| #OpIsrael | #4-EXPLOITATION | #BlackPirateTeam |
| #FckIsrael | #StucxnetCrewMalaysia | #hacktivisindonesia |
| #FreePalestine | #SynixCyberCrimeMy | #EthiopianAnonymous |
| #StopKillingMuslim | #AnonymousMalaysia | #GhostClanOfficial |
| #AnonGhostOfficial | #TeamInsanePK | #TYGTeam |
| #AnonymousSudan | #MinionsCyberCrime | #1915Team |
| #CyberJEArmy | #TeamCordozoDz | #KEPTeam |
| #HacktivistIndonesia | #VMзы47CyberCrew | #1919Team |
| #AllMuslimHackersTeam | #NinjaCrewCyberGhost | #JambiCyberTeam |
| #pejuangcybermuslimn | #UndergroundGhostCrew | #CyberArmyVN |
| #MysteriousTeamBangladesh | #DarkHCyberXArmy | #AllMuslimHackers |
| #EagleCyberCrew | #DarkCyberXPravasiArmy | #BoycottIsrael |
| #eaglecyberwashere | #BangladeshMuslimHackers |
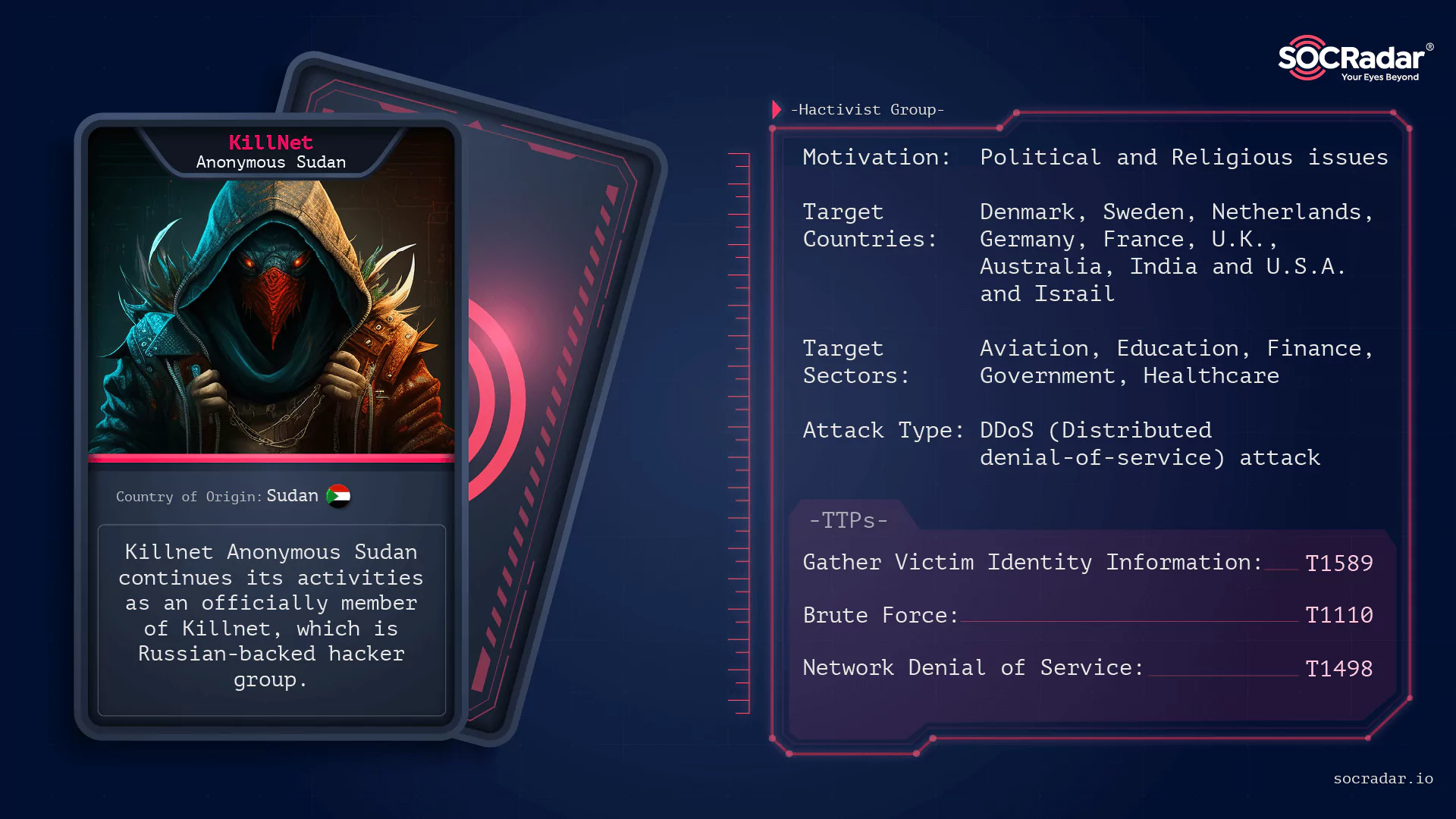

Dark Web Profile: KillNet Anonymous Sudan
[Update] October 17, 2024: “Indictment of Two Sudanese Nationals Behind Anonymous Sudan”
[Update] July 5, 2023: In a recent cyber attack, Anonymous Sudan claimed to have targeted the login portal of Riot Games Inc. Added under the subheading: “Recent Cyber Activities: Microsoft Hacking, UAE-Israel Alliance, and Targeted Attacks.”
[Update] July 4, 2023: Microsoft has denied the claims by “Anonymous Sudan” that they breached the company’s servers and stole credentials for 30 million customer accounts. Microsoft spokesperson stated that their analysis shows no evidence of a data breach or compromise. Added under the subheading: “Recent Cyber Activities: Microsoft Hacking, UAE-Israel Alliance, and Targeted Attacks.”
[Update] July 3, 2023: Anonymous Sudan’s recent cyber activities include an alleged Microsoft hack, claims of a UAE-Israel cyber alliance, and various targeted attacks. Added the subheading: “Recent Cyber Activities: Microsoft Hacking, UAE-Israel Alliance, and Targeted Attacks.”
While Anonymous is a decentralized, anti-political cyber hacktivist movement, and typically anyone can claim to work under the Anonymous banner, groups like Anonymous Russia are not aligned with mainstream and western-based Anonymous groups and support the Russian invasion of Ukraine and target those who support Ukraine. Likewise, KillNet Affiliated Anonymous Sudan is a group of seemingly religiously and politically motivated hackers from Sudan, also located outside the mainstream, who have been conducting DDoS attacks against several countries and organizations’ critical infrastructure, such as Sweden and Denmark, since January 23, 2023.
Original Anonymous Sudan emerged in Sudan in response to the country’s ongoing political and economic challenges. It is also known for its use of digital activism, which includes hacking and DDoS attacks on governments to draw attention to censorship and restriction on free speech. Moreover, they have been involved in the campaign due to being insufficiently democratic and representing the people’s interests against the current Sudanese government. Unlike the newer Anonymous Sudan, it is also known that they were involved in anti-Russia and pro-Ukraine ops with Ghostsec as a member of OpSudan hacktivism.
Origins of the KillNet Anonymous Sudan
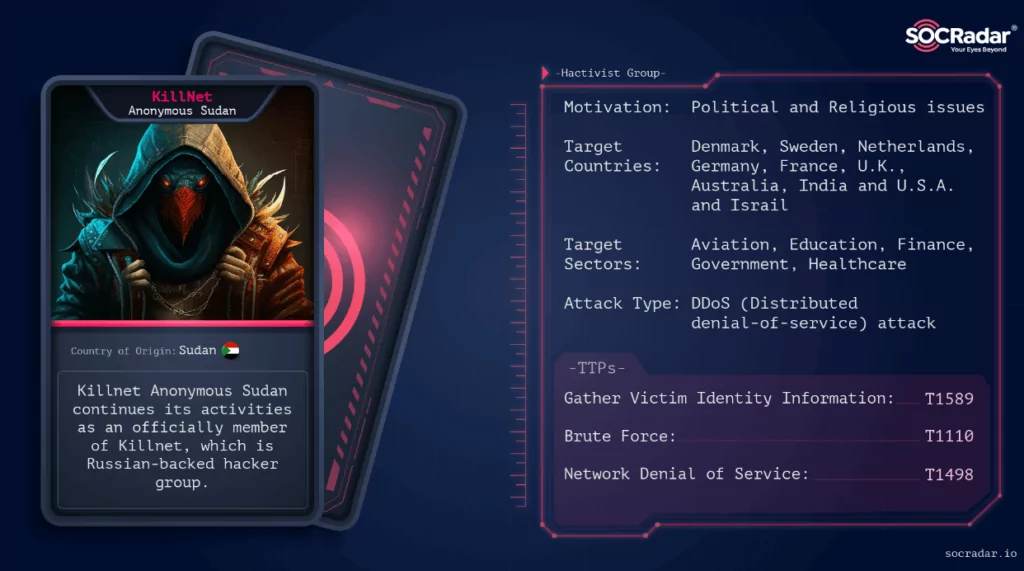
Killnet Anonymous Sudan is a hacker group based in Sudan that claims to engage in cyberactivism and hacking activities. The group is believed to be part of the larger Anonymous network, which is an international group of hacktivists known for their #OP activities (#OPIsrael, #OPAustralia, etc.). The #OP activities are usually related to a specific cause and date on which the group executes its attacks. They claimed responsibility for most DDoS attacks targeting several European countries; according to the SOCRadar Research findings, their attacks started with Sweden and Denmark and continued with organizations of Germany, France, the U.K., Australia, Israel, and India.
They put forward a far-right activist, Rasmus Paludan, who holds both Danish and Swedish citizenship, as the source of their cyber reactions. Paludan burned a copy of the Quran in Sweden on January 21, 2023, and vowed to continue burning the Muslim holy book in Denmark until Sweden is admitted into NATO.
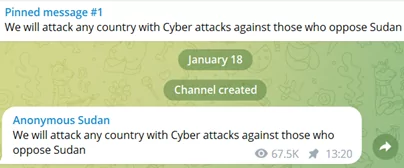
The Anonymous Sudan Telegram channel was established on January 18, 2023, and it was announced that they would attack those who target Sudan. Rasmus Paludan burned a copy of the Quran in Sweden on January 21, 2023; then, on January 23, they announced that some Swedish sites would be attacked.
This group is known for conducting various types of cyberattacks, including DDoS and defacement attacks, and claiming responsibility for their attacks through public statements and Telegrams posts. Apparently, their motivation and purpose are to raise Sudanese people’s voices and awareness about especially religious issues.
Main Characteristics of Anonymous Sudan
Several indicators point out that the new “Anonymous Sudan” has nothing to do with the original Anonymous Sudan or the other Anonymous collective. The characteristic features that distinguish it from other anonymous groups are listed below.
1- They do not use hashtags such as #OPSweden in its campaigns, as other anonymous groups do, except for the recent #OpIsrail campaign; the group is only active in Telegram, and does not use social media power like Twitter and does not seek the support of other pro-Islamic groups.
2- There is no link in its campaigns on political issues related to Sudan.
3- They only interact with Russian hackers and have no relationship with other Islamic groups. In most operations, it has been observed that they support Russian hacktivism with tags such as #infinity #killnet #anonymousrussia.
4- They use the site check-host[.]net, which is website monitoring and checking the availability of hosts to check the status of attacked websites, the same as the other Russian hacktivist groups, especially Killnet.
5- The group insistently claims that “Sudanese Hackers support Russian Hackers for their support of Sudan earlier.”
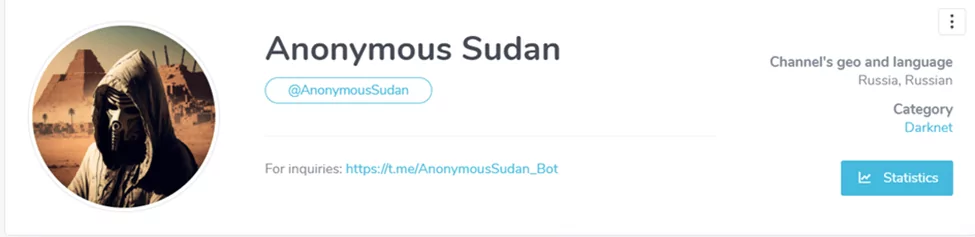
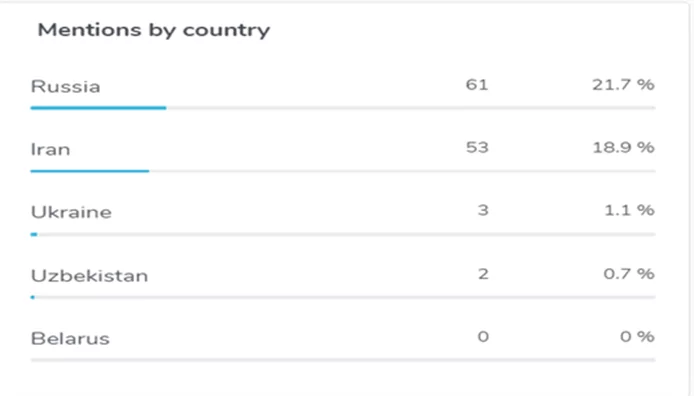
6- Most posts are in English and Russian, and just a few are in Arabic. Russia and Iran are in the first rank in the order of mention by countries. The user location for the Telegram channel is listed as Russia.
7- On January 11, 2023, before Anonymous Sudan was registered on Telegram, a representative for “usersec,” known as the pro-Russian group, referred to bringing a new group that was “multicultural” and “real pros.” Then the same group posted on January 15, 2023, “We are preparing something very large scale and cool” message.
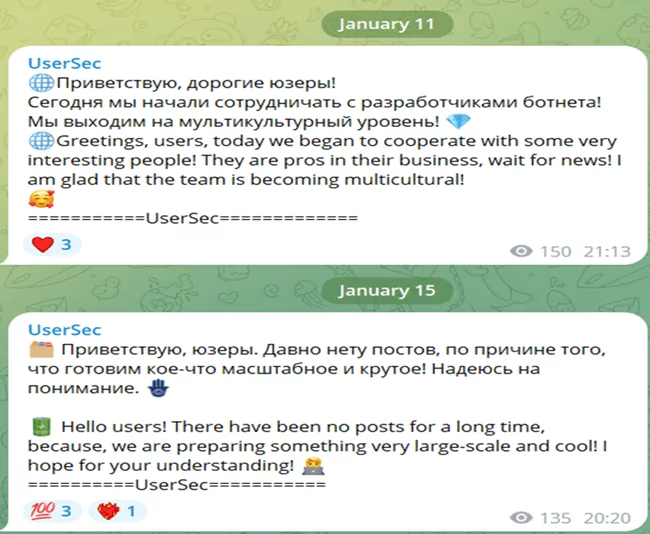
After that, the Anonymous Sudan Telegram channel was established on January 18, 2023, and it was announced that they would attack those who target Sudan.
Prominent Cyber Operations Conducted by KillNet Anonymous Sudan
Let’s evaluate the Anonymous Sudan operations by the time sequence, so we can see that some unclear points have been clarified. Therefore, you can follow the current activities of this group closely followed by the SOCRadar dark web team here.
Jun 26, 2023: www.digitaldubai.ae (“Dubai Now” is the unified application for government services in Dubai), www.bankfab.com (First Abu Dhabi Bank), and www.alarabiya.net (Al Arabiya is an Arab and international news television channel) were allegedly targeted by Anonymous Sudan.

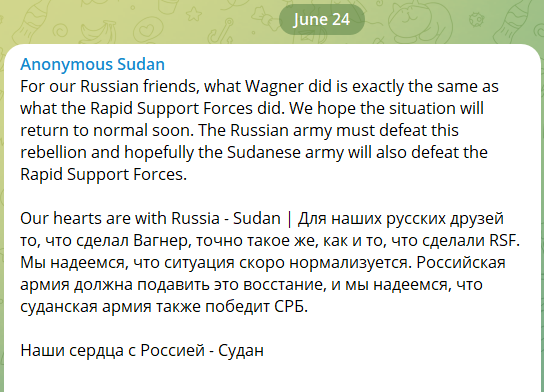
Jun 24, 2023: www.alhadath.net ( Al-Hadath” is an interactive Arabic news channel focusing on political events in the Arab region) and news.ua (latest news from Ukraine and the world. Politics, economics, technologies, cars, sports, and health) were allegedly targeted by Anonymous Sudan. At the same time, Anonymous Sudan published a message of support for the Russian army against the Wagner rebellion, stating that “hopefully, the Sudanese army will also defeat the Rapid Support Forces.”
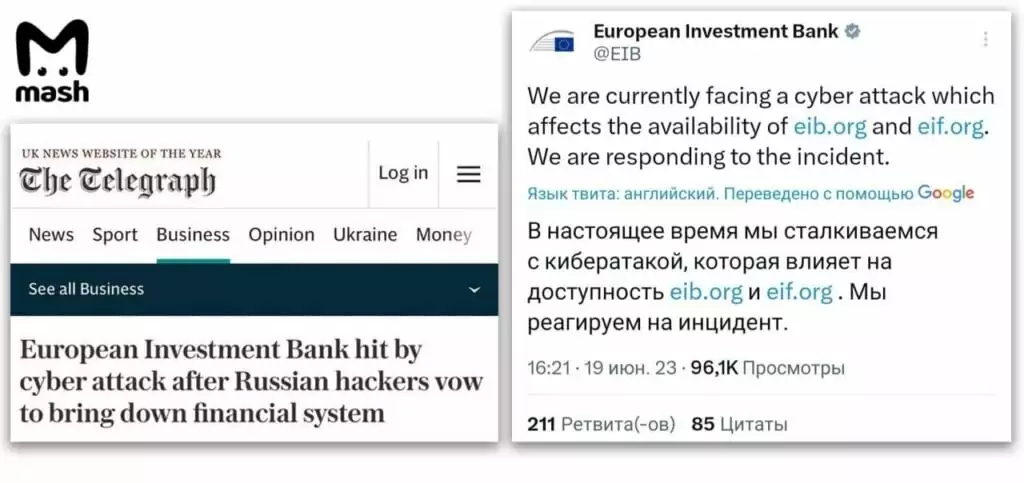
Jun 19, 2023: It was announced that European Investment banks were facing a DDoS attack affecting www.eib.org and www.eif.org websites by Anonymous Sudan.
Jun 18, 2023: US Department of Energy (www.energy.gov) was allegedly targeted by Anonymous Sudan via DDoS attacks.
Jun 14, 2023: The Darknet parliament, including Killnet, Anonymous Sudan, and Revil, released a video announcing that it would target the European financial system within 48 hours and it would paralyze the swift system. This announcement was also shared on the Anonymous Sudan telegram channel.

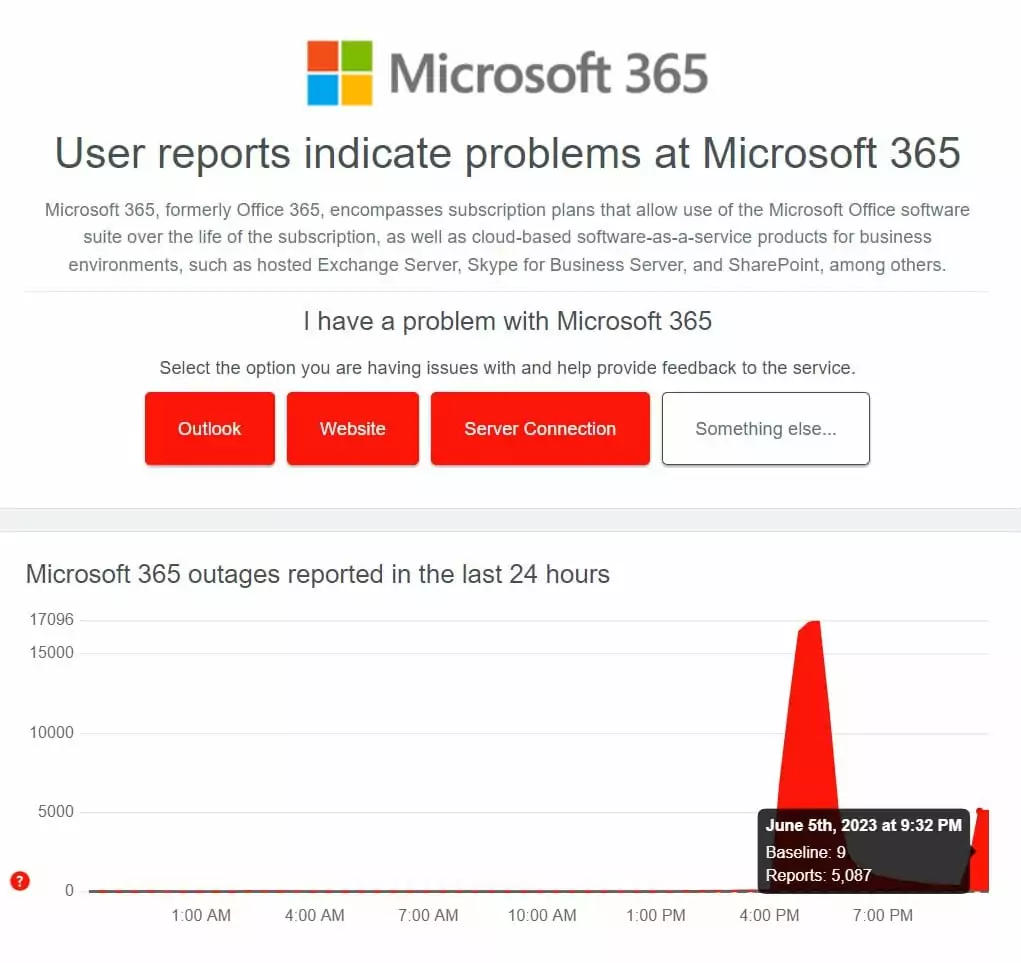
Jun 4, 2023: Microsoft has confirmed (June 18) that Layer 7 DDoS attacks against its services have recently caused outages on the Azure, Outlook, and OneDrive web portals. The attacker is reportedly Storm-1359, identified as Anonymous Sudan. It is understood that the attack chain appears to have started on 5 June and continued for nearly two weeks.
After the burning Quran incident, Anonymous Sudan chose the Swedish and Netherlands organizations as its primary targets.
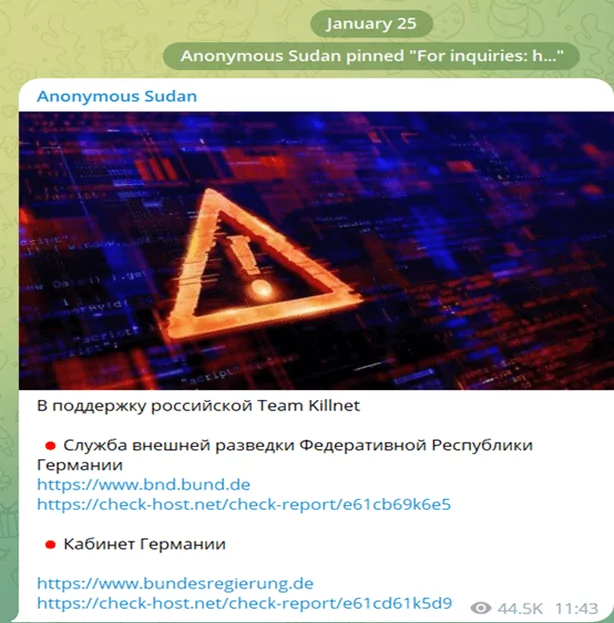
Shortly after the founding of Anonymous Sudan, the first Russian post with the message “Sudanese Hackers support Russian Hackers for their previous support to Sudan” and the first contact on January 25, 2023, resulted in the targeting of the Foreign Intelligence Service of the Federal Republic of Germany and then German airports.
A day later, on January 26, 2023, for the same reason, it was announced that PayPal infrastructure was targeted.

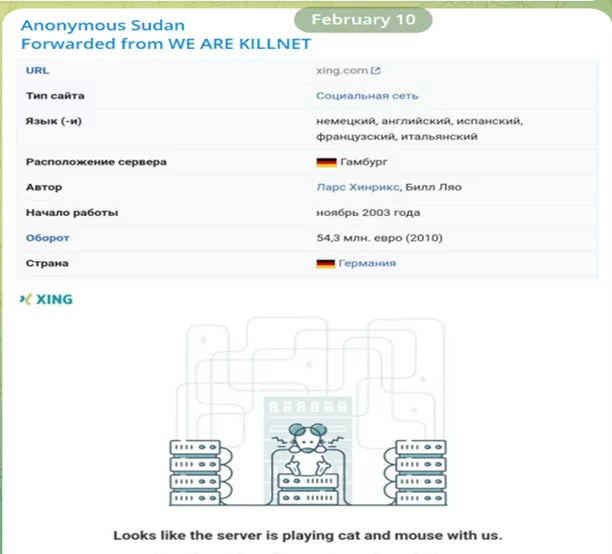
On February 10, 2023, they forwarded the KillNet Telegram post before declaring they were a member.
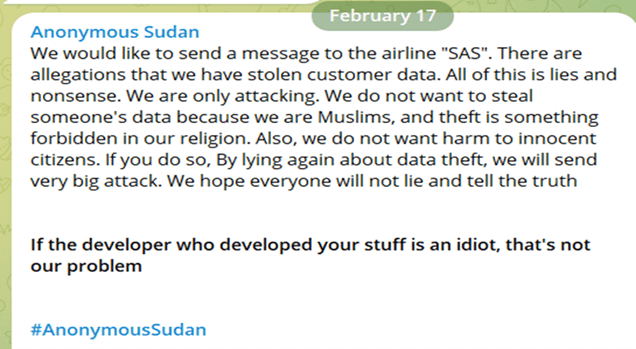
On February 17, 2023, they emphasized Islamic values and stated that they would not sell stolen customer data.
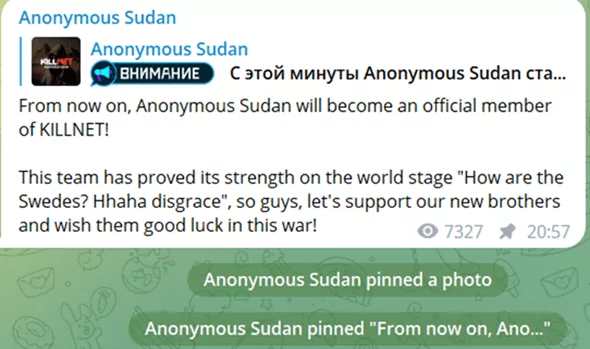
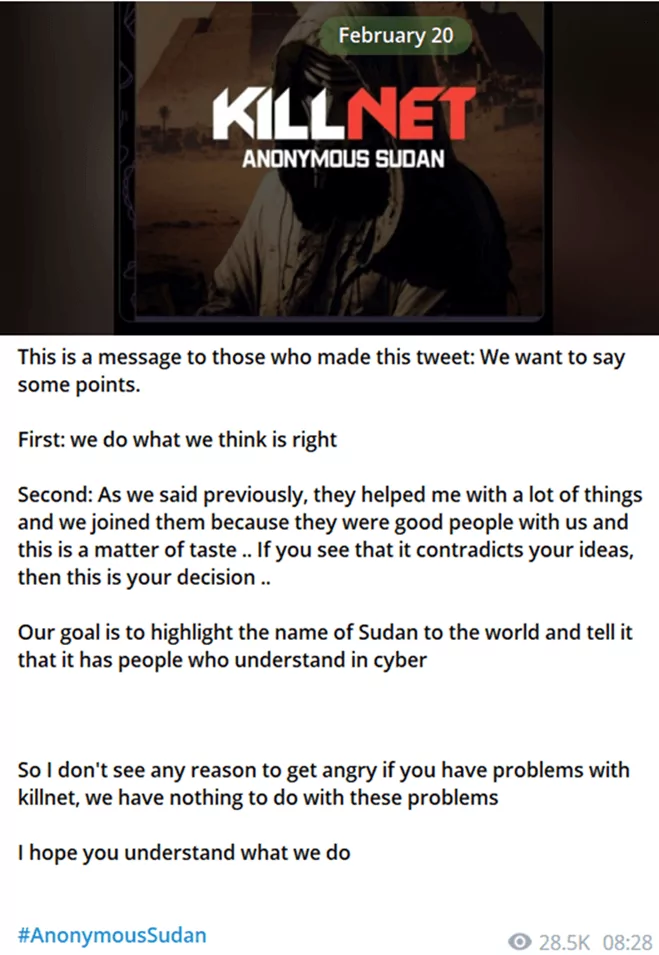
On February 19, 2023, they declared not to belong to Russia and had nothing to do with it. Their main objectives are protecting Sudanese people online and attacking anyone who opposes Islam. And repetitive statements for Russia “We help them because they helped us before, and this is a way to give back only!” One day after, on February 20, 2023, it was declared or was forced to announce that Anonymous Sudan had also become an official member.

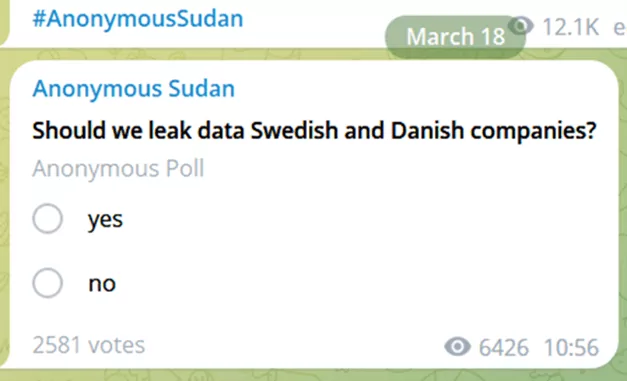
On March 18, 2023, a poll about leaking their data was published, and then PayPal data was leaked.
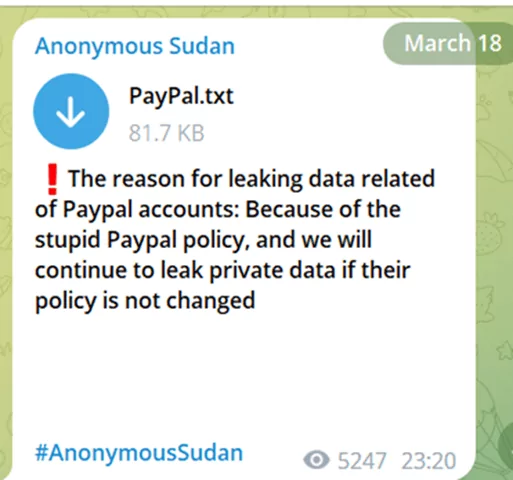
As of March 18, 2023, followed by Maerks, NASA, Air France Transavia, and Flying Blue data samples were leaked, respectively.
Moreover, on March 18, 2023, they claimed that the stolen data from Air France was put up for sale for $3000.

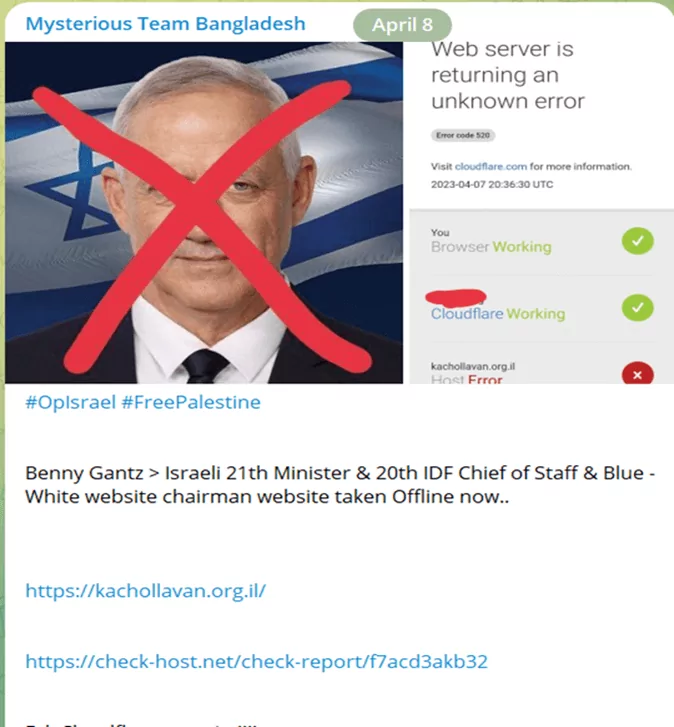
After this date, the UK, Australia, and Israel were threatened and attacked by Anonymous Sudan, respectively. Furthermore, they took part in the #OpIsrael movement with Islamic groups and attacked many state and private institutions in Israel, and were the subject of the news media. Analyses of the Israeli police raid on the Al-Aqsa Mosque and the subsequent developments will be examined under the #OPIsrael title.

OPIsrail Movement And Pro-Islamic Hacktivists
Early on April 5, 2023, an Israeli police raid on the Al-Aqsa Mosque in Jerusalem left at least 12 Palestinians injured during the Muslims’ holy month of Ramadan. At least 400 Palestinians were arrested and remain in Israeli custody, according to Palestinian officials.
This Israil’s operation, which caused outrage in Islamic circles, led to the gathering of Islamic-oriented hacker groups in cyberspace. As a result, the #OpIsrael hacktivist movement launched.
According to Islamic hacker groups, #OpIsrael is an urgent call for all Muslim hackers, human rights organizations, and activists worldwide to unite again and start the campaign against Israel, share what is really going on there, and expose their hostile activity to the world.

Anonymous Sudan has continued its cyber attacks against Israel, including critical infrastructures, without slowing down. For instance, on April 27, 2023, after the announcement of a cyber attack targeting an electricity company, which is the national power provider, the power outages occurrence was accepted in several areas across the country by Israel Electric Corporation (IEC), but it was emphasized that the reason was malfunctioning in the power generation units.
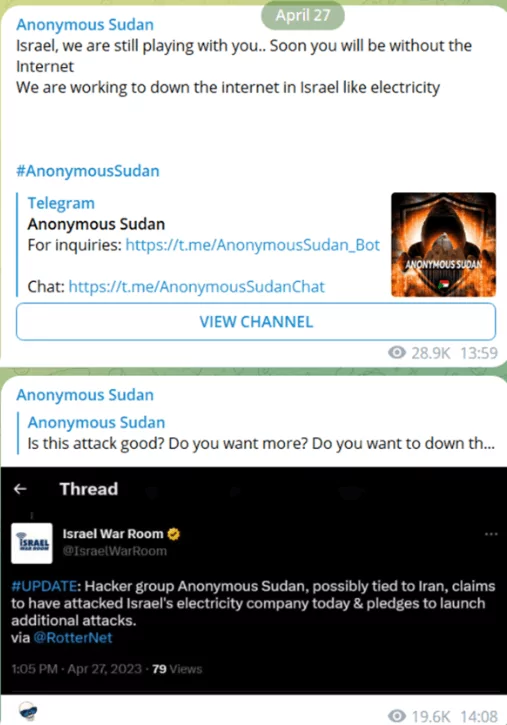
Furthermore, on May 03, 2023, Anonymous Sudan declared that cyber-attacks against Israel would continue after shutting down the electricity. They will also neutralize the missile defense system Iron Dome targeting Gaza and even cutting off the internet; thus, the attacks would continue in parts.

The Islamic groups supporting the movement and the hashtags shared via Telegram channels are listed below.
Since the beginning of the #OpIsrael movement, dozens of official and unofficial Israeli websites have been targeted, and a series of cyber incidents have taken place, ranging from denial-of-service attacks to leaks of personal and sensitive data.
DDoS Campaign in Response to U.S. Secretary of State’s Comments
On June 3, 2023, Anonymous Sudan initiated a new campaign targeting US organizations through a distributed denial-of-service (DDoS) attack.
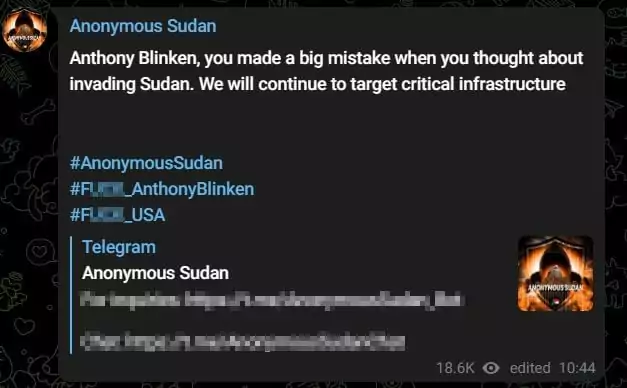
They were motivated by their displeasure with the comments made by the US Secretary of State, Anthony Blinken, regarding potential US involvement in Sudan.
The hacktivist group shared a message on their Telegram channel to express their intentions.
Recent Cyber Activities: Microsoft Hacking, UAE-Israel Alliance, and Targeted Attacks
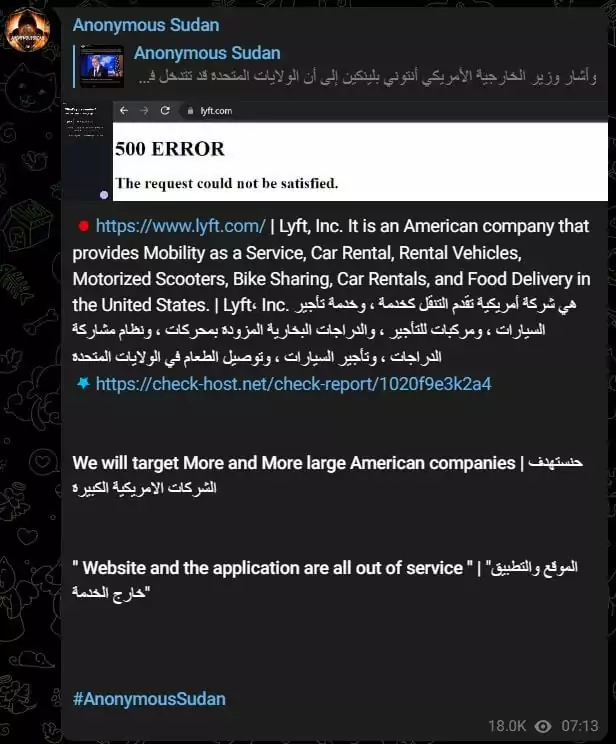
Anonymous Sudan has recently made waves with a series of incidents shared on their Telegram channel.
One notable claim involves the alleged hacking of Microsoft, with the group asserting that they have gained access to a substantial database containing more than 30 million Microsoft accounts, including email addresses and passwords.
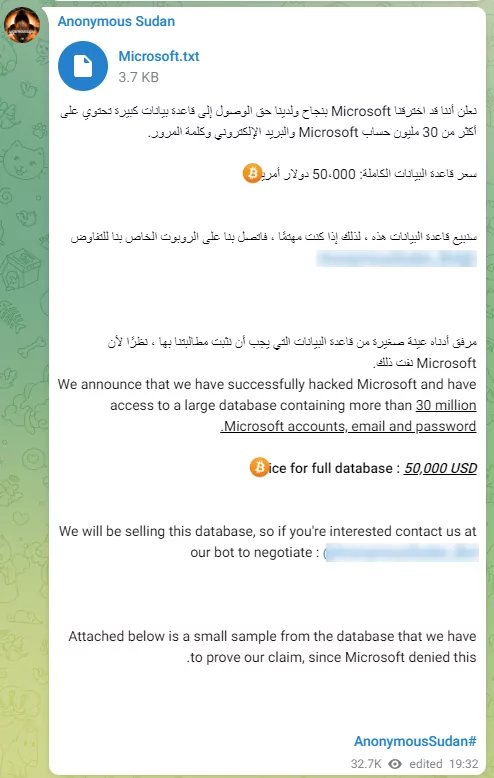
However, it is important to note that the accuracy of this claim has not been confirmed at this time. Following the investigation using the SOCRadar Threat Hunting platform, there are indications that hacking might not have occurred. Instead, it seems the alleged data could have been sourced from stolen credentials via steal logs and potentially offered for sale.
Now, Microsoft has denied the claims by “Anonymous Sudan” hacktivists that they breached the company’s servers and stole credentials for 30 million customer accounts. Microsoft spokesperson stated that their analysis shows no evidence of a data breach or compromise.
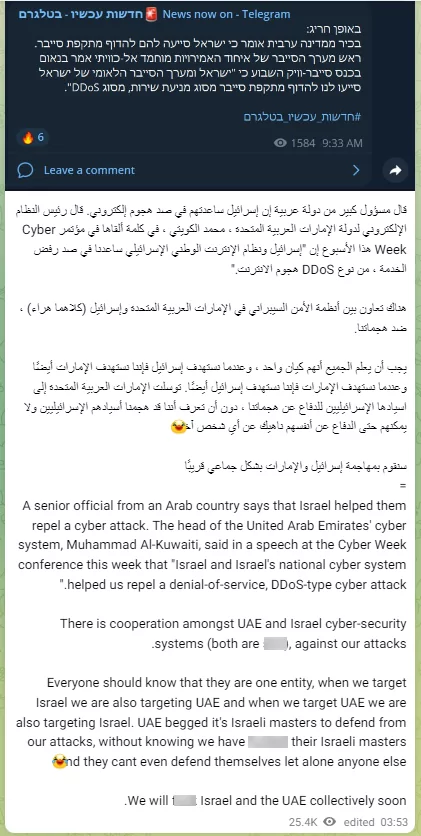
Additionally, Anonymous Sudan has highlighted instances of collaboration between the United Arab Emirates (UAE) and Israel, suggesting that Israel had assisted the UAE in repelling a cyber attack.
The group criticizes the efficacy of these systems, asserting that their attacks target both countries as a unified entity.
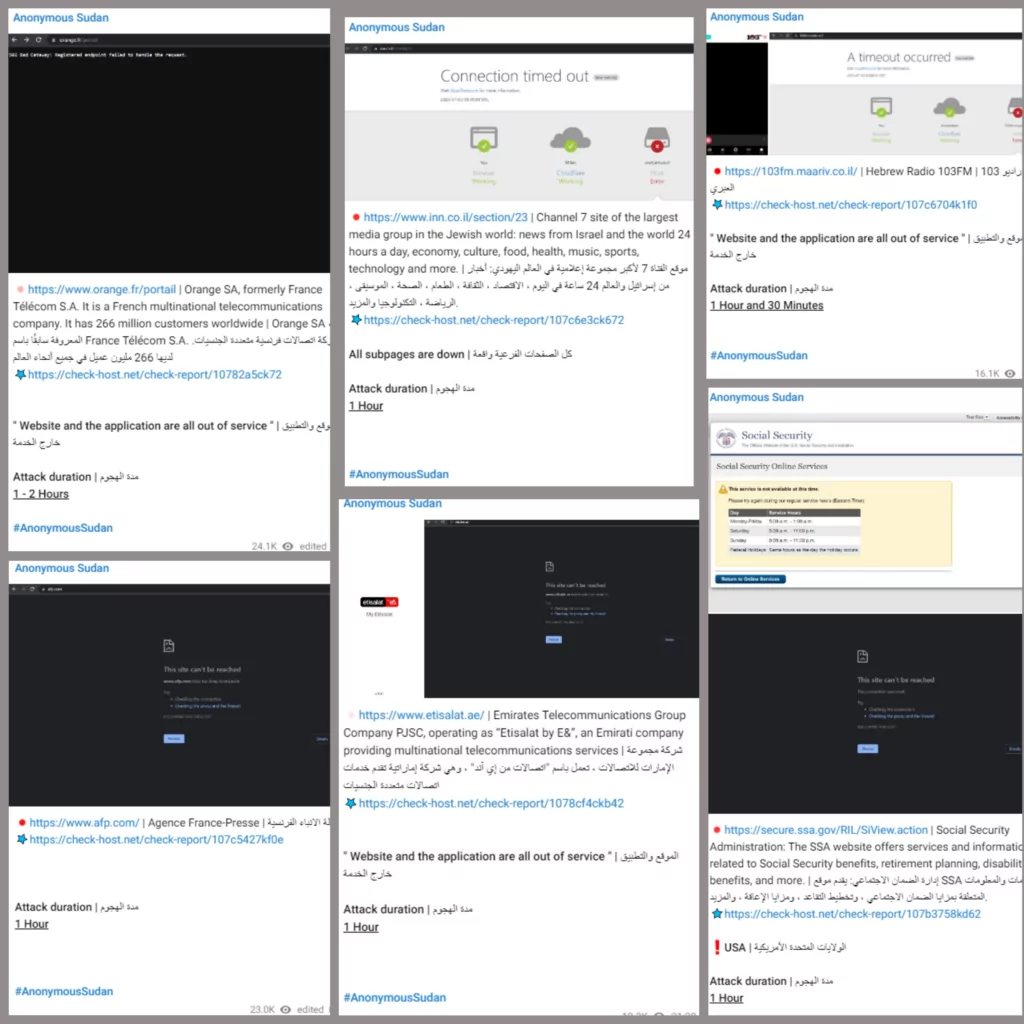
Furthermore, the group has carried out cyber attacks on various websites and applications, resulting in disruptions to services for organizations such as Channel 7, Hebrew Radio 103FM, Agence France-Presse, the Social Security Administration in the USA, Emirates Telecommunications Group Company PJSC (Etisalat), and Orange SA (formerly France Télécom). The duration of these attacks varied, with the longest lasting for one to two hours.
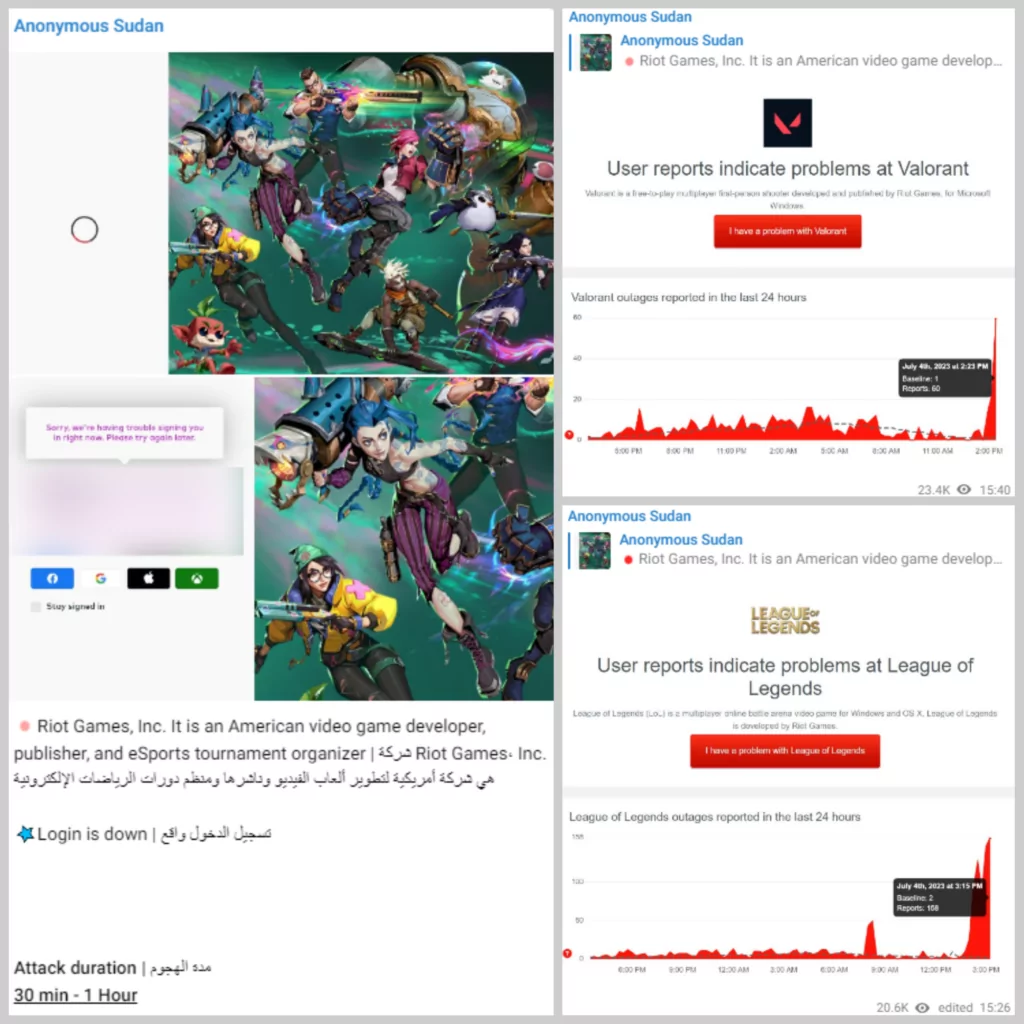
In a recent cyber attack, Anonymous Sudan claimed to have targeted the login portal of Riot Games Inc. Riot Games, Inc. is a prominent American video game developer, publisher, and eSports tournament organizer, widely recognized for its popular games such as Valorant and League of Legends.
During the attack, which lasted for approximately 30 minutes to 1 hour, users reported experiencing difficulties accessing Riot Games’ two games: Valorant, a tactical hero shooter, and League of Legends, a multiplayer battle arena game.
Conclusions and Further Insights
There is ample evidence that Anonymous Sudan is one of the Russian-backed groups, apart from the recent #OPIsrael movement. In an interview with its leaders, it was realized that they speak fluent Arabic, indicating its members are not exclusively Russian and maybe it is cosmopolitan. The fact that the Quran burning incident is used as a pretext for attacking European countries, especially Sweden and Denmark, should not mean they act only on religious reflexes. When the events described above with timeline-based methodology and Killnet support are brought together, it is obvious that some formations are based on intelligence on the back side, which is used for manipulations.
Although some groups here seem to have come together around common interests, it is possible to interpret this as an effort to expand its own front by using Russia’s cyber power and potential, led by some cyber formations via characterizing European countries by Islamophobia.
In the case of the #OpIsrael movement, it is noticeable that other Islamic groups accept Anonymous Sudan as one of them and share their posts. It is normal for such groups operating underground to come together around a common goal and interest, but when we take a closer look at #OpIsrael, observations show how political and religious sensitivities can lead to great outrages. Also, it gives an important message to big states about respect for the sacred.
As long as the international tensions that concern the world, such as the Russian-Ukrainian crisis, where the division between hackers will continue underground, may cause different provocations and manipulations. Therefore, in addition to getting professional DDoS protection and mitigation services, organizations should be vigilant and take proactive measures to safeguard against cyberattacks. SOCRadar’s dark web team continues to provide proactive and predictive information by analyzing threat intelligence data and identifying potential dangers and threats through closely and constantly monitoring cyber threat actors. Moreover, SOCRadar DoS Resilience Service allows you to check your domain’s or subnet’s resilience against DoS attacks.
Indictment of Two Sudanese Nationals Behind Anonymous Sudan
In a significant turn of events, the U.S. Department of Justice has indicted two Sudanese nationals—Ahmed Salah Yousif Omer, 22, and Alaa Salah Yusuuf Omer, 27—believed to be behind the cyber operations of Anonymous Sudan. This action, taken under “Operation PowerOFF,” dismantled the group’s infrastructure, including their tools “Godzilla,” “Skynet,” and “InfraShutdown.”
Anonymous Sudan, previously speculated to be tied to Russian state interests due to their pro-Russian propaganda, has been confirmed as an independent, Sudan-based group unaffiliated with any government. Their activities caused over $10 million in damages through more than 35,000 DDoS attacks, targeting hospitals, schools, and corporations across 70 companies. The Omer brothers were taken into custody by the FBI, facing potentially severe penalties. Ahmed could face life imprisonment, while Alaa may serve up to five years.