
From Azure AD to Microsoft Entra ID: Navigating the Name Change and Strengthening Phishing Defense
Azure AD, now known as Microsoft Entra ID, is undergoing a name change announced by Microsoft on 11 July, 2023. The motive behind this transition is to reflect Microsoft’s vision of offering a unified identity platform that enables universal access to applications across any device.
While the name change does not impact the functionality or features of Azure AD, it introduces both challenges and opportunities for threat intelligence analysts and security professionals.
You See a Change, But Attackers See Opportunities
One of the primary risks associated with this change is the increased potential for phishingand social engineering attacks. Phishing attacks involve cybercriminals employing deceptive emails or fraudulent websites to deceive users into divulging sensitive information or unwittingly installing malware. Social engineering, on the other hand, encompasses a broader range of tactics that manipulate human psychology or behavior.
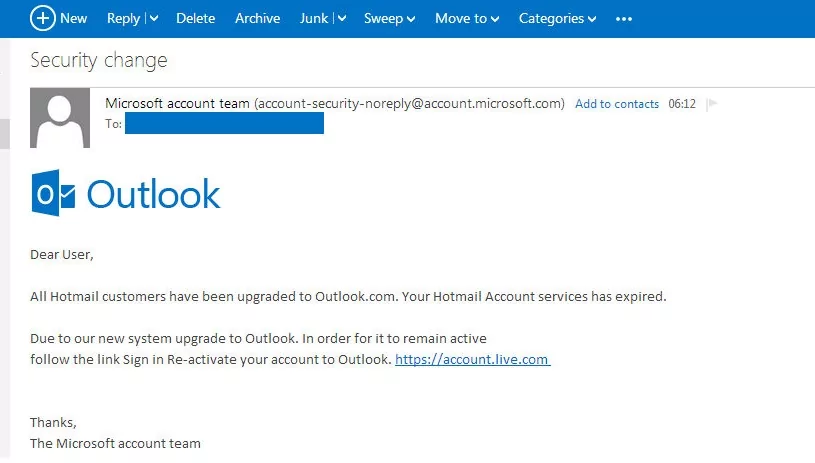
With the introduction of the new name Entra ID, threat actors might exploit this change to create convincing fake emails or websites masquerading as legitimate Microsoft communications or services. For instance, they could send emails requesting users to verify their Entra ID credentials, update their Entra ID settings, or activate their Entra ID subscription. These malicious actors may exploit the name transition to trick users into compromising their personal information or performing actions that could compromise the security of their accounts.
Ensuring Security and Mitigating Threats During the Microsoft Entra ID Name Change
To mitigate the risks associated with phishing and social engineering, it is essential for users and administrators to exercise caution and adopt best practices for identifying and handling potential threats.
Users should remain vigilant and scrutinize any email or website requesting Entra ID-related actions, paying close attention to details such as sender email addresses, website URLs, and the overall legitimacy of the communication.
It is advisable to independently verify such requests by contacting Microsoft through official channels rather than clicking on suspicious links or responding directly to emails.
Furthermore, organizations should emphasize the importance of cybersecurity awareness among their employees and provide regular training to help them recognize and respond to potential threats. Implementing robust email filtering systems and conducting regular security assessments can also help detect and prevent phishing attempts.
Microsoft intends to introduce the Entra ID name change gradually, commencing from the second half of 2023. While this transition is expected to be seamless for end users and administrators in terms of functionality, it is crucial to remain vigilant to safeguard against potential threats and ensure the continued security of Azure AD, now known as Microsoft Entra ID.
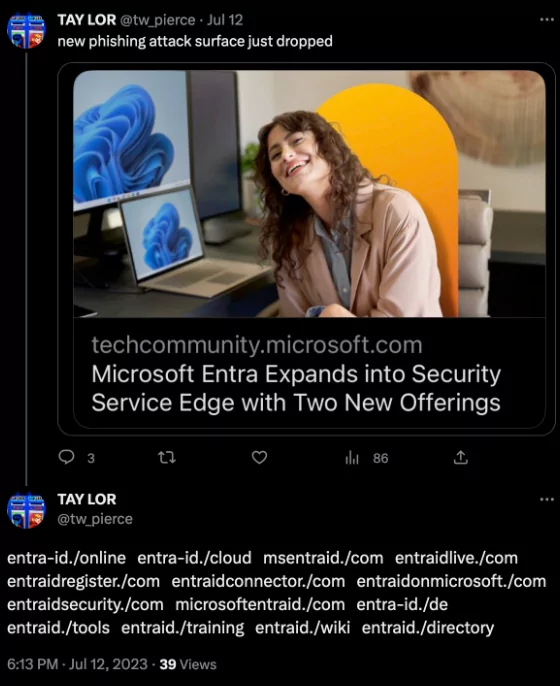
In addition to the challenges and opportunities introduced by the name change from Azure AD to Microsoft Entra ID, recent findings by SOCRadar Analysts have revealed potential threats associated with this transition.
Two Phishing Domains Spotted Mimicking Entra ID
Shortly after Microsoft’s announcement, two registered domains were discovered that appear to have been acquired for phishing purposes.
![A newly registered, phishing candidate domain: entraid-onmicrosoft[.]com](https://socradar.io/wp-content/uploads/2023/07/phishing-domain-1024x272.png)
These domains closely resemble legitimate Microsoft-related addresses and could be used by threat actors to create convincing phishing campaigns targeting Entra ID users. This discovery highlights the importance of heightened vigilance and reinforces the need for users and organizations to implement robust security measures to safeguard against potential phishing attacks during the transition period.
![A newly registered, phishing candidate domain: entraid-internetaccess[.]com, Entra ID](https://socradar.io/wp-content/uploads/2023/07/phishing-domain-2.png)
Considering Microsoft’s prominent position as a major player in the technology industry, it is highly improbable that they would choose to register a brand domain via a platform like GoDaddy right after making a significant brand announcement. Moreover, the registered domains bear a striking resemblance to the domain structure utilized by Azure AD, following the pattern of onmcrosoft.com in their domain names.
Enhancing Phishing Defense with SOCRadar Digital Risk Protection
To help companies mitigate the potential phishing attacks associated with the Microsoft Entra ID transition, SOCRadar offers its AI-enabled Digital Risk Protection platform. This powerful platform analyzes millions of domains across major domain registrars, enabling the detection of malicious domains specifically targeting your brand and entire business network.
SOCRadar also monitors all changes in DNS entries in the phishing domain; by continuously monitoring SOCRadar triggers alerts whenever any suspicious activity or changes are detected. As a part of offering actionable intelligence, SOCRadar allows users to start the takedown process of phishing domain with one click.

Utilizing advanced machine learning algorithms, SOCRadar’s platform can analyze vast amounts of domain data, specifically uncovering lookalike domains that may be used for phishing purposes. This proactive approach allows organizations to stay one step ahead of potential threats and take necessary action to protect their digital assets.




































