Customer Story: Social Media Takedown in the Gulf Region
The birth and growth of social media were one of the events shaping the last decades. It started with a straightforward idea (connecting with your school buddies), but social media affected people’s lives and nations` fate, i.e., Arab Springs.
Therefore, it would be impossible for threat actors to resist entering social media to reach their malicious agenda. All you need to impersonate a person, preferably an influencer in any field, is a picture of them (maybe a tick sign, too?), especially if that person does not have a robust online presence. Then, you could manipulate people to do things they would not normally do.
Threat actors could claim to be a celebrity (a deceased one in the example above) and ask for money to come back to life and make some more music for $600. Or they could pretend to be a company’s CEO and share a link for their followers to click.
One of our customers, a finance organization in the Gulf region, got hit by a similar attack with one of the scenarios above. No, they did not get a message from a dead celebrity.
In a social media site, Instagram, in this case, there were advertisements with a link to a domain impersonating our customer’s website. The ads originated from an account sharing financial news about the Gulf region in Arabic; the ads also had the current CEO’s picture and used the customer’s name and logo.
In addition to blatant brand abuse, this type of attack could end up with credential harvesting of our customer’s users and potential users. Worse, worse; they could download malware without realizing it.
First, let us talk about why it is challenging to discover such ads. These ads consist of a link and a picture. Without image processing in your detection, an automatic keyword search would not detect them. The mentioned ads are also localized, so if your account is not based in the Gulf region, they will not be seen on your timeline. They are also only available for a specific period; there is no chance of catching these malicious ads if no scans are available in the specific period. Last, these ads are only available in the local language, Arabic here. Therefore if the scans are not in the correct language and do not have proper keywords, you will not catch these ads even if they are not image-based.
SOCRadar’s modules implementing hybrid scans combining automated scans and manual efforts are one of the best options to deal with this kind of threat. In addition, SOCRadar analysts will help you further resolve any issue.
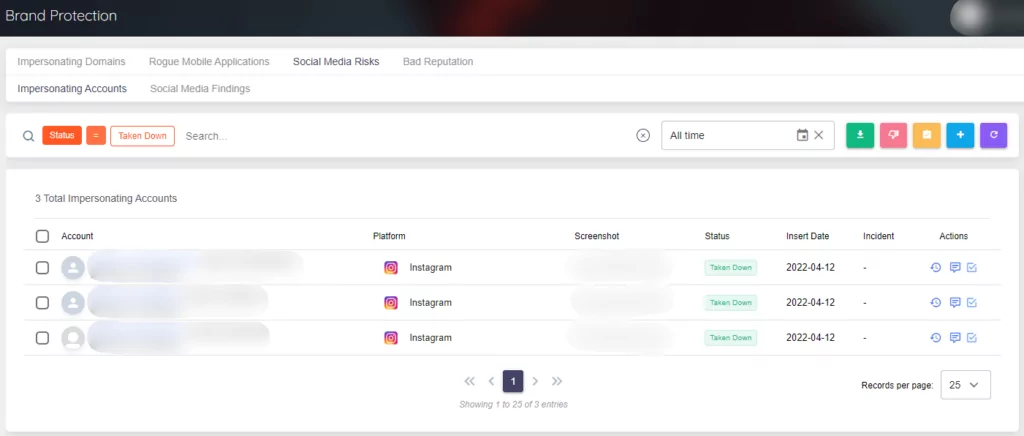
In this case, the customer asked for the takedown of the ad and the impersonating domain. One of the tricky parts of the takedowns is your company’s reputation with domain registrars and social media platforms. One needs to make a case for every request, and all the cases should be based on solid evidence and documentation. Otherwise, completing your request could take longer, or the request could be denied. Thanks to our previous interaction, SOCRadar could complete takedown actions very quickly and without almost no exception. In this case, the ad and the domain took down very quickly.
Our analysts investigated the impersonating website before the takedown. They found no evidence of malicious downloads, but the website was obviously designed for credential harvesting. However, they noticed a link to a private Telegram channel where financial advice was shared. Our analysts enriched their analysis by checking the owner, start dates, and other related information about the social media account and impersonating domain. Our analyst concluded that the phishing website was published earlier than the ads. In addition, the social media account was a compromised account that was stolen and had a name change. The Telegram channel might be a part of an influence operation to change user behavior in the region.
In addition to takedowns of ads and impersonating domains, all these findings were presented to the customer with their legal options to pursue a criminal investigation.
Why is This Important?
A phishing attack deceives victims by creating a sense of urgency combined with social engineering. When the victim opens a phishing email or text message and clicks on the malicious link or a malicious link attached to an ad, as discussed above, they are redirected to a fake website that matches the actual site. Personal information such as social security numbers, phone numbers, and social media account information are common targets for identity theft phishing attacks. These attacks might cause reputational or financial damage to an institution/person and later open a way to decrease the business volume. To avoid phishing attacks at the early stages, SOCRadar generates phishing link alerts with an Extended Threat Intelligence solution for any potential impersonating and typosquatting domains to prevent data breaches and credential thefts.