|
Reports about Australia |
Conclusions |
|
National Cyber Power Index 2022 |
Australia is raised to number 5 in 2022 from number 10 in 2020. Australia is the top country for cyber defense and number 4 for intelligence. However, Australia is the last country under the “Financial” category among the 30 countries. |
|
Australia Digital Readiness Index 2022 |
Australia is down to number 16 from number 12 in the previous report. |
|
Proofpoint 2022 Voice of the CISO |
77% of Australian chief information security officers (CISOs) reported their organizations are unprepared to detect, deter, and recover from a cyber assault. The highest rate among 14 countries, and the rate is up 21% from the 2021 survey. |


Australian Approach After the Recent Cyber Attacks: Hack the Hackers
Recently, one of the attention-grabbing countries in the cyber world is Australia. However, Australia’s cyber capabilities and potential in published reports are conflicting. Additionally, the recent attacks on Australian businesses like Optus and Medibank and the Australian Government’s responses were covered widely in local and international media.
On the other hand, Australia has recent and unwanted attention from threat actors. Between July 2021 and June 2022, according to research by Imperva, there was an 81% increase in cyber security events in Australia.
Recent Breaches and Attacks
Medibank

One of the most significant Australian private health insurance companies, Medibank, was breached by a ransomware group with ties to the defunct REvil gang in October 2022. Medibank acknowledged that the group had obtained approximately 9.7 million customer details for nearly 500,000 customers. You can read about the timeline and further details here.
Mydeal.com.au
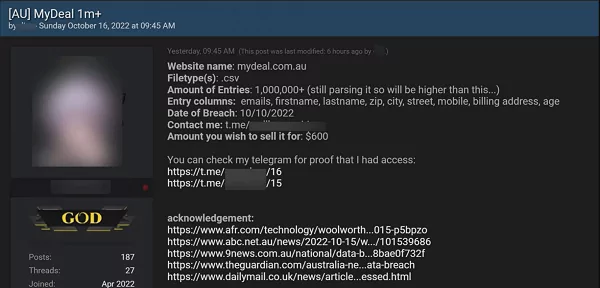
2.2 million customers were impacted by a data leak from mydeal.com.au. Australian retail site MyDeal connects online shoppers with nearby merchants, and it is a subsidiary of Woolworths.
Woolworths’ MyDeal reported a data breach impacting its customers. MyDeal stated that they “identified that the threat actors used a compromised user credential to gain unauthorized access to its Customer Relationship Management (CRM) system resulting in the exposure of some customer data.” On a hacker forum, a person was attempting to sell stolen data. Personal information like names, email addresses, phone numbers, delivery addresses, and, in some cases, birth dates were exposed.
Optus
Optus disclosed a data breach involving around 2.1 million user records in September 2022. Identification numbers and other personal information about customers were made public. The data breach, which Optus disclosed in late September and during which they were double extorted, was what led to the release. According to a media notice from Singtel, the owner of Optus, “Approximately 1.2 million customers have had at least one number from a current and valid form of identification, and personal information, compromised.” Singtel also stated that they are working with agencies to rectify the issue. The alert also mentions that part of the exposed user data was invalid and that roughly 900,000 consumers’ expired IDs were also impacted. The firm also stated that it had informed users whose identification documents were compromised due to the attack. This contains the driver’s license, card information, and Medicare ID numbers.
The University of Western Australia

The University of Western Australia (UWA) also confirmed that it was a data breach victim, stating that attackers accessed both present and former students’ personal information in August 2022. UWA discovered unauthorized login activity to the university’s third-party student information management system. The stolen records include names, pictures, student ID and image, date of birth, contact information, and course information and grades.
Deakin University

In July 2022, Deakin University confirmed that nearly 47,000 current and former students were affected by a data breach, and 10,000 current students were the subject of a “smishing” attempt that used a legitimate communication channel. The attack happened after one of the staff member’s login information was stolen. The attacker was able to access information maintained by a third-party service using the stolen credentials, then sent to students through SMS. The attacker also gained access to the contact details of almost 47,000 current and past Deakin students. The contact details included:
- The student’s name.
- Student ID.
- Student mobile number.
- Deakin email address.
- Comments such as recent unit results.
The attacker downloaded all the information.
A New Australian Cyber Task Force
The Current Australian government has established a joint group to “hack the hackers” and prevent cyberattacks from happening in early November 2022. Government officials described the newly formed task force between the Australian Federal Police and the Australian Signals Directorate as a new paradigm of cyber-policing. 100 personnel from the two security agencies will initially make up the team, which will be a permanent operation. It will investigate threat actors and thwart their plans before they attack.
In addition to Australia’s strong history of investments in cyber and digital security, the joint task force will make threat actors think twice before attacking an Australian enterprise in the future. However, threat intelligence solutions with comprehensive dark web monitoring capabilities, such as SOCRadar, could help map out Australia’s current threat landscape.
Dark Web Radar
The SOCRadar Extended Threat Intelligence follows communication on the dark web using AI and analysts and presents its customers with custom filtration. For the first 11 months of 2022, 12,981 dark web post entry made to the SOCRadar platform. 211 were about Australia, making Australia the 14th most mentioned country in the SOCRadar Platform analytics.
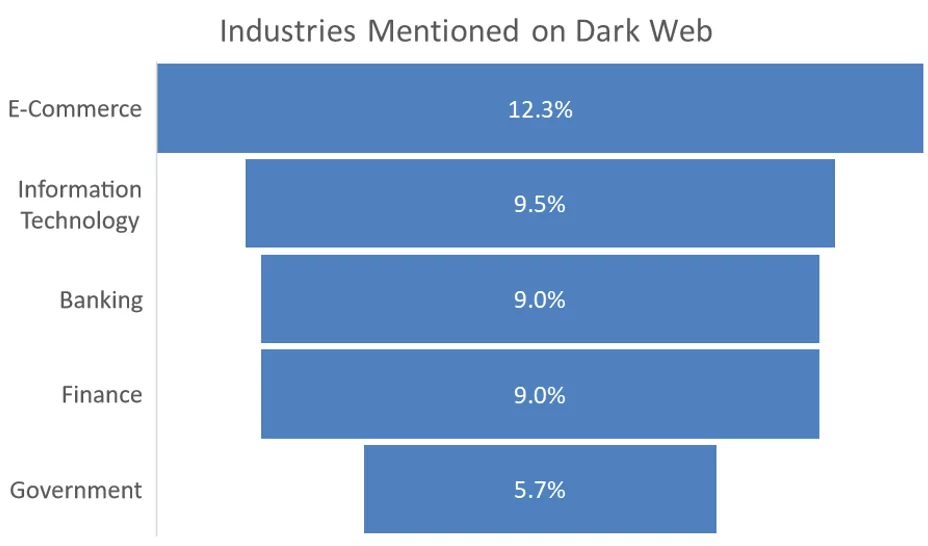
When we look at the posts mentioning Australia on the dark web, we can see that 12.3% of the post are talking about the e-commerce industry, and Information Technology, Banking, and Finance follow it.
Ransomware Statistics
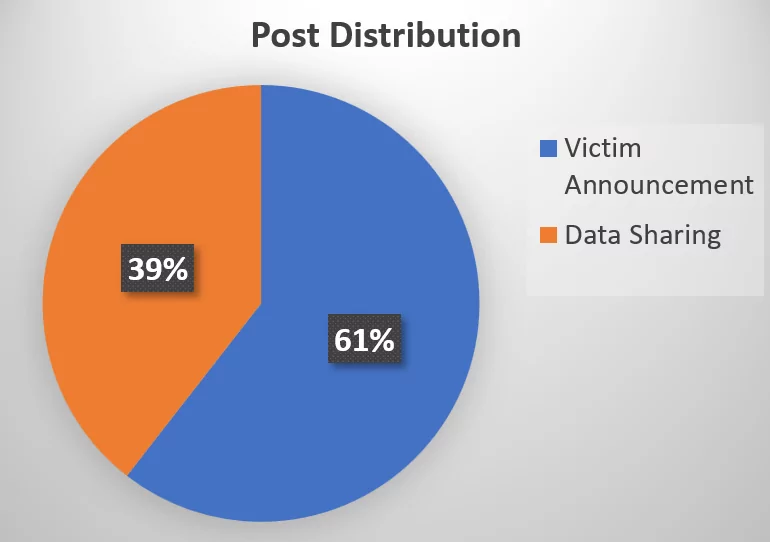
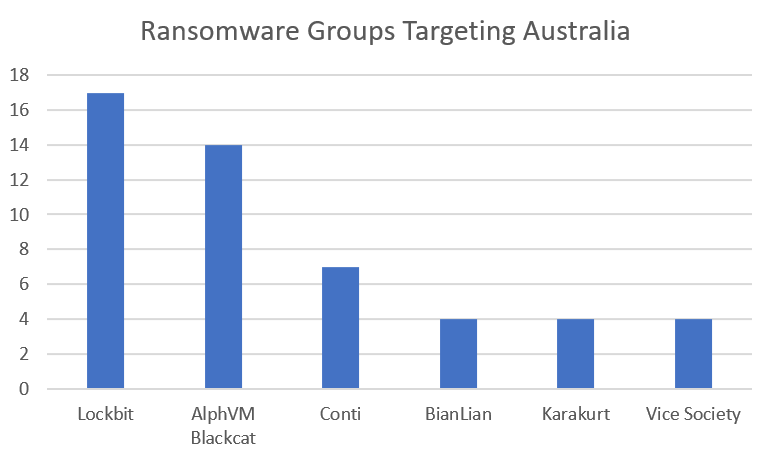
As an XTI solution, SOCRadar also follows ransomware attack posts in a separate category. During the first 11 months of 2022, 76 posts were recorded from various sources like dark web forums, Telegram channels, and blog sites affiliated with ransomware groups.
Recent attacks on Australian organizations show that Australia has become a focus for some threat actors. Even though Australia invested in cyber and digital security, there is still a long way to go against evolving and ever-changing cyber-attack surface. The Extended Threat Intelligence companies like SOCRadar aiming to stop attacks before they even start could help Australia in this journey to cyber resilience.
References:
- https://www.belfercenter.org/sites/default/files/files/publication/CyberProject_National%20Cyber%20Power%20Index%202022_v3_220922.pdf
- https://www.cisco.com/c/dam/m/en_au/digital-readiness/pdfs/cisco-aus-dri-report-2022.pdf
- https://www.proofpoint.com/sites/default/files/white-papers/pfpt-au-wp-voice-of-the-CISO-report.pdf
- https://www.itnews.com.au/news/student-details-photos-exposed-in-university-of-wa-data-breach-583398
- https://www.gizmodo.com.au/2022/07/deakin-university-data-breach/
- https://www.smh.com.au/politics/federal/hack-the-hackers-new-joint-taskforce-will-hunt-cybercriminals-before-they-strike-20221112-p5bxol.html