Dark Web Profile: Everest Ransomware
In the constantly changing landscape of cyber threats, ransomware groups adapt their tactics to outmaneuver defenses. Everest Ransomware recently attracted attention in May 2024 for its notable targets. Since its emergence in December 2020, Everest has seemed to infiltrate and compromise organizations using advanced techniques. This profile examines the origins, operational tactics, and mitigation strategies related to Everest Ransomware, offering essential insights for cybersecurity professionals.
Who is Everest Ransomware
Everest ransomware, active since December 2020, has quickly become known in the cybercriminal landscape. The group’s strategies and high-profile alleged targets, including NASA and the Brazilian Government, highlight their operational capabilities. Once known for their double extortion tactics, Everest did not only encrypt victim data but also threatened to leak sensitive information if ransom demands were not met.
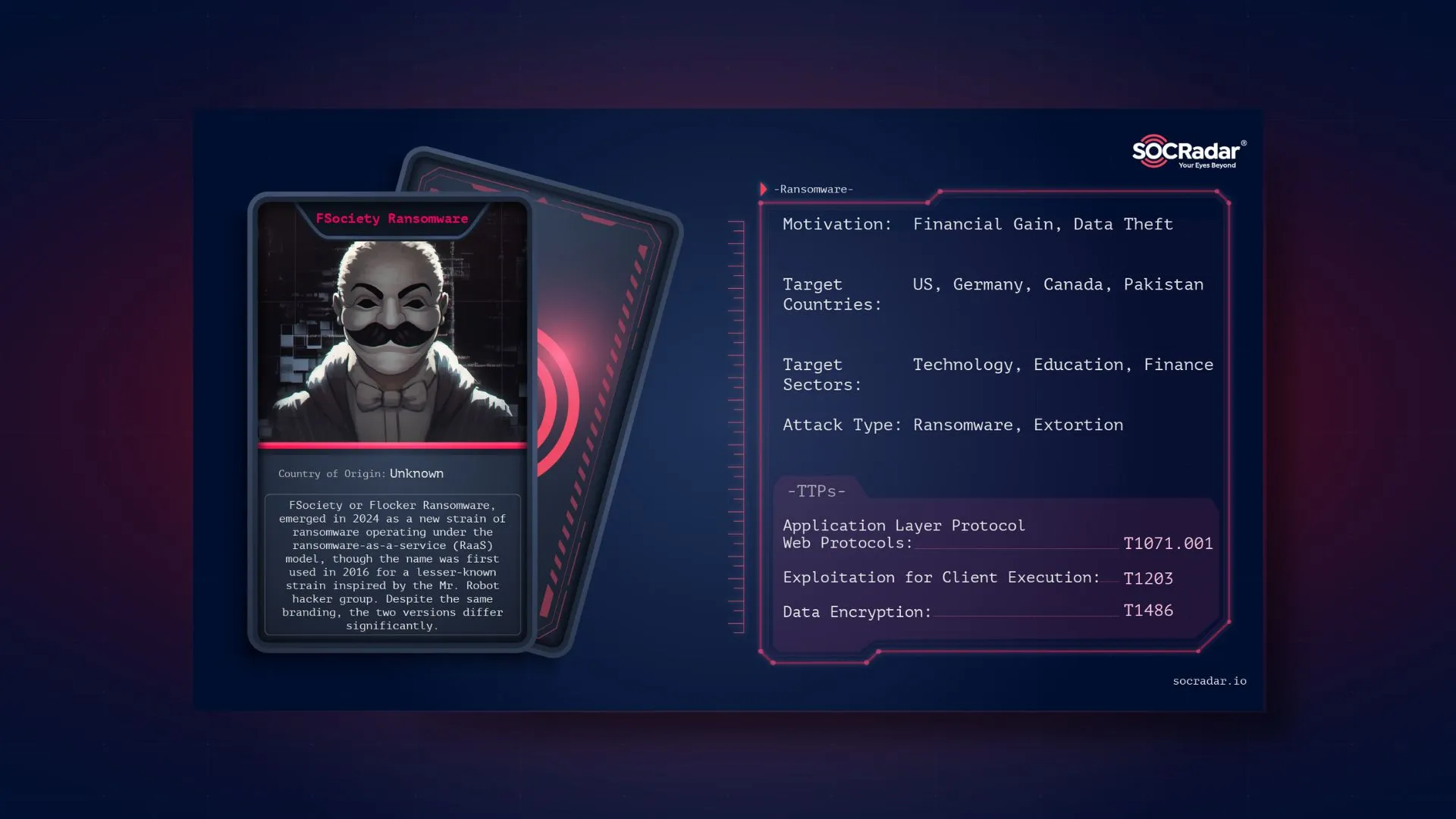
Everest Ransomware’s current home page
However, the group has undergone several transformations. More recently, they have increasingly specialized as an Initial Access Broker and lastly in line with the trend, just data leak threats.
The group, whose data leak sites became inaccessible after the Colonial Pipeline incident, probably turned to less risky cyber crimes and seems to be continuing the same strategy.
Operational Tactics
While it was a fully fledged ransomware operation Everest employed a range of sophisticated tactics, techniques, and procedures (TTPs) to achieve its objectives as suggested by NCC. Their Cyber Kill Chain is as follows:
Lateral Movement: The group uses legitimate compromised user accounts and Remote Desktop Protocol (RDP) to move laterally across networks. By exploiting weak or stolen credentials, they can access multiple systems within a target organization.
Credential Access: Everest utilizes tools like ProcDump to create copies of the LSASS process, allowing them to extract additional credentials. They also create copies of the NTDS database, containing valuable Active Directory data.
Defense Evasion: To avoid detection, Everest routinely removes tools, reconnaissance output files, and data collection archives from compromised hosts. This helps to cover their tracks and maintain persistence within the network.
Discovery: Upon compromising a new host, Everest conducts network discovery using tools such as netscan.exe, netscanpack.exe, and SoftPerfect Network Scanner. These tools enable the group to identify further targets within the network and plan subsequent stages of the attack.
Collection: The group installs WinRAR on file servers to archive data for exfiltration. This archived data is then transferred out of the network for ransom or sale.
Command and Control: Everest primarily uses Cobalt Strike for command and control (C2) communications. They execute Cobalt Strike beacons on compromised hosts through PowerShell commands and also deploy secondary C2 methods using remote access tools like AnyDesk, Splashtop Remote Desktop, and Atera.
Exfiltration: Data exfiltration is conducted using the file transfer capabilities of tools like Splashtop. This ensures that sensitive information is moved out of the network before encryption or other malicious activities are initiated.
Impact: Everest employs a double extortion technique, where they not only encrypt the victim’s data but also exfiltrate sensitive information. This increases pressure on victims to pay the ransom, as failure to do so could result in public data leaks.
However, in their current activities, only data leak sales appear and there is no encryption phrase or reference. Another important detail is that it was once associated with Black-Byte. However, this is not the only known relationship of the group.
In September 4 of 2023 it was noted that they were also collaborating with Ransomed, as evidenced by the victim announcement for SKF.com. Upon reviewing Ransomed’s claim post, it was observed that they also made the same announcement. Both groups have maintained a presence on platforms such as the XSS Forum and Breached.
Given that Ransomed was one of the founders of BlackForums after Breached and Everest was active on Breached, it can be inferred that their collaboration extends beyond a single operation, indicating a history of working together.
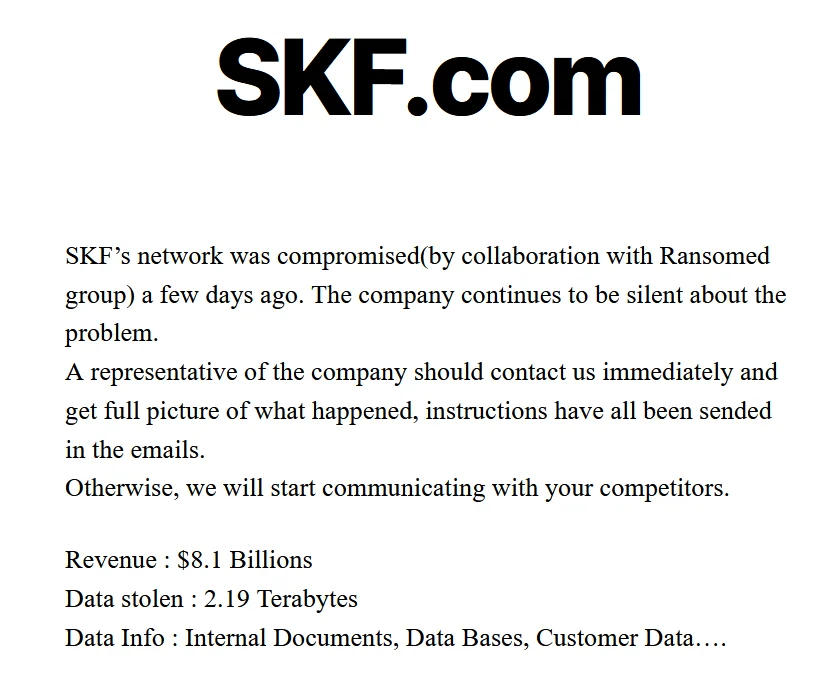
Victim sharing of SKF in Everest Ransomware’s data leak site
Although this context reveals some ties, it is not known whether there is a current tie as Ransomed is no longer active. Breached’s new version BreachForums was also recently subjected to an FBI operation, but XSS is still active and at the beginning of this month, Everest Ransomware shared a few leaks on the forum.
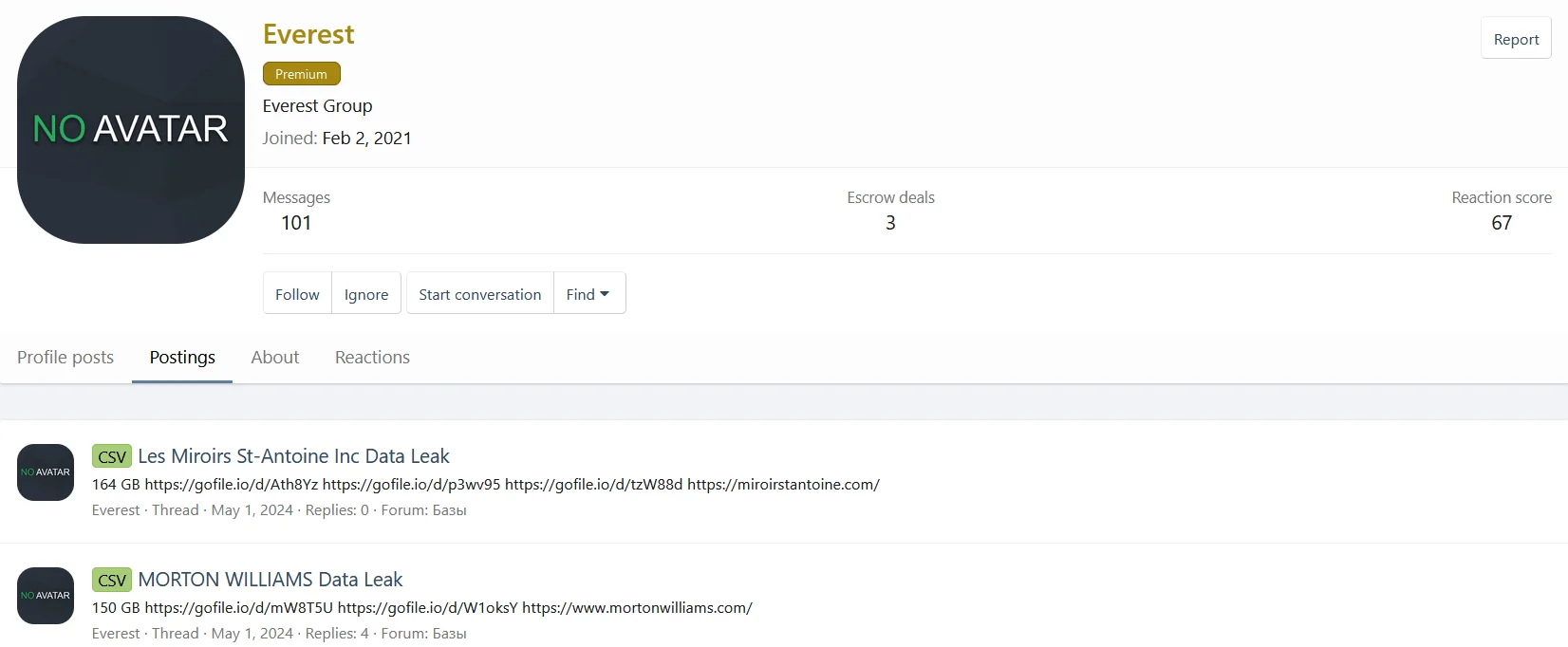
Everest Ransomware is still active on XSS
Transition into an Initial Access Broker
The Everest ransomware group made a significant shift in its tactics by actively seeking access to corporate networks directly from employees. This move was marked by their offer to share a portion of the profits from successful attacks with those facilitating the initial intrusion. They also assured partners of complete transparency regarding the operations and confidentiality regarding their involvement.
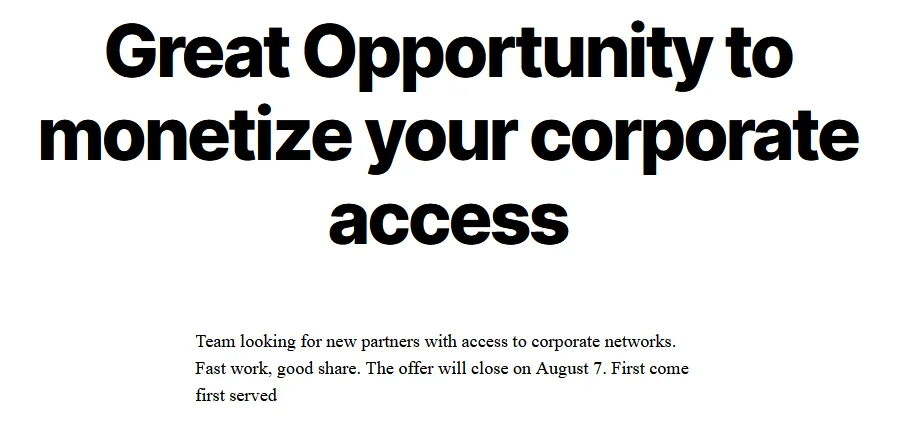
Everest Ransomware’s recruiting post
The group specifically targeted organizations based in the US, Canada, and Europe, and they were open to acquiring remote access through various means such as TeamViewer, AnyDesk, and RDP. This strategic change was observed in their deep web communication, indicating a deliberate effort to reduce reliance on intermediaries and streamline their operations.
Researchers noted a notable increase in Everest’s activity as an Initial Access Broker (IAB) starting from November 2022. This transition was seen as a strategic move to evade law enforcement and enhance their financial gains by eliminating intermediaries.
As stated above, this trend aligns with a broader shift among ransomware groups to minimize intermediaries and maximize profits by directly targeting organizations. However, their latest victim announcements are just data leak threats for various companies, so they are mostly a data broker group for now.
You can visit the SOCRadar Platform Ransomware Intelligence page to see victim organizations, industries and countries.
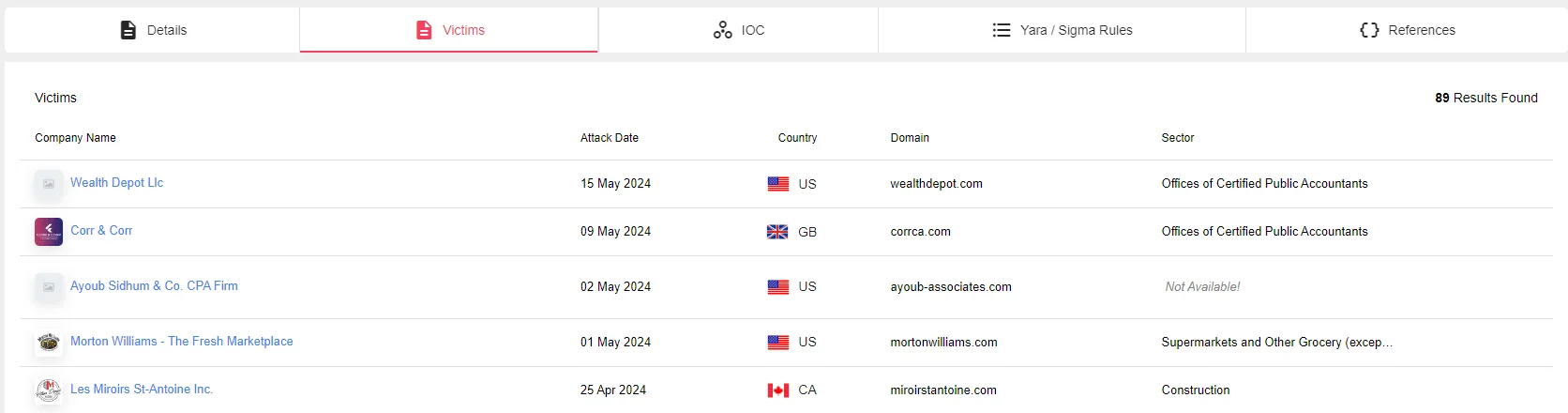
Everest Ransomware has 89 victims, SOCRadar Platform – Ransomware Intelligence
Mitigation Strategies
To defend against the sophisticated tactics employed by Everest Ransomware, organizations should implement the following strategies:
Regular Data Backup: Implement a robust backup strategy to ensure that critical data can be recovered in the event of a ransomware attack. Regular backups reduce the impact of data encryption and facilitate faster recovery.
Security Awareness Training: Educate employees about ransomware threats and cybersecurity best practices. Awareness training can help reduce the risk of falling victim to phishing attacks and other social engineering tactics used by Everest.
Patch and Update Management: Keep systems updated with the latest security patches to address vulnerabilities exploited by ransomware attackers. Regular updates minimize the attack surface and close security gaps.
Network Segmentation: Segment networks to separate critical systems and data from less secure areas. This limits the spread of ransomware within the network and contains potential breaches.
Access Control: Restrict user privileges to minimize the attack surface and prevent the spread of ransomware. Implement the principle of least privilege to ensure that users have only the access they need to perform their jobs.
Email and Web Security: Deploy advanced filtering solutions to detect and block malicious attachments, links, and phishing attempts. Robust email and web security can prevent initial access attempts by ransomware groups.
Endpoint Protection: Use antivirus software, Intrusion Detection Systems (IDS), and Endpoint Detection and Response (EDR) tools to detect and mitigate ransomware threats on endpoints. These tools provide real-time protection and alerting.
Incident Response Plan: Develop and test a response plan specifically for ransomware attacks. This plan should include procedures for identifying, containing, and recovering from incidents to ensure a swift and effective response.
Regular Security Audits: Conduct audits and vulnerability assessments to identify and remediate security gaps. Regular audits help maintain a strong security posture and ensure that defenses are up to date.
Backup Testing: Regularly test backup data integrity and store backups securely to prevent unauthorized access. Testing ensures that backups are reliable and can be restored when needed.
Conclusion
Everest Ransomware’s evolution and operational tactics underscore the dynamic and adaptive nature of cyber threats. By understanding their methods and implementing robust mitigation strategies, organizations can strengthen their defenses and reduce the risk of falling victim to ransomware attacks. Staying vigilant and proactive in cybersecurity efforts is crucial in the fight against ransomware groups like Everest.
We can help you build a proactive security posture. SOCRadar enhances your organization’s security stance against ransomware threats through proactive threat monitoring and intelligence solutions. By utilizing our platform, you can actively search for threat actors, understand their tactics and vulnerabilities, and implement preemptive measures to safeguard your assets.
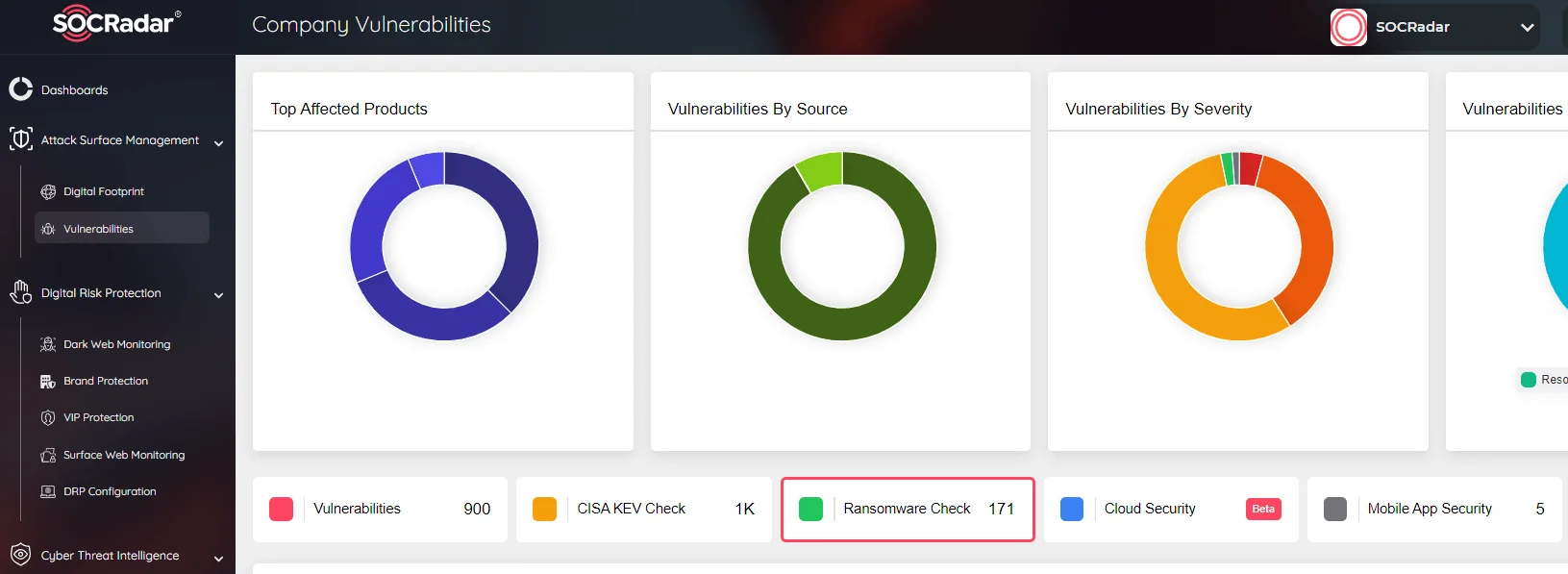
SOCRadar Attack Surface Management has Ransomware Check function
Our Attack Surface Management module provides ongoing monitoring of potential attack vectors, delivering timely alerts for suspicious activities. This proactive approach enables rapid responses to threats, bolstering your overall cybersecurity defenses. Integrating SOCRadar into your cybersecurity framework adds an additional layer of protection against ransomware and other cybersecurity threats.