
How to Protect Yourself from Cyber Attacks During Tax Season?
Not many sane persons in the US will go against the (Internal Revenue Service) IRS. Even some crazies like Batman’s supervillain Joker will stay out of the way of the IRS. However, the IRS’s frightening reputation does not stop cyber threat actors from committing tax fraud.
Joke and the Joker aside, the IRS announced Monday, January 23, 2023, as the start of the 2023 tax year when it started accepting and processing returns for the 2022 tax year. According to the IRS website, most taxpayers have until Tuesday, April 18, 2023, to file their 2022 tax returns, request an extension, and pay any due taxes. During tax season, it’s anticipated that more than 168 million individual tax returns will be submitted.
The Identity Theft Tax Refund Fraud
Obviously, there might be many different tax fraud methods, but we are the most concerned with Identity Theft Tax Refund Fraud (ITTRF). An identity theft tax refund scam “occurs when someone uses your personal [identifying] information (as known as PII) such as your name, Social Security number (SSN) or other identifying information, without your permission, to commit fraud or other crimes,” according to the document, Taxpayer Guide to Identity Theft, prepared by IRS.
ITTRF is a serious problem because the IRS says 92% of all tax returns in 2022 were filed online, and nearly 7.8 million of these activities were reported as suspicious. The Identity Theft Tax Refund Fraud Information Sharing and Analysis Center (ISAC)2022 report cites 5.7 million reports of consumer fraud with a total fraud loss of $5.9 billion in 2021 from the Federal Trade Commission’sCommission’s (FTC) Consumer Sentinel Network report. 25.0% of all reports were about Identity Theft. ISAC commented that “many of those stolen data records will be used for years to come in attempts to defraud the tax system in various forms and schemes.”
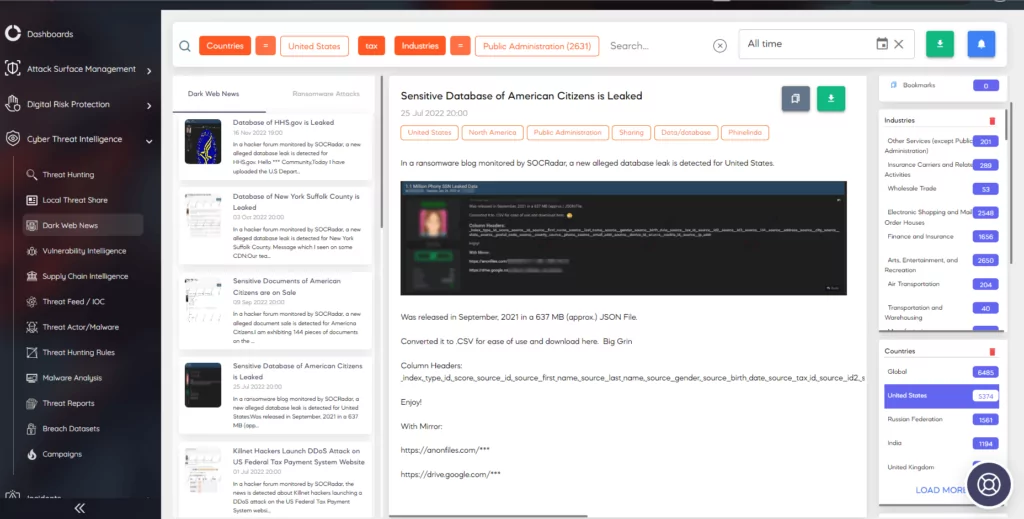
One of the first things you should do to prevent ITTRF is to continuously monitor the dark web for any relevant information about the leaks and breaches that might be relevant to you. SOCRadar’s Dark Web News and Ransomware Attack in the Cyber Threat Intelligence module is ideal for that purpose.
How Secure is Your Tax Info?
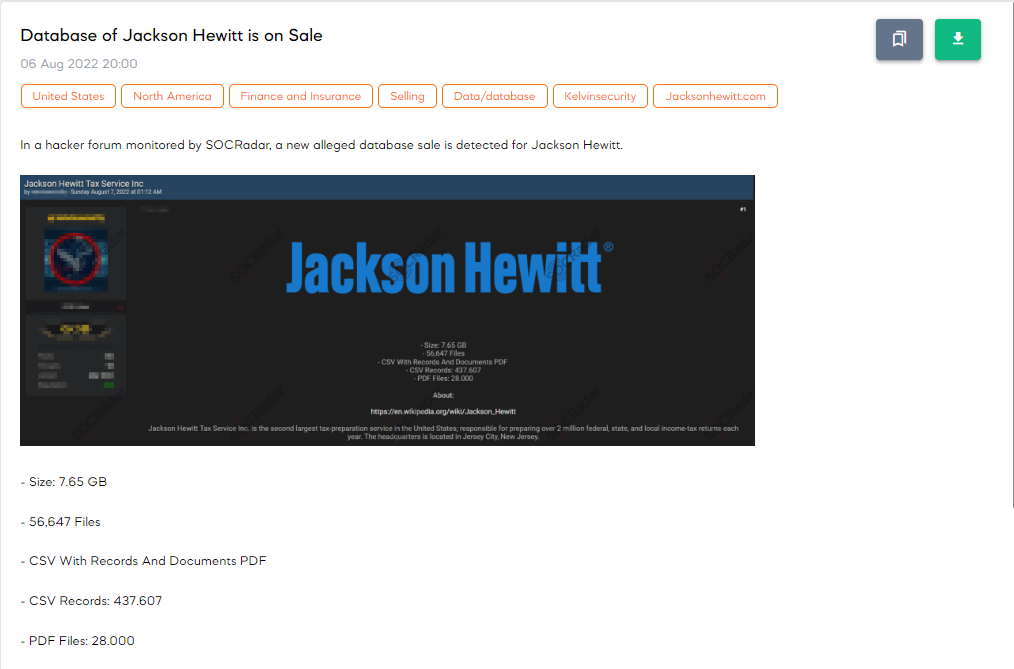
Many people in North America use tax filing platforms like TurboTax, H&R Block, TaxAct, Jackson Hewitt, TaxSlayer, E-file… They all have advantages and disadvantages; people use them for different use cases. Of course, the major tax preparation firms in the US must go through a compliance and audit process to be able to store data. However, that does not mean they are invulnerable to threat actors.
A quick search on Dark Web News in SOCRadar’s Cyber Threat Intelligence module shows that a database allegedly belonging to Jackson Hewitt was on sale in August 2022. Threat actors claimed that the database had 56,647 files, and half of them were pdfs in the 7.65 GB data they had. In addition, the post showed that there were almost 440,000 CSV records.
Another post we came across allegedly belongs to real estate data provider, TaxNetUSA. The entry date of the post to SOCRadar Platform was December 5, 2022. Threat actors claimed they had 121,000 total records.
The platforms related to cryptocurrency could be linked to the cybercrime habitat. However, ZenLedger was a victim in the next post. ZenLedger is one of the leading cryptocurrency tax platforms. On the post, threat actors were selling a database that allegedly belonged to Zenledger, and they claimed the database had more than 60,000 records.
Not only commercial platforms were the victims of threat actors, but also public institutions like Washington State could become a victim. In the following post, threat actors allegedly claimed that they accessed a database of financial institutions through a vulnerability in the CRM (Customer Relationship Management) tool of the Washington State Department of Financial Institutions.
They also stated that the database contained 550,000 contacts, with each contact’scontact’s associated State Licensing information, included personal information such as name, date of birth, mobile phone, email, address, and more.

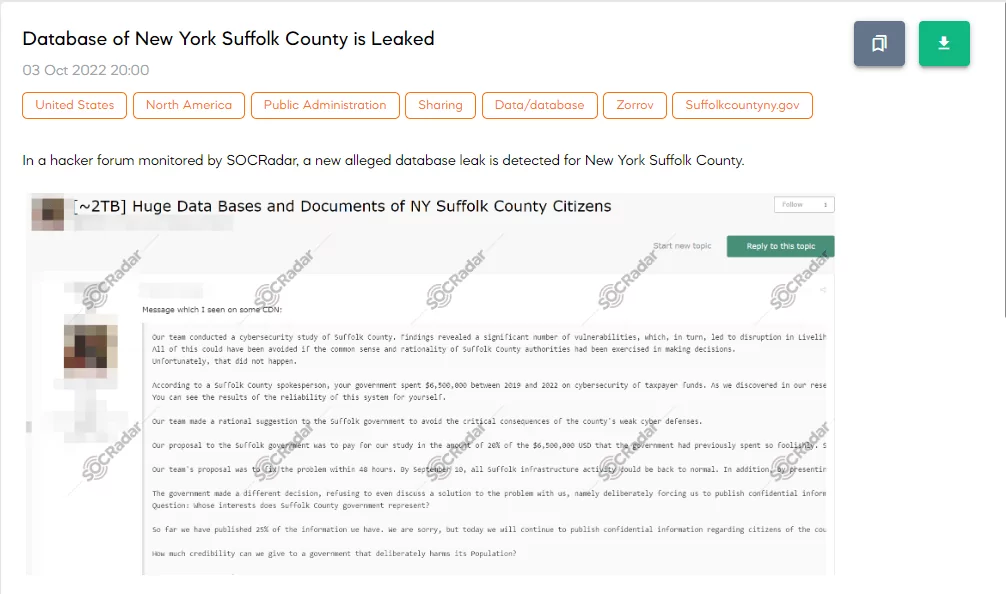
In the next post, an alleged database leak is detected for New York Suffolk County in a hacker forum monitored by SOCRadar.
Many posts also sell individuals’ PII, tax data, and even tax refund forms. This information and documents probably come from personal computers via malware and trojans. In the next post, the threat actor claimed to have pictures of Driving Licenses and Social Security Number Documents and also promised to share some tax documents with the winning bidder.
We cannot take what the threat actors at face value; on the other hand, we cannot ignore what they might have either. Therefore, assuming the worst and preparing for it would be the best course of action.
How Can You Have a More Secure Tax Season?
Even though most threat actors have more time and resources than the defenders, they still have limited resources and scopes. Every layer of security in your cyber defense will deter threat actors and fraudsters, and they will move on to easier and softer targets.
- Using multi-factor authentication where available should be one of the first measures you should take.
- The next should be having a strong password policy or using a dependable password manager.
- Another one is to have an update and patch policy and to use every software in the most secure and updated version.
- Also, filing your taxes early is another good idea. That way, you could avoid a threat actor doing it first.
- If you will use a third party to file your taxes, research them. How and where do they store your info? Do they use encryption? What kind?
As was already indicated, given the continuously changing threat landscape, constantly monitoring the dark web for any breach and leak involving you, your business, and third parties are essential. Dark Web News of SOCRadar Platform will give you this visibility.
The Attack Surface Management (ASM) service of SOCRadar will also generate timely, pertinent, and actionable threat intelligence for the internet-facing assets, ranging from incorrectly configured ports to company credit card numbers.










