CISA Issues a New Warning for Vulnerabilities in Industrial Control Systems (ICS)
The recent advisories issued by the US Cybersecurity and Infrastructure Security Agency (CISA) highlight the serious vulnerabilities in industrial control systems (ICS) used by organizations across multiple critical infrastructure industries.
49 vulnerabilities have been identified in eight ICS products from vendors such as Siemens, Rockwell Automation, Hitachi, Delta Electronics, Keysight, and VISAM.
These vulnerabilities, some of which are unpatched, are remotely exploitable and allow attackers to take control of affected systems, escalate privileges, bypass security controls, steal data, and even crash systems.
Affected Products
The number of vulnerabilities in each affected ICS product line is listed below:
- Siemens RUGGEDCOM APE1808, 7 vulnerabilities
- Siemens Scalance W-700 devices, 17 vulnerabilities
- Delta Electronic InfraSuite Device Master, 13 vulnerabilities
- Vbase Automation technology, 7 vulnerabilities
- Rockwell Automaton, 3 vulnerabilities
- Keysight N6845A Geolocation Server, 1 vulnerability
- Energy GMS600, PWC600, and Relion, 1 vulnerability
Siemens Products Await a Fix
Siemens RUGGEDCOM APE1808 technology is currently vulnerable, and no patches are available. Many critical infrastructure organizations globally rely on this product for hosting commercial applications. The vulnerabilities could allow attackers to either crash the system or gain higher privileges on a compromised system.
In addition, there are 17 other flaws in various third-party components integrated into Siemens Scalance W-700 devices, which organizations in multiple critical infrastructure sectors, such as chemical, energy, food, agriculture, and manufacturing, also use.
Siemens has advised its users to update the software to version 2.0 or later and implement controls to protect network access to the devices.
Delta Electronics ICS Vulnerable to DoS
Delta Electronics’ InfraSuite Device Master, which energy organizations use to monitor critical systems, has newly revealed vulnerabilities. These security flaws can be exploited by attackers to cause denial-of-service issues or to steal sensitive data, which threat actırs can use for future attacks. Below are some of the critical vulnerabilities:
CVE-2023-1133 (CVSS score: 9.8): A critical flaw arises because InfraSuite Device Master is programmed to receive unverified UDP packets and deserialize their contents. This flaw enables a remote attacker to execute any code without being authenticated.
CVE-2023-1136 (CVSS score: 9.8): Prior to version 1.0.5 of Delta Electronics InfraSuite Device Master, an unauthenticated attacker could create a valid token and bypass authentication.
CVE-2023-1140 (CVSS score: 9.8): This flaw exists in versions of Delta Electronics InfraSuite Device Master that are older than 1.0.5 and could let an attacker run unauthenticated remote code as an administrator.
Other vulnerabilities in Delta Electronics Device Master are listed below, all of which have a CVSS score of 8.8:
- CVE-2023-1139: Deserialization Of Untrusted Data
- CVE-2023-1144: Improper Access Control
- CVE-2023-1143: Exposed Dangerous Method Or Function
- CVE-2023-1141: Command Injection
Cisco Discloses Vulnerabilities in WellinTech ICS
Cisco Talos discovered two vulnerabilities in WellinTech’s KingHistorian data manager for industrial control systems.
The first vulnerability, CVE-2022-45124, allows an attacker to steal a user’s credentials by obtaining an authentication packet, whereas the second, CVE-2022-43663, allows an attacker to cause a buffer overflow by sending a malicious packet.
Cisco Talos collaborated with WellinTech for a fix and recommended updating to WellinTech KingHistorian ICS version 35.01.00.05. A Snort rule, 61093, is also provided to detect exploitation attempts.
High Alert for ICS
CISA has issued warnings for vulnerabilities in ICS products before, emphasizing the critical importance of improved cybersecurity strategies in these industries.
You can find some of the previously disclosed vulnerabilities (in GE Digital, Siemens, Contec, and Mitsubishi Electric)in our blog post published in January. In the same month, CISA warned Hitachi, Johnson Controls, Panasonic, and Sewio ICS users about similar threats.
Also, to learn more about the critical infrastructure industries from a cybersecurity perspective, you can check out our analysis on critical infrastructures.
Recommendations
CISA strongly urges administrators and users that use any of the vulnerable ICS products to apply security precautions to evade future risks. Find all advisories issued by CISA relating to this issue here.
You can discover more about a vulnerability’s status on SOCRadar, such as exploitability, attack vectors, and updates.
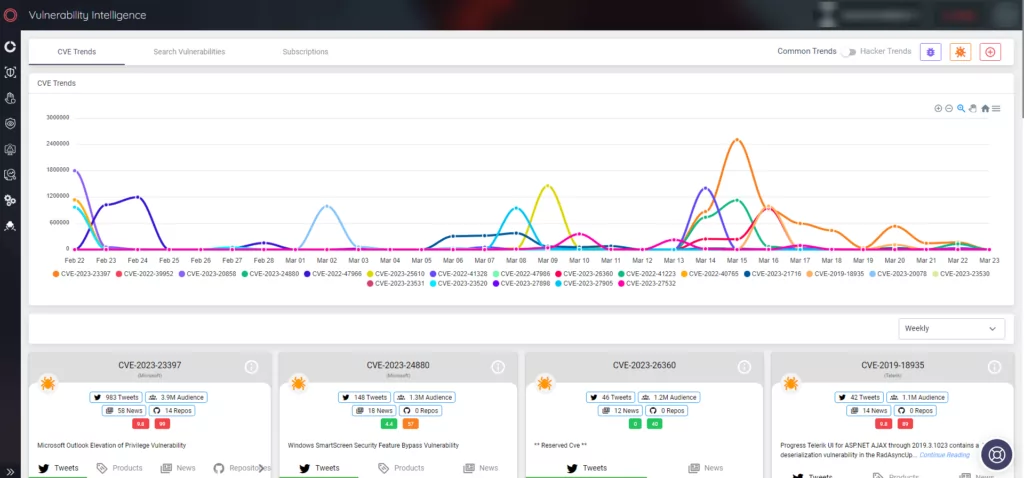
Keeping your systems and software updated is also critical, as it can fortify against the newest security vulnerabilities. SOCRadar monitors organizational assets and sends alarms to ensure you are aware whenever a vulnerability is affecting them, allowing you to prioritize while patching.



































