
Dark Web Sales: Unauthorized Citrix Access, Credit Cards, and Student Documents
The SOCRadar Dark Web Team has been tirelessly monitoring the deep corners of the internet, and their efforts have unearthed several incidents that put various entities at risk.
In this blog post, we will explore four distinct incidents, each posing unique threats to different targets: Unauthorized Citrix access for an American software company, 1,100 Spanish credit cards for potential fraud, 800GB of Indian engineering students’ sensitive documents exposed, and a threat actor boasting about a DDoS attack on The London Metal Exchange. Keep reading for further information.
Find out if your data has been exposed.
Unauthorized Citrix Access Sale is Detected for an American Software Company
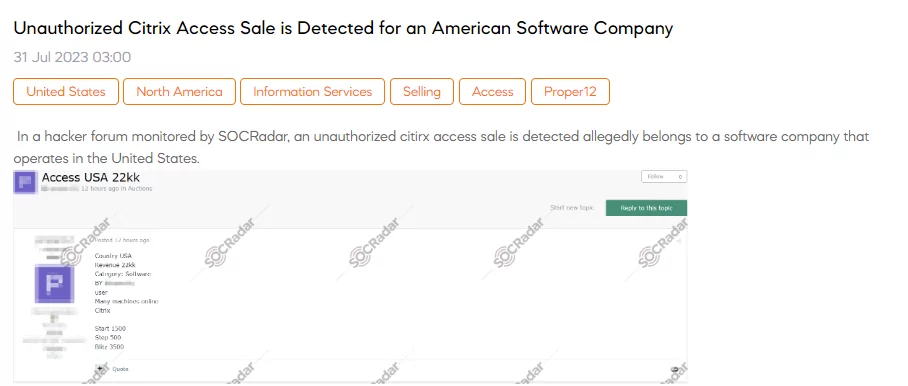
A SOCRadar Dark Web Analyst has detected a post that a threat actor claims to be selling unauthorized Citrix access allegedly belonging to a software company based in the United States. The post mentions that the sale includes access to multiple machines online through Citrix. The seller is offering this unauthorized access with a starting price of $1,500, with increments of $500 for each step, and blitz option for an instant buy priced at $3,500.
1100 Credit Cards Belonging to Spain are on Sale

The SOCRadar Dark Web Team has detected a concerning post in which a threat actor claims to be selling a new batch of credit card information allegedly belonging to Spain. The sale includes 1,100 credit cards with an estimated validity rate of 80-90% obtained through a sniffer. The information being sold for each credit card includes the CC number, expiration date, CVV (Card Verification Value), name, address, phone number, e-mail, date of birth (DoB), IP address, and User Agent (referring to string reveals the web browser or device used during the transaction). The price for this illegal sale starts at $3,850, with increments of $100, and a flash option for $5,500.
Documents of Indian Engineering Students are on Sale
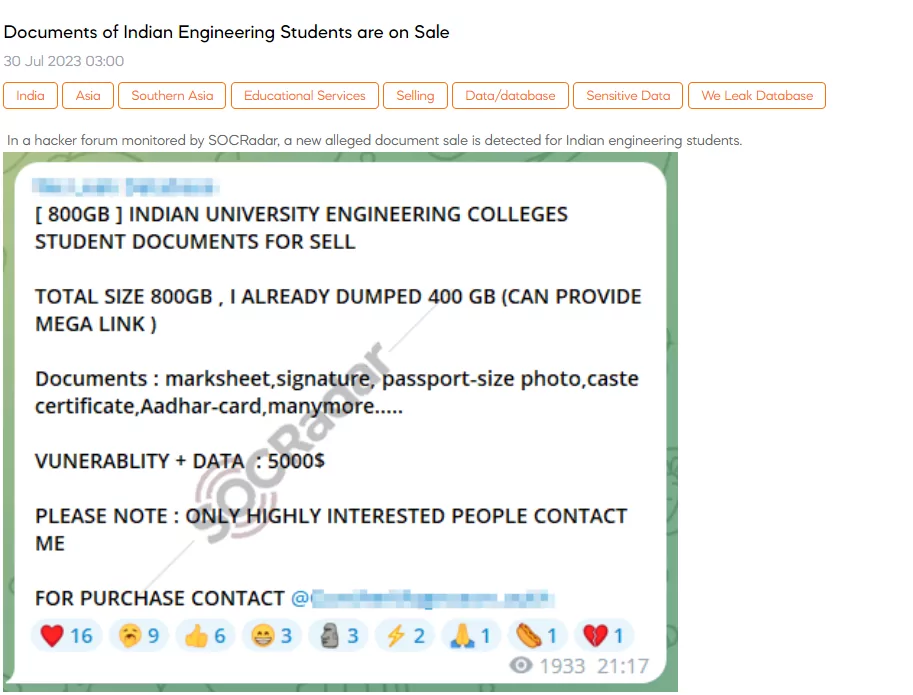
The SOCRadar Dark Web Team has identified a post where a threat actor claims to be selling a vast collection of documents belonging to Indian engineering students. The alleged sale includes a total of 800GB of data, with 400GB already made available through a provided Mega link. The documents being offered for sale encompass various sensitive information, such as marksheets, signatures, passport-size photos, caste certificates, Aadhar cards, and more. The threat actor mentions that the data is accompanied by a vulnerability report, with a combined price of $5,000.
Mobile Data of Qatar are on Sale
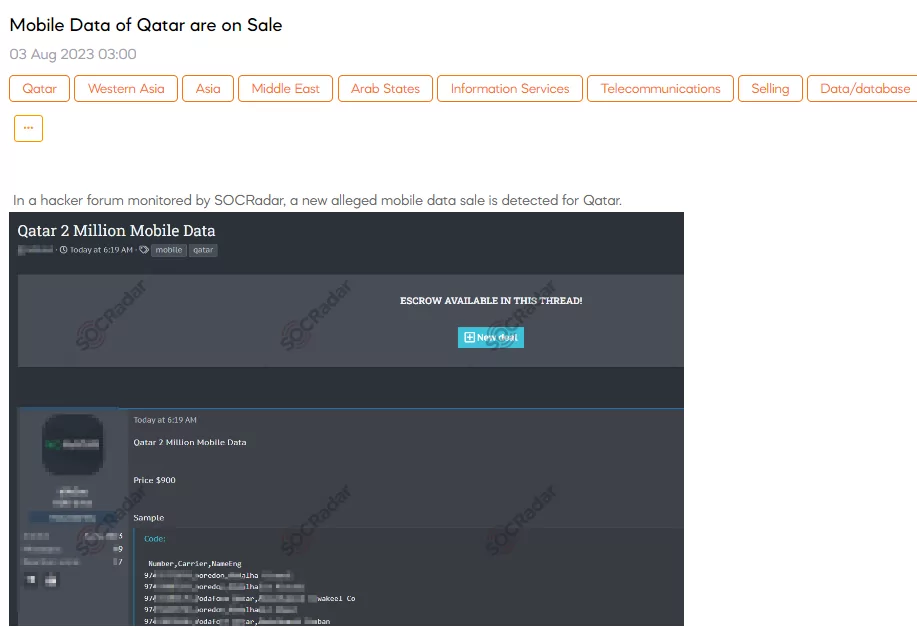
A SOCRadar researcher has detected a concerning post where a threat actor claims to be selling alleged mobile data for Qatar. The data being offered is said to include information from 2 million mobile users in Qatar. The price for this data sale is set at $900. The sample provided by the threat actor includes fields such as number, mobile operator, and name.
Hacking Announcement is Detected for The London Metal Exchange
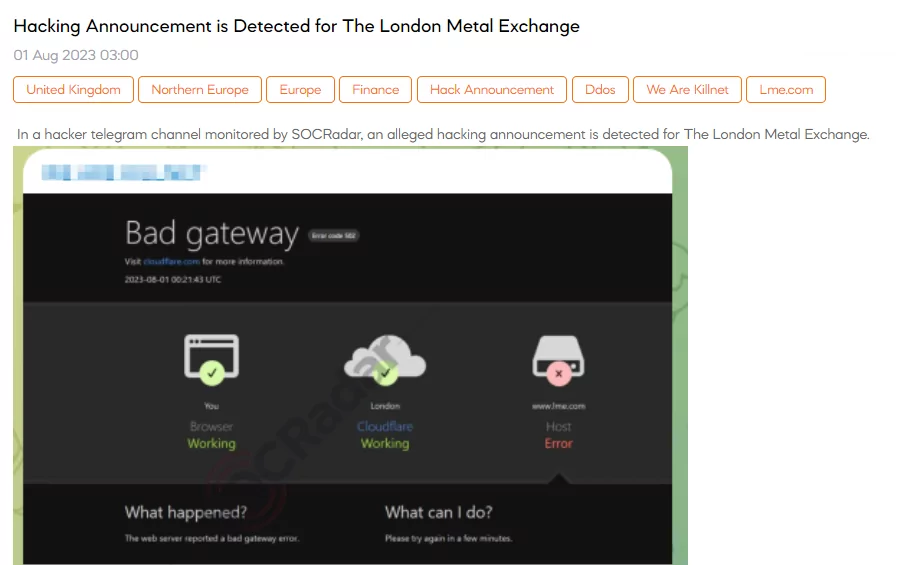
SOCRadar detected an announcement on a Telegram channel that a threat actor claims an alleged hacking attempt targeting The London Metal Exchange (LME) through a Distributed Denial of Service (DDoS) attack. The threat actor boasts about the potential cyber attack, belittling the security measures put in place by stating they can overpower the world’s leading security guards.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.



































