Third-Party Breach Led to Exposure of 9M AT&T Customers’ Information
Recently, AT&T revealed that a data breach in January compromised the personal information of about 9 million of their customers. The breach was caused by a marketing vendor’s hack, and as a result, some Customer Proprietary Network Information (CPNI) was accessed.
The exposed CPNI data includes customer first names, wireless account numbers, wireless phone numbers, and email addresses. However, the breach did not expose credit card information, social security numbers (SSN), account passwords, or other sensitive personal information.
AT&T has verified that some affected customers had their personal information exposed, which pertains to a few years back, including their rate plan names, past due amounts, monthly payment amounts, various monthly charges, and minutes used.
Recommendations
AT&T advises affected customers to toggle off CPNI data sharing on their accounts by making a CPNI Restriction Request. This will reduce the risk of exposure to third-party marketing in the future if AT&T uses the data for this purpose.
AT&T has not disclosed further information about the incident, and it is unknown which vendor’s breach led to the exposure of this data.
What Are the Risks?
Just a few months ago, AT&T denied experiencing a data breach when a threat actor tried to sell a database, claiming it contained the personal information of 70 million of AT&T’s customers.
Threat actors can easily conduct phishing scams using the exposed information, so be wary of any suspicious activity. If any of the sensitive information was compromised in the incident, organizations should consider taking proactive steps to protect it, such as changing passwords and monitoring credit card leaks.
It is also worth noting that threat actors did not breach AT&T’s systems in this vendor security incident. Still, vendor hacks pose a significant risk, and third-party intelligence is essential for avoiding them.
How Can SOCRadar Help?
SOCRadar Labs’ “Account Breach” tab can assist you in identifying any data leaks relating to you on the intranet, dark web, and other channels.
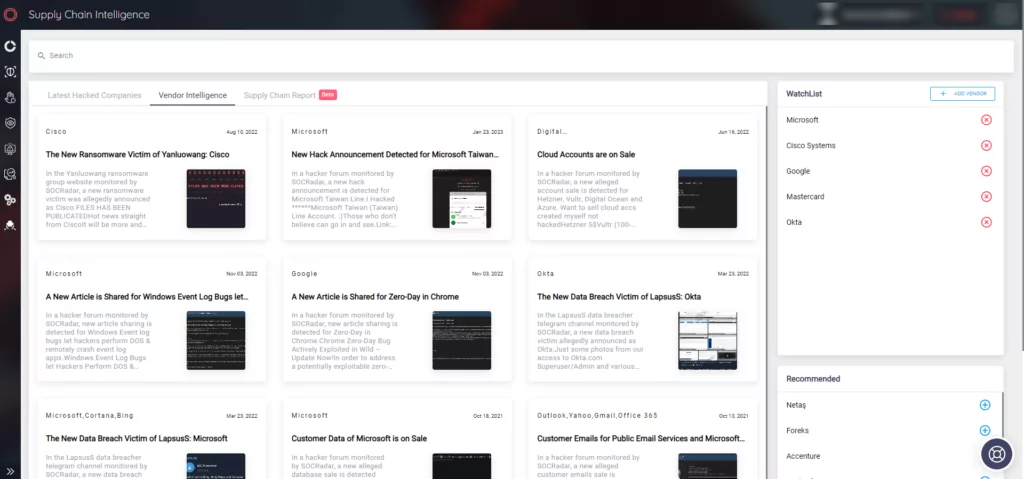
SOCRadar’s platform also includes a Supply Chain Intelligence tab, where you can find the most recently hacked companies and vendors.