Critical Vulnerabilities in Atlassian and Apple Products: Apple Zero-Day Actively Exploited (CVE-2023-38606)
Atlassian and Apple have each promptly addressed critical vulnerabilities threatening their products, including an actively exploited zero-day bug.
Atlassian’s updates tackled vulnerabilities in Atlassian Confluence Server, Data Center, and Bamboo Data Center,potentially leading to remote code execution, while Apple’s updates addressed various security vulnerabilities in numerous products.
Read the blog post to learn more about these critical vulnerabilities and how to protect your systems from potential threats.
Atlassian Releases Critical Updates for Confluence and Bamboo Products
Atlassian has released updates to address security flaws in AtlassianConfluence Server, Data Center, and Bamboo Data Center products. These flaws could lead to remote code execution on vulnerable systems. The identified flaws and their fixes are as follows:
- CVE-2023-22505 (CVSS score: 8.0): RCE in Confluence Data Center and Server (Fixed in versions 8.3.2 and 8.4.0)
- CVE-2023-22508 (CVSS score: 8.5): RCE in Confluence Data Center and Server (Fixed in versions 7.19.8 and 8.2.0)
- CVE-2023-22506 (CVSS score: 7.5): Injection, RCE in Bamboo (Fixed in versions 9.2.3 and 9.3.1)
Both CVE-2023-22505 and CVE-2023-22508 allow an authenticated attacker to execute arbitrary code without requiring user interaction.
CVE-2023-22506 allows an authenticated attacker to modify system call actions and execute arbitrary code without requiring user interaction.
Apple Addresses Zero-Day Bug (CVE-2023-38606) and Multiple Vulnerabilities
Apple has released security updates for various operating systems, including iOS, iPadOS, macOS, tvOS, watchOS, and Safari. These updates address multiple security vulnerabilities, one of which is a zero-day bug that has been actively exploited.
The specific vulnerability, known as CVE-2023-38606, is found in the kernel and allows a malicious app to potentially modify sensitive kernel state. Apple has fixed this issue by improved state management.
The company confirmed this issue had been actively exploited before iOS 15.7.1. The bug is linked to “Operation Triangulation,” a cyber espionage campaign targeting iOS devices since 2019 with zero-click exploits.
The updates are available for various devices and operating systems:
- iOS 16.6 and iPadOS 16.6 – iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
- iOS 15.7.8 and iPadOS 15.7.8 – iPhone 6s (all models), iPhone 7 (all models), iPhone SE (1st generation), iPad Air 2, iPad mini (4th generation), and iPod touch (7th generation)
- macOS Ventura 13.5, macOS Monterey 12.6.8, and macOS Big Sur 11.7.9
- watchOS 9.6 – Apple Watch Series 4 and later
- tvOS 16.6 – Apple TV 4K (all models) and Apple TV HD
Identify and Mitigate Vulnerabilities with SOCRadar
SOCRadar’s Vulnerability Intelligence service assists in managing vulnerabilities and prioritizing patches. The platform allows effortless searching and access to detailed information about vulnerabilities, enabling users to stay ahead of potential threats.

The External Attack Surface Management (EASM) service also plays a crucial role in security. With EASM, SOCRadar diligently monitors the digital landscape, timely alerting users to any emerging issues that may pose a security risk. Customers can rely on SOCRadar’s commitment to ensuring proactive protection for their online presence.
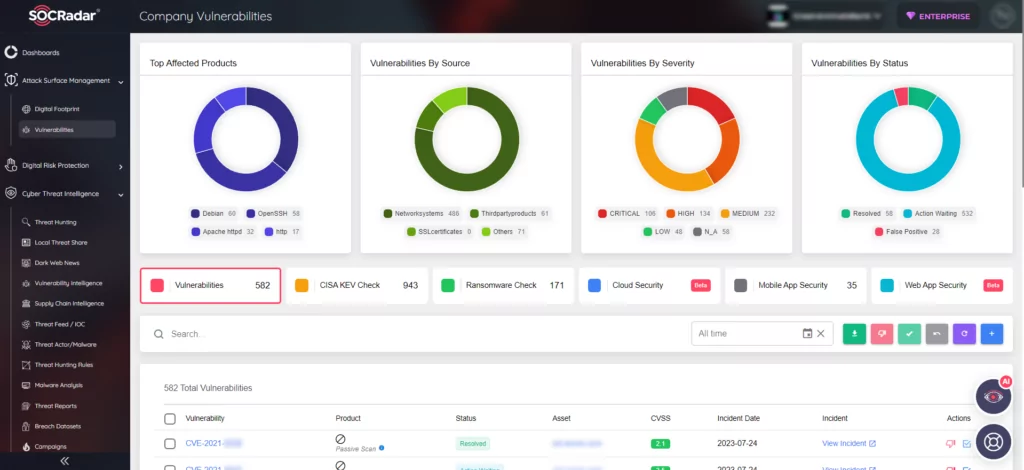
Sign up for a free edition of the SOCRadar to learn more and stay up to date on the latest vulnerabilities.




































