RaidForums Leak, Breached IT Services, and New LockBit Victim
Step into the shadowy world of the dark web as we explore this week’s gripping headlines. From the leaked RaidForum database to unauthorized access sales and the sale of Spanish credit cards, these incidents expose the underworld of cybercrime. Witness the ruthless reign of Lockbit 3.0 as it targets the prestigious YKK Group and the unsettling exposure of the Philippine Ministry of Foreign Affairs database.
Join us as we unravel the unknowns of the dark web, shedding light on the risks and repercussions.
Find out if your data has been exposed.
Database of RaidForums Has Been Leaked
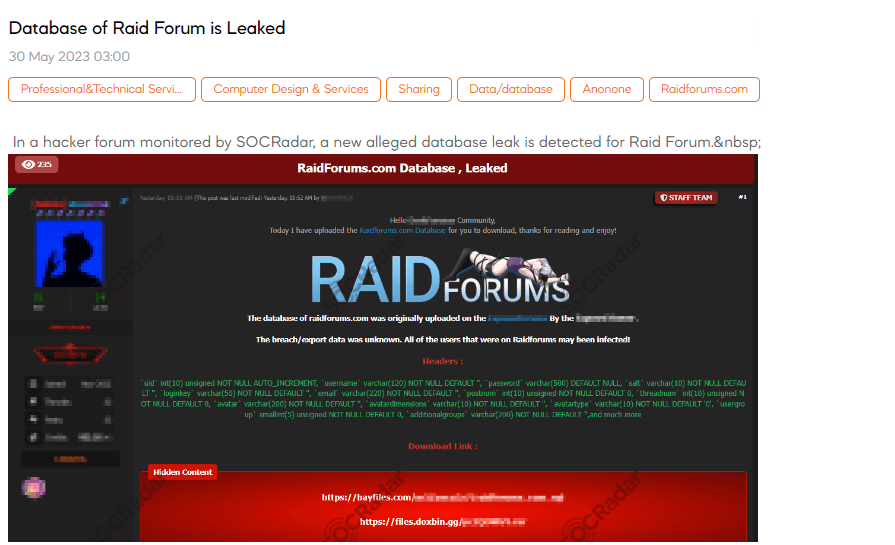
SOCRadar dark web team has detected a post that a threat actor claims exposed the member database of RaidForums, a hacker forum. The exposed database reportedly contains a SQL file with sensitive information, including usernames, email addresses, hashed passwords, registration dates, and other forum-related details. 478,870 members who registered between March 20, 2015, and September 24, 2020, are said to be affected. Soon after the initial leak, the compromised data swiftly spread across various hacker forums, Telegram channels, and the deep and dark web. This incident has provided threat actors and security researchers valuable insights into the former forum’s user base.
Unauthorized Access Sale is Detected for an American IT Support Services Company
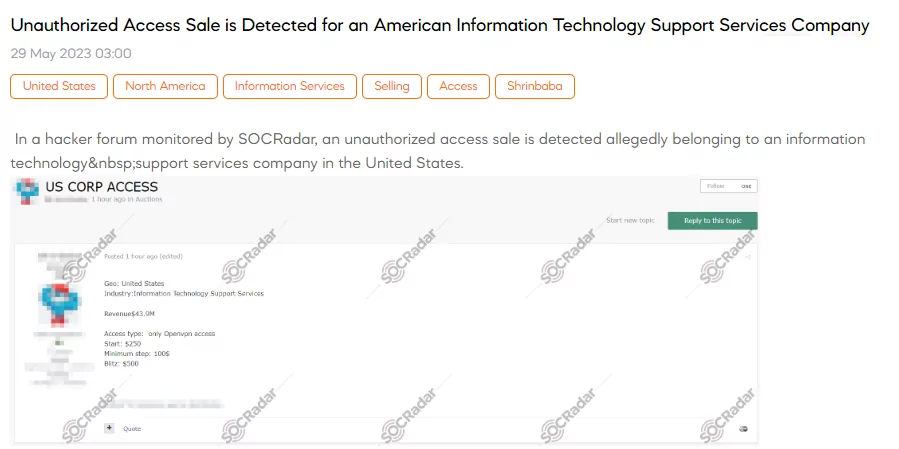
On June 29, a SOCRadar researcher discovered a post that a threat actor claimed to have unauthorized access for sale. The target in question is an information technology and support services company based in the United States. With an estimated revenue of $43.9 million, the company’s security appears to have been compromised, specifically through OpenVPN access. The post lists the starting price for this illicit access at $250, with minimum bidding increments of $100. Additionally, there is an option to make an immediate purchase, referred to as “Blitz,” for $500.
1000 Credit Cards Belonging to Spain are on Sale
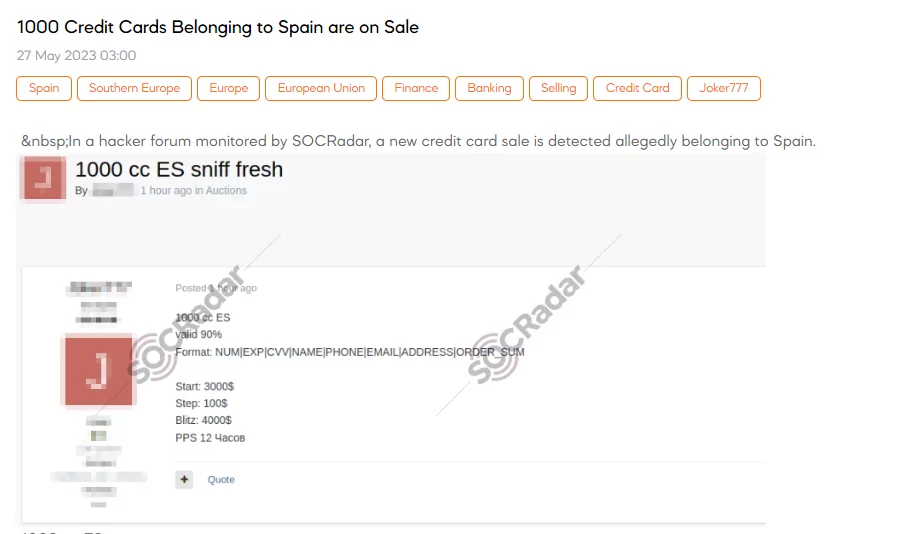
SOCRadar dark web team has detected a post that a threat actor is selling 1000 credit cards allegedly belonging to individuals in Spain. The credit cards are reported to have a 90% validity rate. The format of the information being sold includes the card number, expiration date, CVV code, cardholder’s name, phone number, email address, billing address, and order amount. The starting price for this illicit sale is $3000, with bidding increments of $100. Additionally, an option for an immediate purchase, known as “Blitz,” is priced at $4000.
The New Ransomware Victim of LockBit 3.0: YKK Group
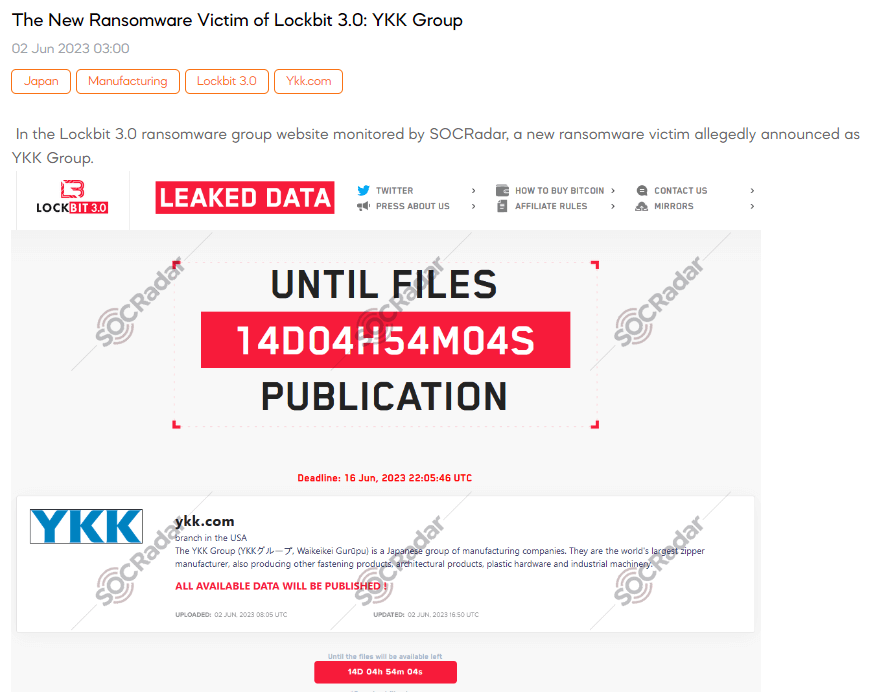
A SOCRadar dark web researcher discovered a post stating that the LockBit ransomware group has targeted YKK, a Japanese manufacturing group known for being the world’s largest zipper manufacturer. The post claims that YKK’s branch in the US has become a victim of the ransomware attack. The post also mentions a deadline of June 16, where all available data will be published if the ransom demands are unmet.
Database of the Philippine Ministry of Foreign Affairs is Leaked

A SOCRadar dark web researcher has identified a post where a threat actor claims to possess secret documents belonging to the Ministry of Foreign Affairs of the Philippines. The alleged database leak reportedly contains a total of 18,155 files. These files are stated to be private and pertain to the year 2022.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.