
Educational Institutions Face 234% Increase in Ransomware Attacks
As the world becomes increasingly digital, educational institutions face a growing cyberattack threat. In 2022, cybersecurity researchers expected these attacks to increase in frequency and complexity as cybercriminals seek to exploit vulnerabilities in school systems and access sensitive information.
One of the main types of cyberattacks against educational institutions is ransomware, where hackers gain access to school networks and lock down files until a ransom is paid. This can result in critical data being lost or compromised, disrupting the school’s operations.
You can download the Education Industry Threat Landscape Report by clicking the button below.
Phishing attacks are another common threat, where attackers send fraudulent emails or messages to obtain sensitive information such as login credentials. Educational institutions are particularly vulnerable to these attacks, as they often have large numbers of staff and students who threat actors may target.
Rising Threat: Ransomware Attacks on Educational Institutions
Ransomware attacks have risen recently, and the education industry is no exception.
In some cases, schools have had to cancel classes to recover from ransomware attacks, and the ransom payment to decrypt the files is another factor to consider. Therefore, K-12 organizations must take preventive measures to protect their systems and data from ransomware attacks.
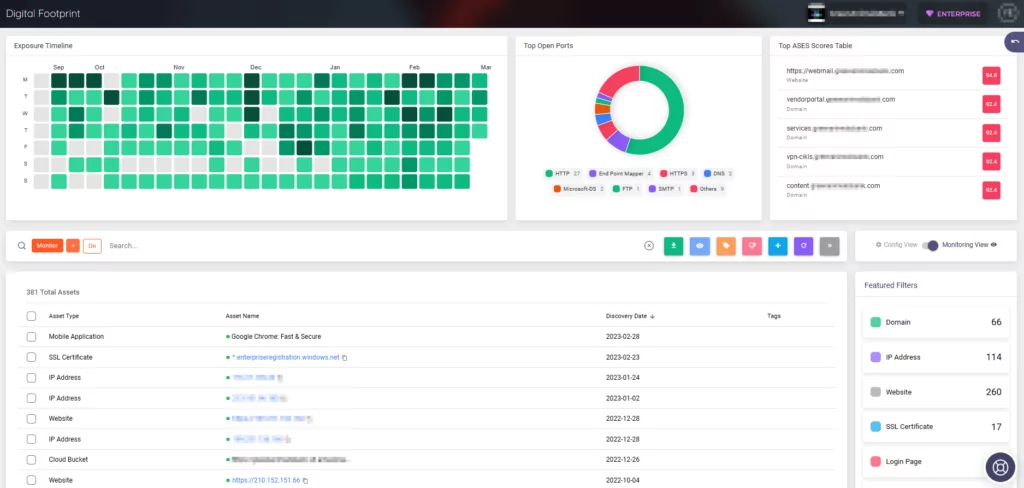
Ransomware attacks can be costly for K-12 organizations, causing disruptions and risking the exposure of sensitive data. To prevent these attacks, SOCRadar crawls through both the surface web and the dark web to find compromised employees’ credentials with access to the organization’s network, which the attackers can leverage to gain initial access into the victim system.
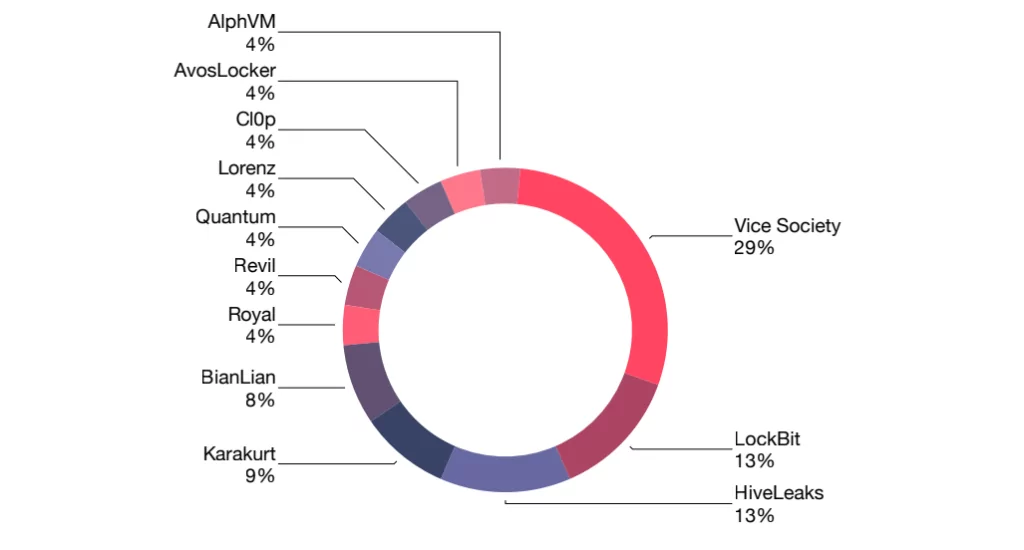
The report also contains information about the distribution of ransomware attacks that occurred in the education industry in both 2021 and 2022.
APT Groups Targeting US Educational Organizations
APT groups are a different type of threat actor that pose a significant danger to companies, government organizations, critical infrastructures, and K-12 organizations. Unlike ransomware gangs, their motive is not financial gain but to carry out their nation’s malicious cyber objectives.
These state-sponsored APT groups target US educational organizations to steal data, which threat actors can use for future cyber espionage or spying activities.
Four main APT groups that target US educational organizations have been identified by SOCRadar’s Cyber Threat Intelligence and are detailed in the report. The prominent APT groups targeting US educational institutions are all backed by China, which has a history of carrying out attacks targeting the personal data of US citizens.
Major Data Breaches
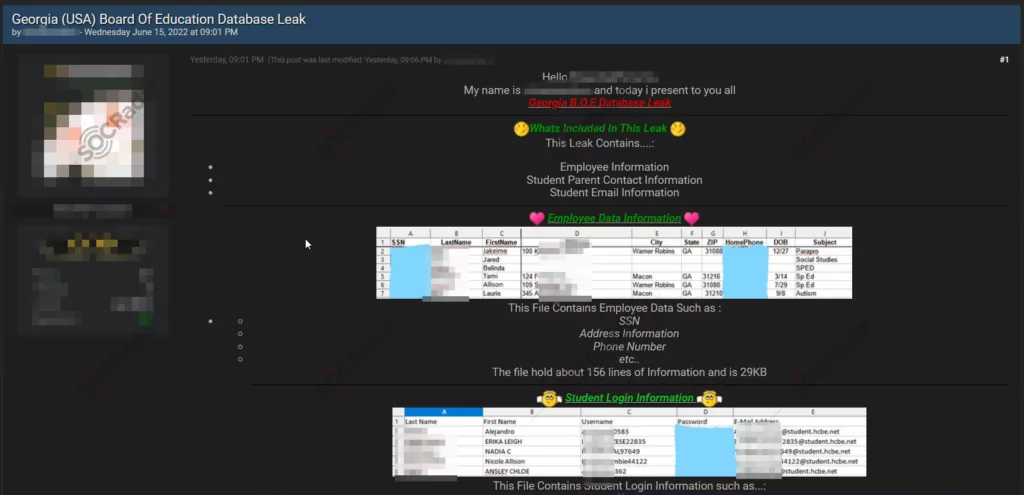
Over the past three years, public school districts have been confronted with incidents of data breaches. Security researchers typically discover these breaches on hacker forums located on the dark web, which SOCRadar constantly monitors. The report lists several incidents that have been tracked.
A new purported database sale for the Georgia Board of Education is discovered in a hacker forum that SOCRadar monitors:
Private schools operating in California are allegedly the victims of another data breach.
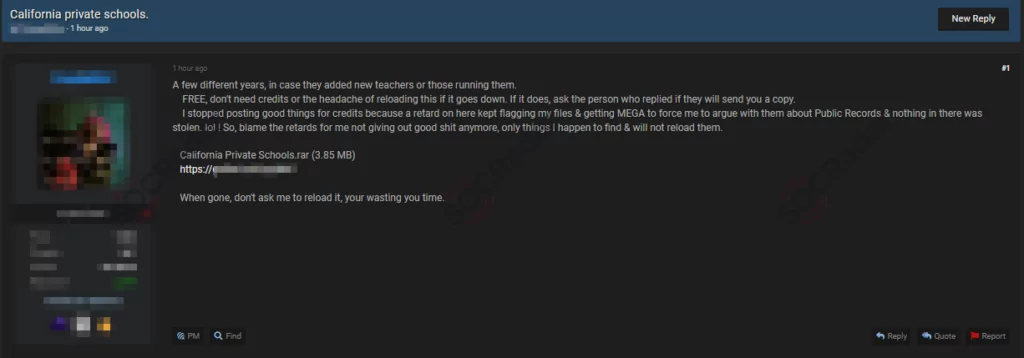
These breaches can have significant consequences, including critical data loss, reputational damage, and legal liabilities.
As the reliance on digital technologies continues to grow in the education industry, institutions must prioritize cybersecurity and take proactive measures to protect themselves and their sensitive information.
Motivations Behinds These Attacks
Educational institutions hold significant personal and confidential information, including personally identifiable information (PII), contact details, social security numbers, bank information, intellectual property, and research findings.
These data are collected from various sources and stored within the educational system. Threat actors are likely to target educational institutions because the attack surface in this industry has recently expanded uncontrollably, and the sensitive data and valuable intellectual property obtained from research programs in the higher education system are valuable in malicious acts.
The industry is also considered vulnerable due to its affected user base, mainly students. Following a ransomware incident, for example, there is no guarantee that the threat actors will provide the decryption key or that the decryption key will restore all data; thus, paying the ransom is a huge risk, and education is still likely to be harmed.
How Can SOCRadar Help?
Third-party vendors, as well as the increased number of devices and accounts used to manage the needs of today’s education systems, contribute to the attack surface of educational institutions.
An uncontrolled, expanding attack surface exposes new vulnerabilities for threat actors. These vulnerabilities necessitate immediate action, so educational institutions should monitor their expanding attack surface with advanced threat intelligence tools.
SOCRadar offers a variety of tools to help you improve your security posture against threats in the education industry and beyond.
The report explains the primary reasons for the increase in attacks on the education industry, as well as all lessons learned from these incidents, which can be interpreted as insights and will greatly contribute to security.
Download SOCRadar Education Threat Landscape Report and get more insights.




































