What are DevOps, DevSecOps, and Rugged DevOps?
We are hearing these two buzzwords, DevSecOps and DevOps, more frequently. For example, Gartner predicts DevSecOps will reach mainstream adoption within two to five years, which means that we will hear about them even more in the coming years. Therefore, what are they, and what are the differences and similarities?
What is DevOps?
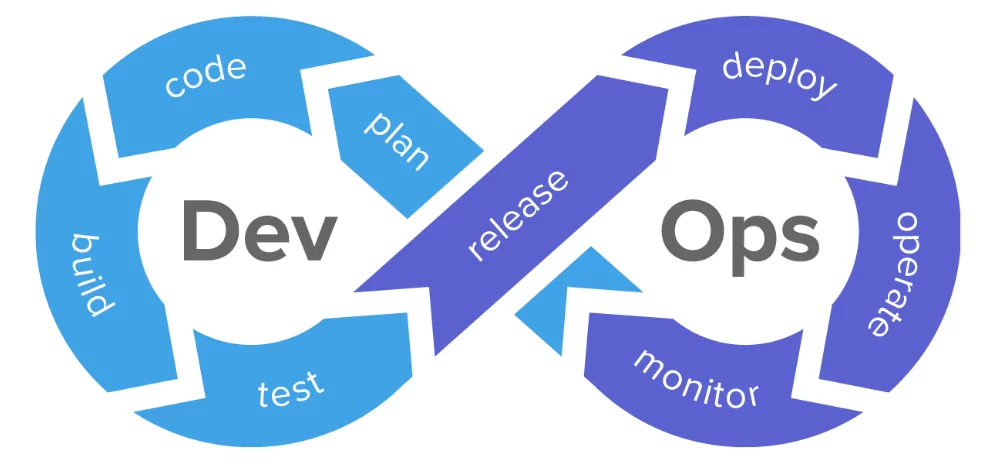
Most enterprises have two separate teams of Development and Operations for their online operations. While the development team is responsible for writing the code, designing, and testing new features, the operations team generally takes care of managing and scaling the servers, backups, and security.
However, when both teams need to work synchronously in instances like publishing a new feature or an update, a multiple-teams approach causes trouble because both teams have different priorities.
DevOps is a collection of strategies to bring software development and IT operations closer, so the development and operations teams are no longer separated in this approach. The goal is to enhance workflow from development to testing to deployment on production servers while lowering risk at each stage. Also, they promote a broad range of skills not limited to a specific function with DevOps.
What is DevSecOps?
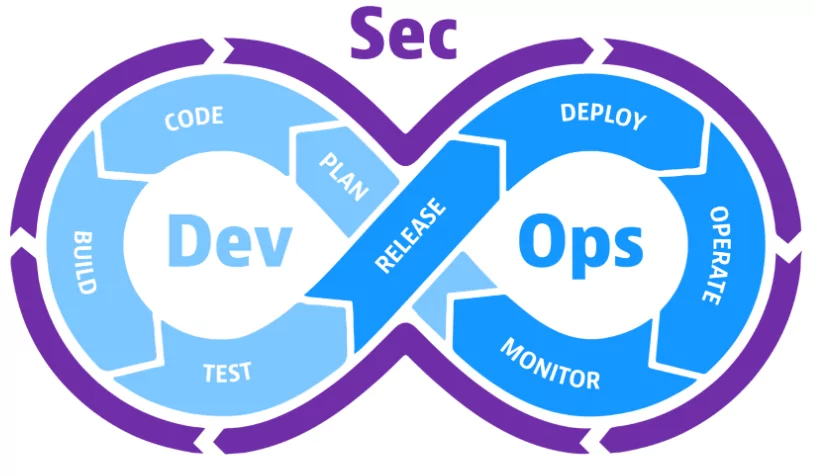
DevSecOps automates the implementation of security at every stage of the software development process, from original design to testing, deployment, and product delivery. It deals with security vulnerabilities when they occur. Therefore, it is easier and less expensive to resolve.
Furthermore, DevSecOps makes the application and infrastructure security a shared responsibility of development, safety, and IT work units, rather than leaving it to the security team. With Azure DevSecOps engineers and AWS DevSecOps engineers, organizations using Azure cloud and AWS can speed up and protect their application development operations.
What are the Similarities Between DevOps and DevSecOps?
- Automation
Both DevOps and DevSecOps can use AI to automate phases in the app development process. This is accomplished in DevOps by using tools like auto-completed code or anomaly detection. In DevSecOps, automated and ongoing security controls and abnormality disclosure can assist proactively in detecting high-risk weaknesses and security risks, even in highly complicated environments. This is especially important when applications operate in distributed, multi-cloud systems and the IT perimeter widens.
- Collaborative Culture
Both require a collaborative culture to achieve development objectives such as rapid iteration and development that does not jeopardize the application environment’s health and security. Also, both approaches include bringing together previously compartmentalized teams to increase visibility across the application’s lifespan, from planning to implementation monitoring.
- Active Monitoring
In both DevOps and DevSecOps, data monitoring for the goal of learning and adjusting is critical. Both approaches are essential to regularly recording and analyzing application data to drive upgrades. Having real-time data is crucial for boosting application speed, reducing the app’s system vulnerabilities, and enhancing the organization’s security status.
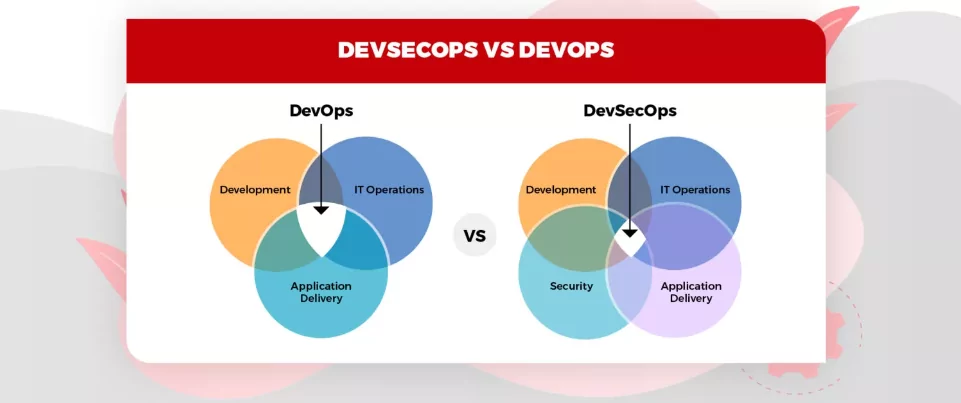
What is the Difference?
As mentioned, security is not another step to include in DevSecOps. Instead, DevSecOps evolved from DevOps as a method to integrate security management before all stages of the development cycle. With this method, application security begins early in the build procedure rather than after the development.
DevSecOps emphasizes the need for developers to write secure code and seeks to address the security concerns left unresolved by DevOps.
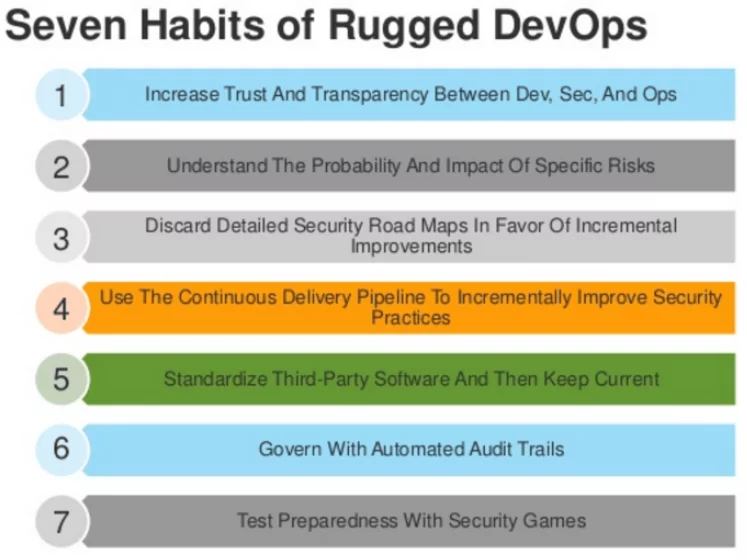
What is Rugged DevOps?
Rugged DevOps is a software development methodology that prioritizes code security at all phases of the software development cycle, utilizing DevOps’ lean thinking and agile attitude and guaranteeing that security is not a post-development concern. Rugged DevOps combines the concepts of DevOps and security and is frequently utilized in cloud software development.
What is the Difference Between Rugged DevOps and DevSecOps?
DevSecOps focuses on integrating security earlier in the application development life cycle to reduce risks and bring security closer to IT and business goals. Rugged DevOps is about transparency and more profound knowledge of potential risks.
This situation is an accelerated strategy where penetration tests are employed throughout the development cycle, and safety guidelines are practiced at the beginning of the project.
What are the Tools for Rugged DevOps?
- Gauntlt
Gauntlt connects to various security technologies, allowing security, development, and operations teams to collaborate on creating rugged software.
- Vault
Vault, a HashiCorp open-source tool, was created to improve the way software teams keep essential keys, tokens, passwords, and other secrets in their projects. Vault is an open-source toolkit for remote management that is environment and infrastructure neutral.
- OWASP Dependency Check
OWASP Dependency-Check controls if your source code contains any publicly published vulnerabilities. It now supports Java and.NET, with some experimental support for Ruby, Node.js, and additional languages.
- Retire.js
Retire.js analyzes your JavaScript libraries and dependencies, flagging any known to be problematic.
- InSpec
InSpec is a testing framework for infrastructure that uses human- and machine-readable language to express compliance, security, and policy requirements. It may also be used to test and audit applications, infrastructure, and various other technologies in your environment to ensure that your buildings follow consistent configuration standards.
In conclusion, employing DevOps vs. DevSecOps entirely depends on organizations and their expectations. However, cyber security should be one of the top concerns in the unsafe contemporary threat landscape.