Cyber Extortion Meets Regulatory Pressure: ALPHV’s SEC Complaint Against MeridianLink
The ALPHV/BlackCat ransomware group, known for their vicious ransomware attacks, has recently taken a surprising action by filing a complaint with the U.S. Securities and Exchange Commission (SEC) against a company they allegedly hacked, MeridianLink, a company offering digital services to banks and other financial groups.
On November 7, ALPHV allegedly broke into MeridianLink’s system and then demanded a ransom, threatening to leak the company’s data according to databreaches.net. They claimed to have gotten the data without locking up the company’s systems, which is uncommon in these kinds of attacks but may not be intentional; encrypting files may be a lot harder than simply extorting data.
ALPHV’s Unconventional Strategy
What’s more uncommon here is that ALPHV has accused MeridianLink of not telling the public about the cyber attack. They even showed a screenshot of their complaint to the SEC, saying MeridianLink didn’t report the breach as they should have, according to the rules.
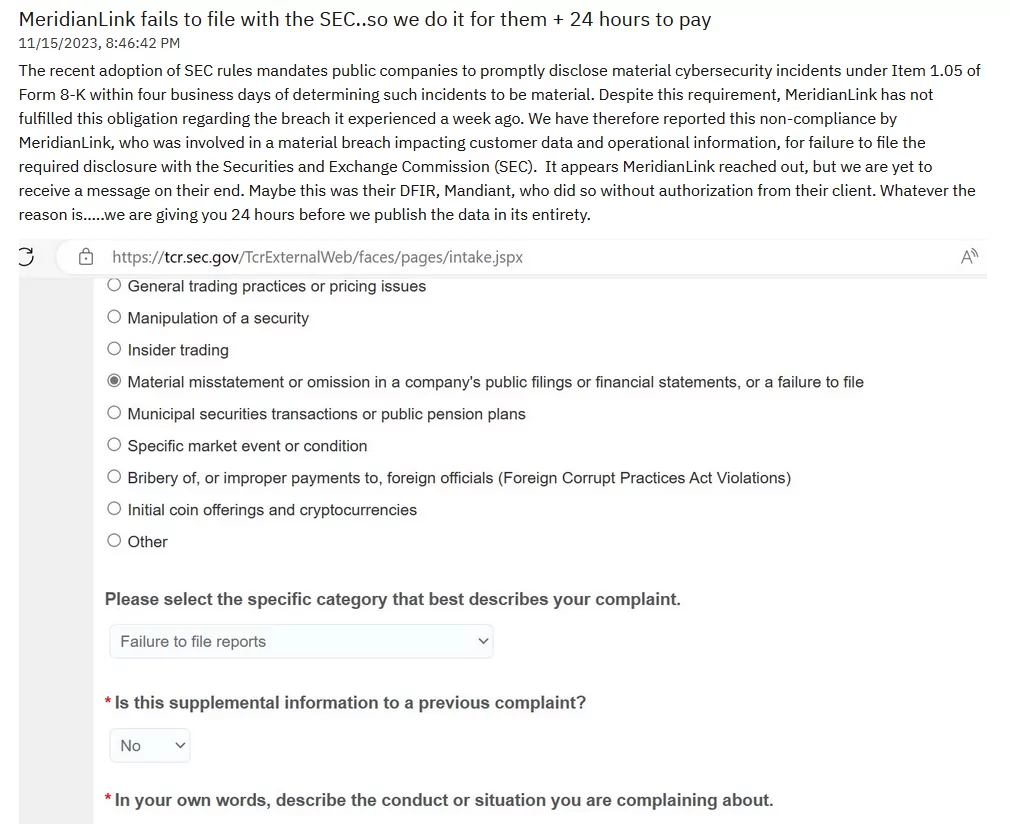
This move by ALPHV is happening at a time when the SEC is about to make new rules. Starting in mid-December 2023, companies will have to quickly tell the public about serious cyber attacks. By complaining to the SEC, ALPHV is putting pressure on MeridianLink about these new rules.
According to the statement of the victim for BleepingComputer, MeridianLink has responded by saying they quickly worked to stop the attack and are looking into it with outside experts. They are trying to find out if any customer data was affected and have said the attack didn’t cause much disruption to their business.
Legal Leverage and New Threats
In a similar strategy, another ransomware group, Ransomed.vc, used Europe’s GDPR laws to threaten companies. They threaten to reveal data unless the company pays a ransom, which could also lead to GDPR fines. These kind of actions indicate new methods that ransomware groups are operating. They are now using legal and regulatory rules to put more pressure on companies, mixing cybercrime with legal pressure.
The Snatch group is making various leak threats to get payments, even for the names of other ransomware groups. Some groups are ironically complaining to the legal authorities, and new and cheaper RaaS services are coming to light, as in the case of GhostLocker.
Additionally, in a separate event that we previously reported on, there were indications that a well-known data recovery company might have worked alongside North Korean hackers in the process of retrieving data.
So, the ransomware threat landscape is more volatile than ever. Thus, cybersecurity strategies are also trying to keep up with the changing tactics of threat actors. One example was this year’s global summit on cybersecurity, hosted by the White House and attended by over 40 countries; one of the key decisions was to refuse the payment of ransoms in ransomware attacks. Still, there may be a need for you to swear word and heart but taking action is more important than intentions.
Conclusion
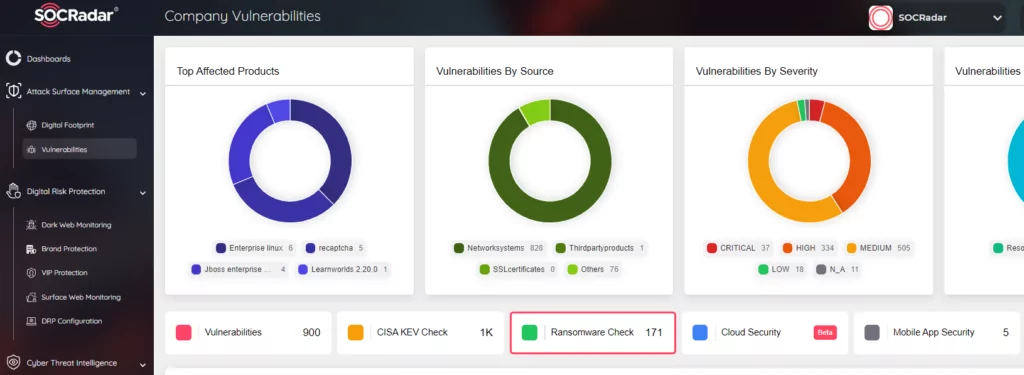
As the ransomware landscape continues to evolve with new tactics and threats, such as the actions of the ALPHV/BlackCat, it becomes increasingly crucial for companies to stay proactive in their cybersecurity measures. In this dynamic environment, the role of advanced cyber intelligence tools like SOCRadar becomes indispensable.
SOCRadar excels at the ransomware landscape, and we prepared a technical white paper with a 100M+ USD ransomware negotiator recently; for further analysis of the mentioned topics and the threat landscape, you should take a look at it. Moreover, SOCRadar XTI offers comprehensive cybersecurity solutions that can help organizations detect and respond to ransomware threats more effectively. By providing detailed intelligence and timely alerts about potential cyber threats, SOCRadar equips companies with the necessary information to preempt attacks or mitigate their impact.