Dark Web Profile: Netwalker Ransomware
Today, with the effects of digitalization, most of the information is stored online. This situation creates a vulnerability for organizations because the number of cyberattacks is increasing daily to steal those data. One example of cyber attackers is Netwalker Ransomware these days.
What is Netwalker Ransomware?
Netwalker Ransomware is a fast-growing Window’s specific ransomware created by one of the cybercriminal groups called ‘Circus Spider’ in 2019. This ransomware acts similar to other ransomware. It leaks to the system differently, then encrypts and exfiltrates the sensitive data.
After an attack, they send a note and demand some money or other things from victims in exchange for their sensitive data. The difference between this group and others is that they are not only hosting the data they stole, but they are also sharing some parts of it online to prove they have the information and to show how serious they are.
Subsequently, they threaten people to share all communication aspects if their needs are not fulfilled in a given time. For example, this group published one of their victims’ stolen data on the dark web in an encrypted folder and then shared the key online.
How Does Netwalker Ransomware Work?
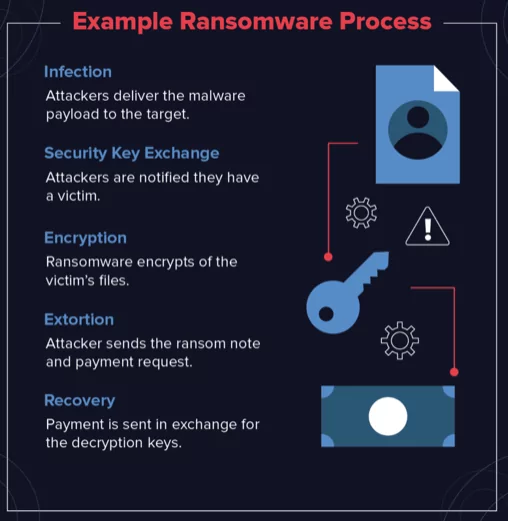
Netwalker Ransomware spreads mainly through phishing e-mails, e-mails coming from a charming, reliable source, as in the other Ransomware. Generally, these e-mails include an external link and give access to the attackers when the receiver clicks on this link.
The victims may be unable to detect Netwalker Ransomware because it works confidentially under the legitimate Microsoft processes. Then Netwalker steals the sensitive data and encrypts them to prevent access from the owner. After the attack is completed, the victim gets a note from the attacker related to the issue and asks for the payment.
Netwalker Ransomware and RaaS Model
Netwalker ransomware shifted to Ransomware-as-a-Service (RaaS) model in March 2020. RaaS is an adaptation of the Software as a Service (SaaS). Similar to the SaaS usage, RaaS users could sign up for the system, enabling them to use Ransomware for their attacks.
By shifting to this model, they expanded their operation scale worldwide in a little while. RaaS model also allowed them to target more organizations since it turned out global. In this matter, the earnings gained by affiliates motivated them to spread this Ransomware more.
What are the Criteria for Affiliates?
After a while, Circus Spider published a list of qualifications for their affiliates which indicates the requirements to join this group. According to this list, network ransomware affiliates:
- must be at a professional level in Russian
- must have comprehensive ransomware attacks experience
- must have a broad list of high-profile targets
- must have expertise in network
- must be capable of presenting their past experiences
Who Does Netwalker Target?
This ransomware group’s targets may vary from one sector to another, such as health, transportation, manufacturing, or infrastructure sectors. For example, some of their targets were Toll Group, K-Electric, the Austrian city of Weiz, and California University’s Covid Research Department.
How to Protect Yourself from Netwalker Ransomware?
- Keep your Software up to date
- Use external hard drives instead of computer
- Update your passwords
- Use two-factor authentication
- Use anti-virus, anti-malware Software
- Only connect secure networks
In the end, even though there are various threats, and their numbers are increasing daily, it is still possible to protect yourself and your organization from those attacks with the proper precautions.
References
Use SOCRadar® FOR FREE 1 YEAR
With SOCRadar® Free Edition, you’ll be able to:
- Prevent Ransomware attacks with Free External Attack Surface Management
- Get Instant alerts for fraudulent domains against phishing and BEC attacks
- Monitor Deep Web and Dark Net for threat trends
- Get vulnerability intelligence when a critical zero-day is disclosed
- Get IOC search & APT tracking & threat hunting in one place
- Get notified with data breach detection
Free for 12 months for one corporate domain and 100 auto-discovered digital assets.
Get Free Access.



































