
CVE-2022-47633 Vulnerability Allows Attackers to Bypass Kyverno Signature Verification
The Kyverno admission controller for container images has been found to have a high-severity security vulnerability. The vulnerability could let attackers introduce malicious code into cloud production environments.
Users can define and enforce policies for their cluster and applications using the open-source Kubernetes policy engine Kyverno, which Red Hat maintains on GitHub. Kyverno can be applied to ensure that a cluster’s resources, applications, and other components adhere to operational, security, and compliance standards.
Kyverno’s admission controller offers a signature verification mechanism to ensure that only signed container images can enter a Kubernetes cluster.
The vulnerability, tracked as CVE-2022-47633, allows a user to bypass the mentioned signature verification.
How Could It Affect?
Attackers may be able to hijack a victim’s pod and use all of its resources, including credentials and API tokens, using the CVE-2022-47633 vulnerability. Successful exploitation of the vulnerability could ultimately cause a supply chain issue.
The vulnerability was introduced in Kyverno version 1.8.3 due to the use of verifyImages rules used for verification, which cannot prevent unknown registries.
Visit the advisory for the CVE-2022-47633 vulnerability here.
How Is It Exploited?
An attacker may use social engineering techniques to persuade an administrator to pull malicious images into containers. Attackers might host these images on compromised accounts and use phishing attacks to trick users into using them as well.
- The user is persuaded to use a malicious proxy to download the container images or to run the signed image from the malicious container registry.
- When the admission controller is asked to validate, it requests a signature from the container registry and the image manifest (to get the image hash accordingly).
- The admission controller verifies the signed image signature returned by the malicious proxy.
- CVE-2022-47633 causes the admission controller to request the manifest of the signed image once more to obtain the digest for mutation. Still, the malicious registry returns it for the unsigned and malicious image.
- Given approval, the pod starts running the malicious image.
The malicious container image can be infected with a wide range of payloads, allowing the attacker to further compromise the environment. Cryptominers, rootkits, infostealers, exploit kits for container escape and lateral movement, and other malware could be deployed.
Is There a Mitigation Available?
Version 1.8.5 addresses the vulnerability by ensuring that the same image hash used to verify signatures is also used to modify the workload specification.
You can use image vulnerability scanning tools to identify threats such as CVE-2022-47633.
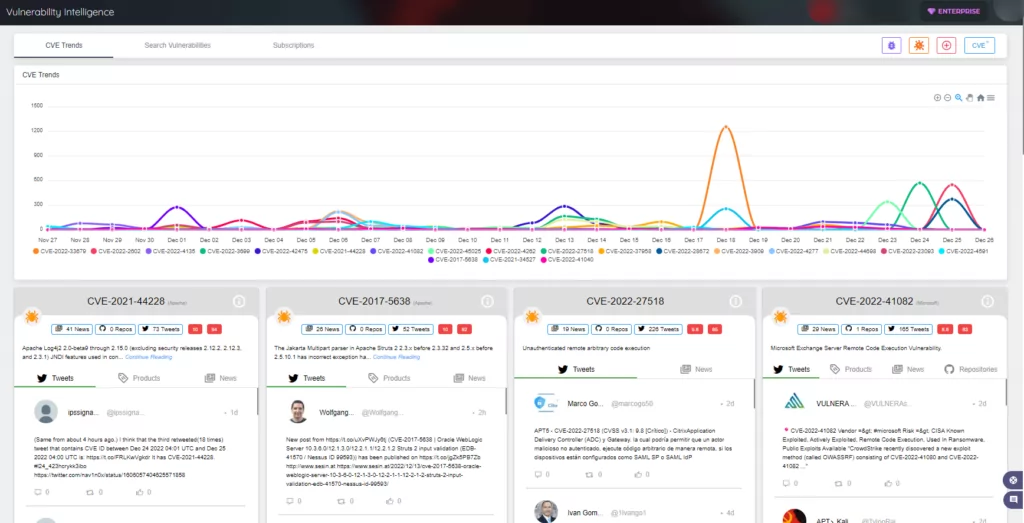
Additionally, by using SOCRadar’s Cloud Security Module (CSM), you can be alerted to security events that affect your cloud environment.
Kyverno advises its users to update to the latest version as soon as possible.




































