
What Do You Need to Know About the Recent Operation of FSB Russia on REvil Ransomware Group
On January 14, 2022, the Russian Federal Security Service (FSB) arrested members of the REvilransomware gang at the request of US authorities. According to a statement from the FSB, a combined operation with the Russian Interior Ministry to disband the gang was initiated in five regions.
This has been an exciting move from Russia amid escalating conflict over Ukraine. Russia’s intelligence agency, the FSB, stated that the REvil group had “ceased to exist.” The organization announced that it had taken over 426 million rubles (£4 million), including roughly £440,000 in cryptocurrency. It also seized more than 20 “luxury automobiles” that had been bought with criminal money.
Who is REvil Ransomware Gang?
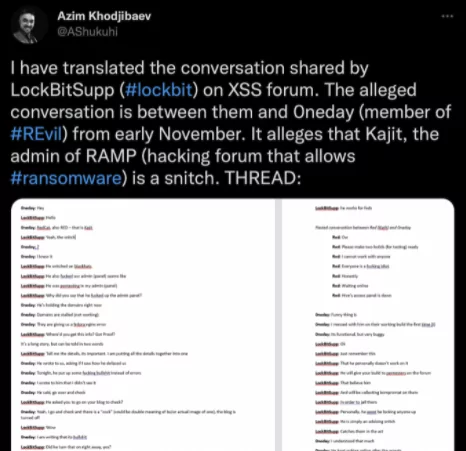
REvil is a well-funded illegal ransomware-as-a-service (RAAS) operation that rose to popularity after the fall of another ransomware organization, GandCrab, in April 2019. The REvil group is also known by various names, including Sodin and Sodinokibi.
REvil is a business that provides third-party hackers hacking technologies and other things. On the dark web, a portion of the Internet that search engines like Google don’t track, REvil members have built online infrastructure for other hackers to upload stolen documents and collect ransomware payments from victims. REvil takes a roughly 20% share of any ransomware payments in exchange for using its services and malware, while its affiliate hackers pocket the other 80%.
REvil has a reputation for attempting to extort much higher sums of money from its corporate victims than is typical of other attacks. Underground cybercrime forums are actively advertised as the most outstanding choice for targeting business networks, where more money is to be made than infecting residential systems.
Outstanding Attacks of REvil
REvil ransomware was released on the networks of hundreds of managed service providers on July 2, 2021, via Kaseya desktop management software. REvil wanted $70 million to restore data that had been encrypted. As a result, the Swedish supermarket chain Coop was obliged to close 800 locations over many days.
JBS S.A. was hit by ransomware on May 30, 2021, forcing the company to temporarily shut down its beef plants in the United States and disrupt operations at poultry and pork plants. A few days later, the White House claimed that REvil was behind the cyberattack on JBS S.A. In a follow-up statement on Twitter, the FBI verified the link. JBS paid REvil an $11 million ransom in Bitcoin.
The Federal Security Service (FSB) and the Prominence of the Recent Operation on REvil
Federal Security Service (FSB), Russian Federalnaya Sluzhba Bezopasnosti, originally Federal Counterintelligence Service (1994–95), Russian internal security and counterintelligence service established in 1994. FSBone of the Soviet-era KGB’s successor agencies. It oversees military counterintelligence, anti-terrorism, and monitoring. Counterintelligence is a strong point for the FSB.
The FSB said in a statement on January 14th that the operation “suppressed the illegal actions” of members of the group during raids on 25 residences, resulting in the arrest of 14 people. The arrests were an unusual public display of US-Russian cooperation when the two countries were at odds over Ukraine. The members of the group have been charged and could face up to seven years in prison, according to the FSB.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free


































