
GitLab’s Critical Security Update: What You Need to Know (CVE-2023-5009)
GitLab is a widely-used DevOps platform that allows for code hosting, continuous integration, and other collaborative features for both Community and Enterprise users. A new critical security release has just been rolled out for GitLab Community Edition (CE) and Enterprise Edition (EE). Here’s what you need to know about the vulnerabilities and the steps for remediation.
What’s the Issue in GitLab?
The security release primarily addresses a critical vulnerability that affects various versions of GitLab EE starting from 13.12 to 16.2.7, and 16.3 to 16.3.4. This vulnerability allows an attacker to execute pipelines as an arbitrary user through the misuse of scheduled security scan policies. The vulnerability has been identified with a critical severity score of 9.6 (CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:N) and is designated as CVE-2023-5009.
Recommended Solutions & Alternate Mitigations
GitLab has already patched this vulnerability in the latest versions — 16.3.4 for Community Edition and 16.2.7 for Enterprise Edition. Upgrading to these versions is the best course of action for instant mitigation.
If you are running an instance with a version prior to 16.2, mitigations are available. The vulnerability only becomes active if both ‘Direct Transfers’ and ‘Security Policies’ features are enabled simultaneously. Disabling one or both of these features will mitigate the risk.
Additional Patches from GitLab
Apart from the critical security fixes, the new GitLab versions also come with non-security patches. These include improvements like a new indexer in 16.3.4 and minor feature reversions in 16.2.7.
Next Steps for Enhanced Security
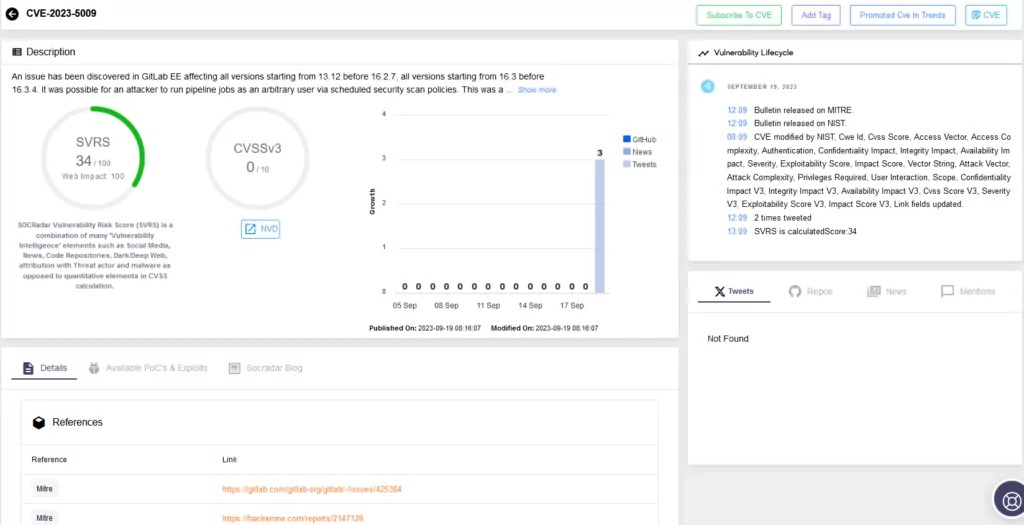
We at SOCRadar strongly urge you to update your GitLab instances immediately to protect against these critical vulnerabilities. Utilizing tools like SOCRadar’s Vulnerability Intelligence and External Attack Surface Management can give you an extra layer of security by providing you insights into your own vulnerabilities and advising on effective remediation methods.
For more information, refer to the official GitLab security release.
Stay safe and keep your codebases safer.




































