

Decryptors Available for the ESXiArgs Incidents and Cl0p Ransomware Variants
Researchers have developed decryptors for some recent ransomware operations. The specific ransomware operations use Cl0p ELF variants and the new variants of ESXiArgs ransomware.
The incidents involving ESXiArgs are more recent. Due to businesses moving to virtual machines for better management, ESXi virtual machines have become a more popular target for attackers worldwide.
CISA Releases Recovery Script for ESXiArgs Ransomware
According to CISA, the recent large-scale ESXiArgs ransomware campaign encrypted 2,800 servers.
In the campaign, the attackers failed to encrypt flat files containing virtual disk data; this allowed YoreGroup Tech researchers to create a decryptor to rebuild virtual machines from these flat files and assist numerous victims in decrypting their systems.
Researchers Enes Sonmez and Ahmet Aykac have published a tutorial to guide victims through decryption. CISA has also released an automated ESXiArgs-Recover script on GitHub based on the tutorial and other public sources for those who have found it difficult to implement.
A Decryptor for Cl0p ELF Variants
Cl0p ransomware (a.k.a. CLOP) is part of the Cryptomix ransomware family and has been active since 2019. It has targeted cybersecurity compliance firm Qualys and several health services and organizations over the years.
The first Linux version of the Clop ransomware has been detected, with a flaw in its encryption algorithm that makes it possible to reverse engineer the process.
Security firm SentinelOne discovered the ELF version on December 26, 2022, and created a decryptor.
Cybersecurity researchers found that the Linux version of the Cl0p is an early-stage version, with some functions missing compared to the Windows version. This suggests that future variants of Cl0p could be more sophisticated and effectively target Linux systems.
Linux users should be ready for more Linux-targeted ransomware attacks in the future, as this variant’s development highlights the trend of threat actors targeting platforms other than Windows.
Prevent & Mitigate Attacks with SOCRadar
SOCRadar can assist organizations in proactively identifying and preventing ransomware attacks and improve their overall security posture by providing real-time visibility and alerting security teams to potential threats. The platform can also alert you to vendor attacks and phishing campaigns, which are common distribution methods.
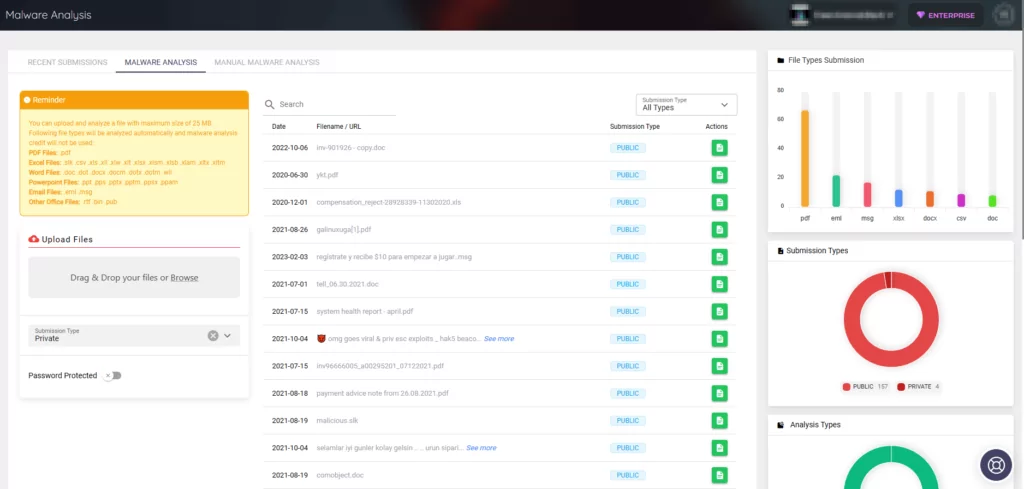
SOCRadar’s Malware Analysis is another useful tool. You can use the tool to evaluate suspicious files and receive a report containing a wealth of information about the malware as well as related security solutions.
You can check out SOCRadar’s blog post about ransomware detection and prevention for CISOs.










