Dark Peep #8: Pirouetting in the Shadows
In the sprawling digital metropolis, where neon lights cast long shadows and data streams flow like rivers through the cybernetic landscape, a new saga unfolds. Welcome, dear navigators of the net, to Dark Peep #8, a journey into the heart of digital intrigue and shadowy conflicts.
As the moon rises over this virtual skyline, we find our diverse cast of digital warriors and cunning tacticians taking their places on the grand stage of cyber espionage. The air crackles with the electric buzz of anticipation and the whispered secrets of the net. In the realm where binary codes hold power and every keystroke can tip the scales of fate, we delve into the tales of BianLian ransomware’s quest for unlikely comrades, including scribes of the modern age – the journalists.
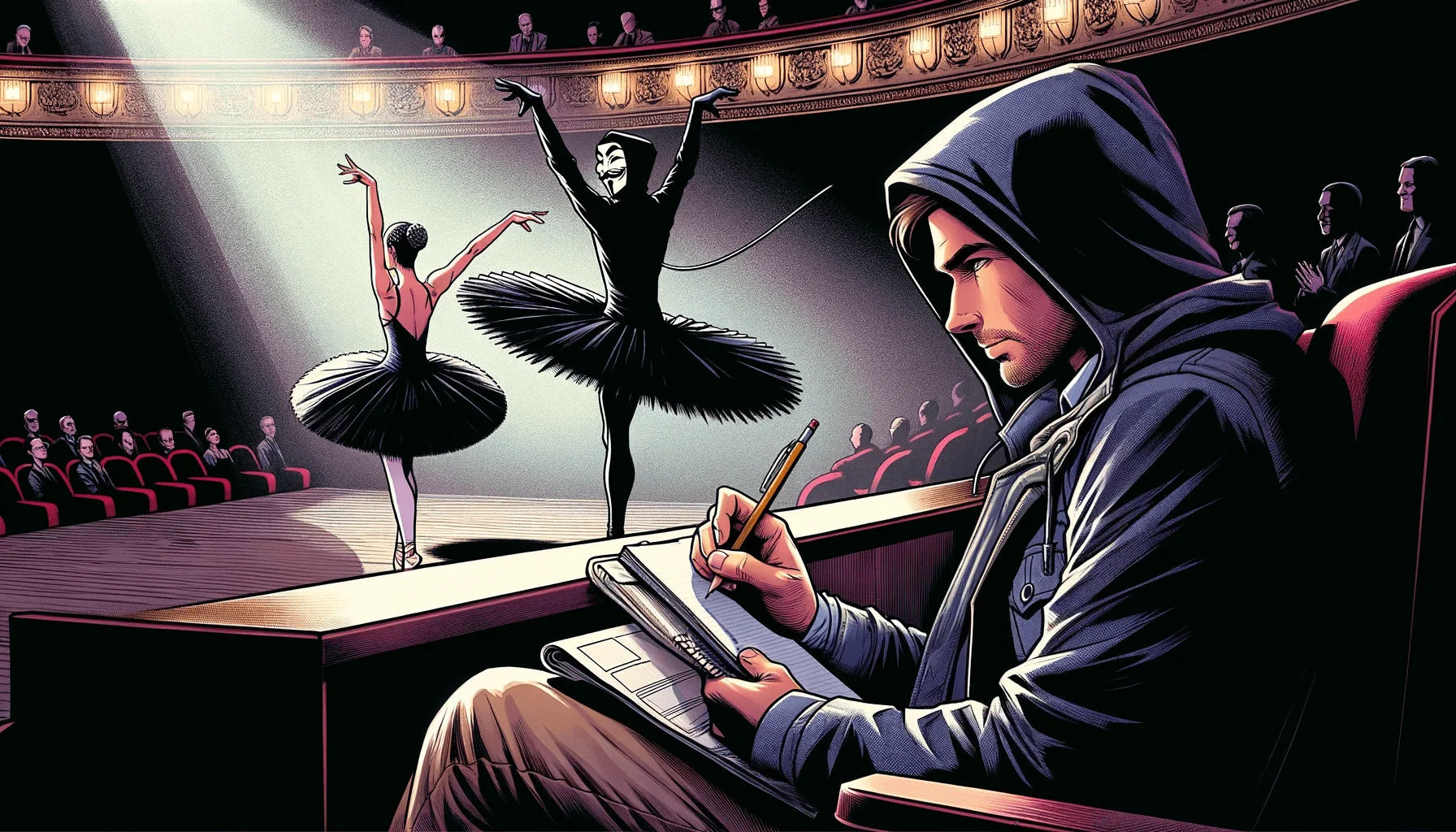
Fig. 1. Illustration of a threat actor attempting to ruin cyber art, and a journalist is helping the threat actor. (generated using OpenAI’s DALL-E 3)
Through the labyrinthine networks and hidden alleys of the internet, we track the elusive movements of LockBit, a master strategist in the high-stakes game of cyber chess. Here, alliances shift like sand, and loyalty is as fleeting as a cursor’s blink.
Each story we uncover is a piece of the puzzle, a fragment of the digital dream—or nightmare—that weaves the fabric of this hidden world. This is a place where heroes and villains swap masks, where the line between savior and hacker blurs, and where every byte of data holds a story waiting to be told.
So, sharpen your wits and open your minds, for “Dark Peep #8” invites you on an epic journey through the mysterious and ever-shifting landscape of the cyber world. In this realm of shadows and light, where truth intertwines with fiction, prepare to witness the untold stories of the digital age.
BianLian Ransomware is Hiring: The Role of Journalists in Cybercrime?
BianLian ransomware is currently seeking new team members. They are looking for targets’ providers, software engineers, pentesters, and journalists. To facilitate secure communication, BianLian has shared a TOX ID and an email address for potential candidates to reach out.
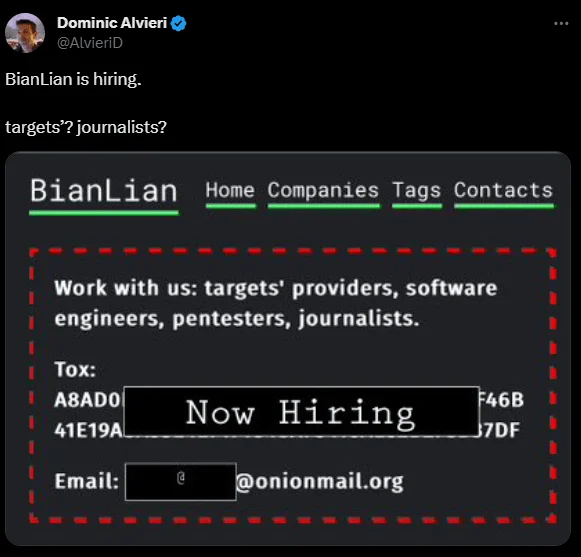
Fig. 2. BianLian’s hiring announcement (Source: X)
And about hiring journalists – it’s not for writing ransomware reviews (or is it?). This move could be BianLian’s play to sway public opinion or peek into the media’s playbook. It’s like they’re assembling a crew for a heist movie, each with their unique set of skills. It makes you wonder: what’s their endgame? A reminder to all, in the cyber world, expect the unexpected!
Raznatovic: The New Face of RansomedVC
Fig. 3. RandomedVC’s name change announcement (Source: X)
RansomedVC has made a comeback under a new guise, Raznatovic. A post on Ransomed[.]vc announced the change, featuring a Tor address.
LockBit’s Extended Deadline: A Peculiar Strategy Against La Policia Nacional de Peru
LockBit has added La Policia Nacional de Peru (National Police of Peru) in their victim list and has surprised cybersecurity observers by setting an unusually long deadline for La Policia Nacional de Peru, marking January 30, 2025, as the cut-off. This timeline starkly contrasts the average two-week ultimatum typically issued by LockBit, sparking a debate on the strategic implications behind this extended period.
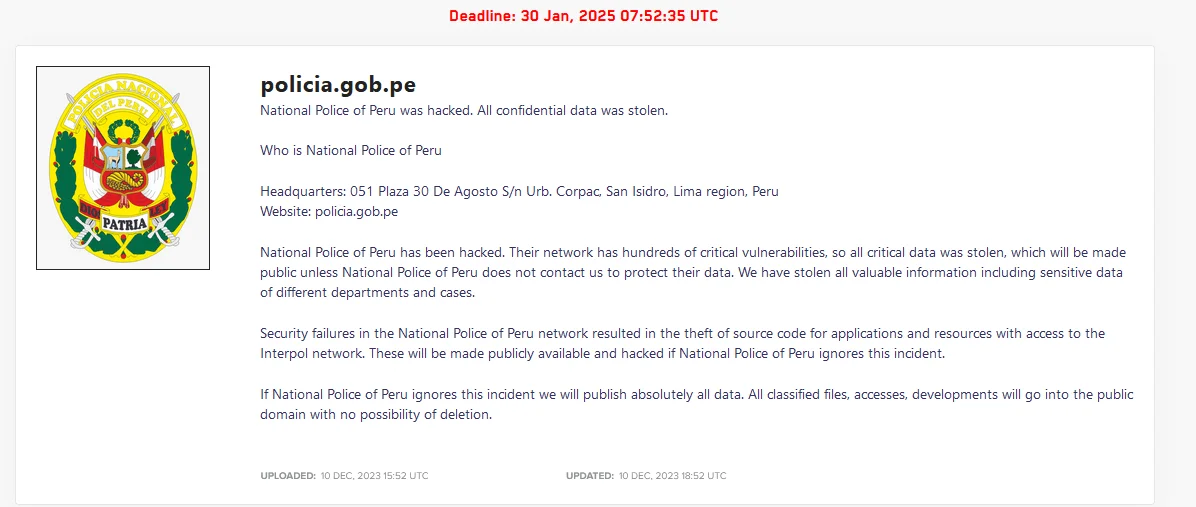
Fig. 4. LockBit’s dark web platform
The group asserts that they’ve exploited “hundreds of critical vulnerabilities” within the National Police’s network, resulting in extensive data theft. According to their claims, all valuable information, including sensitive details of various departments and cases, has been compromised. They stress the severity of the security lapses, noting the theft of source code for critical applications and access to the Interpol network.
This extended deadline could be a tactic to increase negotiation leverage, allow time for a complex data review, or intensify psychological pressure on the affected organization.
SkidSec Leaks Calls for Donations
SkidSec Leaks, a threat group, recently reached out on Telegram, seeking financial support They humorously framed their request for donations as supporting the “weaponization of autism,” referencing a stereotype about obsessive focus. The group has provided an XMR (Monero cryptocurrency) address for anyone interested in contributing to their cause.
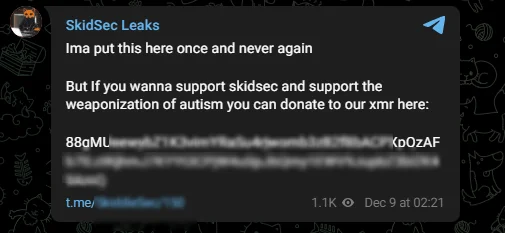
Fig. 5. SkidSec Leaks’ donation message
UserSec’s Quest for Cyber Mastery
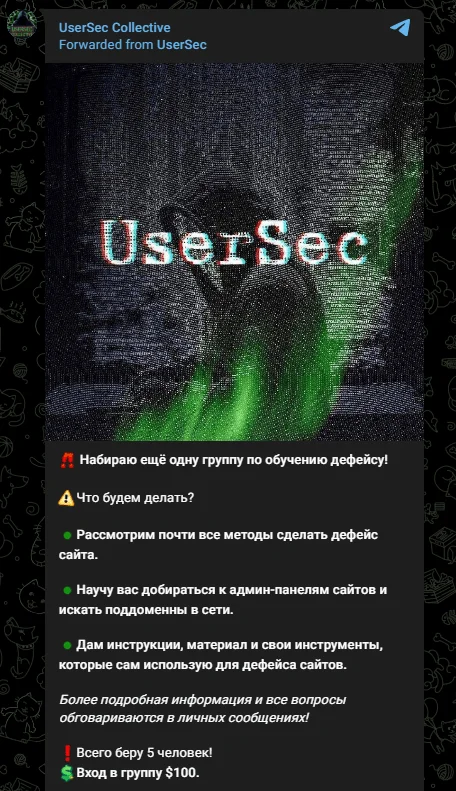
Fig. 6. UserSec’s announcement
In the ever-shifting shadows of the digital underground, a new chapter is unfolding with the pro-Russian threat group UserSec. Sources whisper of their latest endeavor: a covert recruitment drive, not for the many, but for the select few. This group, infamous for its brazen cyber escapades, is reportedly on the hunt for fresh talent to join their ranks in website defacement – an art, some might say, in the world of digital anarchy.
Poaching Talent in Ransomware Disarray
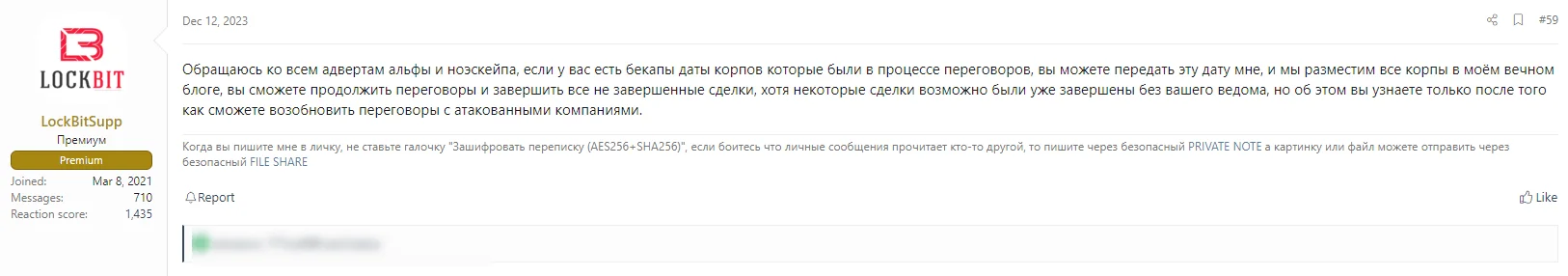
Fig. 7. LockBit’s comment in the Russian-speaking hacker forum
The LockBit ransomware group is making a bold move in the cybercrime world. After problems hit rival groups BlackCat/ALPHV and NoEscape, including a sudden shutdown of NoEscape’s websites and rumors of them stealing ransoms, LockBit is now trying to recruit their members.
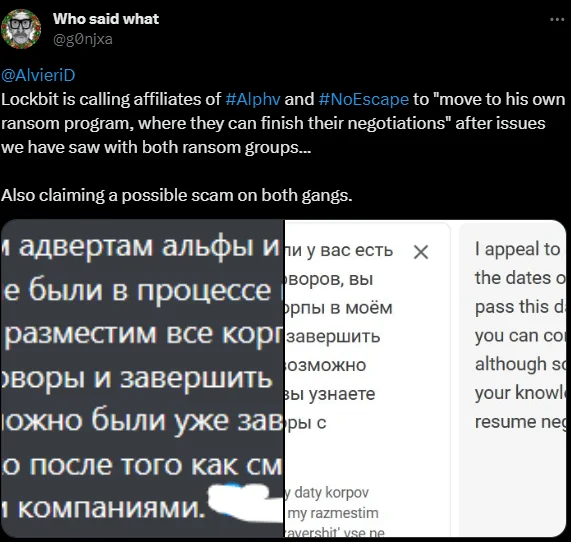
Fig. 8. A tweet about LockBit’s call to ALPHV and NoEscape affiliates (Source: X)
LockBit’s manager, LockBitSupp, has been actively inviting these stranded threat actors on a Russian forum. They’re offering them a chance to use LockBit’s tools and platforms to continue extorting their victims. This strategy seems to be working, as some victims previously targeted by BlackCat have been spotted on LockBit’s data leak site, showing a notable shift in the cybercrime scene.
UserSec Joins Forces with Anonymous Sudan

Fig. 9. The alliance of UserSec and Anonymous Sudan.
The dark web is abuzz with the latest development: a strategic alliance between UserSec and Anonymous Sudan. This union, merging pro-Russian UserSec with the elusive Anonymous Sudan, signals a significant shift in the cyber landscape.
A Sinister Step: The Ballet Competition Data Hack
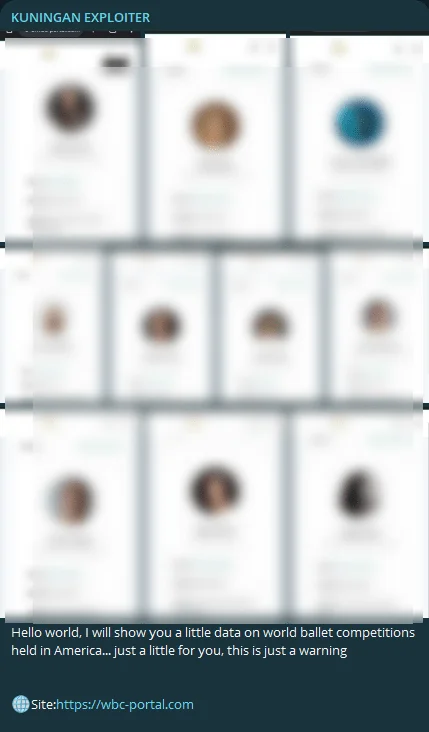
Fig. 10. Kuningan Exploiter’s statement
In a pirouette of cyber intrusion, a threat actor known as Kuningan Exploiter claimed a spotlight not on the stage, but in the digital shadows, allegedly breaching the World Ballet Competition Portal. Exhibiting an apparent disinterest in privacy and ethics, they shared screenshots that reveal intimate details of contestants – including photos, names, emails, phone numbers, birthdays, addresses, and last login data.
This intrusion is not just a violation of personal data but a stark reminder of the vulnerabilities in cyber defenses, even in seemingly less targeted sectors like the performing arts. It underscores the pressing need for robust cybersecurity measures across all domains, emphasizing that no arena, no matter how refined, is immune to the machinations of evil hackers.
Conclusion
As we close the curtains on this edition of Dark Peep, it becomes increasingly clear that the undercurrents of the Dark Web are as relentless and unpredictable as the ocean’s tides. With each passing moment, the landscape shifts, ushering in new alliances, threats, and strategies. In this ever-evolving realm of digital shadows, complacency is not an option.
To keep your finger on the pulse of these clandestine activities, we invite you to leverage the power of SOCRadar XTI’s Cyber Threat Intelligence module. Here, you’ll find the most up-to-date Dark Web News, offering a window into the depths of the cyber underworld. Stay informed, stay vigilant, and join us as we continue to navigate through these turbulent digital waters.
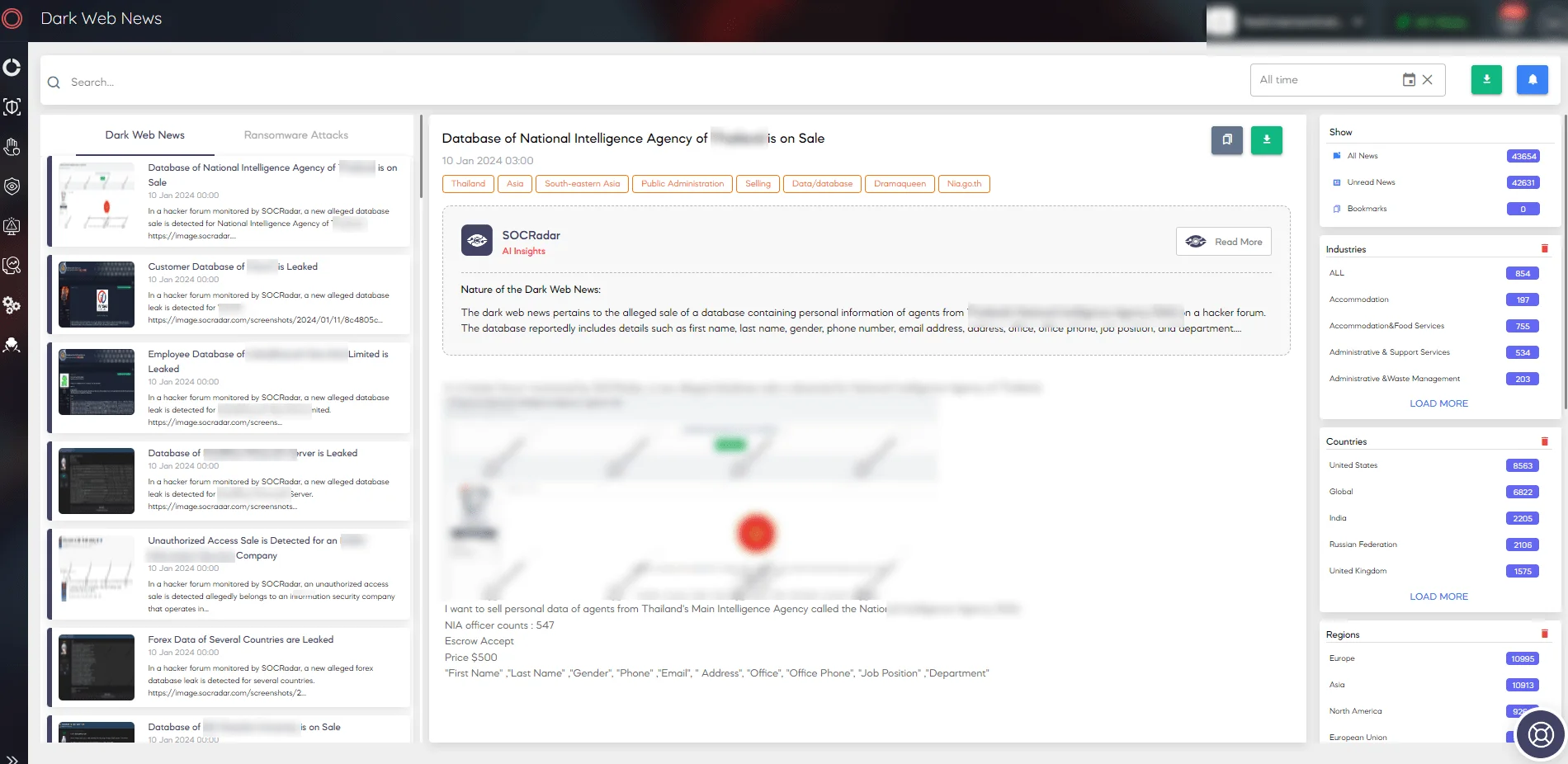
SOCRadar Dark Web News
Remember, in the world of cyber espionage and digital warfare, knowledge is not just power—it’s protection. Until next time, keep a watchful eye on the Dark Web’s ever-shifting landscape.




































