
Exclusive Interview: Dark Web Monitoring, AI’s Role and Strategic Investments in Cyber Security
We are delighted to present an exclusive interview with Nigel Simpson, Head of Global Cybersecurity for International Data Group. With an inspiring career that reflects a deep commitment to safeguarding the digital world, Nigel brings a wealth of knowledge and insights into cybersecurity.
During our enlightening conversation, Nigel sheds light on a myriad of cybersecurity issues, emphasizing the critical importance of vigilant monitoring of the Dark Web.
In addressing the organization’s defenses against emerging threats from the Dark Web, he underscored the indispensable role of third-party monitoring services, highlighting the imperative for enhanced visibility and control coverage.
“Continuous surveillance of the Dark Web by a third party is crucial,” he stated. “It’s an effective strategy to monitor chatter related to your organization, be it stolen company credit cards or employee credentials available for sale.” The C-level manager strongly recommends partnering with security firms that specialize in Dark Web monitoring and employ top-notch analysts to conduct thorough investigations, ensuring a robust defense against the underground cyber threats emerging from the dark corners of the internet.
Moreover, he stressed the importance of proactive security through superior intelligence. “In the realm of cybersecurity, knowledge is indeed power. The amalgamation of precise threat intelligence with a comprehensive suite of security solutions covering most, if not all, domains lays a resilient foundation for safeguarding an organization,” he elaborated.
This proactive approach, which intertwines visibility, control, and intelligent threat detection, is vital in effectively anticipating and neutralizing both present and future cyber threats.
Three Key Countermeasures Against Ransomware
When asked by SOCRadar about the principal threats that significantly endanger businesses today, Sampson identified ransomware as the most formidable among them. He added, “Ransomware is particularly menacing because it is employed by numerous threat actors who utilize diverse methods to breach business infrastructures.”
According to recent studies, in 2022, there were 1.7 million ransomware attacks every day, meaning every second 19 ransomware attacks. The first half of last year saw nearly 236.7 million ransomware attacks worldwide.
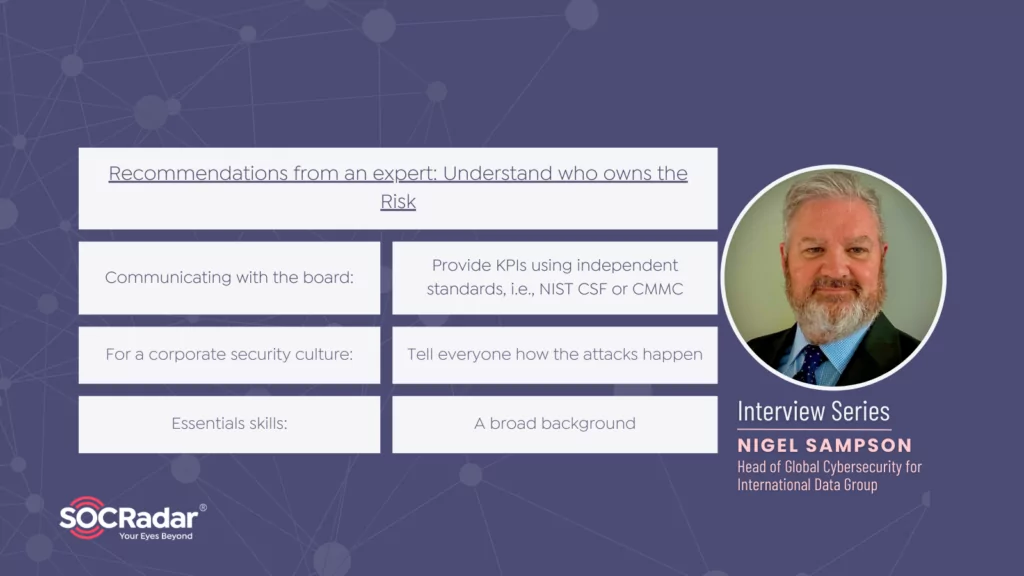
Explaining the proactive solutions that he advised to counter the mounting threat of ransomware attacks, Sampson pointed out three critical steps:
- Security awareness
- Secure email gateways
- Robust NDR
As a seasoned expert in cybersecurity, Simpson emphasized the pivotal role of security awareness training, describing it as ‘one of the simplest ways to combat ransomware’ “Giving employees the tools to identify and block phishing emails that can lead to ransomware is key.”
Highlighting the critical necessity of implementing secure email gateways along with robust Network Detection and Response (NDR) mechanisms, Simpson shed light on their significance, stating, “Secure email gateways provide an automated solution to block suspicious emails with attachments or URLs that lead to breaches.
Although configuring DMARC and SPF proves beneficial, businesses are engaged in sending emails on their customers’ behalf, unable to leverage these technologies due to the looming risk of their communications being thwarted by SPAM detectors. In scenarios where secure email gateways or perimeter defenses exhibit vulnerabilities, Endpoint Detection and Response (EDR)—not to be confused with NDR—plays a crucial role. A proficient EDR system is instrumental in thwarting attacks directed at endpoints, regardless of whether these attacks are orchestrated in memory or within the file system.”
More Investment in AI Technologies Leads to More Efficient Security Solutions
Nigel Simpson also touched upon the impact of AI-based technologies in cyber security and noted that some security vendors quickly adapt to this newly emerging technology.
Simpson emphasized that the fruitful application and effectiveness of Artificial Intelligence (AI) within cybersecurity significantly hinge on the level of investment channeled toward its incorporation across all cybersecurity domains. “I have enlisted best-in-class solutions that incorporate AI, and these have proven highly effective,” the expert shared.
With thoughtful investment, AI serves as the cohesive element fortifying a cybersecurity program and substantially enhances its efficacy and efficiency. This strategic integration ultimately leads to a noteworthy reduction in the overall costs associated with cybersecurity. However, the expert also cautiously noted that the full impact of AI and Machine Learning (ML) on cybersecurity might only unfold distinctly over the next five to eight years, marking a period of anticipatory evolution and refinement in the industry.
Consolidation is on the Rise, and Strategic Budget Allocation is Needed
In the rapidly evolving cybersecurity landscape, the experienced security officer highlighted the ongoing trend of security solution consolidation. “Security companies are aiming to be one-stop shops, expanding their solutions amidst increasing competition,” he noted, pointing out a surge in the use of AI and a focus on Managed Detection and Response (MDR) due to businesses struggling to maintain staffing levels.
Given the persistent and growing threats like ransomware, phishing, and malware, Nigel Simpson advised businesses to strategically allocate their 2024 budgets. “Every business faces common threats, regardless of their size or budget,” the expert cautioned. They recommend investing in secure email, endpoint protection, data loss prevention, and security awareness training for adequate defense, tailoring these investments to each organization’s unique needs and maturity levels. also adding, “Investment in employee training, hiring, and threat intelligence is essential, as these areas are critical for strengthening our security framework.”
Who is Nigel Simpson?
He is a seasoned professional with a comprehensive background encompassing technical skills in computer operations, network engineering, and management. With ten years dedicated to security assessments, audits, and risk management, he has developed a deep understanding and expertise in these crucial areas.
The subsequent fourteen years in security engineering and management have further honed his skills, providing him with a robust foundation in systems and networking and security and risk management. His career, marked by a blend of technical acumen and extensive experience, has made him a knowledgeable and reliable figure in cybersecurity.










