Dark Web Profile: NoEscape Ransomware
Avaddon, a notorious Ransomware-as-a-Service (RaaS) that emerged in early 2019 was known for its double-extortion tactics. It not only encrypted victims’ files but also threatened to release stolen data publicly. Avaddon’s modus operandi involved targeting a diverse range of sectors, including healthcare, government, financial services, legal, hospitality, education, and retail. Interestingly, while Avaddon was active, some of its affiliates focused on individual targets rather than large corporations. The ransomware had built-in mechanisms to avoid attacks in certain countries of the former Soviet Union, mainly those still aligned with Russia.
However, in 2021, Avaddon ceased its operations, and decryption keys were released to all its victims. This cessation marked the end of one threat but paved the way for another. NoEscape Ransomware surfaced in June 2023, and its tactics and operations bore a striking resemblance to Avaddon. The similarities between the two are not just coincidental.
The cybercriminal landscape is ever-evolving, and as one threat diminishes, another rises, often building upon the strategies and tactics of its predecessors. This article delves into the targets and latest activities of NoEscape Ransomware.
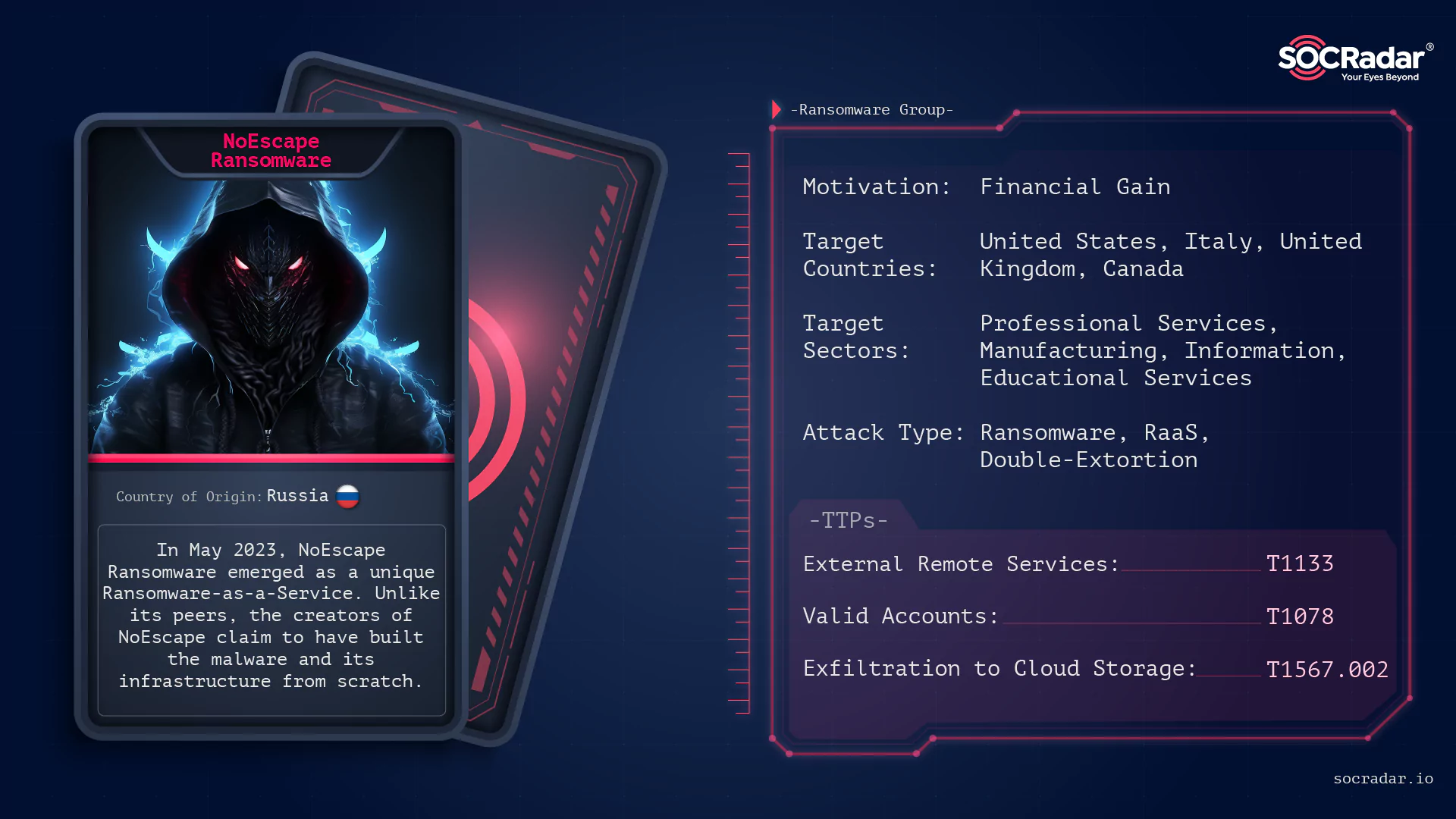
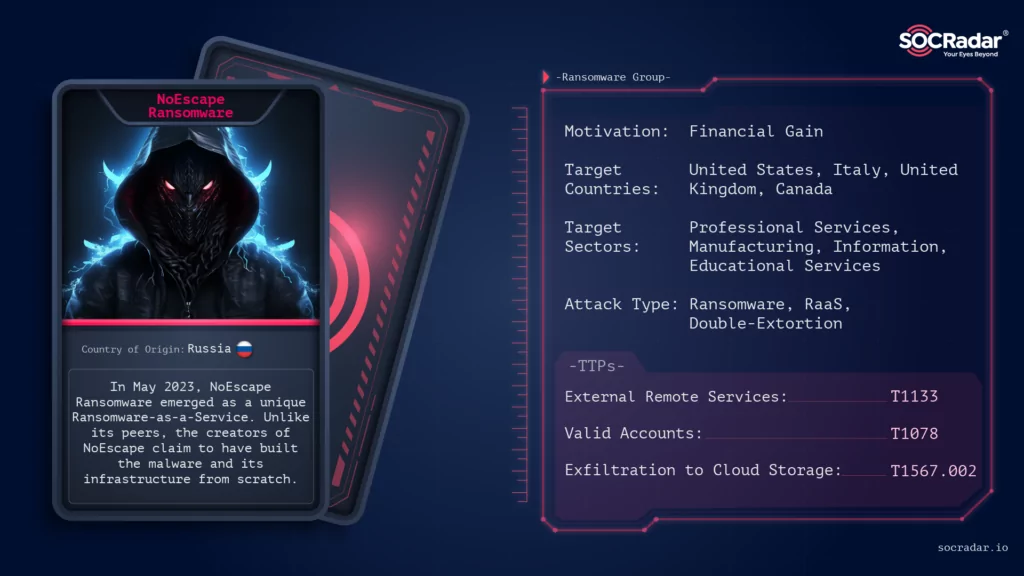
Who is NoEscape Ransomware?
NoEscape Ransomware surfaced in May of 2023, distinguishing itself as a Ransomware-as-a-Service (RaaS). Unlike many of its contemporaries, the developers of NoEscape assert that they have constructed the malware and its associated infrastructure entirely from the ground up, deliberately avoiding the use of source code or leaks from other established ransomware families.

Presently, NoEscape RaaS operators furnish affiliates with a comprehensive platform that facilitates the creation and management of payloads tailored for both Windows and Linux operating systems. Furthermore, NoEscape is recognized for its multi-extortion tactics, maintaining a TOR-based blog to publicly list its victims and display the exfiltrated data of those who resist meeting their demands.
How does the NoEscape Ransomware Attack?
NoEscape ransomware operates as a Ransomware-as-a-Service (RaaS), which means it provides a platform for affiliates to build and manage ransomware payloads. These payloads are designed for both Windows and Linux systems. The ransomware’s operation is based on a shared-profit model. For instance, any ransom collected over $3 million USD results in a 90/10 split in favor of the affiliates. The percentage changes with lower ransom amounts, such as an 80/20 split for a one million dollar payout.
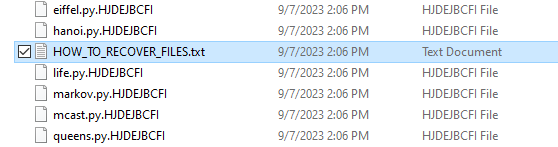
In terms of its technical capabilities, NoEscape ransomware supports multiple encryption modes, including full, fast, or strong. It leverages encryption algorithms like RSA and ChaCHA20 for file encryption. The ransomware has features like process termination, safe-mode operation, spreading and encryption over SMB or DFS, and the use of the Windows Restart Manager to bypass any processes that might block the encryption process. A unique feature is the shared encryption, which allows a single encryption key to be used across all infected files in a network, facilitating efficient encryption and quick decryption if the ransom is paid. Victims of the ransomware find notes titled “HOW_TO_RECOVER_FILES.TXT” in each folder with encrypted files.
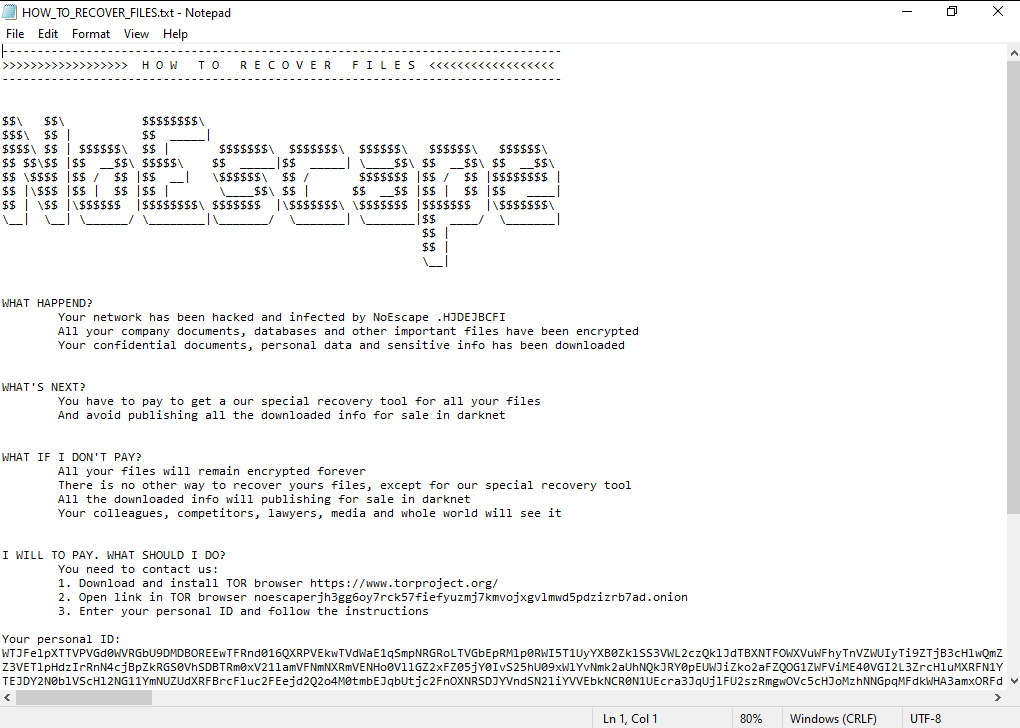
Encrypted files are appended with a ten-character identifying extension, such as “.CCBDFHCHFD” or “.CBCJDHIHBB”.
Overview of NoEscape Ransomware
There are separate variants of NoEscape for Linux and Windows, we gathered two samples from open source that were developed for Microsoft Windows.
The hash values of our samples are in order:
- Sample A: 68ff9855262b7a9c27e349c5e3bf68b2fc9f9ca32a9d2b844f2265dccd2bc0d8 (SHA256) and
- Sample B: 9d346518330eeefbf288aeca7b2b6243bc158415c7fee3f2c19694f0e5f7d51c (SHA256)
When we check the properties of our samples, we see that they are developed with C++:

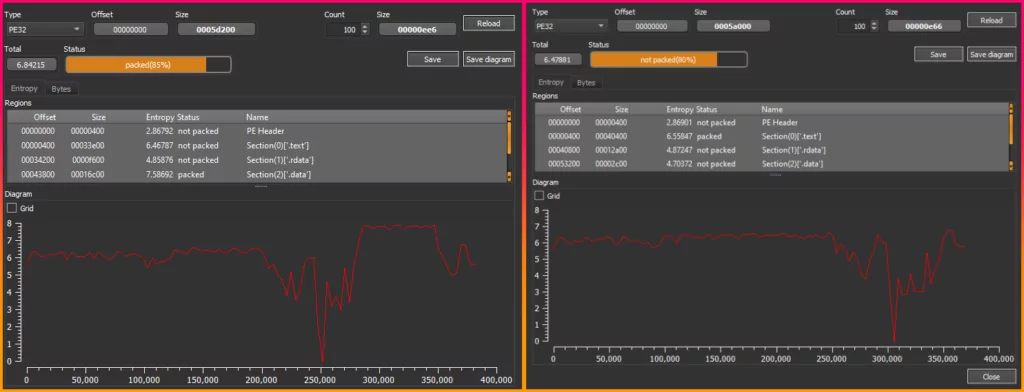
Looking at the entropy values and pack statuses of Sample A and Sample B:
- Sample A: This sample exhibited an entropy of 6.84215. Such a high value indicates a significant level of randomness. Coupled with the fact that it’s 85% packed, it’s evident that this ransomware is employing obfuscation techniques, likely to evade detection.
- Sample B: With an entropy of 6.47881, Sample B is slightly less random compared to the first. Interestingly, it is not packed (80% unpacked). This could suggest that while it has some level of encryption or randomness, it might not be employing the same level of obfuscation as the first sample.
We continued our analysis on Sample B because it was not packed, but we also observed the behavior of Sample A.
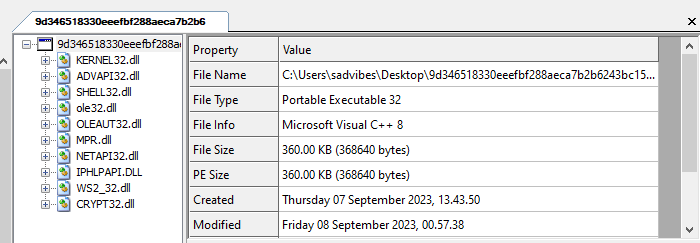
When we checked the DLLs contained in Sample B, KERNEL32.dll, SHELL32.dll, and CRYPT32.dll caught our attention, and we decided to look at the imported APIs:
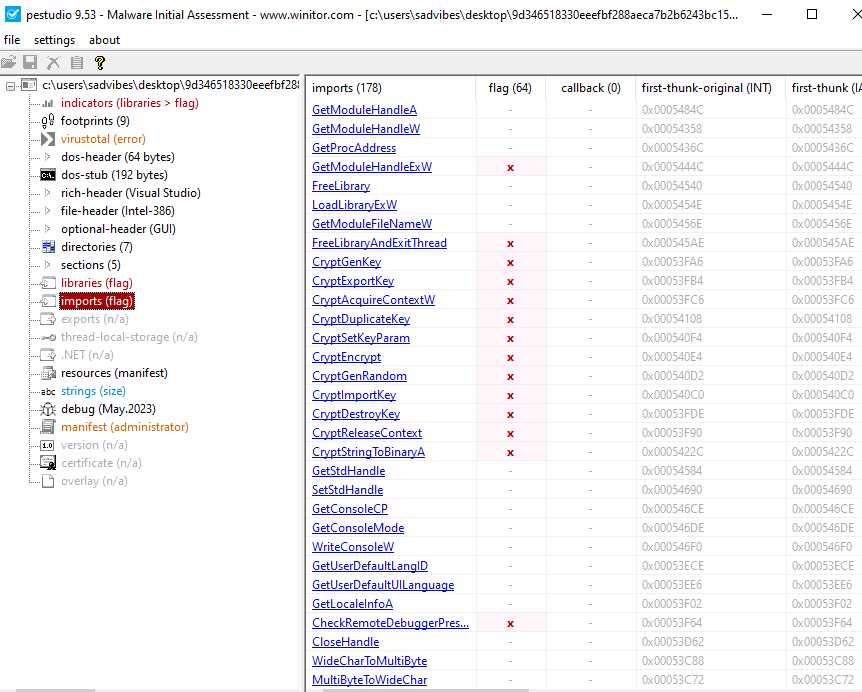
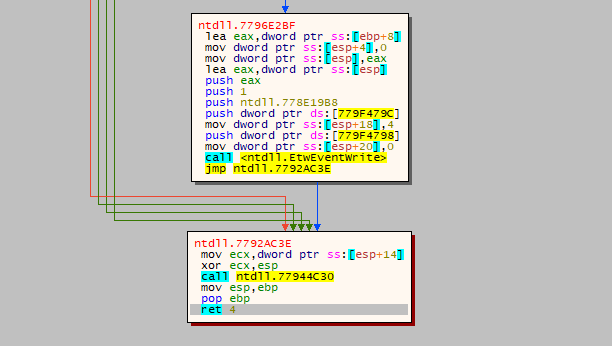
We observed that Sample B used the EtwEventWrite API, part of the Event Tracing for Windows (ETW) framework. This discovery has led to speculation that the malware might generate ETW events to avoid detection, as these events can mask malicious activities among genuine system processes. By doing so, the malware could secretly exfiltrate data through ETW events, potentially mislead security experts with deceptive events, and reduce its detectable footprint on the system. Using the EtwEventWrite API presents a significant challenge for cybersecurity defense mechanisms.
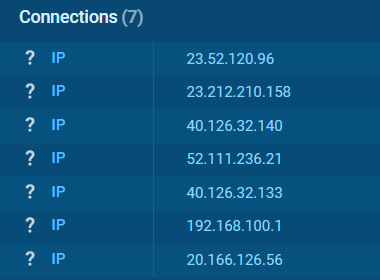
The IP addresses that NoEscape Ransomware’s Sample B connects to during operation (not necessarily malicious IPs) are shown in the image below:
The Connection Between Avaddon and NoEscape Ransomware
Several key points highlight the connection between Avaddon and NoEscape:
- Encryption Similarities: Both Avaddon and NoEscape encryptors are nearly identical. The primary difference lies in the encryption algorithm. While Avaddon utilized AES for file encryption, NoEscape adopted the Salsa20 algorithm. Despite this difference, the encryption logic and file formats used by both ransomware are strikingly similar.
- Configuration Overlaps: Both ransomware use the same configuration file and directives, further cementing the belief in their intertwined origins.
- Tactical Resemblance: NoEscape’s overall strategy mirrors that of Avaddon. From gaining access to corporate networks to employing double-extortion tactics, the parallels are evident.
- Geographical Exemptions: Just like Avaddon, NoEscape refrains from targeting countries of the former Soviet Union. Victims from these regions are provided with free decryption keys.
- Possible Rebranding: The emergence of NoEscape shortly after Avaddon’s cessation, combined with the aforementioned similarities, suggests a potential rebranding. Some researchers believe that key players from the Avaddon campaign have now integrated into the NoEscape group.
In conclusion, while NoEscape presents itself as a new threat, its roots can be traced back to the Avaddon ransomware gang.
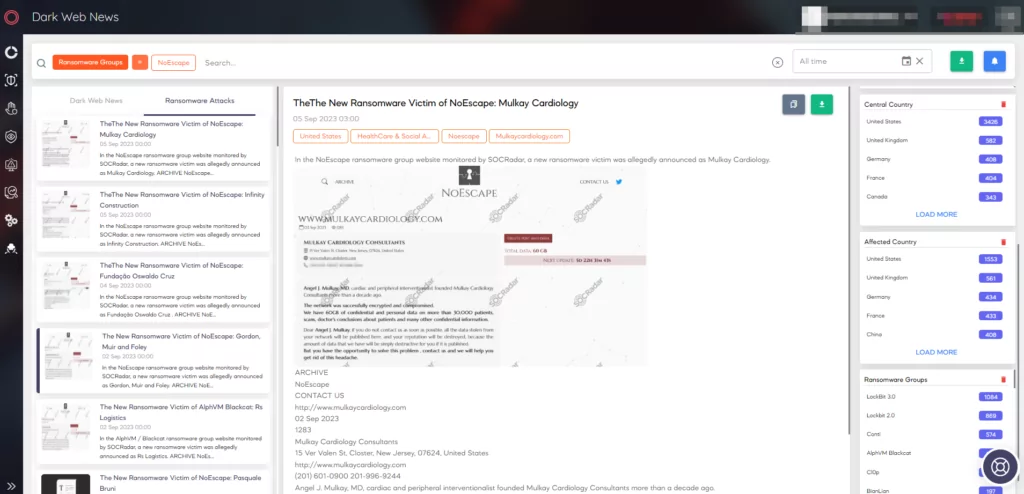
A Quick look at NoEscape Ransomware’s TOR site
Looking at NoEscape’s TOR page, we can see that there is a logo with a lock icon (meaningful) and victim announcements list at the entrance:

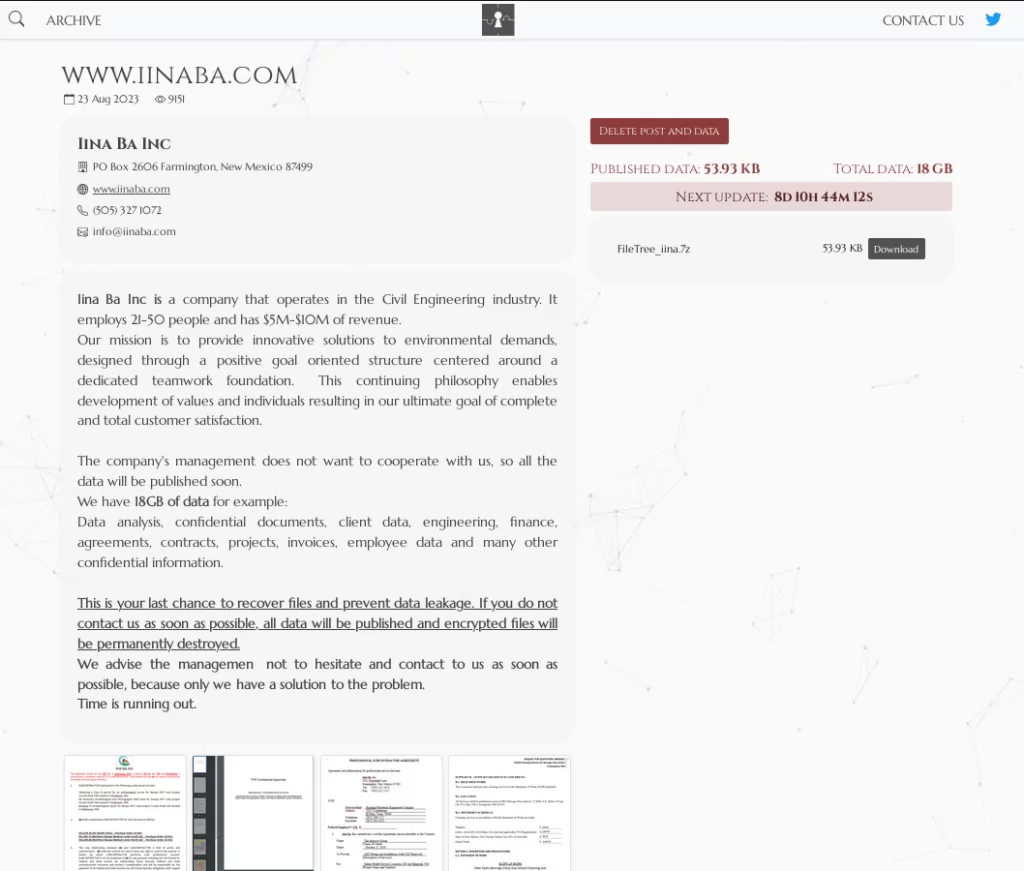
In the Archive tab, it is seen that there are leaked data and company details listed:

Leak data sharing is partial and there is a continuous countdown cycle in every claim page:
In the Contact Us section, there is a download link for access via TOX and a form where you can fill in your information for NoEscape to contact you:
If you are a victim of NoEscape, the TOR address in the ransom note takes you to a platform where you can enter the victim ID (personal ID) assigned to you for negotiate the ransom:
What are the targets of NoEscape Ransomware?
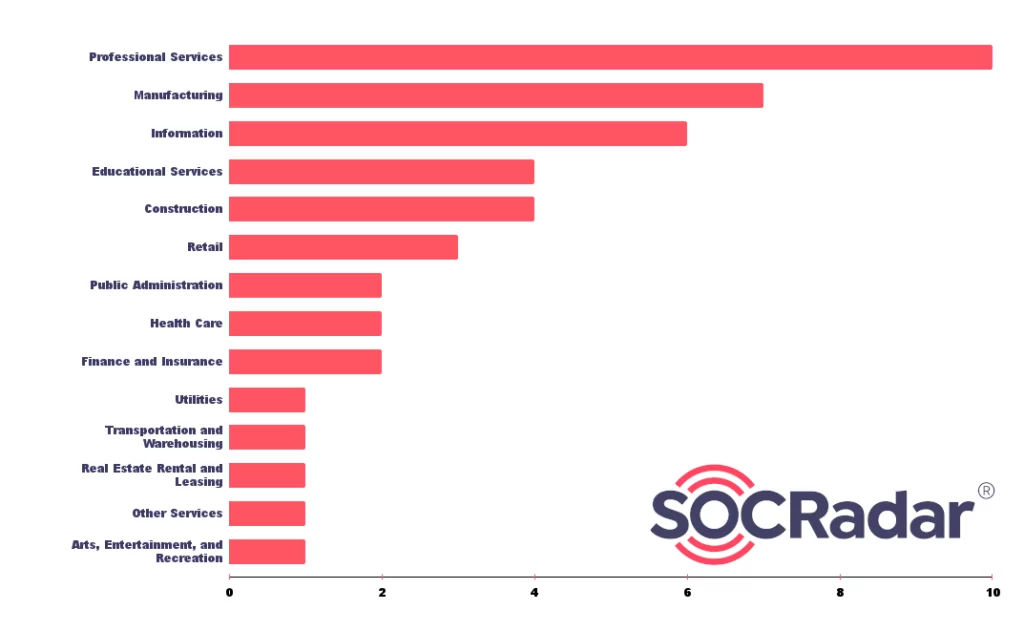
Target Sectors:
When observing the NoEscape’s attacks, it can be inferred that it mostly targets the organizations operating in the Professional Services, Manufacturing, and Information (mostly in Telecommunications) fields.
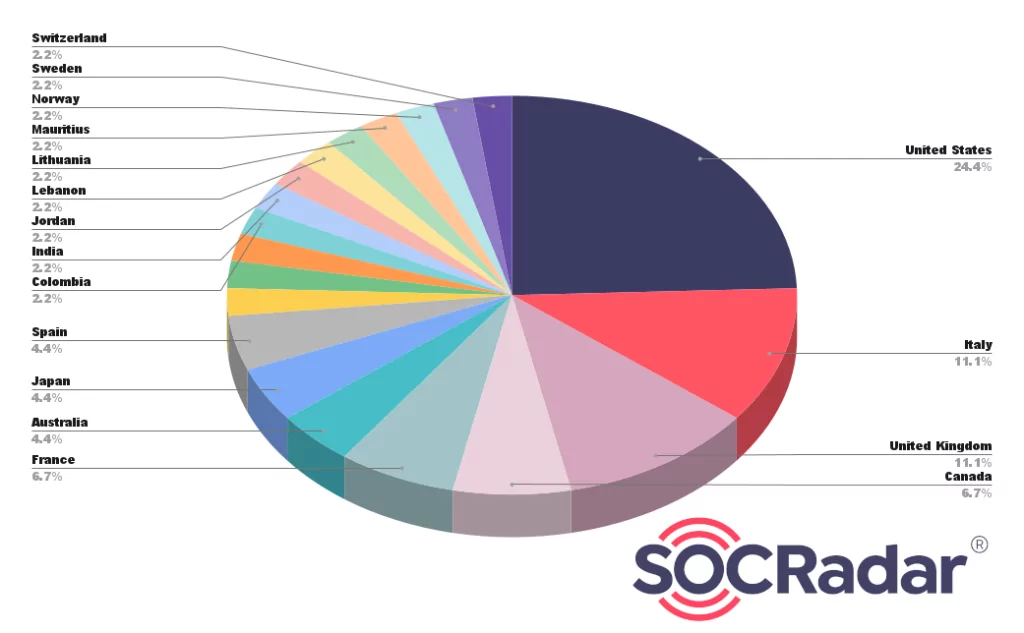
Target Countries:
Looking at the countries where the organizations affected by NoEscape Ransomware are located, it can be inferred that it is mostly active in North America, Europe,and Southeast Asia.

When the country distributions are analyzed, we conclude that the United States (about 25%), Italy (11%), United Kingdom (11%), and Canada (about 7%) are targeted more than other countries, respectively.
Latest Activities of NoEscape Ransomware
Infinity Construction Company:

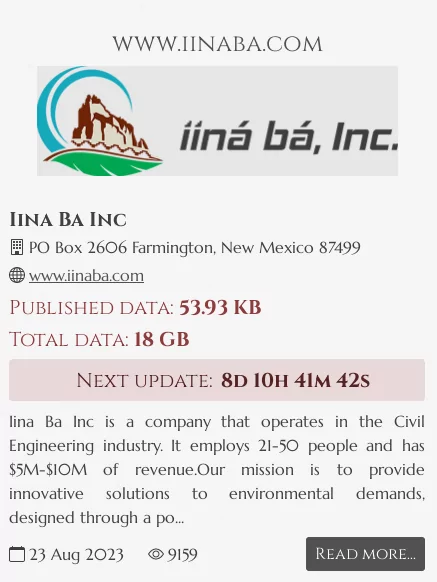
Iina Ba, Inc:
Conclusion
NoEscape Ransomware has rapidly emerged as a formidable threat in the cybersecurity landscape. Its evolution and tactics signify the adaptability and resilience of modern ransomware groups. While it is believed to be a rebrand of the Avaddon ransomware gang, NoEscape has carved its niche with unique features and aggressive extortion methods. The ransomware primarily targets Windows and Linux machines and has even shown compatibility with VMware ESXi. Its encryption methods, combined with its double extortion tactics, make it a significant concern for businesses and individuals alike.
The recent activities, including the imitation by other threat actors, highlight the prominence and influence of NoEscape in the cybercriminal community. However, with proactive cybersecurity measures, regular backups, and awareness, individuals and organizations can mitigate the risks posed by such ransomware.
Security Recommendations against NoEscape Ransomware
To safeguard against NoEscape Ransomware and similar threats, consider the following security recommendations:
- Regular Backups: Ensure that you maintain regular backups of your critical data. Store these backups in a secure location, preferably offline, to prevent them from being targeted by ransomware.
- Update Software: Keep all software, especially your operating system and security solutions, up to date. Regular updates often contain patches for known vulnerabilities that ransomware might exploit.
- E-mail Caution: Be wary of email attachments and links, especially from unknown senders. Phishing e-mails are a common method used by ransomware to infiltrate systems.
- Strong Passwords: Use strong, unique passwords for all accounts and enable multi-factor authentication wherever possible.
- Security Solutions: Invest in reliable cybersecurity solutions that offer real-time protection against malware and ransomware threats.
- Educate and Train: Regularly train and educate employees about the dangers of ransomware and how to recognize potential threats.
- Incident Response Plan: Have a well-defined incident response plan in place. In case of a ransomware attack, knowing the immediate steps to take can significantly reduce damage.
- Avoid Suspicious Downloads: Refrain from downloading files or software from untrusted sources or websites.
- Network Security: Implement firewalls and other network security measures to monitor and control incoming and outgoing network traffic.
- Proactive Security: For a proactive security approach, you can stay one step ahead of attackers and strengthen your security posture by using a cyber threat intelligence platform such as SOCRadar. For more detailed information, you can browse our Platform and check out our blog post on How to prevent Ransomware Attacks.
MITRE ATT&CK TTPs of NoEscape Ransomware
|
MITRE ATT&CK Tactic |
MITRE ATT&CK Technique/Procedure |
|
Initial Access |
External Remote Services (T1133) |
|
Valid Accounts (T1078) |
|
|
Execution |
User Execution (T1204.002) |
|
Scheduled Task/Job (T1053.005) |
|
|
Persistence |
Registry Run Keys / Startup Folder (T1547.001) |
|
Valid Accounts (T1078) |
|
|
Privilege Escalation |
Valid Accounts (T1078) |
|
Defense Evasion |
Disable or Modify Tools (T1562.001) |
|
Software Packing (T1027.002) |
|
|
Process Injection (T1055) |
|
|
Indicator Removal on Host (T1070.004) |
|
|
Modify Registry (T1112) |
|
|
Deobfuscate/Decode Files or Information (T1140) |
|
|
Virtualization/Sandbox Evasion (T1497.001) |
|
|
Credential Access |
OS Credential Dumping (T1003) |
|
Discovery |
Account Discovery (T1078) |
|
Domain Trust Discovery (T1482) |
|
|
Permissions Groups Discovery (T1069) |
|
|
Lateral Movement |
Remote Services (T1021) |
|
Remote Desktop Protocol (T1021.001) |
|
|
Collection |
Archive via Utility (T1560.001) |
|
Command and Control |
Web Protocols (T1071.001) |
|
Exfiltration to Cloud Storage (T1567.002) |




































