![SOCRadar® Cyber Intelligence Inc. | Deep Web Profile: AgainstTheWest / BlueHornet [Part 2]](https://socradar.io/wp-content/uploads/2022/04/deep-web-profile-againstthewest-bluehornet-part-2.png)
Deep Web Profile: AgainstTheWest / BlueHornet [Part 2]
As explained in the first part, the famous leak group AgainstTheWest/BlueHornet decided to shut their operations after their unsuccessful private forum attempt. Still, two significant incidents had crucial effects on their decision: the shutdown of RaidForums on the 25th of February and, most importantly, the Russian-Ukraine crisis starting on the 24th.
Part 2: The Aftermath of the Russian Ukraine Crisis
SOCRadar’s analysts think that a vast advertisement opportunity has risen as the world is focused on Russia and Ukraine could have made them abandon their decision to shut their operations. In addition, the fact that the shutdown of RaidForums has given them a new chance to become famous and reach new audiences on different platforms such as Telegram and Twitter could also have assisted them in their decision to continue.
Escaping RaidForums, Gave AgainstTheWest New Platforms To Reach New Audiences
After RaidForums had shut down, AgainstTheWest/BlueHornet did not wait long to carry their operations to new platforms. On the 26th of February, they opened their Telegram leak channel and announced that they would continue posting leaks of the companies they have leaked here.
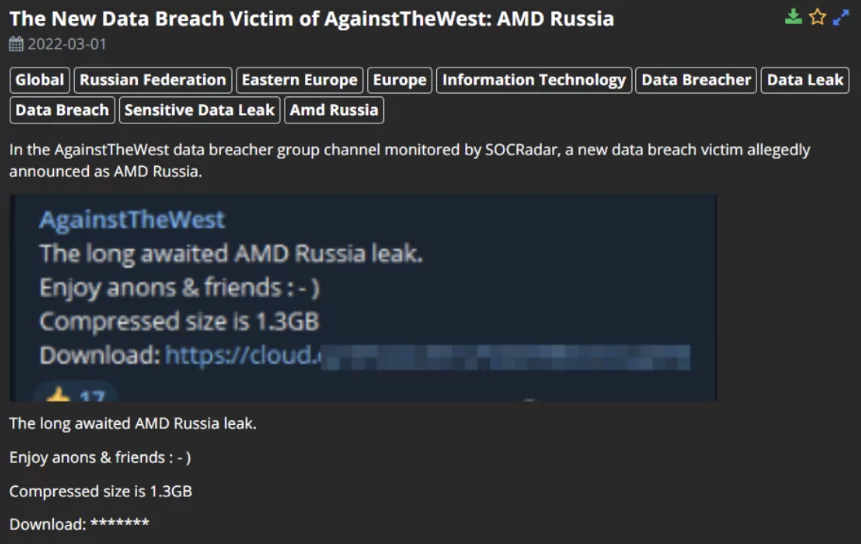
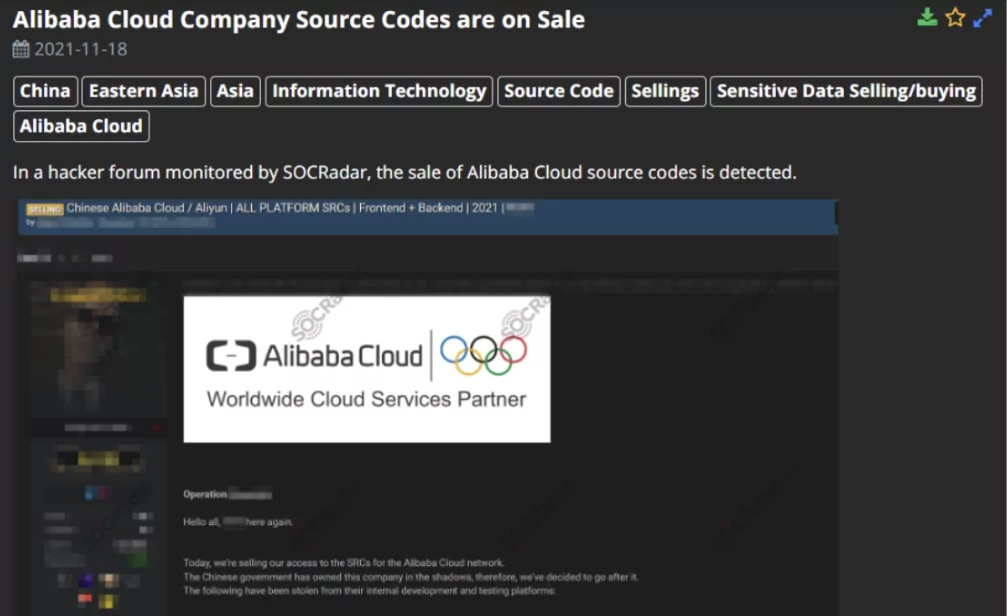
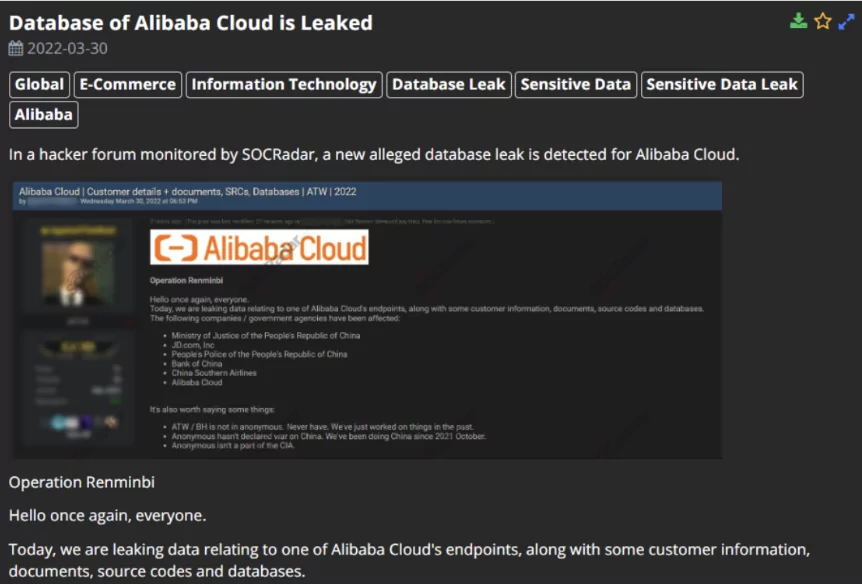
From now on, their primary focus of interest was Russian enterprises while occasionally leaking Chinese companies. SOCRadar has been monitoring multiple platforms AgainstTheWest/BlueHornet is actively using to share their leaks to bring you the latest news and updates about their victims. Below, you can see an example Telegram post monitored by SOCRadar.
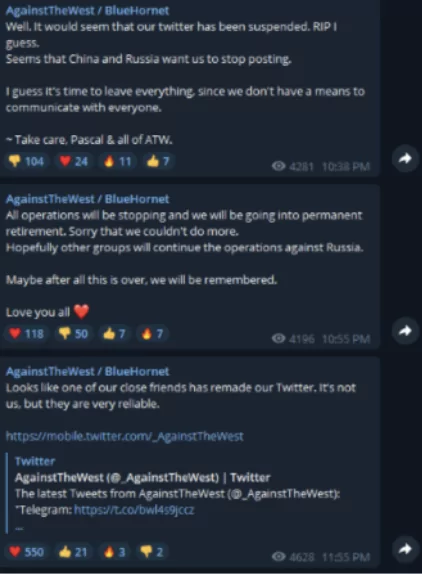
Along with Telegram, ATW/BH has opened a Twitter account to interact with its followers. They have been actively using Twitter, but their account keeps getting suspended by Twitter, which they just continue on a new account.
An interesting thing about the group is that ATW/BH occasionally decides to announce that they have shut their operations, which they did not stop and continued their operations in each case.
AgainstTheWest Joins a New Hacker Forum: breached.co
A new hacker forum emerged on the 16th of March to fill the void RaidForums had created, with the link breached. co. ATW/BH does not wait long to join the new platform that is getting popular each day. ATW/BH joins breached.co. After two days, the forum opened and started posting its leaks on the forum. Some of their leaks are still being posted on their Telegram account, while others are being published on their page.
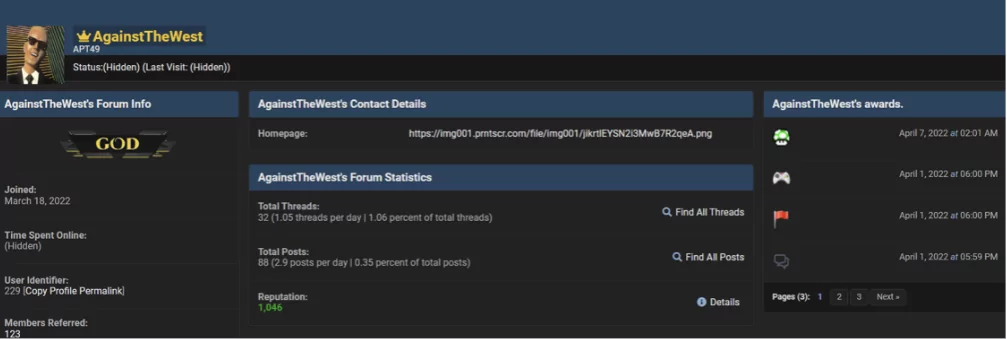
It is essential to state that they continue attacking Russian companies and Chinese enterprises. They are actively leaking sensitive data of major companies on breached.co and Telegram. However, SOCRadar’s analysts have detected a repeating trend in their leak posts. Some of the companies they have leaked have been leaked before in their earlier posts dating back to October 2021. Are they reuploading old leaks?
It is crucial to consider the possibility that the group could have been posting old leaks since their popularity has risen since October/November 2021. Another option is that significant events that were not intriguing back in the group’s first months could have become necessary after some circumstances, such as the Russia-Ukraine crisis.
People would be interested in the previously unpopular leaks, so the group gets more recognition, and their follower base expands by reuploading old leaks. Still, there’s no way to know without checking the contents of both leaks, we cannot say for sure that the group has been reuploading old leaks, but the possibility exists.
Announcing AgainstTheWest’s End Once Again
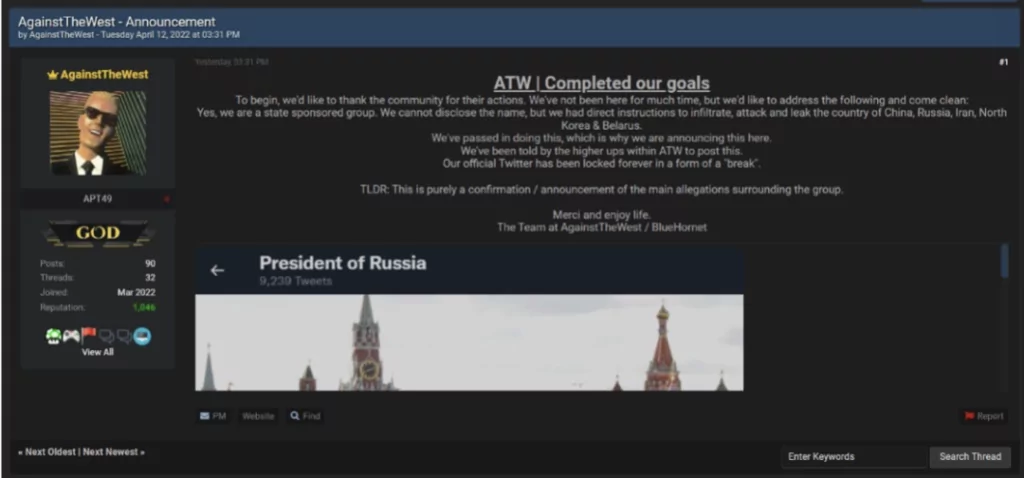
On April 12th, 2022, AgainstTheWest announced that they had completed their goals and are stopping their operations. The group also states that they are a state-sponsored group without disclosing the state’s name. Still, they say that they are told to infiltrate, attack, and leak companies and government agencies of China, Russia, Iran, North Korea, and Belarus.
So, is this the end for AgainstTheWest, or will they come back just as they did in their old announcements on shutting down their operations?
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access.
![SOCRadar® Cyber Intelligence Inc. | Deep Web Profile: AgainstTheWest / BlueHornet [Part 2]](https://socradar.io/wp-content/themes/socradar/assets/image/static/shadow-5.png)
![SOCRadar® Cyber Intelligence Inc. | Deep Web Profile: AgainstTheWest / BlueHornet [Part 2]](https://socradar.io/wp-content/themes/socradar/assets/image/static/shadow-6.png)

































