
Dark Opinion: Doing Things Under the Rose, Proxy Data Recovery Companies for Ransomware Negotiation
During the pandemic, a lot of untrue stories spread around. This happened a lot after people started questioning the COVID-19 vaccine. One common belief was that “the vaccine producers are the ones spreading the viruses.” Many people who are against vaccines believed this pretty quickly.
It resembles stories about anti virus companies in the 90s. These kinds of stories can really take off online. Nowadays, many organizations are fighting against a wave of serious cyber attacks, including ransomware. This has made a lot of people start thinking about these issues.
Ransomware is a rising industry amongst cyber threat actors because of different reasons. In the business world, it’s like a product that fits the market really well. It takes advantage of the fact that a lot of people don’t know much about cyber security. There’s also more digital stuff to attack and new weaknesses found every day.
Once ransomware hits, it feels like there’s no choice but to pay or engage in negotiation to get your data back. Even the FBI has said that sometimes, if you need your data, paying is the only way. A big example of this is what happened in May 2021 with Colonial Pipeline. This major U.S. fuel pipeline got hit by a ransomware attack, and it messed up fuel distribution across the East Coast. The company ended up paying 75 bitcoins (which was about $4.4 million at that time) to get back control of their systems. This shows how hard the choices can be when important stuff is at risk.
Concern About Being Assumed to Support Terrorist Organizations and Cyber Gangs
The U.S. Treasury’s Office of Foreign Assets Control (OFAC) has warned that if you pay a ransom to a group that is on their sanctions list, you could end up facing big fines. So, there is a legal risk too.
Walking on the Edge of a Sword: The Reality of Ransomware Negotiation
A lot of people, and rightfully so, are scared to pay the ransom. They really need their data back to keep their work going, but it is not a simple decision.
First, paying does not guarantee you will get your data back, and it does not mean the criminals will not release your data anyway.
Second, legally, you could be blamed in the future for giving money to terrorists or criminal groups.
And third, believe it or not, the ransomware criminals are usually in a hurry. They have a lot of victims and want to close deals quickly. So, they need your money as much as you need your data. This is why we now have something called Ransomware Negotiation – it is a new kind of business.
Signal Flare of New Fashion: Doing Things Under the Rose, Proxy Data Recovery Companies
Before knocking doors of the cyber gangs, victims first look for how they can recover their data, legit companies they can get help from. To be honest, knocking on the doors of the gang is always the last option, many times instead of legal concerns, first no one wants to pay huge amounts of money as ransom. According to a report from South Korea media, apparently a legit data recovery company conspired with North Korean threat actors while “recovering” data.
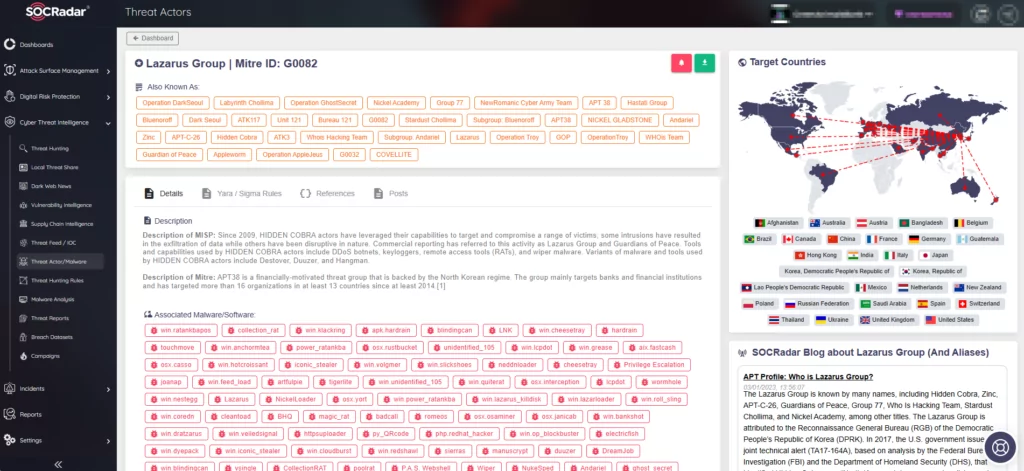
The company is using Google Ads to promote itself as a trusted data recovery company, whereas under the hood they had collaboration with North Korean Lazarus Group according to reporter Kim Jeong-beom from Maekyung.com. The group, Lazarus, is not famous just for their advanced techniques, they are also known for their attractive ways to attract new talents and allies. They also use some tricks to get information, like publishing job classifieds to lure possible candidates who work or have knowledge/experience in the targeted industry/organization. After the police operation to the alleged company, police captured many messages sent through Telegram between the alleged company and threat actors, which is Lazarus according to report.
In a world where every bit counts, threat actors can adopt this approach widely through proxy companies or new kinds of data recovery company looking affiliates. Maybe in the coming days we will see 90s urban stories about anti viruses developed by virus writers come to life as reality.
Cyber gangs would likely find this approach particularly advantageous. They can remain under the radar until the moment someone traces the virus back to their operations. Meanwhile, they can maintain their reputation for swift data recovery, disguising their methods as confidential company secrets or proprietary software, in line with trade laws.



































