
Dark Web Profile: Haghjoyan
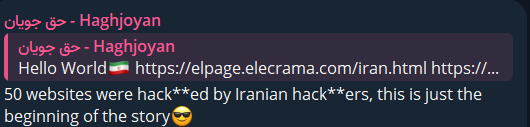
The Haghjoyan hacker group, self-identifying as the Iranian cyber army, emerged at the forefront of cyber warfare during the Israel-Hamas conflict. Their presence, prominently appearing on their Telegram channel, distinguishes them as one of the few groups openly declaring Iranian affiliation. This declaration is significant, as it sets Haghjoyan apart from many possible nation-sponsored or endorsed groups that often operate in secrecy.

With fluctuating 25,000 followers on Telegram, yet having previously surpassed 40,000 subscribers, Haghjoyan demonstrates a determined effort to maintain its online presence amidst potential bans and restrictions.
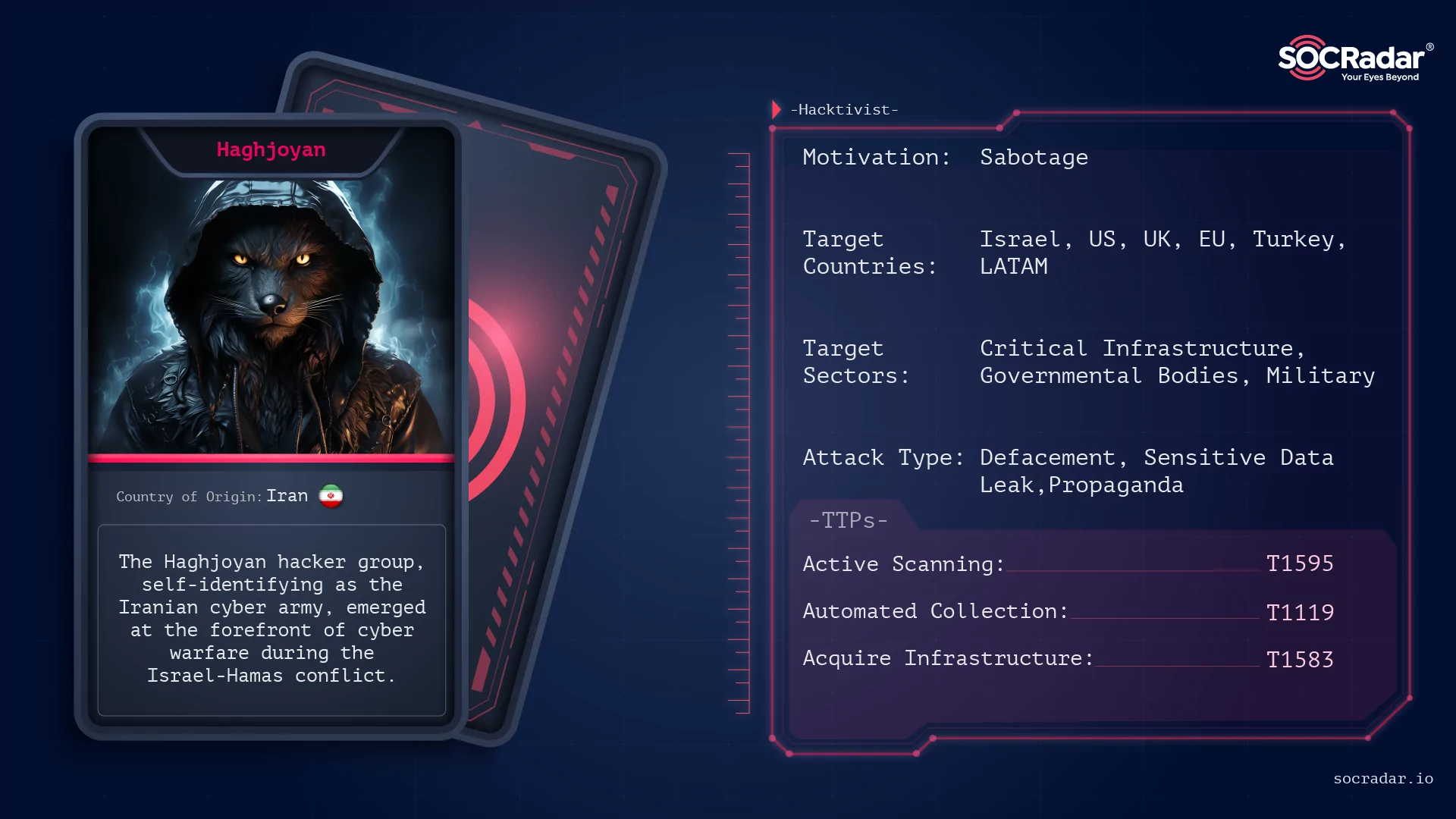
Threat Actor Card of Haghhoyan
Background and Origins of Haghjoyan
The Haghjoyan group emerged during the intense period of the Israel-Hamas conflict, marking a new entrant in cyber warfare. This group, proclaiming themselves as “Iran’s cyber army,” set a distinctive tone from the outset, openly associating themselves with Iran. This explicit declaration of their national affiliation is a notable divergence from the typical anonymity maintained by many cyber warfare groups.
Haghjoyan’s early activities were primarily focused on Israel, aligning with the broader conflict narrative. Their presence on Telegram, a platform often used by such groups for communication and propaganda, has been dynamic, with their follower count varying significantly over time. This fluctuation, combined with efforts to circumvent platform bans, indicates a dedicated attempt to sustain their influence and reach.
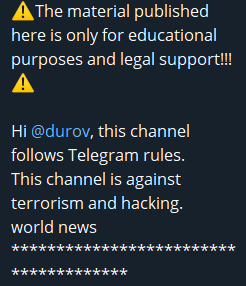
The group, which did not want to lose its Telegram channels again, claims that it is for educational purposes and shares “world news.”
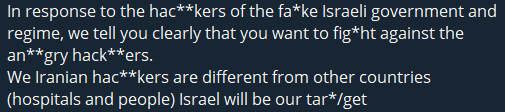
However, what they do brighter than mockup channel info is a logical solution to both avoid ban hammer and prevent automatic scrapes. They write words such as hacker, fake, target, and fight by censoring them.
The group’s self-identification and evolving online strategy provide insight into their motivations and objectives in the cyber domain, setting the stage for their subsequent operations and tactics.
Haghjoyan’s Modus Operandi
Haghjoyan’s cyber operations are characterized by a diverse array of tactics, primarily focusing on data leaks, defacement attacks, and propaganda. Their activities showcase a blend of cyber warfare techniques aimed at causing disruption and spreading their message.
Data Leaks and Sales
Haghjoyan is known for leaking sensitive data, including information related to U.S. military personnel, which they offer for sale in exchange for Bitcoin. This approach of monetizing stolen data indicates a sophisticated understanding of the cybercrime ecosystem.
Even though they think they are doing the right and just actions, they do not hesitate to sell data in exchange for money.
Defacement Attacks
The group frequently engages in website defacements, a tactic that serves both as a means of disruption and a tool for propaganda. These defacements often carry messages aligning with their political stance. Their first attack was on various websites, which we also stated in our reflections blog.
Geopolitical Alignment
Haghjoyan’s activities and public statements suggest sympathy towards Russia, mirroring Iran’s current political discourse. This geopolitical alignment hints at potential future collaborations with Russian groups targeting Israel and the US.
Propaganda Efforts
They use their cyberattacks and public channels like Telegram for propaganda purposes, reinforcing their political messages and objectives.
The operations of Haghjoyan, spanning various cyber tactics, reflect a multi-faceted approach to cyber warfare, intertwined with the broader geopolitical tensions involving Iran, Israel, and the United States.
Notable Attacks of Haghjoyan
The Haghjoyan hacker group has claimed responsibility for a series of significant cyberattacks, underscoring their capabilities and objectives:
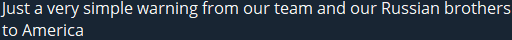
Israeli Red Alert Emergency Response System: In one of their first notable attacks, Haghjoyan claimed to have targeted the Israeli Red Alert Emergency Response system, demonstrating their focus on critical communication infrastructures.
VNC Systems and Infrastructure Attacks: The group also claimed to have attacked several VNC systems controlling Israeli water pumps, electricity distribution units, and gas stations just like other alleged Iranian groups. This highlights their ability to target and potentially disrupt essential services and infrastructure.
Data Exfiltration and Malware Deployment: Haghjoyan claimed to have infected over 5,000 Israeli computer users with malware and exfiltrated over 2 TB of data, indicating their possible proficiency in sophisticated cyber espionage and data theft operations.
Surveillance Camera Systems: The group also targeted a significant number of cameras and DVR systems, primarily from Hikvision, showcasing their ability to infiltrate and potentially manipulate surveillance systems.
These attacks by Haghjoyan illustrate a strategic approach to cyber warfare, targeting systems that have a direct impact on national security and public safety, and aligning with their broader geopolitical motives.
Political Alignment and Intentions
The Haghjoyan hacker group’s activities and public communications clearly reflect their political alignments and intentions:
The group’s self-identification as Iranian and their focus on targeting Israeli infrastructure strongly align with Iranian geopolitical interests. This alignment is significant in the context of the ongoing regional conflicts and cyber warfare scenarios.
Additionally, Haghjoyan shows a marked sympathy towards Russia, echoing Iran’s political stance. This inclination indicates potential ideological alignments and possibly future collaborations with Russian groups that share similar targets, notably Israel and the U.S.
Haghjoyan effectively uses their cyberattacks and public statements for propaganda purposes. Their operations and the messaging disseminated via platforms like Telegram are geared towards advancing specific political narratives and objectives, which are critical to understanding their cyber operations and the impact thereof.
There is also an indication of potential affiliations or coordination with other hacker groups. These affiliations are likely with groups that share similar geopolitical views or targets, pointing to a broader network of cyber warfare actors working in concert or at least with shared objectives.
In essence, understanding Haghjoyan’s political alignment and intentions is crucial for comprehending the context and motives behind their cyber activities, as these factors heavily influence their choice of targets and the nature of their operations.
Community and Influence
The Haghjoyan hacker group’s approach to using their Telegram channels is quite distinctive and merits a separate discussion:
Their Telegram channel’s follower count has shown significant fluctuations, indicating active engagement with a broad audience. Despite the closure of their channels at times, they have demonstrated a capability to quickly regain a high number of followers. This resilience in maintaining their digital presence, even in the face of potential platform bans, is noteworthy.
Their community engagement and the growth of their follower base, at times exceeding 40,000, reflect their substantial reach and influence within the cyber community. These fluctuations in follower numbers might point to the group’s increasing prominence as well as the transient nature of digital platforms for such groups.
However, usage of follower bots is also possible since it has reached 40.000 followers within their few attacks.
Haghjoyan’s consistent efforts to evade platform restrictions and continue their operations on platforms like Telegram highlight their adaptability and dedication to spreading their message and propaganda.
In their online activities and claims, the group has been actively trying to shape public perception and discourse, particularly regarding the Israel-Hamas conflict and the broader geopolitical tensions involving Iran. This indicates their intent to influence public opinion and narrative through their digital presence.
In summary, Haghjoyan’s community and influence in the digital landscape demonstrate their strategic use of digital platforms to further their objectives and maintain relevance in the domain of cyber warfare.
Conclusion
The Haghjoyan hacker group represents a distinct and influential force in the landscape of cyber warfare. As a self-proclaimed Iranian cyber army, their operations extend beyond mere hacking activities; they are intertwined with the geopolitical conflict between Iran and Israel, and more recently, their focus has expanded to include the United States and India.
Their tactics, ranging from data leaks to propaganda, demonstrate not only technical expertise but also a strategic approach to cyber warfare. This is further emphasized by their ability to maintain a resilient online presence, particularly on Telegram, despite the challenges of platform restrictions. The fluctuating follower count on their Telegram channel indicates a dynamic engagement with the cyber community, reflecting their impact and reach.
Moreover, their political alignment and intentions, especially their expressed sympathy towards Russia and potential affiliations with other hacker groups, hint at a broader network of cyber warfare actors with shared objectives. This alignment not only aligns with Iran’s current political discourse but also opens possibilities for future collaborations in the cyber domain.
In summary, understanding the Haghjoyan hacker group’s operations, motivations, and influence is crucial in the context of global cybersecurity. Their activities underscore the increasingly complex nature of cyber warfare, where state-sponsored and ideologically driven hacker groups play a pivotal role in shaping geopolitical dynamics.
For a comprehensive understanding of the Haghjoyan hacker group and their impact, it is crucial to follow their activities and have a proactive security stance especially for US and Israeli companies and organizations.
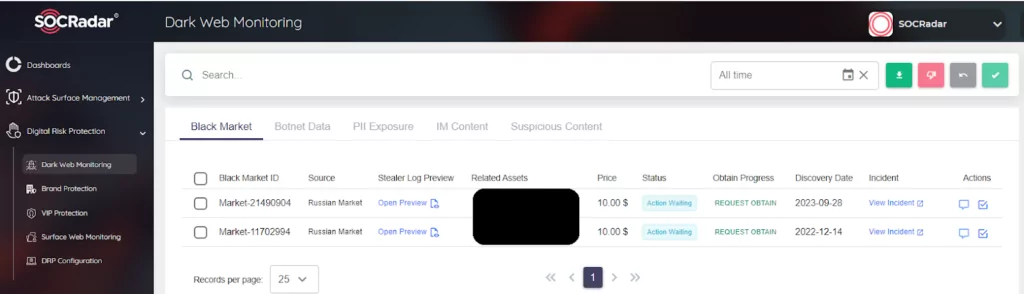
For this capability, SOCRadar Dark Web Monitoring and Dark Web News are example solutions.
MITRE ATT&CK Tactic Table of Haghjoyan
| MITRE ATT&CK Tactic | MITRE ATT&CK Technique | Description |
| TA0043: Reconnaissance | T1595: Active Scanning | Haghjoyan likely conducts scanning to identify vulnerable systems, especially those with exposed RDP ports. |
| TA0005: Defense Evasion | T1070: Indicator Removal on Host | The group may employ techniques to remove traces of their presence in compromised systems. |
| TA0009: Collection | T1119: Automated Collection | Haghjoyan’s data exfiltration efforts suggest automated collection of sensitive information. |
| TA0040: Impact | T1485: Data Destruction | Their attacks, particularly malware deployment, could lead to data destruction or manipulation. |
| TA0006: Credential Access | T1110: Brute Force | They may use brute force attacks to gain unauthorized access, especially in cases of weak or default credentials. |
| TA0042: Resource Development | T1583: Acquire Infrastructure | Haghjoyan might acquire and use specific infrastructure to support their cyber operations. |




































