Dark Web Profile: Who is ‘Stormous Ransomware’ Claiming to Leak Epic Games Information
[Update] July 28, 2023: The Stormous ransomware gang has recently made a comeback. Added the subheading: “Stormous Ransomware Gang Resurfaces with New Data Leak Site and Partnerships”
The Stormous ransomware group has touted itself as the actor behind some attacks since early 2022. Discussions began to revolve around some of these attacks being carried out by other threat actors, with the Stormous group making it seem like they did it.
Finally, Stormous claimed to obtain 200GB of data belonging to Epic Games. We share with you some information obtained by SOCRadar analysts by monitoring the dark web.
Who is Stormous Ransomware Group?

The Stormous ransomware group has sought to make its name by taking advantage of the rising tensions between Russia and Ukraine. SOCRadar analysts think the group is trying to make a name for itself by using the agenda of groups like Conti.
Threat intelligence experts have yet to agree on whether the Stormous group makes these claims for political agenda or forward-looking financial gain. However, the general opinion is that this is an advertising campaign.
What are Stormous Group’s Claims?
The Stormous group claims to target western countries and companies. There are some recorded attacks so far, but it should be noted that these are dubious. There has been no confirmation from the companies the group claims to have attacked.

The Stormousannounced on March 1 that they had attacked the network of the Ministry of Foreign Affairs of Ukraine. They claimed to have obtained a lot of sensitive data such as phone numbers, emails, passwords, and card numbers from the ministry’s database.
However, it was known that this data was circulating on the dark web for a long time and was shared for free. This is “Is Stormous a scam?” brought up the argument.
Epic Games Alleged Data Breach
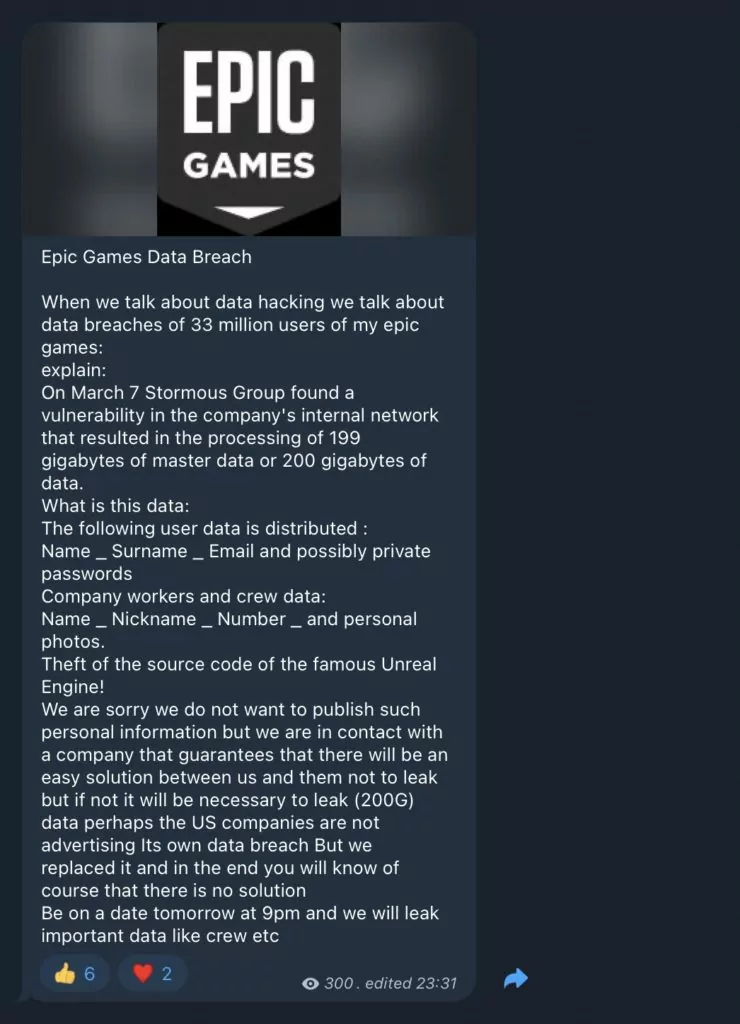
The Stormous gang came to the fore with the Epic Games breach. The threat actor claimed that they discovered a vulnerability in the company’s internal network and stole nearly 200 gigabytes of data, including the information of 33 million users. They added that they would continue to leak data about company employees, not users’ personal information.
In the post shared by the group on Telegram, it seems that they do not share any content about the leaked data. This again brings to mind the possibility of a scam.
Is Stormous Ransomware a Scam?
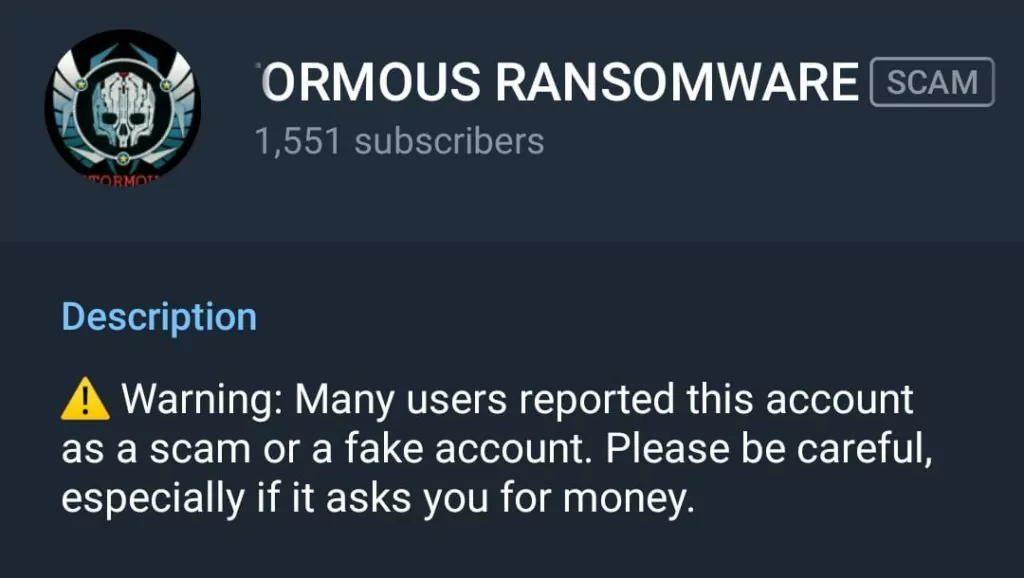
Attacks by the Stormous ransomware group are also called “scavenger operations” in cybersecurity. These operations are carried out by targeting companies whose data was leaked by another threat actor before. However, the general opinion about Stormous is that it is a scam.
As we mentioned before, the group may be trying to create an agenda to make its name known and may want to consolidate its reputation with actual attacks later on. For this reason, SOCRadar analysts have put the group under observation.
Stormous Ransomware Gang Resurfaces with New Data Leak Site and Partnerships
The Stormous ransomware gang, allegedly active since 2021, has recently made a comeback with their previously inaccessible data leak site, which now features new pages and information. Among the additions are a main page listing their recent victims, a “Shop” section offering data for sale from specific companies, and a “Job Application” page seeking individuals skilled in extortion and hacking.
Additionally, the group has formed a partnership with GhostSec, which they announced on July 13, 2023, via GhostSec’s Telegram channel. Together, they have declared their collaboration to target organizations in Cuba, and they have listed three Cuban government ministries as their targets on their respective platforms. Also, GhostSec has expressed potential collaboration for future joint operations targeting other countries.
Despite presenting themselves as a ransomware operation, it remains uncertain whether Stormous actually uses ransomware in their attacks. Some of the data they have claimed to steal and share has been found to be fake, raising doubts about the legitimacy of their claims and intrusions.




































