Critical Auth Bypass Vulnerabilities: SonicWall Urges Immediate Patching for GMS/Analytics
SonicWall has issued an urgent security notice regarding critical vulnerabilities impacting their Global Management System (GMS) firewall management and Analytics network reporting engine software suites.
The vulnerabilities, disclosed responsibly, include four high-risk vulnerabilities that enable attackers to bypass authentication and potentially expose sensitive information to unauthorized actors. Immediate patching is strongly advised to mitigate the risks associated with these vulnerabilities.
The Impact of SonicWall Vulnerabilities
The suite of vulnerabilities discovered in SonicWall’s GMS/Analytics presents significant risks to organizations. Exploiting these vulnerabilities allows attackers to view and manipulate data that would normally be inaccessible to them. This includes sensitive information belonging to other users or any data within the compromised application’s reach. Successful exploitation could lead to persistent changes in the application’s content and behavior, posing serious security and privacy concerns.
The Critical Vulnerabilities
Among the 15 vulnerabilities identified, four have been rated as critical with a CVSSv3 rating. These vulnerabilities demand immediate attention and patching. The critical vulnerabilities include:
- CVE-2023-34133 (CVSS Score: 9.8): Unauthenticated attackers may use this SQL injection vulnerability to extract sensitive data from the application database. The vulnerability arises as a result of improper neutralization of special elements used in SQL commands.
- CVE-2023-34134 (CVSS Score: 9.8): The vulnerability permits authenticated attackers to read the administrator password hash by making a web service call.
- CVE-2023-34124 (CVSS Score: 9.4): Insufficient checks in the authentication mechanism of SonicWall GMS and Analytics Web Services have resulted in an authentication bypass vulnerability.
- CVE-2023-34137 (CVSS Score: 9.4): The CAS Web Services application exhibits an authentication bypass vulnerability due to the utilization of static values for authentication without proper checks.
Exploitation of these vulnerabilities does not require user interaction and can be executed remotely by unauthenticated threat actors.
Mitigation Steps for Vulnerabilities in SonicWall
SonicWall PSIRT strongly advises organizations using the affected GMS/Analytics On-Prem versions to immediately upgrade to the respective patched versions. Given the severity of the risks, organizations must upgrade to the patched versions, GMS 9.3.3 and Analytics 2.5.2, to effectively mitigate these vulnerabilities.
SonicWall has provided deployment guides to assist organizations in this critical patching process. SonicWall emphasizes the importance of adhering to security best practices and keeping software up to date to ensure a proactive defense against evolving threats.
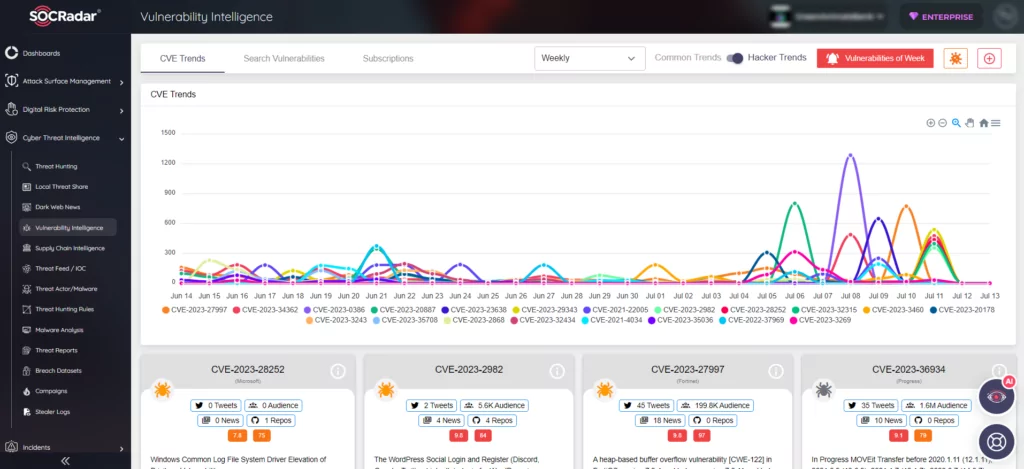
Supercharge Your Patch Management with SOCRadar
By incorporating SOCRadar’s Vulnerability Intelligence module, organizations can strengthen their defenses against vulnerabilities similar to those found in SonicWall’s GMS/Analytics. This powerful tool provides real-time information on emerging security flaws and recommended patches, enabling proactive identification and remediation of potential risks. With SOCRadar’s comprehensive vulnerability management capabilities, organizations can effectively safeguard their network infrastructure and maintain a robust security posture.