VMware Patches Critical RCE Vulnerabilities in vRealize Log Insight
UPDATE (February 1, 2023):
Proof-of-concept (PoC) code for a VMware vRealize Log Insight vulnerability chain has been made available by researchers.
VMware patched several vulnerabilities found in its vRealize Log Insight appliance. The vulnerabilities are identified as CVE-2022-31704, CVE-2022-31706, CVE-2022-31710, and CVE-2022-31711.
The vRealize Log Insight by VMware is a virtual appliance that allows administrators to gather and monitor Syslog data, as well as analyze it. CVE-2022-31704 and CVE-2022-31706 are the most severe vulnerabilities in the product, both with a CVSS score of 9.8.
If exploited successfully, these two critical vulnerabilities could allow an unauthenticated, remote attacker to execute arbitrary code and gain complete control of a target system.
Details About the vRealize Log Insight Vulnerabilities
An unauthenticated attacker can exploit CVE-2022-31706 or CVE-2022-31704 to inject files into the operating system of a vulnerable device, which can lead to remote code execution. These vulnerabilities are easily exploitable, and they do not require user interaction.
One of the vulnerabilities, identified as CVE-2022-31706, is a directory traversal vulnerability that threat actors can use to inject files into the impacted appliances’ operating system to execute code remotely.
The second vulnerability, CVE-2022-31704, is a broken access control vulnerability that threat actors can exploit to gain remote code execution on exposed devices by injecting maliciously crafted files.
VMware also fixed the following vulnerabilities:
CVE-2022-31710 (CVSS score 7.5): It is a deserialization vulnerability that allows remote attackers to cause the deserialization of untrusted data, which may lead to a denial of service.
CVE-2022-31711 (CVSS score 5.3): A remote attacker could use this information disclosure vulnerability to gather private session and application data without authentication.
Proof-of-Concept Exploit
Horizon3 has published the proof-of-concept (PoC) exploit steps for the chain exploit, describing how it uses various Thrift RPC endpoints to perform remote code execution with root privilege.
Because vRealize Log Insight is unlikely to be accessible over the internet, the attacker must have some infrastructure or a network foothold to deliver malicious payloads; aside from that, the exploit is relatively simple to execute.
The procedures for combining the three CVEs (CVE-2022-31706, CVE-2022-31704, CVE-2022-31711) to obtain remote code execution are as follows:
- Creating a Thrift client and permitting unauthenticated access to the Log Insight Thrift server.
- Utilizing a legitimate Pak file to create a malicious tar file that contains a directory traversal.
- Uploading the malicious Pak file to /tmp/
.pak using remotePakDownloadCommand. - Using the pakUpgradeCommand to make the Pak file be extracted in the chosen place on the filesystem.
Is There a Mitigation Available?
VMware patched the vulnerabilities in vRealize Log Insight version 8.10.2 and issued an advisory to guide users through the upgrade process.
No reports of these vulnerabilities being exploited in the wild, but the company recommends patching them as soon as possible.
VMware has also provided a workaround for users who cannot apply the patches immediately. Use SSH to connect as root to each vRealize Log Insight node in your cluster and run the workaround scripts published by VMware.
Additionally, admins are urged to log the actions taken on each node where the workaround script was run in order to verify the workaround.
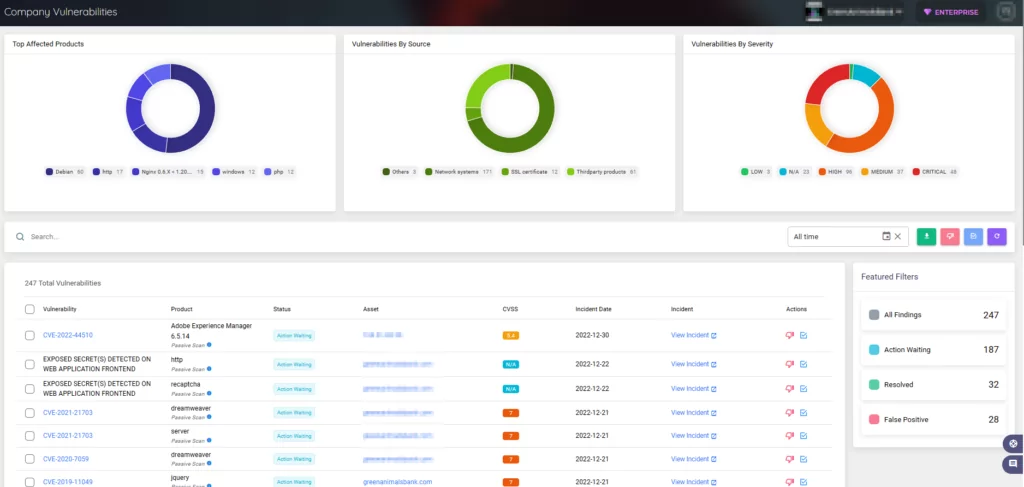
Don’t Let Vulnerabilities Compromise Your Organization
SOCRadar’s Vulnerability Intelligence can assist you in better managing vulnerability issues and prioritizing patches; you can search for and view detailed information about vulnerabilities on the platform. At the same time, its External Attack Surface Management (EASM) can discover your digital assets and alert you to any emerging issues.