
What Do You Need To Know About Vulnerability Intelligence
A vulnerability is a weakness in computer software or hardware that allows an attacker to gain access to higher privilege levels. This could lead to the leaking of sensitive information, system manipulation, or genuine users being denied access to services or information (i.e., denial of service).
What is Vulnerability Management
Vulnerability management is a set of security methods for proactively identifying, preventing, mitigating, and classifying vulnerabilities in an IT system, and it’s a crucial aspect of any cybersecurity strategy.
Vulnerability management is an ongoing process that comprises proactive asset discovery, continuous monitoring, mitigation, remediation, and defense strategies to avoid your organization’s attack surface from exposure.
Why Vulnerability Intelligence is Critical for Solid Cybersecurity

As the number of Common Vulnerabilities and Exposures (CVE) continues to rise, they constitute a serious security threat to businesses. One of the most significant issues for businesses is that their security teams cannot patch all of the vulnerabilities discovered during scans.
External vulnerability databases like the NVD and scan vulnerability data are unquestionably helpful.
However, they do not provide a comprehensive view of the organization’s genuine threats. These resources are merely a starting point for understanding the risk profile and reducing hazards. Vulnerability intelligence comes into play here. They can make well-informed judgments about which vulnerabilities to prioritize, how to remediate them, and how to respond to incidents.
Vulnerability intelligence is more than just revealing information about vulnerabilities. Instead, it further assigns risk rankings to each vulnerability throughout the entire digital footprint. These scores adjust to real-world exploits and are based on real-time exploitation evidence.
More Contextual Information

This information can be used by security and IT teams to identify the most significant threats, prioritize updates, and mitigate major vulnerabilities before they become exploited. The finest vulnerability intelligence tools combine robust telemetry with deep machine learning to provide security workers with the context they need to prioritize threats and risks better.
Real-Time Insights
Comprehensive vulnerability intelligence gives security teams real-time insights into threat actor behavior, allowing them to understand better why and how some vulnerabilities are targeted while others are ignored. Automated discovery finds hidden vulnerabilities — even early-stage ones — throughout the attack surface, assigns risk-based priority, raises alerts, and speeds up repair.
Finally, vulnerability intelligence feeds allow security staff to concentrate on the most significant “patch now or invite trouble soon” vulnerabilities while streamlining workflows, increasing team efficiency, avoiding wasted effort, and decreasing downtime.
SOCRadar ThreatFusion: Cyber Threat Intelligence
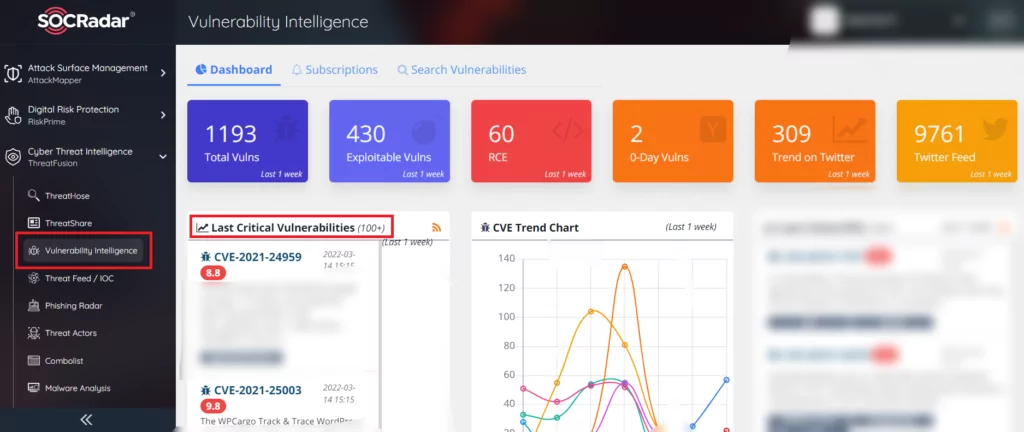
SOCRadar’s ThreatFusion offers an in-depth and real-time threat investigation module powered by big data. It feeds on data sources on the surface, deep and dark web, ensuring you are prepared for potential industry-based threats.
ThratFusion’s modules include:
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access


































