRadar Helps You Stay Ahead of Dark Web Threats
Incidents like the one involving SendGrid underline a critical truth in cybersecurity: by the time a data leak surfaces publicly, the damage may already be in motion. Today, many cyberattacks begin with early signals on the dark web—signals that are often missed without the right visibility.
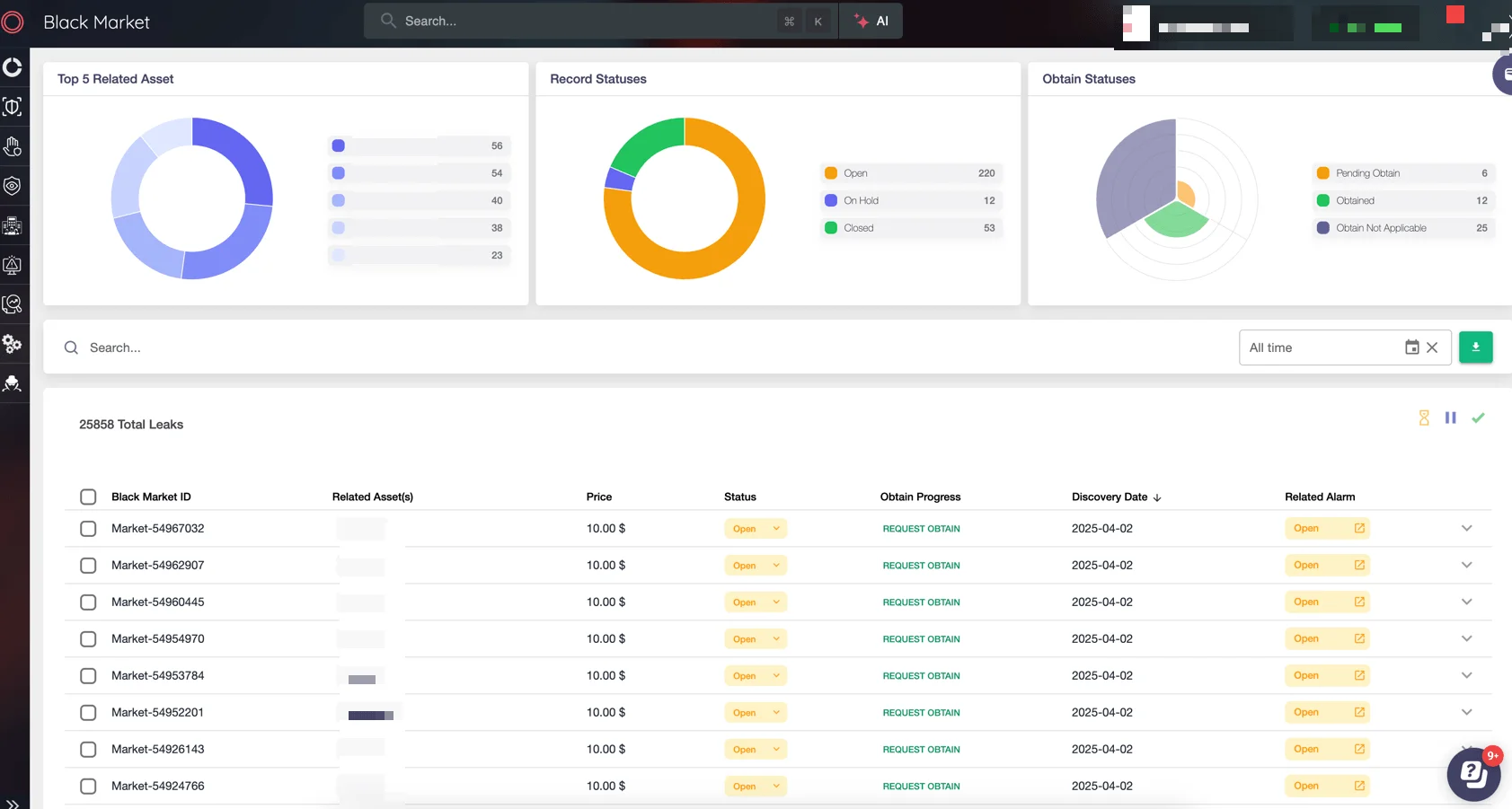
This is where SOCRadar’s Advanced Dark Web Monitoring becomes essential. Designed to give organizations proactive insight into dark web activity, the platform continuously scans a wide range of underground sources—including hacker forums, black markets, Telegram channels, and private messaging groups.
With capabilities such as detecting leaked credentials, monitoring botnet-related threats, identifying exposed PII, and even alerting on mentions of your brand or executives, SOCRadar acts as a digital periscope into the dark web—helping you detect risks before they escalate into real incidents.
Whether you’re defending against impersonation, data theft, or early access sales, SOCRadar’s Advanced Dark Web Monitoring offers a structured approach to:
- Monitor your organization’s digital assets in real time
- Detect and respond to threats across dark web sources
- Protect employees, infrastructure, and brand reputation
Security teams can also leverage its search engine, customizable dashboards, and daily threat intelligence to maintain visibility and improve response times. Getting started is simple—with just a few steps, you can define your scope, activate monitoring, and begin receiving actionable alerts tailored to your organization’s needs.