
Russia-Linked APT Group Gamaredon Starting Extortion 30-50 Minutes After First Initial Access
The threat group, Gamaredon, linked to Russia, has been observed engaging in data exfiltration activities shortly after gaining initial access to targeted systems. The Computer Emergency Response Team of Ukraine (CERT-UA) recently released an analysis of the group, stating that emails and messages in popular messengers like Telegram, WhatsApp, and Signal are the primary means of initial compromise. In most instances, the group gains access by utilizing previously compromised accounts.
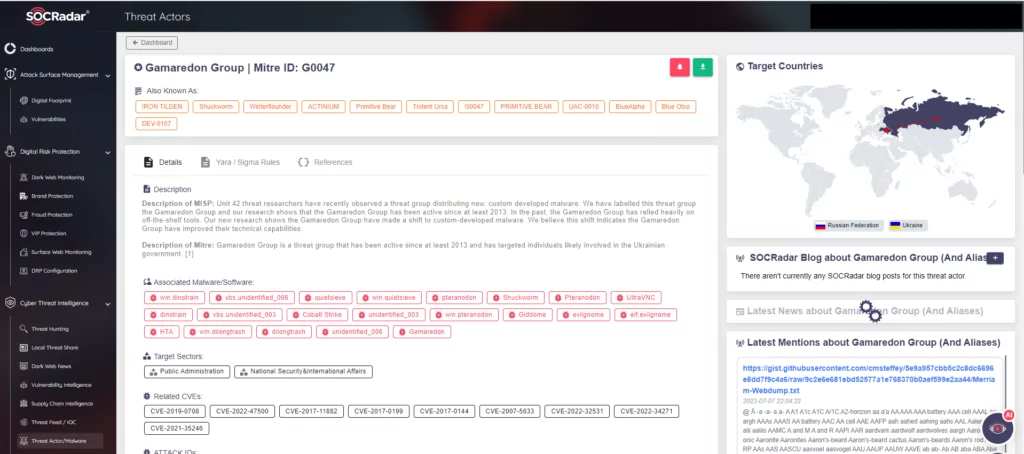
Gamaredon, also known by various aliases such as Aqua Blizzard, Armageddon, Shuckworm, or UAC-0010, is believed to be a state-sponsored actor with affiliations to the SBU Main Office in the Autonomous Republic of Crimea. This region was annexed by Russia in 2014. The group’s operations have led to the infection of thousands of government computers.
Since the beginning of the Russo-Ukrainian war in February 2022, Gamaredon has been among the numerous Russian hacking groups that have continued to operate actively. Utilizing phishing campaigns, the group delivers PowerShell backdoors like GammaSteel to perform reconnaissance and execute further commands. The group’s most dangerous characteristic lies in their ability to complete the extortion process within a concise timeframe of 30 to 50 minutes after infiltrating the target system.
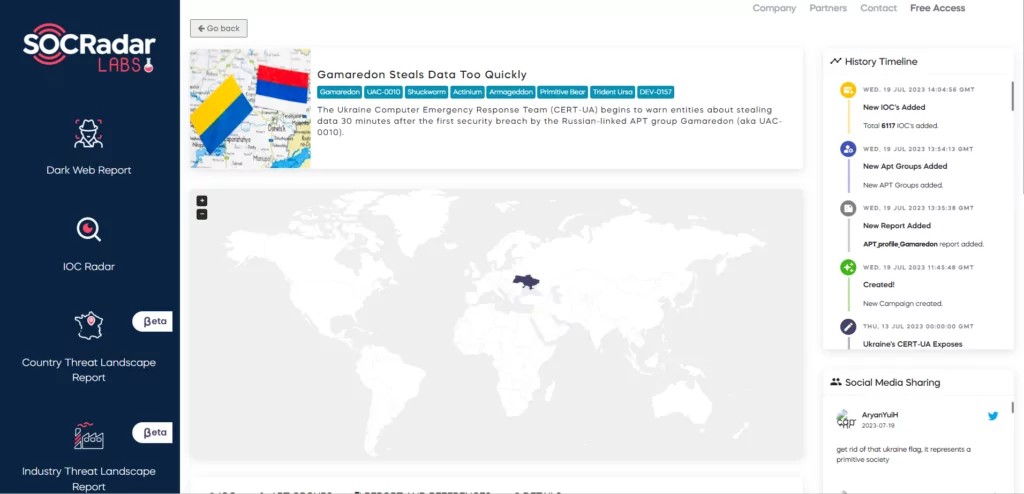
Detailed information regarding this ongoing campaign, including campaign details, YARA Rules, IoCs (Indicators of Compromise), and TTPs (Tactics, Techniques, and Procedures), can be accessed for free on SOCRadar Labs. For more comprehensive information about the Gamaredon, you may explore the SOCRadar Platform.




































