
Brute Ratel C4 Toolkit Gets Cracked and Distributed Online
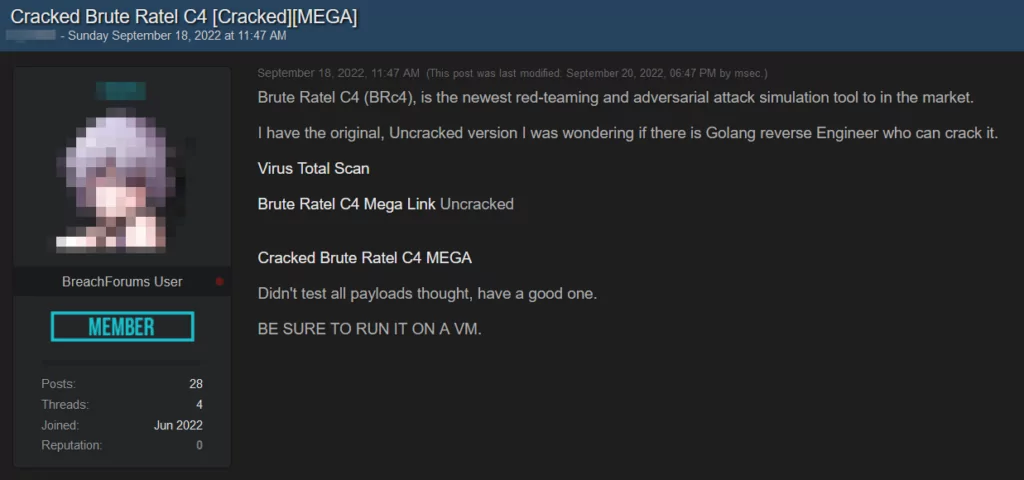
The cracked version of Brute Ratel C4 (BRC4) is currently being distributed on hacker platforms for free. Posts spreading it have been seen in multiple hacking forums and Telegram and Discord channels.
BRC4 post-exploitation toolkit was originally created for red team researchers to replace Cobalt Strike in penetration testing utilities.
Cobalt Strike’s cracked version has also been abused by many threat actors and in ransomware operations; therefore, some threat actors have been moving to Brute Ratel to avoid the detection risks brought along with the attention on Cobalt Strike.
How Was It Cracked?
Brute Ratel requires licensing for its use. At first, hackers could acquire leaked licenses for it. Some also created fake companies to get around the license requirements.
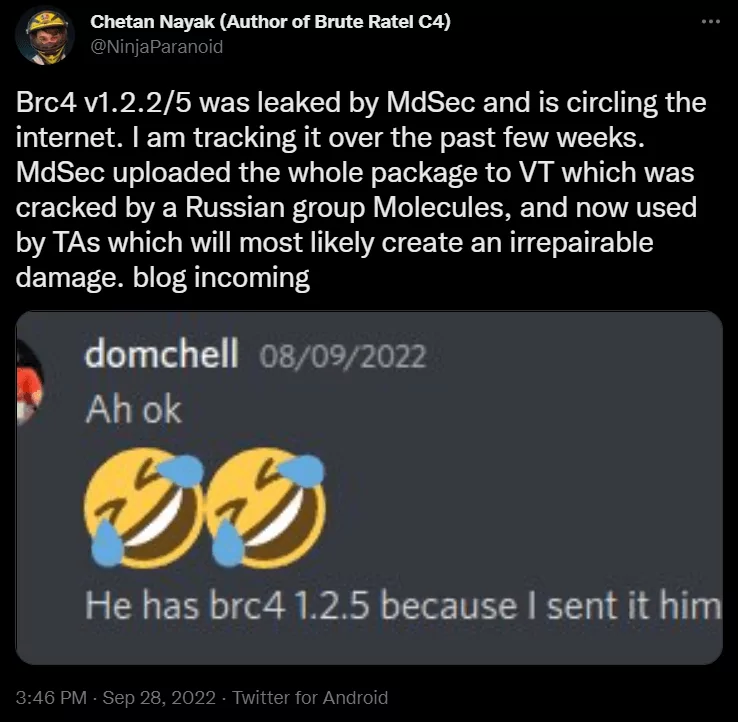
Developer of BRC4, Chetan Nayak, explained that the toolkit was cracked by the Russian group “Molecules” to remove its license validation after its uncracked version (bruteratel_1.2.2.Scandinavian_Defense.tar.gz) was uploaded to VirusTotal in mid-September. Nayak also accused MdSec of having done the upload, but it is still unclear who uploaded the files.
Researcher Will Thomas stated in his blog: “One of the most concerning aspects of the BRC4 tool for many security experts is its ability to generate shellcode that is undetected by many EDR and AV products.”, further adding it would give attackers enough time to acquire initial access and persistence. He also recommended using behavior-based detection.
Check for indicators of compromise in our previous Brute Ratel blog post.



































