Dark Web Profile: LockBit 3.0 Ransomware
[Update] August 31, 2023: See the subheading: “LockBit’s Operational Struggles, Empty Threats, and Sudden Surge.”
[Update] July 03, 2023: LockBit claimed to hack Taiwan Semiconductor Manufacturing Company (TSMC), but TSMC clarified that only one of its suppliers, Kinmax Technology, was breached. Added the subheading: “TSMC Confirms Supplier Hack Following Lockbit’s Claim.”
[Update] June 23, 2023: LockBit is reportedly developing ransomware capable of targeting a broader range of systems, added the subheading: “LockBit Tries to Expand Reach to Different Architectures: Apple, Linux, FreeBSD.”
[Update] June 15, 2023: LockBit was identified as the most active global ransomware group and RaaS provider based on the number of victims on their data leak site. Added under the subheading “The Most Active Ransomware Group of 2022: LockBit.”
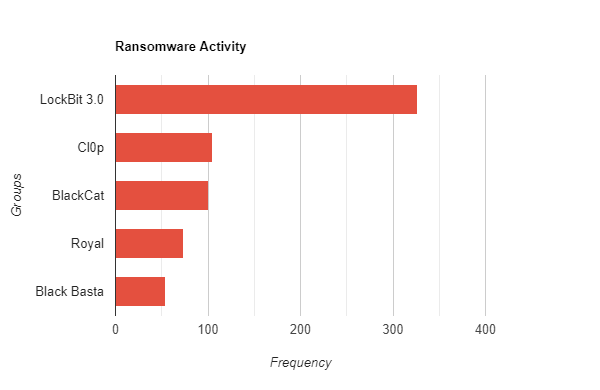
The frequency of ransomware attacks is on the rise every year. A single group, the LockBit Ransomware Group, is accountable for over one-third of all ransomware attacks in the latter half of the previous year, the initial quarter of 2023.
LockBit Ransomware Group was first observed in September 2019, it became the most active ransomware group of 2022 with the shutdown of Conti, and as of the first quarter of 2023, they still stand out as the most active ransomware group. The group, which has over 1500 victim announcement records on the SOCRadar platform, broke the record in the first quarter of 2023 as the most active ransomware group by far, with over 300 announced victims.
Atento, a CRM company, showed the impact of an attack by LockBit as $42.1 million in its financial performance report published in 2021. $34.8 million was due to revenue loss, and $7.3 million was mitigation expenses. Even if these astronomical numbers could vary from company to company, the total financial loss caused by LockBit’s malicious acts can exceed billions of dollars.
Security researchers also have found new strains and evidence that the group responsible for LockBit 3.0 plans to expand the malware’s infection capacity. While the latest variant LockBit 3.0, had previously targeted Windows, Linux, and VMware ESXi servers, alleged new versions of LockBit encryptors have been identified that can also affect macOS, ARM, FreeBSD, MIPS, and SPARC CPUs. Given the group’s already sizable attack volume, it is likely that they will continue to increase the number of target devices, which could result in a significant surge in LockBit attacks soon.
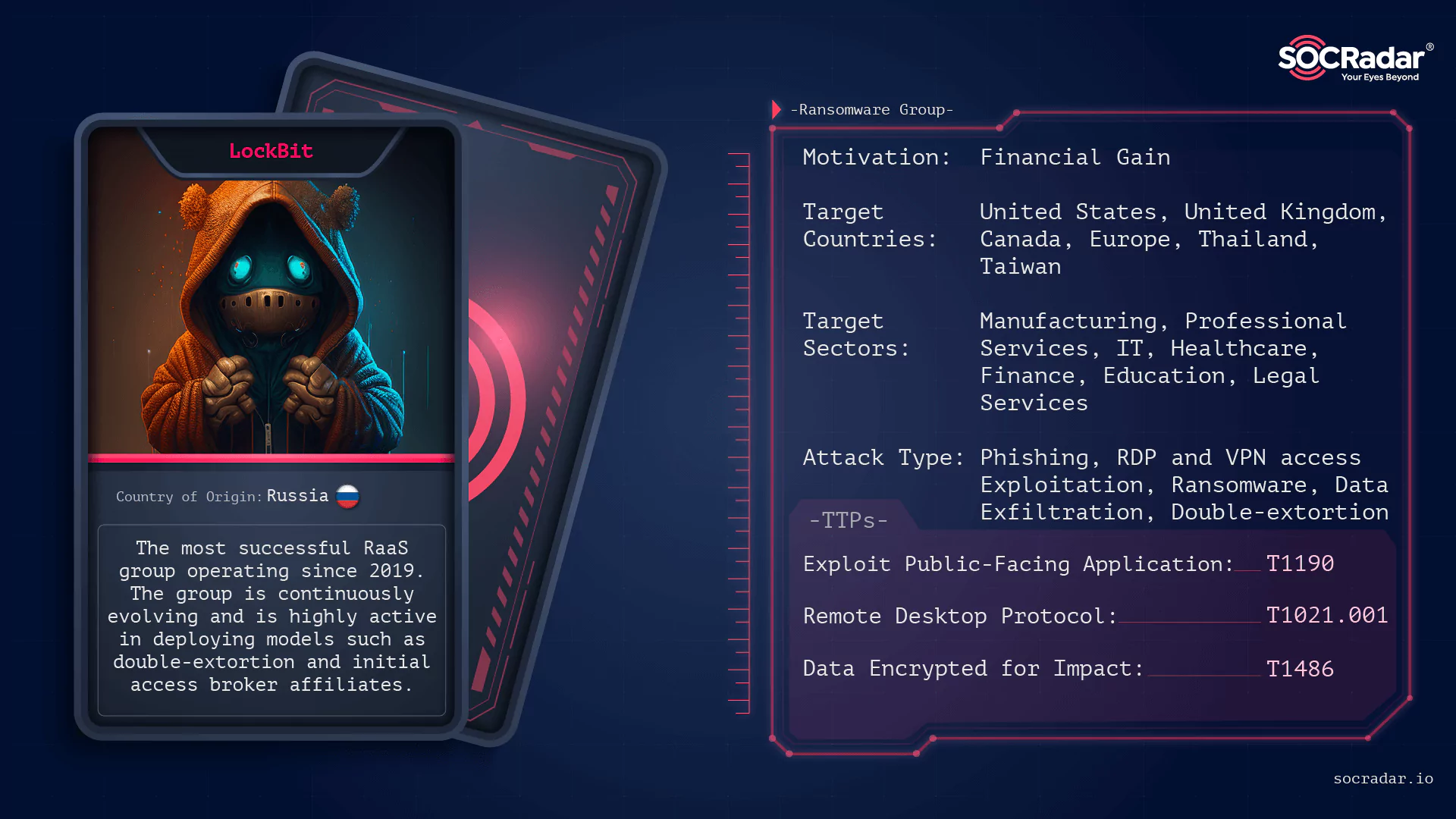
Who is LockBit 3.0 Ransomware Group
LockBit 3.0 is a Ransomware-as-a-Service (RaaS) group that continues the legacy of LockBit and LockBit 2.0. From January 2020, LockBit adopted an affiliate-based ransomware approach, where its affiliates use various tactics to target a wide range of businesses and critical infrastructure organizations. LockBit has been highly active in deploying models such as double extortion, initial access broker affiliates, and advertising on hacker forums. They have even been known to recruit insiders and make contests in forums for recruiting skilled hackers; such expansionist policies have attracted numerous affiliates, have victimized thousands of entities, and continue their malicious acts.

LockBit Black, also known as LockBit 3.0, has been recalled as the latest variant of LockBit since July 2022. One of the key differences from its predecessor is the ability to customize various options during both the compilation and execution of the payload. LockBit 3.0 utilizes a modular approach and encrypts the payload until execution, which presents significant obstacles to malware analysis and detection.
What are the LockBit 3.0’s Targets
LockBit 3.0 infects the target system if it is not on the exclusion list of specific languages. Excluded languages include the local language of Russian-influenced countries and the languages of Russian-allied countries.
To confirm the location of the targeted system, LockBit ransomware employs the functions:
- GetSystemDefaultUILanguage()
- GetUserDefaultUILanguage()
It cross-checks the result against a set of countries, and in case the locale doesn’t match any of the specified countries, the malware proceeds to the subsequent verification step. Some of the languages that are excluded are Romanian (Moldova), Arabic (Syria), and Tatar (Russia), but this is not an exhaustive list.
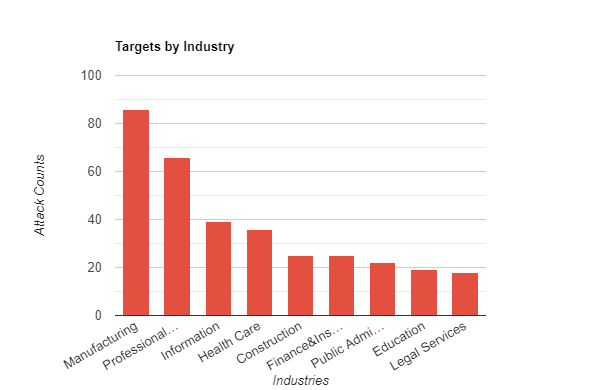
Although the ransomware group claims not to engage in politics, many of its targets appear to be NATO and allied countries. According to SOCRadar data, about half of the attacks with the LockBit 3.0 variant affect US companies.
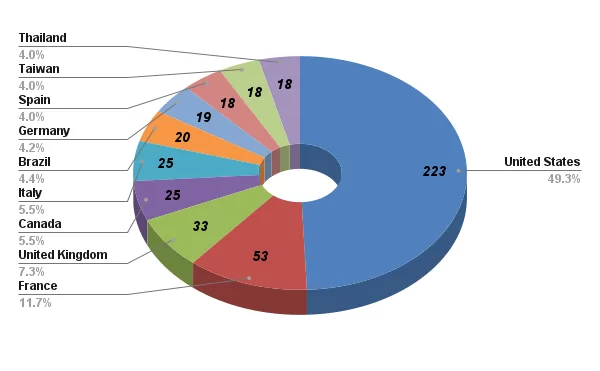
Again, according to SOCRadar data, manufacturing takes the lead on a sectoral basis, but it is impossible to identify a specifically targeted industry. The fact that healthcare and education are among the sectors they target the most reveals that no industry is excluded, and in terms of business type. However, it is seen that it usually targets small or medium-sized organizations; huge companies such as IT company Accenture can also fall into the victim category for LockBit.
Findings on LockBit 3.0 Ransomware
According to CISA’s advisory:
LockBit 3.0, a Ransomware-as-a-Service (RaaS), has several options for configuring its behavior during compilation. Once executed in a victim’s system, LockBit 3.0 affiliates can modify its behavior using additional arguments, such as lateral movement or safe mode. If LockBit affiliates lack access to the passwordless version of the ransomware, they must provide a password during execution. Provided cryptographic key decodes the ransomware’s executable to protect the encoded file uploaded to the target system.
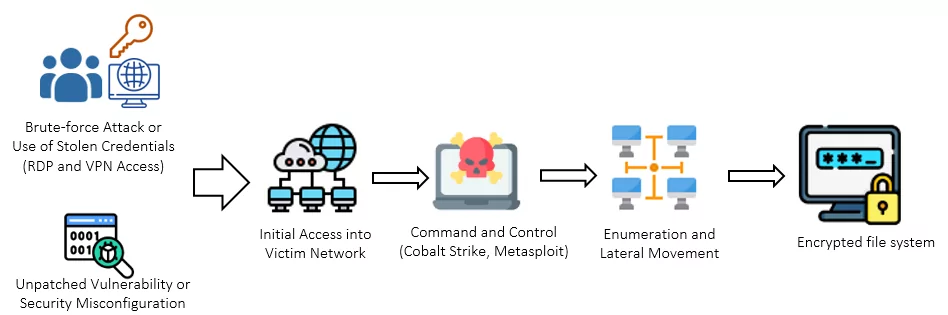
LockBit 3.0 affiliates use diverse methods for initial access, including exploiting RDP, launching phishing campaigns, and exploiting vulnerabilities in public-facing applications. Using an open-source package installer known as Chocolatey to install and execute malicious payloads is a recurring feature in LockBit 3.0 attacks, likely employed to evade detection.
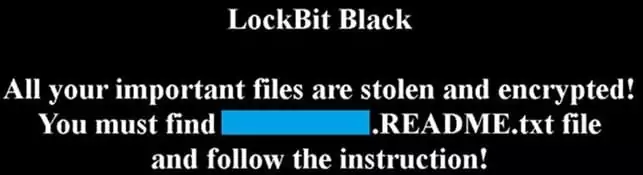
LockBit 3.0 uses hardcoded credentials or compromised local accounts with elevated privileges to spread through a victim network. Using the Server Message Block (SMB) protocol, it can also spread via Group Policy Objects and PsExec. After encryption, LockBit 3.0 drops a ransom note and changes the host’s wallpaper and icons to LockBit branding. It may also send encrypted host and bot information to a command and control server.
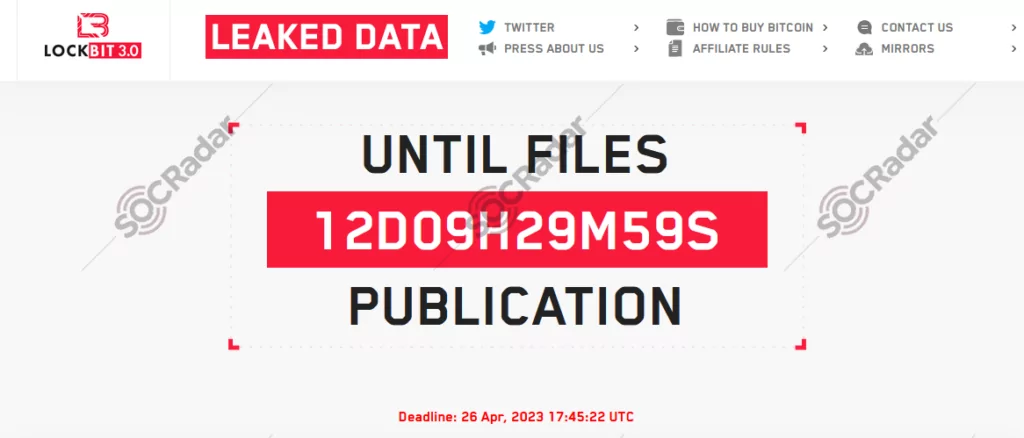
LockBit 3.0 affiliates exfiltrate sensitive company data files before encryption using Stealbit, rclone, -exfiltration tools that LockBit commonly uses- and public file-sharing services. Their affiliates also use other public file-sharing services to exfiltrate data. LockBit threat actors use various tools such as ProDump and SoftPerfect Network Scanner to collect information about hostnames, network services, and remote access protocols. They also use remote desktop software, popular file transfer tools, and PuTTY Link to move between hosts and transfer files between compromised hosts and their command and control servers.
LockBit ransomware deletes log files, files in the recycle bin, and volume shadow copies after encrypting the victim’s files. The group also employs a hybrid encryption approach using AES and RSA encryption algorithms.
The Most Active Ransomware Group of 2022: LockBit
The LockBit group is responsible for approximately one in six ransomware attacks targeting U.S. government offices in 2022, according to the U.S. Cybersecurity and Infrastructure Security Agency (CISA), FBI, and other cybersecurity authorities.
In a collaborative effort, the agencies published an extensive examination of LockBit, which is considered the most widely deployed ransomware variant worldwide, in 2022.
LockBit Conducted Nearly 1,700 Attacks and Gained $91 Million from Victims in the US
The agencies disclosed that LockBit had claimed responsibility for at least 1,653 ransomware attacks by listing the victims on its leak site, and since the first attack in the U.S. in January 2020, the group has extorted approximately $91 million from its victims in the United States.
Each participating country shared statistics showcasing LockBit’s prevalence in their respective regions. For example, Australia reported that the gang accounted for 18% of total reported ransomware incidents in the past year. LockBit was responsible for over 20% of attacks in Canada and New Zealand in 2022.
In the U.S., LockBit targeted public entities, including municipal and county governments, public education institutions, and emergency services such as law enforcement agencies, constituting 16% of attacks.
The Growing Impact of LockBit
The advisory on CISA outlines LockBit’s tactics and exploited vulnerabilities, highlighting the group’s utilization of affiliates who employ diverse methods to breach organizations. Some affiliates have also leveraged popular vulnerabilities like Log4j.
Operating as a Ransomware-as-a-Service (RaaS), LockBit attracts affiliates to conduct a variety of ransomware attacks. Additionally, CERT NZ observed LockBit affiliates engaging in secondary ransomware extortion by targeting organizations responsible for managing other networks. After infecting the primary target, affiliates proceed to extort customer companies using secondary ransomware, locking down the services they use. These findings emphasize LockBit’s widespread reach and the decentralized network of threat actors involved in these attacks.
LockBit has continuously improved its operations, evolving through multiple versions since LockBit Red, such as LockBit 2.0 and LockBit 3.0 (LockBit Black). The group integrated tooling from other ransomware strains, such as BlackMatter and ALPHV (BlackCat Ransomware), into LockBit 3.0. In January 2023, LockBit released LockBit Green, incorporating source code from the ended Conti ransomware.
Cybersecurity experts have noted LockBit’s distinctive approach in consistently enhancing its model. The introduction of LockBit 2.0 in mid-2021 had an immediate impact on the cybercriminal market.
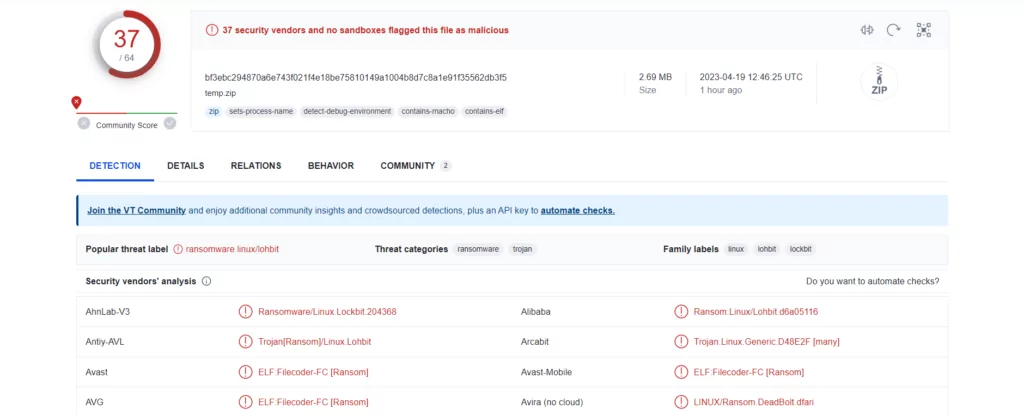
LockBit Tries to Expand Reach to Different Architectures: Apple, Linux, FreeBSD
LockBit is reportedly developing ransomware capable of targeting a broader range of systems, extending beyond the Windows environment.
Researchers from Kaspersky recently discovered a ZIP file containing LockBit malware samples that targeted FreeBSD, Linux, and various embedded technologies, including diverse CPU instruction set architectures, including ARM, MIPS, ESA/390, PowerPC, and even the Apple M1 chip utilized in Mac and iPad devices.
Researchers state that these samples originate from LockBit’s earlier encryptor variations, which threat actors used when targeting VMWare ESXiservers. However, the samples are still being developed as some are unsigned and cannot be executed yet.
Still, the fact LockBit is trying to develop such ransomware signifies a growing trend among ransomware actors to expand their target platforms. If released, these new ransomware variants could present new challenges for victims and further establish LockBit’s position in the evolving threat landscape.
TSMC Confirms Supplier Hack Following Lockbit’s Claim
Taiwan Semiconductor Manufacturing Company (TSMC) confirmed that one of its hardware suppliers was hacked, but assured that it had no impact on its operations or customer data.
The group demanded a $70 million ransom from TSMC, but there were no indications of any plans to pay.
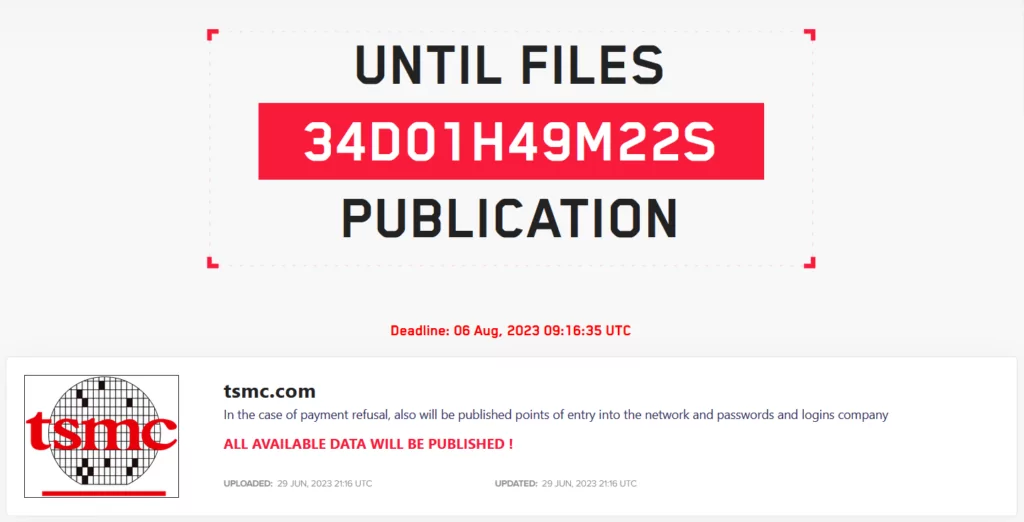
The supplier, Kinmax, acknowledged the breach in its internal testing environment, which contained system installation preparations for customers. TSMC promptly terminated data exchange with Kinmax following the breach.
Kinmax has apologized to affected customers and implemented enhanced security measures to prevent future incidents.
LockBit’s Operational Struggles, Empty Threats, and Sudden Surge
The cybersecurity realm has been engaged in discussions concerning LockBit’s predicament for a while now. Researchers have reported that there are operational challenges within the ransomware gang.
The gang’s challenges have led to a noticeable decline in the quality of their ransomware activities. Nonetheless, the notorious gang continues to project a facade of strong narratives in their communication.
However, despite maintaining their facade, the researchers’ observation holds true – LockBit has consistently stumbled in their attempts to actually release the stolen data. This disconnection between their claims and actions has led to the conclusion that their threats were hollow, relying solely on their infamous reputation to pressure victims into paying ransom.
As these discussions persist, a recent turn of events has come to the fore. After a period of relative inactivity spanning several months, the LockBit ransomware group has listed more than 20 victims within a single day.
The latest tweet from vx-underground not only confirms this surge in activity but also highlights that the gang has reindexed their entire website. As of August 31, 2023, the revamped site now lists over 100 previous victims whose data has supposedly been leaked.
As these leaks emerged subsequent to claims about LockBit’s struggles, it almost appears as if the gang is trying to disprove the assertions and mitigate their impact on the gang’s reputation.
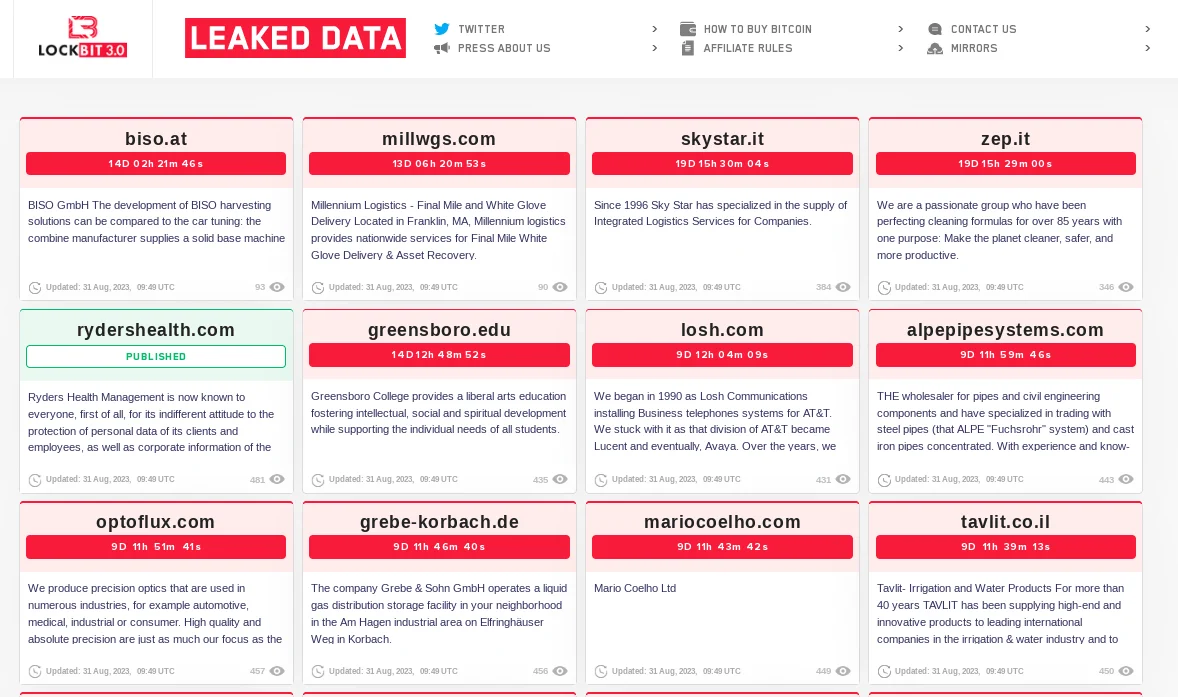
LockBit’s latest leaks
Conclusion
In conclusion, LockBit 3.0 is a highly active and expanding Ransomware-as-a-Service (RaaS) group that has victimized thousands of organizations worldwide and employs various tactics, techniques, and procedures due to its wide number of affiliates. Moreover, there is a high probability that the number of victims and target pool will keep increasing, leading to a notable upsurge in LockBit attacks in the upcoming days, especially if they manage to become the first notable ransomware affecting IOS devices. The group’s targeting of many countries and sectors, and its efforts to increase the number of systems it can infect, also show that it poses a significant danger to all organizations.
How can SOCRadar Help?
LockBit affiliates commonly use phishing campaigns to gain initial access to their ransomware attacks. To prevent this, organizations can use SOCRadar’s Digital Risk Protection for brand protection, which proactively denies potential phishing campaigns that impersonate their domains.
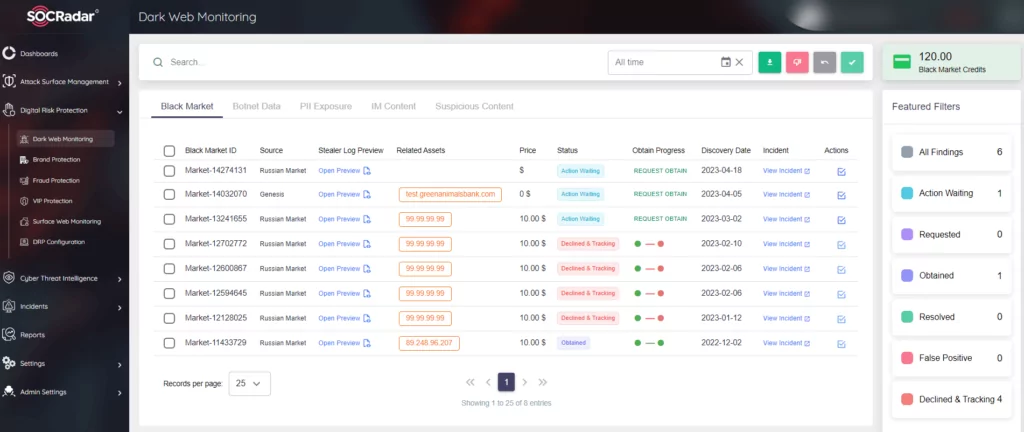
In addition, LockBit affiliates also use spam emails containing malicious documents, and they may use stolen credentials to gain access. To prevent these, it is crucial to demand the use of multi-factor authentication and to be cautious when opening any email attachments.
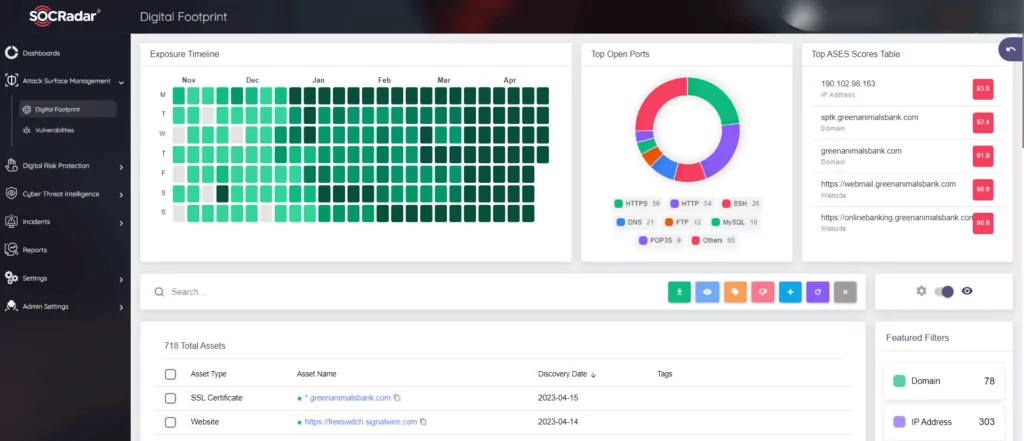
The most crucial step in preventing ransomware attacks is to keep offline backups. However, the group uses a double extortion model, stealing the victim’s data before encrypting it, making even offline backups insufficient to avoid paying the ransom. Organizations should be aware of any vulnerabilities in their environment to prevent this, which can be achieved with SOCRadar’s Attack Surface Management. This provides visibility into external-facing digital assets, allowing security teams to track vulnerabilities and limit the attack surface that ransomware operators may exploit.
MITRE ATT&CK TTPs
| Tactics | Technique | ID |
| Initial Access | Valid Accounts | T1078 |
| Exploit External Remote Services | T1133 | |
| Drive-by Compromise | T1189 | |
| Exploit Public-Facing Application | T1190 | |
| Phishing | T1566 | |
| Execution | Execution | TA0002 |
| Software Deployment Tools | T1072 | |
| Persistence | Valid Accounts | T1078 |
| Boot or Logo Autostart Execution | T1547 | |
| Privilege Escalation | Privilege Escalation | TA0004 |
| Boot or Logo Autostart Execution | T1547 | |
| Defense Evasion | Obfuscated Files or Information | T1027 |
| Indicator Removal: File Deletion | T1070.004 | |
| Execution Guardrails: Environmental Keying | T1480.001 | |
| Credential Access | OS Credential Dumping: LSASS Memory | T1003.001 |
| Discovery | Network Service Discovery | T1046 |
| System Information Discovery | T1082 | |
| System Location Discovery: System Language Discovery | T1614.001 | |
| Lateral Movement | Remote Services: Remote Desktop Protocol | T1021.001 |
| Command and Control | Application Layer Protocol: File Transfer Protocols | T1071.002 |
| Protocol Tunnel | T1572 | |
| Exfiltration | Exfiltration | TA0010 |
| Exfiltration Over Web Service | T1567 | |
| Exfiltration Over Web Service: Exfiltration to Cloud Storage | T1567.002 | |
| Impact | Data Destruction | T1485 |
| Data Encrypted for Impact | T1486 | |
| Service Stop | T1489 | |
| Inhibit System Recovery | T1490 | |
| Defacement: Internal Defacement | T1491.001 |
Common CVEs Exploited by LockBit Affiliates
CISA notes that LockBit affiliates take advantage of both old and new exploits, including:
- CVE-2021-22986: F5 iControl REST Unauthenticated Remote Code Execution Vulnerability
- CVE-2023-0669: Fortra GoAnyhwere Managed File Transfer (MFT) Remote Code Execution Vulnerability
- CVE-2023-27350: PaperCut MF/NG Improper Access Control Vulnerability
- CVE-2021-44228: Apache Log4j2 Remote Code Execution Vulnerability
- CVE-2021-22986: F5 BIG-IP and BIG-IQ Centralized Management iControl REST Remote Code Execution Vulnerability
- CVE-2020-1472: NetLogon Privilege Escalation Vulnerability
- CVE-2019-0708: Microsoft Remote Desktop Services Remote Code Execution Vulnerability
- CVE-2018-13379: Fortinet FortiOS Secure Sockets Layer (SSL) Virtual Private Network (VPN) Path Traversal Vulnerability
See CISA’s Known Exploited Vulnerabilities (KEV) list for more information on mentioned vulnerabilities.
Tools Used by LockBit Affiliates
LockBit has been identified to use the following tools, as CISA lists:
| Tool | Intended Use | Repurposed Use by LockBit Affiliates | MITRE ATT&CK ID |
| 7-zip | Compresses files into an archive. | Compresses data to avoid detection before exfiltration. | T1562 |
| AdFind | Searches Active Directory (AD) and gathers information. | Gathers AD information used to exploit a victim’s network, escalate privileges, and facilitate lateral movement. | S0552 |
| Advanced Internet Protocol (IP) Scanner | Performs network scans and shows network devices. | Maps a victim’s network to identify potential access vectors. | T1046 |
| Advanced Port Scanner | Performs network scans. | Finds open Transmission Control Protocol (TCP) and User Data Protocol (UDP) ports for exploitation. | T1046 |
| AdvancedRun | Allows software to be run with different settings. | Enables escalation of privileges by changing settings before running software. | TA0004 |
| AnyDesk | Enables remote connections to network devices. | Enables remote control of the victim’s network devices. | T1219 |
| Atera Remote Monitoring & Management (RMM) | Enables remote connections to network devices. | Enables remote control of the victim’s network devices. | T1219 |
| Backstab | Terminates antimalware-protected processes. | Terminates endpoint detection and response (EDR)- protected processes. | T1562.001 |
| Bat Armor | Generates .bat files using PowerShell scripts. | Bypasses PowerShell execution policy. | T1562.001 |
| Bloodhound | Performs reconnaissance of AD for attack path management. | Enables identification of AD relationships that can be exploited to gain access to a victim’s network. | T1482 |
| Chocolatey | Handles command-line package management on Microsoft Windows. | Facilitates installation of LockBit affiliate actors’ tools. | T1072 |
| Defender Control | Disables Microsoft Defender. | Enables LockBit affiliate actors to bypass Microsoft Defender. | T1562.001 |
| ExtPassword | Recovers passwords from Windows systems. | Obtains credentials for network access and exploitation. | T1003 |
| FileZilla | Performs cross-platform File Transfer Protocol (FTP) to a site, server, or host. | Enables data exfiltration over FTP to the LockBit affiliate actors’ site, server, or host. | T1071.002 |
| FreeFileSync | Facilitates cloud-based file synchronization. | Facilitates cloud-based file synchronization for data exfiltration. | T1567.002 |
| GMER | Removes rootkits. | Terminates and removes EDR software. | T1562.001 |
| Impacket | Collection of Python classes for working with network protocols. | Enables lateral movement on a victim’s network. | S0357 |
| LaZagne | Recovers system passwords across multiple platforms. | Collect credentials for accessing a victim’s systems and network. | S0349 |
| Ligolo | Establishes SOCKS5 or TCP tunnels from a reverse connection for pen testing. | Enables connections to systems within the victim’s network via reverse tunneling. | T1095 |
| LostMyPassword | Recovers passwords from Windows systems. | Obtains credentials for network access and exploitation. | T1003 |
| MEGA Ltd MegaSync | Facilitates cloud-based file synchronization. | Facilitates cloud-based file synchronization for data exfiltration. | T1567.002 |
| Microsoft Sysinternals ProcDump | Monitors applications for central processing unit (CPU) spikes and generates crash dumps during a spike. | Obtains credentials by dumping the contents of the Local Security Authority Subsystem Service (LSASS). | T1003.001 |
| Microsoft Sysinternals PsExec | Executes a command-line process on a remote machine. | Enables LockBit affiliate actors to control victim’s systems. | S0029 |
| Mimikatz | Extracts credentials from a system. | Extracts credentials from a system for gaining network access and exploiting systems. | S0002 |
| Ngrok | Enables remote access to a local web server by tunneling over the internet. | Enables victim network protections to be bypassed by tunneling to a system over the internet. | S0508 |
| PasswordFox | Recovers passwords from Firefox Browser. | Obtains credentials for network access and exploitation. | T1555.003 |
| PCHunter | Enables advanced task management, including system processes and kernels. | Terminates and circumvents EDR processes and services. | T1562.001 |
| PowerTool | Removes rootkits and detects, analyzes, and fixing kernel structure modifications. | Terminates and removes EDR software. | T1562.001 |
| Process Hacker | Removes rootkits. | Terminates and removes EDR software. | T1562.001 |
| PuTTY Link (Plink) | Automates Secure Shell (SSH) actions on Windows. | Enables LockBit affiliate actors to avoid detection. | T1572 |
| Rclone | Manages cloud storage files using a command-line program. | Facilitates data exfiltration over cloud storage. | S1040 |
| Seatbelt | Performs numerous security-oriented checks. | Performs numerous security-oriented checks to enumerate system information. | T1082 |
| ScreenConnect (also known as ConnectWise) | Enables remote connections to network devices for management. | Enables LockBit affiliate actors to remotely connect to a victim’s systems. | T1219 |
| SoftPerfect Network Scanner | Performs network scans for systems management. | Enables LockBit affiliate actors to obtain information about a victim’s systems and network. | T1046 |
| Splashtop | Enables remote connections to network devices for management. | Enables LockBit affiliate actors to remotely connect to systems over Remote Desktop Protocol (RDP). | T1021.001 |
| TDSSKiller | Removes rootkits. | Terminates and removes EDR software. | T1562.001 |
| TeamViewer | Enables remote connections to network devices for management. | Enables LockBit affiliate actors to remotely connect to a victim’s systems. | T1219 |
| ThunderShell | Facilitates remote access via Hypertext Transfer Protocol (HTTP) requests. | Enables LockBit affiliate actors to remotely access systems while encrypting network traffic. | T1071.001 |
| WinSCP | Facilitates file transfer using SSH File Transfer Protocol for Microsoft Windows. | Enables data exfiltration via the SSH File Transfer Protocol. | T1048 |
IOCs
IoCs from US Governmental Agencies’ #StopRansomware initiation report on LockBit 3.0;
File Sharing Sites:
- https://www.premiumize[.]com
- https://anonfiles[.]com
- https://www.sendspace[.]com
- https://fex[.]net
- https://transfer[.]sh
- https://send.exploit[.]in
Freeware and Open-Source Tools:
- Chocolatey
- FileZilla
- Impacket
- MEGA Ltd MegaSync
- Microsoft Sysinternals ProcDump
- Microsoft Sysinternals PsExec
- Mimikatz
- Ngrok
- PuTTY Link (Plink)
- Rclone
- SoftPerfect Network Scanner
- Splashtop
- WinSCP
Mutex:
- Global
UAC Bypass via Elevated COM Interface:
- C:WindowsSystem32dllhost.exe
Volume Shadow Copy Deletion:
- Select * from Win32_ShadowCopy
Registry Artifacts:
- HKCR.
- HKCRDefaultIcon
- HKCUControl PanelDesktopWallPaper
- SOFTWAREPoliciesMicrosoftWindowsOOBE
- SOFTWAREMicrosoftWindows NTCurrentVersionWinlogon
IoCs from the SOCRadar Platform:
| Type | Value |
| IP | 212[.]102[.]39[.]138 |
| IP | 194[.]32[.]122[.]35 |
| IP | 178[.]175[.]129[.]35 |
| IP | 178[.]162[.]209[.]138 |
| IP | 178[.]162[.]209[.]137 |
| IP | 172[.]93[.]181[.]238 |
| IP | 156[.]146[.]41[.]94 |
| IP | 216[.]24[.]213[.]7 |
| IP | 37[.]46[.]115[.]29 |
| IP | 37[.]46[.]115[.]26 |
| IP | 37[.]46[.]115[.]24 |
| IP | 37[.]46[.]115[.]17 |
| IP | 37[.]46[.]115[.]16 |
| IP | 212[.]102[.]35[.]149 |
| IP | 178[.]175[.]129[.]37 |
| IP | 91[.]90[.]122[.]24 |
| SHA256 | 5fff24d4e24b54ac51a129982be591aa59664c888dd9fc9f26da7b226c55d835 |
| SHA256 | bb574434925e26514b0daf56b45163e4c32b5fc52a1484854b315f40fd8ff8d2 |
| SHA256 | 9a3bf7ba676bf2f66b794f6cf27f8617f298caa4ccf2ac1ecdcbbef260306194 |
| SHA1 | e141562aab9268faa4aba10f58052a16b471988a |
| SHA1 | 3d62d29b8752da696caa9331f307e067bc371231 |
| SHA1 | 3d62d29b8752da696caa9331f307e067bc371231 |
| MD5 | 03f82d8305ddda058a362c780fe0bc68 |
| MD5 | fd8246314ccc8f8796aead2d7cbb02b1 |
| MD5 | f41fb69ac4fccbfc7912b225c0cac59d |
| MD5 | ee397c171fc936211c56d200acc4f7f2 |
| MD5 | dfa65c7aa3ff8e292e68ddfd2caf2cea |
| MD5 | d1d579306a4ddf79a2e7827f1625581c |
| MD5 | b806e9cb1b0f2b8a467e4d1932f9c4f4 |
| MD5 | 8ff5296c345c0901711d84f6708cf85f |
| MD5 | 8af476e24db8d3cd76b2d8d3d889bb5c |
| MD5 | 6c247131d04bd615cfac45bf9fbd36cf |
| MD5 | 58ea3da8c75afc13ae1ff668855a63 |




































