
Hacked Healthcare: Rising Security Breaches in the US
The healthcare industry is an attractive, prime target for ransomware groups; the AIDS Trojan, also known as the PC Cyborg virus, was the first-ever ransomware virus documented. It targeted the healthcare industry. The AIDS trojan was created by a biologist Joseph Popp who handed out 20,000 infected disks to attendees of the World Health Organization’s AIDS conference. Unlike the recent ransomware, the AIDS Trojan was easy to overcome as it used simple symmetric cryptography, and tools were soon available to decrypt the files.
Download SOCRadar’s Healthcare Threat Landscape Report to get full insights and analysis on recent cyber incidents concerning healthcare organizations.
Department of Health and Human Services
The Department of Health and Human Services (HHS) is a US federal executive department responsible for protecting and enhancing the health and well-being of Americans. The data managed by HHS encompasses a wide range of health-related information. This includes health statistics, research findings, public health data, healthcare quality and performance metrics, healthcare utilization and cost data, health insurance information, Medicare and Medicaid data, and much more.
Under the HIPAA Breach Notification Rule, covered entities (such as healthcare providers, health plans, and healthcare clearinghouses) and their business associates must report breaches of unsecured PHI to HHS. A breach is the unauthorized acquisition, access, use, or disclosure of PHI that compromises its security or privacy.
US Department of Health and Human Services Office for Civil Rights is posting a list of unsecured protected health information breaches affecting 500 or more individuals according to section 13402(e)(4) of the HITECH Act. We analyzed the reported breach data from April 2021- March 2023.
The Reported Incidents Concerning Healthcare
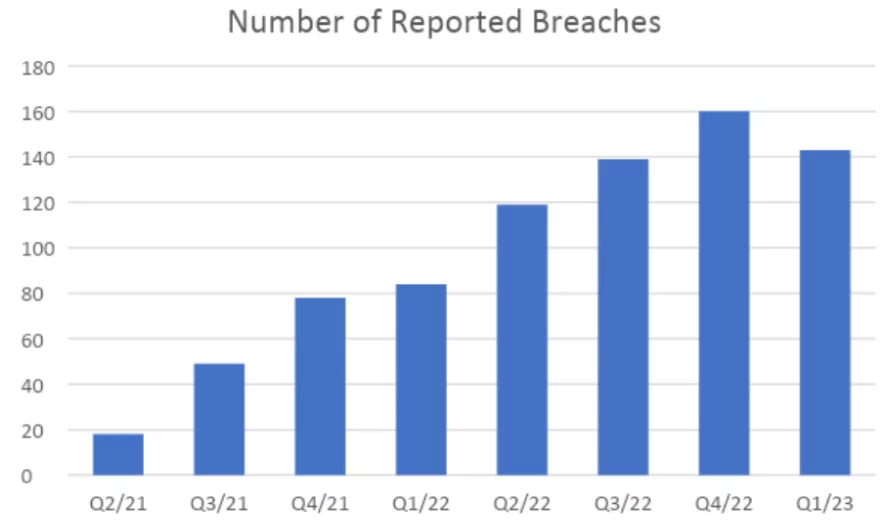
There were 790 incidents in US affecting more than 68.2 million citizens. When we look at the change in the number of reported breaches, it shows almost a linear increase. This indicates an increase in cyber attacks against the healthcare sector. Still, it also represents that the breached organizations chose to be more transparent about the attacks and involve the authorities much quicker.
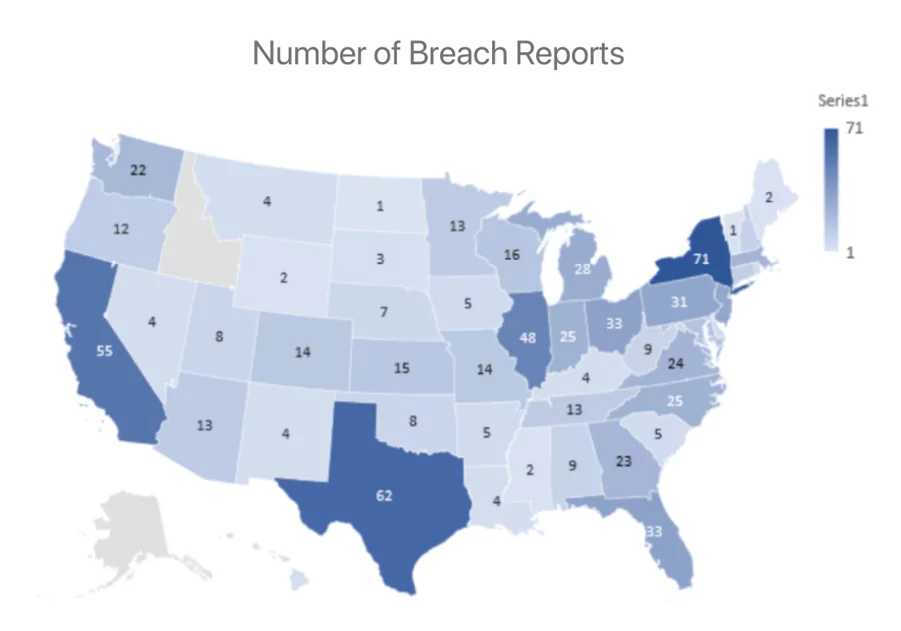
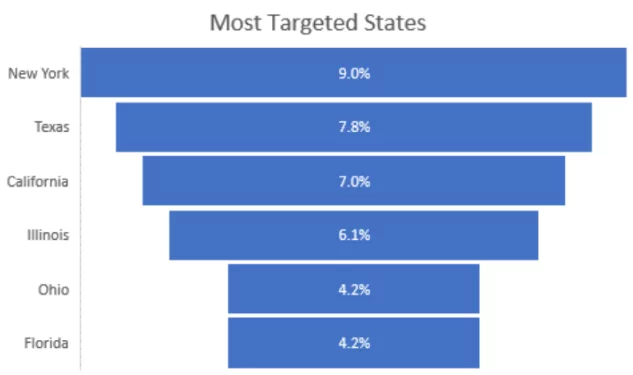
When we looked at the geographic distribution, New York, Texas, California, and Illinois were the most targeted states, and 30% of breach reports came from these states. There were no breach reports from Alaska and Idaho in the scope of this data.
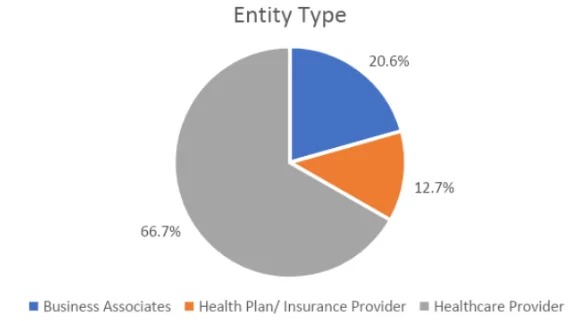
HHS divided the affected entities into Healthcare Providers, Health Plan / Insurance Providers, and Business Associates. The breaches hit mostly healthcare organizations with 66.7%.
Attack Vectors
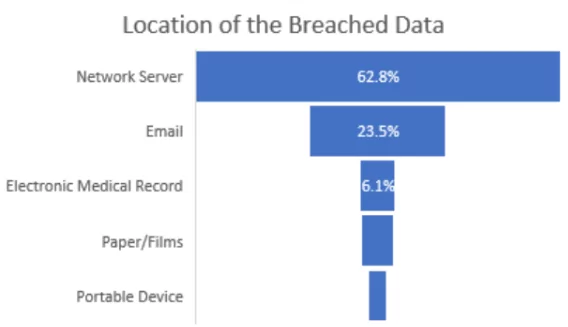
The analysis of attack vectors in healthcare industry breaches reveals that most incidents are classified as hacking (78.9%) or unauthorized access (17.0%). Regarding breached information, network servers were the most commonly targeted location in the breach reports, accounting for nearly 500 out of 790 breaches.
This suggests threat actors are often sophisticated, either having the necessary privileges or acquiring them through privilege escalation. As a result, organizations in the healthcare industry must prioritize dark web monitoring alongside traditional cyber defenses to detect and respond to such threats.
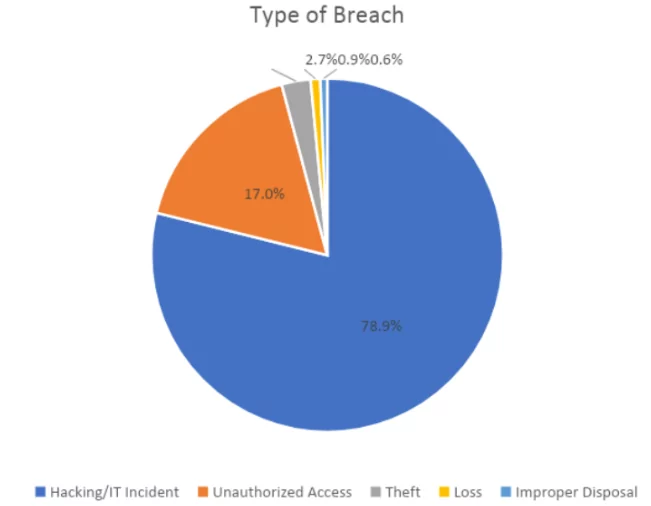
Another prominent attack vector observed is email, which accounted for approximately one-fourth of the breached data locations. This highlights the prevalence of phishing attacks in the healthcare sector. Phishing is a cyber-attack where malicious actors deceive individuals by impersonating trustworthy entities or creating deceptive websites or emails. The ultimate goal is to trick users into divulging sensitive information that can be exploited for fraud.
Phishing Domain Detection
SOCRadar’s Digital Risk Protection platform utilizes artificial intelligence to detect malicious domains that target brands and business networks. The platform can identify suspicious domains and trigger alerts when any changes occur by analyzing millions of domains from major registrars. Machine learning algorithms enable the identification of lookalike domains, while real-time alerts notify users before a domain and SSL certificate expirations, helping maintain a secure digital presence.




































