
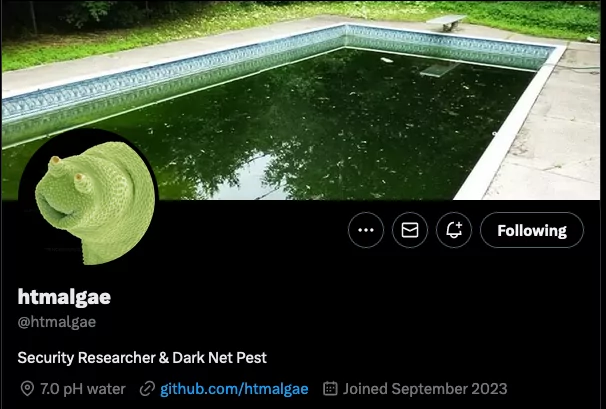
Decrypting the Shadows: Revealing the Secrets of Ransomware Operators – An Interview with @htmalgae
Meet @htmalgae, an anonymous security researcher with a wealth of experience in web application development. In the digital realm, htmalgae operates under this unique handle, and in the physical world, he holds the role of a senior software engineer at a prominent company. His recent findings have garnered significant attention, shedding light on the inner workings of ransomware operators.
htmalgae’s work is characterized by a remarkable ability to unveil the hidden aspects of ransomware groups’ operations. Notably, he has recently exposed fascinating details about various ransomware gangs. For instance, he revealed that the ThreeAM ransomware gang is utilizing an ancient PHP script called Yugeon Web Clicks v0.1, originally released in 2004, to track page views on their shame site. Additionally, he discovered vulnerabilities in the flatfile database accessible through the operator’s web page.
Furthermore, he shared insights into the Medusa ransomware group’s online presence, highlighting that README files in their website lists their technology stack. He also exposed the webserver access logs of the Snatch ransomware group, revealing intriguing details about their activities.
Notably, htmalgae’s investigative prowess extends to identifying individuals involved with ransomware groups. He famously spotted the person responsible for the 8Base ransomware websites, tracing their digital footprint all the way to their LinkedIn profile.
In the following interview, we will delve into htmalgae’s experiences and insights as he navigates the intricate world of ransomware operators. We’ll explore his motivations, tools, and techniques, as well as his thoughts on operational security and the importance of remaining vigilant against evolving cyber threats.
Can you please introduce yourself briefly? What is your profession?
Sure. I’m an anonymous security researcher who goes by the handle @htmalgae. In real life, I’m a senior software engineer working for a large company.
How did you first become interested in exploring ransomware operators’ pages? Was it a spontaneous decision or part of a planned research effort?
Ever since first hearing about CryptoLocker in 2013, I’ve been fascinated by cyber-criminals, in particular ransomware groups. Recently, after reading about the MGM ransomware attack, I decided to spend a few hours a day attempting to de-anonymize these criminals.
Your discovery involving 8Base’s page revealed a significant amount of information due to a verbose error page. After identifying the developer and prompting the removal of the repository, do you believe the individual was simply a freelancer and not directly involved with the ransomware group?
Freelancer or not, they were in full control of the hidden service that they also — at least partially — developed, so I’d consider that “directly involved”.
Ransomware operators are known for their advanced malware development skills. What are your thoughts on the awkwardness of their web development practices, considering their likely strong financial resources? Why do they opt for older technologies, instead of investing in development of secure pages?
Nowadays, with MaaS (malware-as-a-service), anybody can start a ransomware gang. This leads to a wide gamut of operators, some professional and some not so much. It’s all an affiliate pyramid scheme and it’s easy to tell who’s at the top.
Is there any information or findings you have not yet disclosed to the public regarding ransomware groups, or shared with just legal entities?
Yes, absolutely.
Have you ever received any threats or intimidation from ransomware operators due to your research?
Yes, but not as much as I’d have expected. In general, they are a pretty quiet bunch.
Do you plan to continue your work in auditing ransomware operators’ pages in the future? We get a signal from you since you created a repository in GitHub to curate such findings.
I indeed plan on continuing and will share raw data on my Github to supplement published articles.
Can you share some of the tools and techniques you use in your research when auditing these operators’ pages?
Sure. Nuclei, Shodan and Burp is a fantastic tool stack. I’m a huge fan of Nuclei automation with custom templates. And of course, just being familiar with web technologies from time spent developing with it, is the most useful tool for me.
Have any legal entities or organizations contacted you as a result of your findings or research in this field?
No. I like to think it’s because they already knew everything I revealed, or at least I hope so.
What could be the reason for such vital mistakes from an OpSec (Operational Security) perspective?
Humans doing human things. We rush through tasks, get impatient, over-confident and complacent.
What insights or information would you like to share with SOCRadar’s blog readers?
Would love to remind everybody, even the most savvy readers: Don’t click on links in emails or text messages. Don’t trust anybody who calls you on the phone. Don’t click Google results to download software. There’s some really scary malware out there, even on macOS. The best way to prevent being compromised is being proactive with your device usage.



































