
Loader Malware Emotet is Now Led by Quantum and BlackCat
Emotet (also known as SpmTools) is a sophisticated, modular banking trojan. Emotetmostly serves as a downloader or dropper of other banking trojans. It is a loader-as-a-service (LaaS). It is mainly distributed by spam emails (malspam).
Malicious scripts, document files with built-in macros, or malicious links can all spread the infection. Emotet has become a prominent, intrusive malware loader due to changes throughout time, mainly as a result of its capacity to carry out a complete infection cycle and smoothly spread other types of malware.
BlackCat and Quantum Use Emotet as Initial Attack Vector
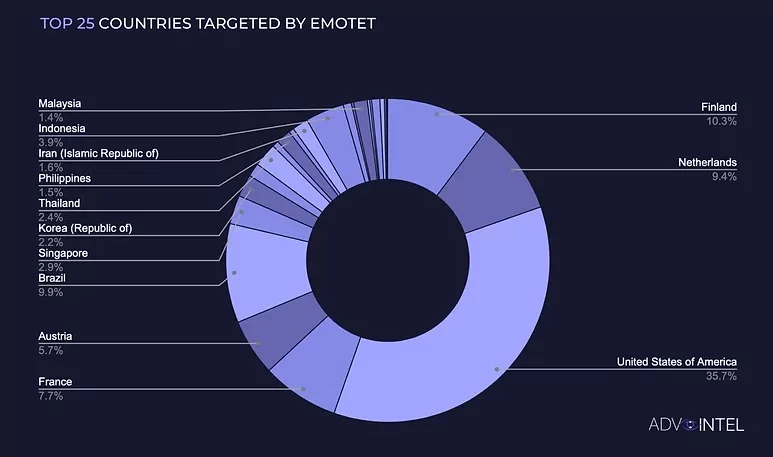
AdvIntel recorded 1,267,598total Emotet infections globally in 2022. Further data from the research shows that Emotet infections peaked at the beginning of the Russian/Ukrainian crisis, with groups like Quantum and BlackCat starting to use the malware after Conti. The malware’s most targeted country is the U.S., with an approximately 36% rate.
Emotet was once a tool mainly used by Conti affiliates. It has also been used by many threat actors and groups in various cyberattacks. Now, Quantum and BlackCat are the ones who lead the Emotet infection chain.
Emotet’s botnet attack flow utilizes Cobalt Strike to launch ransomware. In other words, threat actors presently use Emotet primarily as a dropper or downloader for a Cobalt Strike beacon, which distributes a payload enabling threat actors to hijack networks and carry out ransomware operations.
TTPs & IoCs
Emotet TTPs
|
ID |
Name |
|
|
Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
||
|
Credentials from Password Stores: Credentials from Web Browsers |
||
Latest Emotet IoCs
|
URL |
Date Added |
|
2022-09-07 |
|
|
2022-08-24 |
|
|
2022-08-17 |
|
|
http://scandryer.se/you-d-not-agree-to-elements-of-the-letter-s/ |
2022-08-09 |
|
2022-08-09 |
|
|
2022-08-09 |
|
|
2022-08-09 |
|
|
https://fractal.vn/users_contact/ol-e-g-d-m-i-tr-ie-nko4-9-7gmail-com/ |
2022-08-09 |
|
https://progea4d.pl/waloryzacja-przyrodnicza-kamieniolomow-mydlniki-oraz-bodzow/ |
2022-08-09 |
|
2022-08-09 |
Emotet botnet IoCs can be found here. CIRT published a longer list of IoCs.
IoCs for BlackCat and Quantum Locker are also available.




































